你当前正在访问 Microsoft Azure Global Edition 技术文档网站。 如果需要访问由世纪互联运营的 Microsoft Azure 中国技术文档网站,请访问 https://docs.azure.cn。
Microsoft Defender for IoT 用户管理
Microsoft Defender for IoT 在 Azure 门户和本地均提供有工具,用于跨 Defender for IoT 资源管理用户访问权限。
Defender for IoT 的 Azure 用户
在 Azure 门户,使用 Microsoft Entra ID 和 Azure 基于角色的访问控制 (RBAC) 在订阅级别管理用户。 Azure 订阅用户可以有一个或多个用户角色,这决定了他们可以从 Azure 门户(包括 Defender for IoT 中)访问的数据和操作。
使用门户或 PowerShell 为 Azure 订阅用户分配查看数据和执行操作所需的特定角色,例如他们是要查看警报或设备数据,还是要管理定价计划和传感器。
有关详细信息,请参阅在 Azure 门户中管理用户和用于 OT 和企业 IoT 监视的 Azure 用户角色。
Defender for IoT 的本地用户
使用 OT 网络时,除了 Azure 门户外,还可以从本地 OT 网络传感器和本地传感器管理控制台获取 Defender for IoT 服务和数据。
除了 Azure 之外,还需要在 OT 网络传感器和本地管理控制台上定义本地用户。 OT 传感器和本地管理控制台都安装了一组默认特权用户,可用于定义其他管理员和用户。
登录到 OT 传感器以定义传感器用户,并登录到本地管理控制台以定义本地管理控制台用户。
有关详细信息,请参阅使用 Defender for IoT 进行 OT 监视的本地用户和角色。
传感器和本地管理控制台上的 Microsoft Entra ID 支持
你可能想要配置传感器与 Microsoft Entra ID 之间的集成,以允许 Microsoft Entra ID 用户登录到传感器,或使用 Microsoft Entra ID 组,以及分配给组中所有用户的集体权限。
例如,如果拥有大量要向其分配只读访问权限的用户,并且想要在组级别管理这些权限,请使用 Microsoft Entra ID。
Defender for IoT 与 Microsoft Entra ID 的集成支持 LDAP v3 和以下类型的基于 LDAP 的身份验证:
完全身份验证:从 LDAP 服务器检索用户详细信息。 例如名字、姓氏、电子邮件和用户权限。
受信任的用户:仅检索用户密码。 检索到的其他用户详细信息基于传感器中定义的用户。
有关详细信息,请参阅:
用于登录到传感器控制台的单一登录
可以使用 Microsoft Entra ID 为 Defender for IoT 传感器控制台设置单一登录 (SSO)。 通过 SSO,组织的用户可以轻松登录到传感器控制台,不需要跨不同传感器和站点的多个登录凭据。 有关详细信息,请参阅为传感器控制台设置单一登录。
本地全局访问组
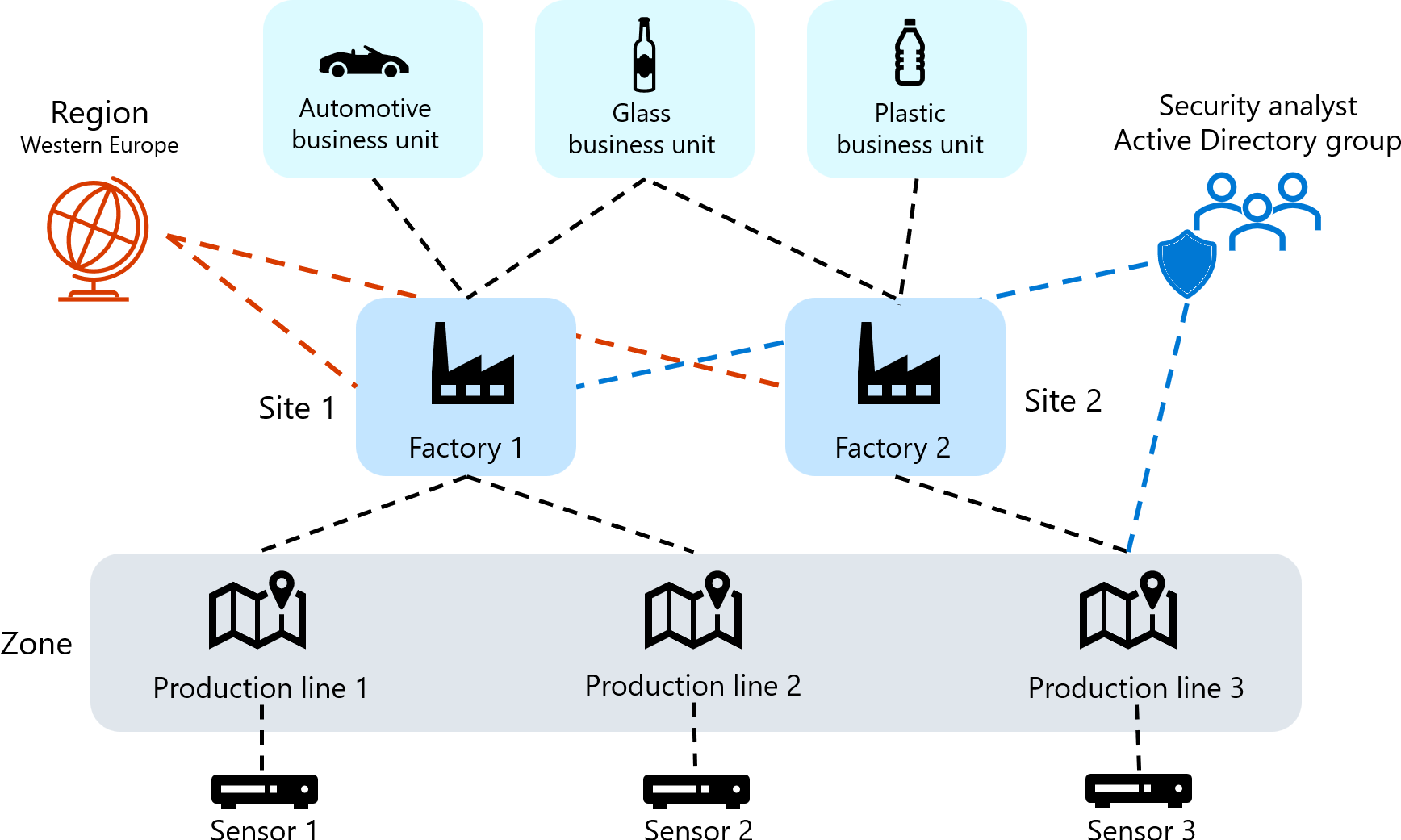
大型组织通常具有基于全局组织结构的复杂用户权限模型。 若要管理本地 Defender for IoT 用户,请使用基于业务部门、区域和站点的全局业务拓扑,然后围绕这些实体定义用户访问权限。
创建用户访问组,以跨 Defender for IoT 本地资源建立全局访问控制。 每个访问组都包含有关可以访问业务拓扑中特定实体(包括业务部门、区域和站点)的用户的规则。
例如,下图显示了如何允许来自 Active Directory 组的安全分析师访问所有西欧汽车和玻璃生产线,以及同一区域中的塑料生产线:
有关详细信息,请参阅为本地用户定义全局访问权限。
提示
访问组和规则通过控制用户在 Defender for IoT 传感器和本地管理控制台上管理和分析设备的位置,帮助实施零信任策略。 有关详细信息,请参阅零信任和 OT/IoT 网络。
后续步骤
有关详细信息,请参阅: