Azure 檔案儲存體和 Azure 檔案同步提供兩種主要類型的端點,用來存取 Azure 檔案共用:
- 公用端點,具有公用 IP 位址,並可從全球任何地方存取。
- 私人端點,存在於虛擬網路內,並具有該虛擬網路位址空間內的私人 IP 位址。
針對 Azure 檔案儲存體 和 Azure 檔案同步,Azure 管理物件(記憶體帳戶和記憶體同步服務)會同時控制公用和私人端點。 記憶體帳戶是一種管理建構,代表您可以部署多個檔案共用的共用記憶體集區,以及其他記憶體資源,例如 Blob 或佇列。 儲存體同步服務是一種管理建構,代表已註冊的伺服器,這是具有與 Azure 檔案同步建立的信任關係的 Windows 檔案伺服器,以及定義同步關聯性拓撲的同步群組。
本文著重於如何為 Azure 檔案儲存體與 Azure File Sync 設定網路端點。若要了解如何為直接存取 Azure 檔案共用 (而非透過 Azure File Sync 在內部部署快取) 設定網路端點,請參閱設定 Azure 檔案儲存體網路端點。
建議您先閱讀 Azure 檔案同步網路注意事項,再閱讀本指南。
必要條件
本文假設:
- 您有 Azure 訂用帳戶。 如果您還沒有訂用帳戶,則先建立免費帳戶,再開始操作。
- 您已在儲存體帳戶中建立 Azure 檔案共用,並希望從內部部署連線至該共用。 若要了解如何建立 Azure 檔案共用,請參閱建立 Azure 檔案共用。
- 您允許將網域流量傳送至下列端點,請參閱 Azure 服務端點:
此外:
- 如果您想要使用 Azure PowerShell,請安裝最新版本。
- 如果您想要使用 Azure CLI,請安裝最新版本。
建立私人端點
建立 Azure 資源的私人端點時,系統會部署下列資源:
-
私人端點:一個 Azure 資源,表示用於儲存體帳戶或儲存體同步服務的私人端點。 您可以將此視為連接 Azure 資源和網路介面的資源。
-
網路介面 (NIC):維護指定虛擬網路/子網路中私人 IP 位址的網路介面。 這是當您部署虛擬機 (VM) 時所部署的完全相同資源,但是不是指派給 VM,而是由私人端點所擁有。
-
私人 DNS 區域:如果您之前從未對此虛擬網路部署過私人端點,系統將會為虛擬網路部署新的私人 DNS 區域。 此 DNS 區域中也會為 Azure 資源建立 DNS A 記錄。 如果您已在此虛擬網路中部署私人端點,將會在現有的 DNS 區域中新增一筆 Azure 資源記錄。 部署 DNS 區域是選擇性的,但強烈建議您簡化所需的 DNS 管理。
注意
本文使用適用於 Azure 公用區域的 DNS 尾碼、適用於儲存體帳戶的 core.windows.net,以及儲存體同步服務的 afs.azure.net。 這也適用於 Azure 主權雲端,例如 Azure 美國政府雲端,只需將適當的後綴取代為您的環境即可。
建立儲存體帳戶的私人端點
瀏覽至您想要為其建立私人端點的儲存帳戶。 從 [服務] 功能表的 [安全性 + 網络] 底下,選取 [網络]、[私人端點連線],然後選取 [+ 私人端點] 以建立新的私人端點。

產生的精靈會有多個頁面需要完成。
在基本窗格中,選取所需的訂用帳戶、資源群組、名稱、網路介面名稱,以及私人端點的區域。 您可以任意選取這些項目,而不一定要與儲存體帳戶相符,但您建立私人端點的所在區域,必須與您要在其中建立私人端點的虛擬網路相同。 然後選取 [下一步:資源]。

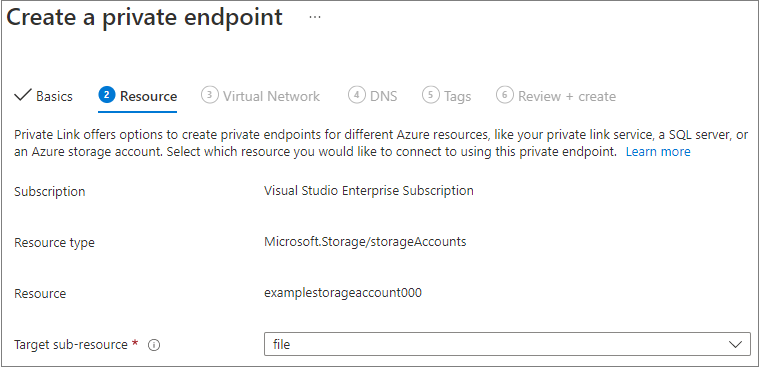
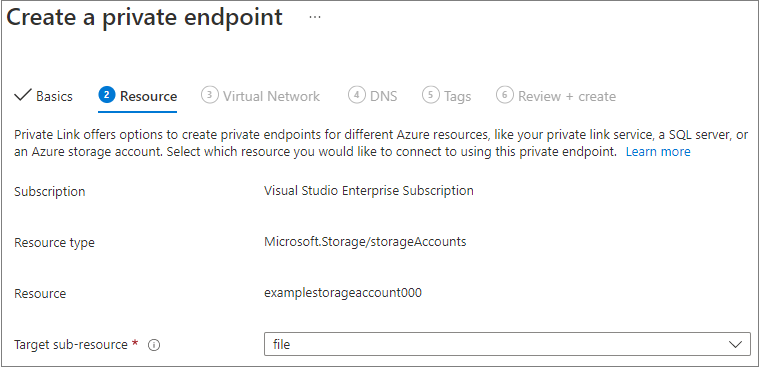
在 [資源] 刀鋒視窗中,選取目標子資源的 [檔案]。 然後選取 [下一步:虛擬網路]。
[c0]虛擬網路[/c0] 面板允許您選擇要新增私人端點的特定虛擬網路和子網路。 為新增的私人端點選取動態或靜態 IP 位址分配。 若選擇靜態,則您也必須提供名稱和私人 IP 位址。 您也可以選擇性指定應用程式安全性群組。 完成後,選取 [下一步:DNS]。

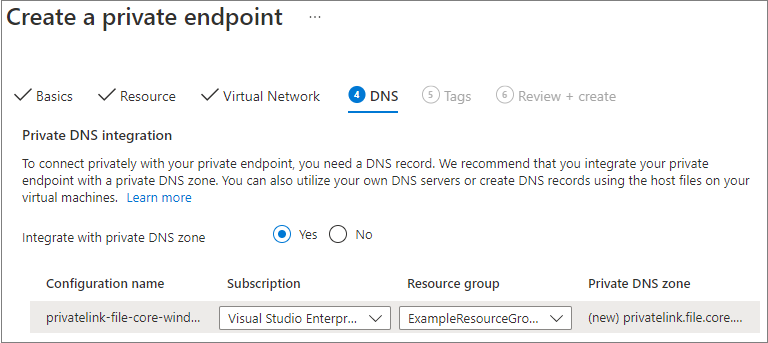
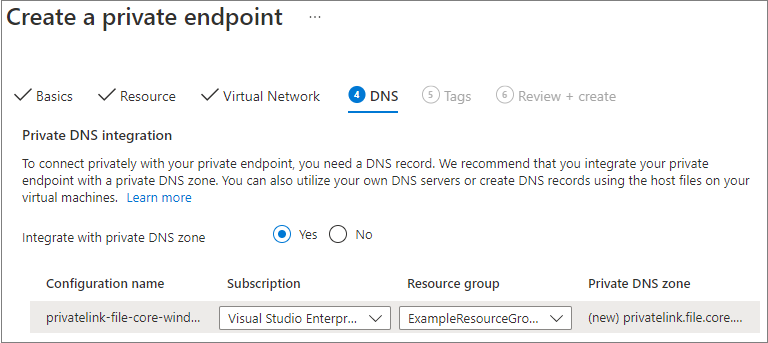
在 DNS 面板包含整合您的私人端點與專用 DNS 區域的資訊。 確定訂用帳戶和資源群組正確,然後選取 [下一步:標籤]。
您可以選擇性地套用標籤來分類您的資源,例如將 Environment 名稱和 Test 值套用到所有測試資源。 視需要輸入名稱/值組,然後選取 [下一步:檢閱 + 建立]。

選取 [建立] 以建立私人端點。
如果您的虛擬網路中有 VM,或已依照設定 Azure 檔案儲存體的 DNS 轉送所述設定 DNS 轉送,您可以從 PowerShell、命令列或終端機 (適用於 Windows、Linux 或 macOS) 執行下列命令,以測試您的私人端點是否正確設定。 您必須將 <storage-account-name> 取代為適當的儲存體帳戶名稱:
nslookup <storage-account-name>.file.core.windows.net
如果一切順利運作,您應該會看到下列輸出,其中 192.168.0.5 是虛擬網路中私人端點的私人IP位址(Windows 顯示的輸出):
Server: UnKnown
Address: 10.2.4.4
Non-authoritative answer:
Name: storageaccount.privatelink.file.core.windows.net
Address: 192.168.0.5
Aliases: storageaccount.file.core.windows.net
若要為您的儲存體帳戶建立私人端點,您必須先取得儲存體帳戶與要新增私人端點之虛擬網路子網路的參考。 取代下方的 <storage-account-resource-group-name>、<storage-account-name>、<vnet-resource-group-name>、<vnet-name> 和 <vnet-subnet-name>:
$storageAccountResourceGroupName = "<storage-account-resource-group-name>"
$storageAccountName = "<storage-account-name>"
$virtualNetworkResourceGroupName = "<vnet-resource-group-name>"
$virtualNetworkName = "<vnet-name>"
$subnetName = "<vnet-subnet-name>"
# Get storage account reference, and throw error if it doesn't exist
$storageAccount = Get-AzStorageAccount `
-ResourceGroupName $storageAccountResourceGroupName `
-Name $storageAccountName `
-ErrorAction SilentlyContinue
if ($null -eq $storageAccount) {
$errorMessage = "Storage account $storageAccountName not found "
$errorMessage += "in resource group $storageAccountResourceGroupName."
Write-Error -Message $errorMessage -ErrorAction Stop
}
# Get virtual network reference, and throw error if it doesn't exist
$virtualNetwork = Get-AzVirtualNetwork `
-ResourceGroupName $virtualNetworkResourceGroupName `
-Name $virtualNetworkName `
-ErrorAction SilentlyContinue
if ($null -eq $virtualNetwork) {
$errorMessage = "Virtual network $virtualNetworkName not found "
$errorMessage += "in resource group $virtualNetworkResourceGroupName."
Write-Error -Message $errorMessage -ErrorAction Stop
}
# Get reference to virtual network subnet, and throw error if it doesn't exist
$subnet = $virtualNetwork | `
Select-Object -ExpandProperty Subnets | `
Where-Object { $_.Name -eq $subnetName }
if ($null -eq $subnet) {
Write-Error `
-Message "Subnet $subnetName not found in virtual network $virtualNetworkName." `
-ErrorAction Stop
}
若要建立私人端點,您必須對儲存體帳戶建立私人連結服務連線。 私人連結服務連線是建立私人端點時的輸入項目。
# Disable private endpoint network policies
$subnet.PrivateEndpointNetworkPolicies = "Disabled"
$virtualNetwork = $virtualNetwork | `
Set-AzVirtualNetwork -ErrorAction Stop
# Create a private link service connection to the storage account.
$privateEndpointConnection = New-AzPrivateLinkServiceConnection `
-Name "$storageAccountName-Connection" `
-PrivateLinkServiceId $storageAccount.Id `
-GroupId "file" `
-ErrorAction Stop
# Create a new private endpoint.
$privateEndpoint = New-AzPrivateEndpoint `
-ResourceGroupName $storageAccountResourceGroupName `
-Name "$storageAccountName-PrivateEndpoint" `
-Location $virtualNetwork.Location `
-Subnet $subnet `
-PrivateLinkServiceConnection $privateEndpointConnection `
-ErrorAction Stop
建立 Azure 私人 DNS 區域可讓儲存體帳戶的原始名稱 (例如 storageaccount.file.core.windows.net) 解析為虛擬網路內的私人 IP。 雖然從建立私人端點的角度來看,這是選擇性項目,但直接使用 AD 使用者主體來掛接 Azure 檔案共用或透過 REST API 來存取時,這確實是必要項目。
# Get the desired storage account suffix (core.windows.net for public cloud).
# This is done like this so this script will seamlessly work for non-public Azure.
$storageAccountSuffix = Get-AzContext | `
Select-Object -ExpandProperty Environment | `
Select-Object -ExpandProperty StorageEndpointSuffix
# For public cloud, this will generate the following DNS suffix:
# privatelink.file.core.windows.net.
$dnsZoneName = "privatelink.file.$storageAccountSuffix"
# Find a DNS zone matching desired name attached to this virtual network.
$dnsZone = Get-AzPrivateDnsZone | `
Where-Object { $_.Name -eq $dnsZoneName } | `
Where-Object {
$privateDnsLink = Get-AzPrivateDnsVirtualNetworkLink `
-ResourceGroupName $_.ResourceGroupName `
-ZoneName $_.Name `
-ErrorAction SilentlyContinue
$privateDnsLink.VirtualNetworkId -eq $virtualNetwork.Id
}
if ($null -eq $dnsZone) {
# No matching DNS zone attached to virtual network, so create new one.
$dnsZone = New-AzPrivateDnsZone `
-ResourceGroupName $virtualNetworkResourceGroupName `
-Name $dnsZoneName `
-ErrorAction Stop
$privateDnsLink = New-AzPrivateDnsVirtualNetworkLink `
-ResourceGroupName $virtualNetworkResourceGroupName `
-ZoneName $dnsZoneName `
-Name "$virtualNetworkName-DnsLink" `
-VirtualNetworkId $virtualNetwork.Id `
-ErrorAction Stop
}
現在您已有專用 DNS 區域的參照,接下來您必須為儲存體帳戶建立 A 記錄。
$privateEndpointIP = $privateEndpoint | `
Select-Object -ExpandProperty NetworkInterfaces | `
Select-Object @{
Name = "NetworkInterfaces";
Expression = { Get-AzNetworkInterface -ResourceId $_.Id }
} | `
Select-Object -ExpandProperty NetworkInterfaces | `
Select-Object -ExpandProperty IpConfigurations | `
Select-Object -ExpandProperty PrivateIpAddress
$privateDnsRecordConfig = New-AzPrivateDnsRecordConfig `
-IPv4Address $privateEndpointIP
New-AzPrivateDnsRecordSet `
-ResourceGroupName $virtualNetworkResourceGroupName `
-Name $storageAccountName `
-RecordType A `
-ZoneName $dnsZoneName `
-Ttl 600 `
-PrivateDnsRecords $privateDnsRecordConfig `
-ErrorAction Stop | `
Out-Null
如果您的虛擬網路內有 VM,或如 Azure 檔案儲存體的 DNS 轉送設定中所述已設定 DNS 轉送,您可以使用下列命令測試您的私人端點是否已正確設定。
$storageAccountHostName = [System.Uri]::new($storageAccount.PrimaryEndpoints.file) | `
Select-Object -ExpandProperty Host
Resolve-DnsName -Name $storageAccountHostName
如果一切順利運作,您應該會看到下列輸出,其中 192.168.0.5 是虛擬網路中私人端點的私人IP位址:
Name Type TTL Section NameHost
---- ---- --- ------- --------
storageaccount.file.core.windows CNAME 60 Answer storageaccount.privatelink.file.core.windows.net
.net
Name : storageaccount.privatelink.file.core.windows.net
QueryType : A
TTL : 600
Section : Answer
IP4Address : 192.168.0.5
若要為您的儲存帳戶建立私人端點,您必須先取得對儲存帳戶及您希望新增私人端點之虛擬網路子網路的參考資料。 取代下方的 <storage-account-resource-group-name>、<storage-account-name>、<vnet-resource-group-name>、<vnet-name> 和 <vnet-subnet-name>:
storageAccountResourceGroupName="<storage-account-resource-group-name>"
storageAccountName="<storage-account-name>"
virtualNetworkResourceGroupName="<vnet-resource-group-name>"
virtualNetworkName="<vnet-name>"
subnetName="<vnet-subnet-name>"
# Get storage account ID
storageAccount=$(az storage account show \
--resource-group $storageAccountResourceGroupName \
--name $storageAccountName \
--query "id" | \
tr -d '"')
# Get virtual network ID
virtualNetwork=$(az network vnet show \
--resource-group $virtualNetworkResourceGroupName \
--name $virtualNetworkName \
--query "id" | \
tr -d '"')
# Get subnet ID
subnet=$(az network vnet subnet show \
--resource-group $virtualNetworkResourceGroupName \
--vnet-name $virtualNetworkName \
--name $subnetName \
--query "id" | \
tr -d '"')
若要建立私人端點,您必須先確定子網路的私人端點網路原則已設定為停用。 然後,您可以使用 az network private-endpoint create 命令來建立私人端點。
# Disable private endpoint network policies
az network vnet subnet update \
--ids $subnet \
--disable-private-endpoint-network-policies \
--output none
# Get virtual network location
region=$(az network vnet show \
--ids $virtualNetwork \
--query "location" | \
tr -d '"')
# Create a private endpoint
privateEndpoint=$(az network private-endpoint create \
--resource-group $storageAccountResourceGroupName \
--name "$storageAccountName-PrivateEndpoint" \
--location $region \
--subnet $subnet \
--private-connection-resource-id $storageAccount \
--group-id "file" \
--connection-name "$storageAccountName-Connection" \
--query "id" | \
tr -d '"')
建立 Azure 私人 DNS 區域可讓儲存體帳戶的原始名稱 (例如 storageaccount.file.core.windows.net) 解析為虛擬網路內的私人 IP。 雖然從建立私人端點的角度來看,這是選擇性項目,但使用 AD 使用者主體來掛接 Azure 檔案共用或透過 REST API 來存取時,這確實是必要項目。
# Get the desired storage account suffix (core.windows.net for public cloud).
# This is done like this so this script will seamlessly work for non-public Azure.
storageAccountSuffix=$(az cloud show \
--query "suffixes.storageEndpoint" | \
tr -d '"')
# For public cloud, this will generate the following DNS suffix:
# privatelink.file.core.windows.net.
dnsZoneName="privatelink.file.$storageAccountSuffix"
# Find a DNS zone matching desired name attached to this virtual network.
possibleDnsZones=""
possibleDnsZones=$(az network private-dns zone list \
--query "[?name == '$dnsZoneName'].id" \
--output tsv)
dnsZone=""
possibleDnsZone=""
for possibleDnsZone in $possibleDnsZones
do
possibleResourceGroupName=$(az resource show \
--ids $possibleDnsZone \
--query "resourceGroup" | \
tr -d '"')
link=$(az network private-dns link vnet list \
--resource-group $possibleResourceGroupName \
--zone-name $dnsZoneName \
--query "[?virtualNetwork.id == '$virtualNetwork'].id" \
--output tsv)
if [ -z $link ]
then
echo "1" > /dev/null
else
dnsZoneResourceGroup=$possibleResourceGroupName
dnsZone=$possibleDnsZone
break
fi
done
if [ -z $dnsZone ]
then
# No matching DNS zone attached to virtual network, so create a new one
dnsZone=$(az network private-dns zone create \
--resource-group $virtualNetworkResourceGroupName \
--name $dnsZoneName \
--query "id" | \
tr -d '"')
az network private-dns link vnet create \
--resource-group $virtualNetworkResourceGroupName \
--zone-name $dnsZoneName \
--name "$virtualNetworkName-DnsLink" \
--virtual-network $virtualNetwork \
--registration-enabled false \
--output none
dnsZoneResourceGroup=$virtualNetworkResourceGroupName
fi
現在您已取得私人 DNS 區域的參考,必須為您的儲存體帳戶建立 A 記錄。
privateEndpointNIC=$(az network private-endpoint show \
--ids $privateEndpoint \
--query "networkInterfaces[0].id" | \
tr -d '"')
privateEndpointIP=$(az network nic show \
--ids $privateEndpointNIC \
--query "ipConfigurations[0].privateIPAddress" | \
tr -d '"')
az network private-dns record-set a create \
--resource-group $dnsZoneResourceGroup \
--zone-name $dnsZoneName \
--name $storageAccountName \
--output none
az network private-dns record-set a add-record \
--resource-group $dnsZoneResourceGroup \
--zone-name $dnsZoneName \
--record-set-name $storageAccountName \
--ipv4-address $privateEndpointIP \
--output none
如果您的虛擬網路內有 VM,或者如設定 Azure 檔案儲存體的 DNS 轉送中所述,您已設定 DNS 轉送,您可以使用下列命令測試您的私人連接點是否已正確設定。
httpEndpoint=$(az storage account show \
--resource-group $storageAccountResourceGroupName \
--name $storageAccountName \
--query "primaryEndpoints.file" | \
tr -d '"')
hostName=$(echo $httpEndpoint | cut -c7-$(expr length $httpEndpoint) | tr -d "/")
nslookup $hostName
如果一切順利運作,您應該會看到下列輸出,其中 192.168.0.5 是虛擬網路中私人端點的私人IP位址:
Server: 127.0.0.53
Address: 127.0.0.53#53
Non-authoritative answer:
storageaccount.file.core.windows.net canonical name = storageaccount.privatelink.file.core.windows.net.
Name: storageaccount.privatelink.file.core.windows.net
Address: 192.168.0.5
建立儲存體同步服務私人端點
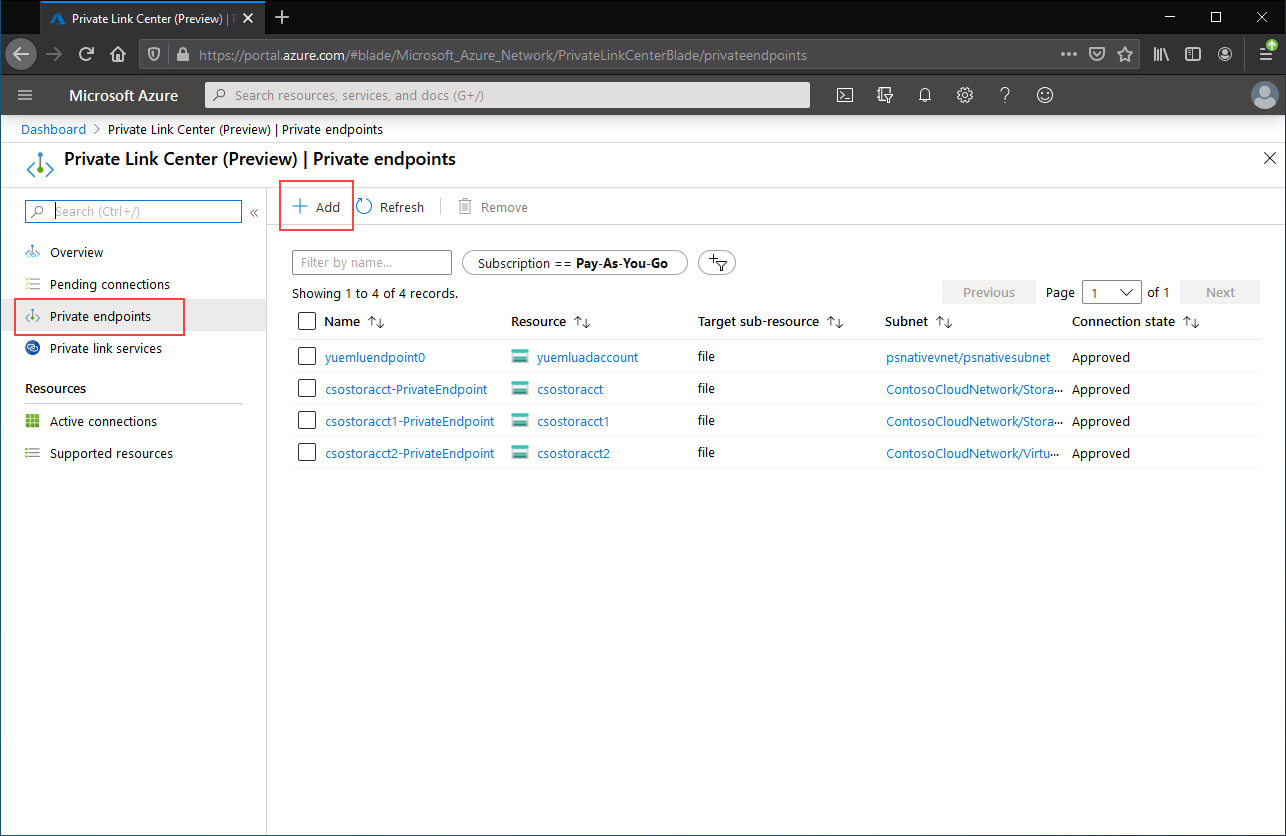
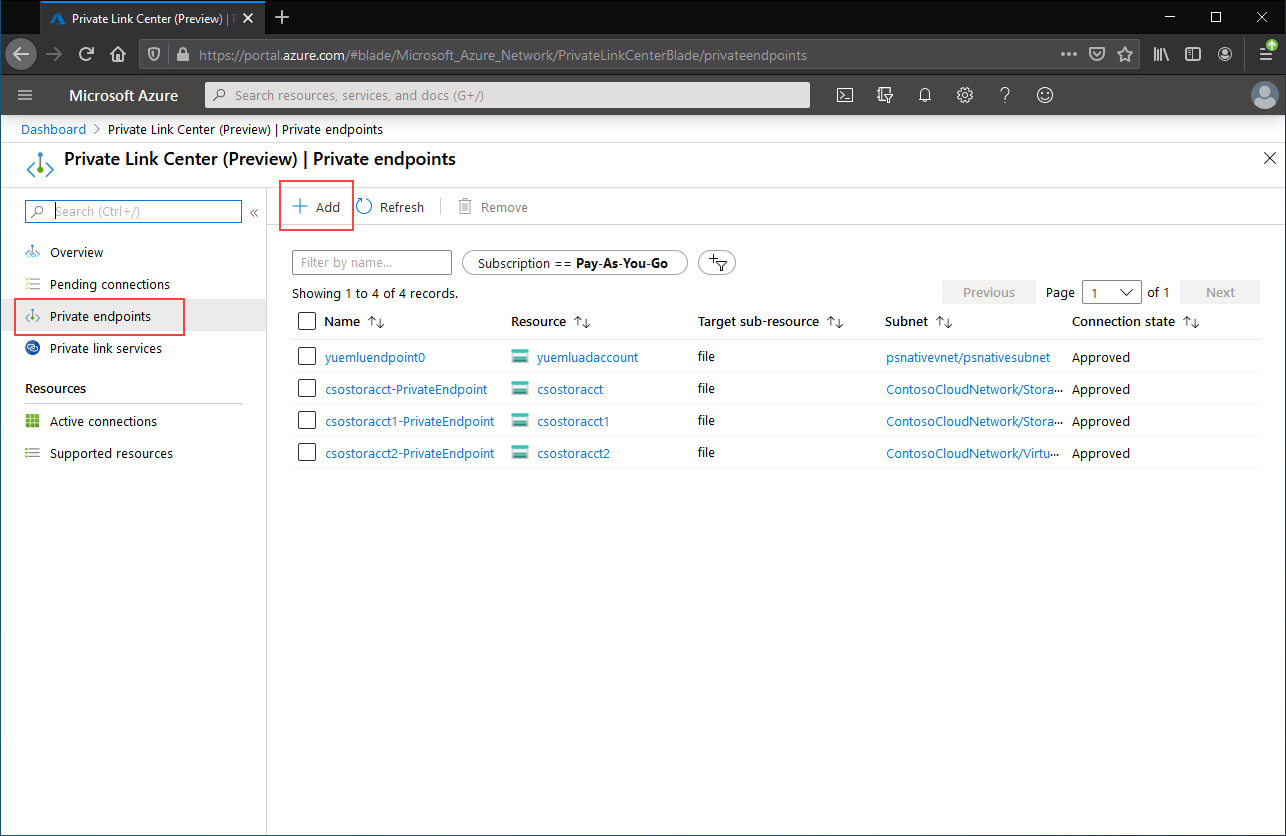
在 Azure 入口網站頂端的搜尋列中輸入 Private Link,瀏覽至 Private Link 中心。 在 Private Link 中心的目錄中,選取 [私人端點],然後 [+ 新增] 以建立新的私人端點。
產生的精靈會有多個頁面需要完成。
在基本窗格中,選取所需的資源群組、名稱,以及私人端點的區域。 這些可以是您想要的任何內容,而不一定要與儲存體同步服務相符,但您建立私人端點的所在區域,必須與您要在其中建立私人端點的虛擬網路相同。
![建立私人端點區段 [基本] 區段的螢幕快照](media/storage-sync-files-networking-endpoints/create-storage-sync-private-endpoint-1.png)
在資源窗格中,選取連線至我目錄中的 Azure 資源的選項按鈕。 在 [資源類型] 下,針對資源類型選取 [Microsoft.StorageSync/storageSyncServices]。
組態窗格可讓您選取要新增私人端點的特定虛擬網路與子網路。 選取與您在上述儲存體帳戶中使用的相同虛擬網路。 [設定] 面板也包含用於建立/更新私有 DNS 區的資訊。
選取 [檢閱 + 建立] 以建立私人端點。
您可以執行下列 PowerShell 命令,測試您的私人端點是否已正確設定。
$privateEndpointResourceGroupName = "<your-private-endpoint-resource-group>"
$privateEndpointName = "<your-private-endpoint-name>"
Get-AzPrivateEndpoint `
-ResourceGroupName $privateEndpointResourceGroupName `
-Name $privateEndpointName `
-ErrorAction Stop | `
Select-Object -ExpandProperty NetworkInterfaces | `
Select-Object -ExpandProperty Id | `
ForEach-Object { Get-AzNetworkInterface -ResourceId $_ } | `
Select-Object -ExpandProperty IpConfigurations | `
Select-Object -ExpandProperty PrivateLinkConnectionProperties | `
Select-Object -ExpandProperty Fqdns | `
ForEach-Object { Resolve-DnsName -Name $_ } | `
Format-List
如果一切正常運作,您應該會看到下列輸出,其中 192.168.1.4、 192.168.1.5192.168.1.6和 192.168.1.7 是指派給私人端點的私人IP位址:
Name : mysssmanagement.westus2.afs.azure.net
Type : CNAME
TTL : 60
Section : Answer
NameHost : mysssmanagement.westus2.privatelink.afs.azure.net
Name : mysssmanagement.westus2.privatelink.afs.azure.net
QueryType : A
TTL : 60
Section : Answer
IP4Address : 192.168.1.4
Name : myssssyncp.westus2.afs.azure.net
Type : CNAME
TTL : 60
Section : Answer
NameHost : myssssyncp.westus2.privatelink.afs.azure.net
Name : myssssyncp.westus2.privatelink.afs.azure.net
QueryType : A
TTL : 60
Section : Answer
IP4Address : 192.168.1.5
Name : myssssyncs.westus2.afs.azure.net
Type : CNAME
TTL : 60
Section : Answer
NameHost : myssssyncs.westus2.privatelink.afs.azure.net
Name : myssssyncs.westus2.privatelink.afs.azure.net
QueryType : A
TTL : 60
Section : Answer
IP4Address : 192.168.1.6
Name : mysssmonitoring.westus2.afs.azure.net
Type : CNAME
TTL : 60
Section : Answer
NameHost : mysssmonitoring.westus2.privatelink.afs.azure.net
Name : mysssmonitoring.westus2.privatelink.afs.azure.net
QueryType : A
TTL : 60
Section : Answer
IP4Address : 192.168.1.7
若要為儲存體同步服務建立私人端點,您必須先取得儲存體同步服務的參考資料。 請記得將 <storage-sync-service-resource-group> 和 <storage-sync-service> 取代為適用於您環境的正確值。 下列 PowerShell 命令假設您已填入虛擬網路資訊。
$storageSyncServiceResourceGroupName = "<storage-sync-service-resource-group>"
$storageSyncServiceName = "<storage-sync-service>"
$storageSyncService = Get-AzStorageSyncService `
-ResourceGroupName $storageSyncServiceResourceGroupName `
-Name $storageSyncServiceName `
-ErrorAction SilentlyContinue
if ($null -eq $storageSyncService) {
$errorMessage = "Storage Sync Service $storageSyncServiceName not found "
$errorMessage += "in resource group $storageSyncServiceResourceGroupName."
Write-Error -Message $errorMessage -ErrorAction Stop
}
若要建立私人端點,您必須建立儲存體同步服務的私人連結服務連線。 私人連結連線是建立私人端點時的輸入項目。
# Disable private endpoint network policies
$subnet.PrivateEndpointNetworkPolicies = "Disabled"
$virtualNetwork = $virtualNetwork | `
Set-AzVirtualNetwork -ErrorAction Stop
# Create a private link service connection to the storage account.
$privateEndpointConnection = New-AzPrivateLinkServiceConnection `
-Name "$storageSyncServiceName-Connection" `
-PrivateLinkServiceId $storageSyncService.ResourceId `
-GroupId "Afs" `
-ErrorAction Stop
# Create a new private endpoint.
$privateEndpoint = New-AzPrivateEndpoint `
-ResourceGroupName $storageSyncServiceResourceGroupName `
-Name "$storageSyncServiceName-PrivateEndpoint" `
-Location $virtualNetwork.Location `
-Subnet $subnet `
-PrivateLinkServiceConnection $privateEndpointConnection `
-ErrorAction Stop
建立 Azure 私人 DNS 區域,可讓儲存體同步服務的主機名稱 (例如 mysssmanagement.westus2.afs.azure.net) 解析為虛擬網路中儲存體同步服務的正確私人 IP。 雖然從建立私人端點的觀點而言是選擇性的,但 Azure 檔案同步 代理程式必須明確存取記憶體同步服務。
# Get the desired Storage Sync Service suffix (afs.azure.net for public cloud).
# This is done like this so this script will seamlessly work for non-public Azure.
$azureEnvironment = Get-AzContext | `
Select-Object -ExpandProperty Environment | `
Select-Object -ExpandProperty Name
switch($azureEnvironment) {
"AzureCloud" {
$storageSyncSuffix = "afs.azure.net"
}
"AzureUSGovernment" {
$storageSyncSuffix = "afs.azure.us"
}
"AzureChinaCloud" {
$storageSyncSuffix = "afs.azure.cn"
}
default {
Write-Error
-Message "The Azure environment $_ is not currently supported by Azure File Sync." `
-ErrorAction Stop
}
}
# For public cloud, this will generate the following DNS suffix:
# privatelink.afs.azure.net
$dnsZoneName = "privatelink.$storageSyncSuffix"
# Find a DNS zone matching desired name attached to this virtual network.
$dnsZone = Get-AzPrivateDnsZone | `
Where-Object { $_.Name -eq $dnsZoneName } | `
Where-Object {
$privateDnsLink = Get-AzPrivateDnsVirtualNetworkLink `
-ResourceGroupName $_.ResourceGroupName `
-ZoneName $_.Name `
-ErrorAction SilentlyContinue
$privateDnsLink.VirtualNetworkId -eq $virtualNetwork.Id
}
if ($null -eq $dnsZone) {
# No matching DNS zone attached to virtual network, so create new one.
$dnsZone = New-AzPrivateDnsZone `
-ResourceGroupName $virtualNetworkResourceGroupName `
-Name $dnsZoneName `
-ErrorAction Stop
$privateDnsLink = New-AzPrivateDnsVirtualNetworkLink `
-ResourceGroupName $virtualNetworkResourceGroupName `
-ZoneName $dnsZoneName `
-Name "$virtualNetworkName-DnsLink" `
-VirtualNetworkId $virtualNetwork.Id `
-ErrorAction Stop
}
現在您已有私人 DNS 區域的參考,接下來您必須為儲存體同步服務建立 A 記錄。
$privateEndpointIpFqdnMappings = $privateEndpoint | `
Select-Object -ExpandProperty NetworkInterfaces | `
Select-Object -ExpandProperty Id | `
ForEach-Object { Get-AzNetworkInterface -ResourceId $_ } | `
Select-Object -ExpandProperty IpConfigurations | `
ForEach-Object {
$privateIpAddress = $_.PrivateIpAddress;
$_ | `
Select-Object -ExpandProperty PrivateLinkConnectionProperties | `
Select-Object -ExpandProperty Fqdns | `
Select-Object `
@{
Name = "PrivateIpAddress";
Expression = { $privateIpAddress }
}, `
@{
Name = "FQDN";
Expression = { $_ }
}
}
foreach($ipFqdn in $privateEndpointIpFqdnMappings) {
$privateDnsRecordConfig = New-AzPrivateDnsRecordConfig `
-IPv4Address $ipFqdn.PrivateIpAddress
$dnsEntry = $ipFqdn.FQDN.Substring(0,
$ipFqdn.FQDN.IndexOf(".", $ipFqdn.FQDN.IndexOf(".") + 1))
New-AzPrivateDnsRecordSet `
-ResourceGroupName $virtualNetworkResourceGroupName `
-Name $dnsEntry `
-RecordType A `
-ZoneName $dnsZoneName `
-Ttl 600 `
-PrivateDnsRecords $privateDnsRecordConfig `
-ErrorAction Stop | `
Out-Null
}
若要為您的 Storage Sync Service 建立私人端點,您必須先取得 Storage Sync Service 的參考。 請記得將 <storage-sync-service-resource-group> 和 <storage-sync-service> 取代為適用於您環境的正確值。 下列 CLI 命令假設您已填入虛擬網路資訊。
storageSyncServiceResourceGroupName="<storage-sync-service-resource-group>"
storageSyncServiceName="<storage-sync-service>"
storageSyncService=$(az resource show \
--resource-group $storageSyncServiceResourceGroupName \
--name $storageSyncServiceName \
--resource-type "Microsoft.StorageSync/storageSyncServices" \
--query "id" | \
tr -d '"')
storageSyncServiceRegion=$(az resource show \
--resource-group $storageSyncServiceResourceGroupName \
--name $storageSyncServiceName \
--resource-type "Microsoft.StorageSync/storageSyncServices" \
--query "location" | \
tr -d '"')
若要建立私人端點,您必須先確定子網路的私人端點網路原則已設定為停用。 然後,您可以使用 az network private-endpoint create 命令來建立私人端點。
# Disable private endpoint network policies
az network vnet subnet update \
--ids $subnet \
--disable-private-endpoint-network-policies \
--output none
# Get virtual network location
region=$(az network vnet show \
--ids $virtualNetwork \
--query "location" | \
tr -d '"')
# Create a private endpoint
privateEndpoint=$(az network private-endpoint create \
--resource-group $storageSyncServiceResourceGroupName \
--name "$storageSyncServiceName-PrivateEndpoint" \
--location $region \
--subnet $subnet \
--private-connection-resource-id $storageSyncService \
--group-id "Afs" \
--connection-name "$storageSyncServiceName-Connection" \
--query "id" | \
tr -d '"')
建立 Azure 私人 DNS 區域,可讓儲存體同步服務的主機名稱 (例如 mysssmanagement.westus2.afs.azure.net) 解析為虛擬網路中儲存體同步服務的正確私人 IP。 雖然從建立私人端點的觀點而言是選擇性的,但 Azure 檔案同步 代理程式必須明確存取記憶體同步服務。
# Get the desired storage account suffix (afs.azure.net for public cloud).
# This is done like this so this script will seamlessly work for non-public Azure.
azureEnvironment=$(az cloud show \
--query "name" |
tr -d '"')
storageSyncSuffix=""
if [ $azureEnvironment == "AzureCloud" ]
then
storageSyncSuffix="afs.azure.net"
elif [ $azureEnvironment == "AzureUSGovernment" ]
then
storageSyncSuffix="afs.azure.us"
else
echo "Unsupported Azure environment $azureEnvironment."
fi
# For public cloud, this will generate the following DNS suffix:
# privatelinke.afs.azure.net.
dnsZoneName="privatelink.$storageSyncSuffix"
# Find a DNS zone matching desired name attached to this virtual network.
possibleDnsZones=""
possibleDnsZones=$(az network private-dns zone list \
--query "[?name == '$dnsZoneName'].id" \
--output tsv)
dnsZone=""
possibleDnsZone=""
for possibleDnsZone in $possibleDnsZones
do
possibleResourceGroupName=$(az resource show \
--ids $possibleDnsZone \
--query "resourceGroup" | \
tr -d '"')
link=$(az network private-dns link vnet list \
--resource-group $possibleResourceGroupName \
--zone-name $dnsZoneName \
--query "[?virtualNetwork.id == '$virtualNetwork'].id" \
--output tsv)
if [ -z $link ]
then
echo "1" > /dev/null
else
dnsZoneResourceGroup=$possibleResourceGroupName
dnsZone=$possibleDnsZone
break
fi
done
if [ -z $dnsZone ]
then
# No matching DNS zone attached to virtual network, so create a new one
dnsZone=$(az network private-dns zone create \
--resource-group $virtualNetworkResourceGroupName \
--name $dnsZoneName \
--query "id" | \
tr -d '"')
az network private-dns link vnet create \
--resource-group $virtualNetworkResourceGroupName \
--zone-name $dnsZoneName \
--name "$virtualNetworkName-DnsLink" \
--virtual-network $virtualNetwork \
--registration-enabled false \
--output none
dnsZoneResourceGroup=$virtualNetworkResourceGroupName
fi
現在您已有私人 DNS 區域的參考,接下來您必須為儲存體同步服務建立 A 記錄。
privateEndpointNIC=$(az network private-endpoint show \
--ids $privateEndpoint \
--query "networkInterfaces[0].id" | \
tr -d '"')
privateIpAddresses=$(az network nic show \
--ids $privateEndpointNIC \
--query "ipConfigurations[].privateIpAddress" \
--output tsv)
hostNames=$(az network nic show \
--ids $privateEndpointNIC \
--query "ipConfigurations[].privateLinkConnectionProperties.fqdns[]" \
--output tsv)
i=0
for privateIpAddress in $privateIpAddresses
do
j=0
targetHostName=""
for hostName in $hostNames
do
if [ $i == $j ]
then
targetHostName=$hostName
break
fi
j=$(expr $j + 1)
done
endpointName=$(echo $targetHostName | \
cut -c1-$(expr $(expr index $targetHostName ".") - 1))
az network private-dns record-set a create \
--resource-group $dnsZoneResourceGroup \
--zone-name $dnsZoneName \
--name "$endpointName.$storageSyncServiceRegion" \
--output none
az network private-dns record-set a add-record \
--resource-group $dnsZoneResourceGroup \
--zone-name $dnsZoneName \
--record-set-name "$endpointName.$storageSyncServiceRegion" \
--ipv4-address $privateIpAddress \
--output none
i=$(expr $i + 1)
done
限制公用端點的存取
您可以限制對儲存體帳戶和儲存體同步服務的公用端點的存取。 藉由確保只接受來自已核准位置的網路封包,限制對公用端點的存取可提供額外的安全性。
限制對儲存體帳戶公用端點的存取
公用端點的存取限制是使用儲存體帳戶防火牆設定來完成。 一般而言,大部分的儲存體帳戶防火牆原則都會將網路存取限制在一或多個虛擬網路內。 有兩種方法可以將對於儲存體帳戶的存取限制在虛擬網路內:
-
建立儲存體帳戶的一或多個私人端點 並停用公用端點的存取權。 此動作可確保只有來自所需虛擬網路內的流量,才能存取儲存體帳戶中的 Azure 檔案共用。
- 將公用端點限制在一或多個虛擬網路內。 其運作方式是使用稱為「服務端點」的虛擬網路功能。 當您透過服務端點限制記憶體帳戶的流量時,您仍會透過公用IP位址存取記憶體帳戶。
注意
您必須在儲存體帳戶上選取 [允許受信任服務清單上的 Azure 服務存取此儲存體帳戶] 例外狀況,以允許信任的第一方 Microsoft 服務 (例如 Azure 檔案同步) 來存取儲存體帳戶。 若要深入瞭解,請參閱 [授與受信任 Azure 服務的存取權]。
重要
Azure 檔案同步在網路安全邊界(NSP)方面有已知的限制。
儲存同步服務無法放置在邊界內,且不支援完整的邊界整合。
要將儲存同步服務連接到受 NSP 保護的儲存帳號:
- 將儲存同步服務設定為使用 受管理身份。
- 建立 NSP 傳入設定檔規則,將裝載 Storage Sync Service 的訂用帳戶加入允許清單。
儲存同步服務必須保持在邊界外,同步才能正常運作。
授與受信任 Azure 服務的存取權,並停用對儲存體帳戶公用端點的存取權
當公用端點的存取權停用時,仍然可以透過其私人端點來存取儲存體帳戶。 否則,對儲存體帳戶公共端點的有效要求將遭到拒絕。
瀏覽至您想要限制所有對公共端點存取的儲存體帳戶。 在儲存體帳戶的目錄中,選取 [網路]。
在頁面頂端,選取從選取的虛擬網路和 IP 位址啟用選項按鈕。 這會取消隱藏多項用來控制公共端點限制的設定。 請選取 [允許受信任服務清單上的 Azure 服務存取此儲存體帳戶],允許受信任的第一方 Microsoft 服務 (例如 Azure 檔案同步) 存取儲存體帳戶。

下列 PowerShell 命令會拒絕所有傳送至儲存體帳戶公用端點的流量。 請注意,此命令會將 -Bypass 參數設定為 AzureServices。 這會允許受信任的第一方服務 (例如 Azure 檔案同步) 透過公用端點存取儲存體帳戶。
# This assumes $storageAccount is still defined from the beginning of this of this guide.
$storageAccount | Update-AzStorageAccountNetworkRuleSet `
-DefaultAction Deny `
-Bypass AzureServices `
-WarningAction SilentlyContinue `
-ErrorAction Stop | `
Out-Null
下列 CLI 命令會拒絕所有傳送至儲存體帳戶公用端點的流量。 請注意,此命令會將 -bypass 參數設定為 AzureServices。 這會允許受信任的第一方服務 (例如 Azure 檔案同步) 透過公用端點存取儲存體帳戶。
# This assumes $storageAccountResourceGroupName and $storageAccountName
# are still defined from the beginning of this guide.
az storage account update \
--resource-group $storageAccountResourceGroupName \
--name $storageAccountName \
--bypass "AzureServices" \
--default-action "Deny" \
--output none
將存取權授與受信任的 Azure 服務,並將儲存體帳戶公用端點的存取權限制為特定虛擬網路
當您將記憶體帳戶限制為特定虛擬網路時,您會允許來自指定虛擬網路內的公用端點要求。 其運作方式是使用稱為「服務端點」的虛擬網路功能。 可以使用私人端點,也可以不使用。
瀏覽至您想要將其公用端點限制為特定虛擬網路的儲存體帳戶。 在儲存體帳戶的目錄中,選取 [網路]。
在頁面頂端,選取從選取的虛擬網路和 IP 位址啟用選項按鈕。 這會取消隱藏多項用來控制公共端點限制的設定。 選取 [+ 新增現有的虛擬網路],選取應允許透過公用端點存取儲存體帳戶的特定虛擬網路。 選取虛擬網路和該虛擬網路的子網路,然後選取 [啟用]。
請選取 [允許受信任服務清單上的 Azure 服務存取此儲存體帳戶],允許受信任的第一方 Microsoft 服務 (例如 Azure 檔案同步) 存取儲存體帳戶。

若要使用服務端點來將儲存體帳戶的公用端點存取限制為特定虛擬網路,我們必須先收集儲存體帳戶和虛擬網路的相關資訊。 填入 <storage-account-resource-group>、<storage-account-name>、<vnet-resource-group-name>、<vnet-name> 和 <subnet-name> 以收集這些資訊。
$storageAccountResourceGroupName = "<storage-account-resource-group>"
$storageAccountName = "<storage-account-name>"
$restrictToVirtualNetworkResourceGroupName = "<vnet-resource-group-name>"
$restrictToVirtualNetworkName = "<vnet-name>"
$subnetName = "<subnet-name>"
$storageAccount = Get-AzStorageAccount `
-ResourceGroupName $storageAccountResourceGroupName `
-Name $storageAccountName `
-ErrorAction Stop
$virtualNetwork = Get-AzVirtualNetwork `
-ResourceGroupName $restrictToVirtualNetworkResourceGroupName `
-Name $restrictToVirtualNetworkName `
-ErrorAction Stop
$subnet = $virtualNetwork | `
Select-Object -ExpandProperty Subnets | `
Where-Object { $_.Name -eq $subnetName }
if ($null -eq $subnet) {
Write-Error `
-Message "Subnet $subnetName not found in virtual network $restrictToVirtualNetworkName." `
-ErrorAction Stop
}
為了使 Azure 網路架構允許虛擬網路的流量進入儲存帳戶公用端點,虛擬網路的子網路必須將 Microsoft.Storage 服務端點公開。 下列 PowerShell 命令會將 Microsoft.Storage 服務端點新增至子網路 (如果尚未新增)。
$serviceEndpoints = $subnet | `
Select-Object -ExpandProperty ServiceEndpoints | `
Select-Object -ExpandProperty Service
if ($serviceEndpoints -notcontains "Microsoft.Storage") {
if ($null -eq $serviceEndpoints) {
$serviceEndpoints = @("Microsoft.Storage")
} elseif ($serviceEndpoints -is [string]) {
$serviceEndpoints = @($serviceEndpoints, "Microsoft.Storage")
} else {
$serviceEndpoints += "Microsoft.Storage"
}
$virtualNetwork = $virtualNetwork | Set-AzVirtualNetworkSubnetConfig `
-Name $subnetName `
-AddressPrefix $subnet.AddressPrefix `
-ServiceEndpoint $serviceEndpoints `
-WarningAction SilentlyContinue `
-ErrorAction Stop | `
Set-AzVirtualNetwork `
-ErrorAction Stop
}
限制儲存體帳戶流量的最後一個步驟是建立網路規則,並將其新增至儲存體帳戶的網路規則集。
$networkRule = $storageAccount | Add-AzStorageAccountNetworkRule `
-VirtualNetworkResourceId $subnet.Id `
-ErrorAction Stop
$storageAccount | Update-AzStorageAccountNetworkRuleSet `
-DefaultAction Deny `
-Bypass AzureServices `
-VirtualNetworkRule $networkRule `
-WarningAction SilentlyContinue `
-ErrorAction Stop | `
Out-Null
若要使用服務端點來將儲存體帳戶的公用端點存取限制為特定虛擬網路,我們必須先收集儲存體帳戶和虛擬網路的相關資訊。 填入 <storage-account-resource-group>、<storage-account-name>、<vnet-resource-group-name>、<vnet-name> 和 <subnet-name> 以收集這些資訊。
storageAccountResourceGroupName="<storage-account-resource-group>"
storageAccountName="<storage-account-name>"
restrictToVirtualNetworkResourceGroupName="<vnet-resource-group-name>"
restrictToVirtualNetworkName="<vnet-name>"
subnetName="<subnet-name>"
storageAccount=$(az storage account show \
--resource-group $storageAccountResourceGroupName \
--name $storageAccountName \
--query "id" | \
tr -d '"')
virtualNetwork=$(az network vnet show \
--resource-group $restrictToVirtualNetworkResourceGroupName \
--name $restrictToVirtualNetworkName \
--query "id" | \
tr -d '"')
subnet=$(az network vnet subnet show \
--resource-group $restrictToVirtualNetworkResourceGroupName \
--vnet-name $restrictToVirtualNetworkName \
--name $subnetName \
--query "id" | \
tr -d '"')
為了使 Azure 網路的網狀架構能夠允許來自虛擬網路的流量到達儲存體帳戶的公用端點,必須在虛擬網路的子網路中啟用 Microsoft.Storage 服務端點。 下列 CLI 命令會將 Microsoft.Storage 服務端點新增至子網路 (如果尚未新增)。
serviceEndpoints=$(az network vnet subnet show \
--resource-group $restrictToVirtualNetworkResourceGroupName \
--vnet-name $restrictToVirtualNetworkName \
--name $subnetName \
--query "serviceEndpoints[].service" \
--output tsv)
foundStorageServiceEndpoint=false
for serviceEndpoint in $serviceEndpoints
do
if [ $serviceEndpoint = "Microsoft.Storage" ]
then
foundStorageServiceEndpoint=true
fi
done
if [ $foundStorageServiceEndpoint = false ]
then
serviceEndpointList=""
for serviceEndpoint in $serviceEndpoints
do
serviceEndpointList+=$serviceEndpoint
serviceEndpointList+=" "
done
serviceEndpointList+="Microsoft.Storage"
az network vnet subnet update \
--ids $subnet \
--service-endpoints $serviceEndpointList \
--output none
fi
限制儲存體帳戶流量的最後一個步驟是建立網路規則,並將其新增至儲存體帳戶的網路規則集。
az storage account network-rule add \
--resource-group $storageAccountResourceGroupName \
--account-name $storageAccountName \
--subnet $subnet \
--output none
az storage account update \
--resource-group $storageAccountResourceGroupName \
--name $storageAccountName \
--bypass "AzureServices" \
--default-action "Deny" \
--output none
停用儲存體同步服務公用端點的存取權
Azure 檔案同步可讓您僅透過私人端點來限制對特定虛擬網路的存取權;Azure 檔案同步不支援服務端點,以限制對特定虛擬網路的公用端點的存取權。 這表示儲存體同步服務的公用端點的兩個狀態分別為 [已啟用] 和 [已停用]。
重要
您必須先建立私人端點,才能停用公用端點的存取權。 如果公用端點已停用且未設定私人端點,則同步無法運作。
若要停用對儲存體同步服務公用端點的存取權,請遵循下列步驟:
- 登入 Azure 入口網站。
- 瀏覽至儲存體同步服務,然後從左側導覽列中選取 [設定]> [網路]。
- 在 [允許存取來源] 下,選取 [僅限私人端點]。
- 從 [私人端點連線] 清單中選取私人端點。
若要停用對儲存體同步服務的公用端點的存取權,請將儲存體同步服務上的 incomingTrafficPolicy 屬性設定為 AllowVirtualNetworksOnly。 如果您想要啟用儲存體同步服務的公用端點的存取權,請改為將 incomingTrafficPolicy 設定為 AllowAllTraffic。 請記得將 <storage-sync-service-resource-group> 和 <storage-sync-service> 取代為您自己的值。
$storageSyncServiceResourceGroupName = "<storage-sync-service-resource-group>"
$storageSyncServiceName = "<storage-sync-service>"
Set-AzStorageSyncService `
-ResourceGroupName $storageSyncServiceResourceGroupName `
-Name $storageSyncServiceName `
-IncomingTrafficPolicy AllowVirtualNetworksOnly
Azure CLI 不支援在記憶體同步服務上設定 incomingTrafficPolicy 屬性。 請選取 [Azure PowerShell] 索引標籤,取得如何停用儲存體同步服務公用端點的相關指示。
Azure 原則
Azure 原則可協助您強制執行組織標準,並針對這些標準大規模評估合規性。 Azure 檔案儲存體和 Azure 檔案同步會公開幾個實用的稽核與補救網路原則,以協助您監視和自動化部署。
如果您的儲存體帳戶或儲存體同步服務偏離了定義的行為,策略將會稽核您的環境並發出警示。 例如,當您的原則設定為停用公共端點時,卻已啟用公共端點。 修改/部署原則會採取進一步的步驟,並主動修改資源(例如記憶體同步服務)或部署資源(例如私人端點)以配合原則。
下列預先定義的原則適用於 Azure 檔案儲存體和 Azure 檔案同步:
| 動作 |
服務 |
條件 |
原則名稱 |
| 審計 |
Azure 檔案儲存體 |
儲存體帳戶的公用端點已啟用。 如需詳細資訊,請參閱授與受信任 Azure 服務的存取權,並停用對儲存體帳戶公用端點的存取權。 |
儲存體帳戶應限制網路存取 |
| 稽核 |
Azure 檔案同步 |
儲存體同步服務的公用端點已啟用。 如需詳細資訊,請參閱停用對儲存體同步服務公用端點的存取。 |
應為 Azure 檔案同步停用公用網路存取 |
| 稽核 |
Azure 檔案儲存體 |
儲存體帳戶需要至少一個私人端點。 如需詳細資訊,請參閱建立儲存體帳戶私人端點。 |
儲存體帳戶應使用私人連結連線 |
| 審計 |
Azure 檔案同步 |
儲存體同步服務需要至少一個私人端點。 如需詳細資訊,請參閱建立儲存體同步服務私人端點。 |
Azure 檔案同步應使用私人連結 |
| 修改 |
Azure 檔案同步 |
停用儲存體同步服務的公用端點。 |
修改 - 設定 Azure 檔案同步以停用公用網路存取 |
| 部署 |
Azure 檔案同步 |
部署儲存體同步服務的私人端點。 |
使用私人端點設定 Azure 檔案同步 |
| 部署 |
Azure 檔案同步 |
將 A 記錄部署至 privatelink.afs.azure.net DNS 區域。 |
設定 Azure 檔案同步以使用私人 DNS 區域 |
設定私人端點部署原則
若要設定私人端點部署原則,請移至 Azure 入口網站,並搜尋 原則。 Azure 原則中心應該會是最上方的結果。 在原則中心的目錄中,瀏覽至撰寫>定義。 產生的 [定義] 窗格包含所有 Azure 服務中的預先定義原則。 若要尋找特定的原則,請選取 [類別] 篩選條件中的 [儲存體] 類別,或搜尋設定具有私人端點的 Azure 檔案同步。 選取 [...],然後選取 [指派] 以從定義建立新的原則。
指派原則精靈的 [基本] 索引標籤可讓您設定範圍、資源或資源群組排除清單,並為您的原則提供便於辨識的名稱,以協助您加以區別。 您不需要修改這些政策,政策就能運作,但如果您想要進行修改,也可以這麼做。 選取 下一步 以進入 參數 頁面。
在參數窗格上,選取 privateEndpointSubnetId 下拉式清單旁的 ...,以選取應部署 Storage Sync Service 資源私人端點的虛擬網路和子網路。 產生的精靈可能需要幾秒鐘才能在您的訂用帳戶中載入可用的虛擬網路。 為您的環境選取適當的虛擬網路/子網路,然後按一下 [選取]。 選取下一步以前往補救窗格。
若要在識別到沒有私人端點的 Storage Sync Service 時部署私人端點,您必須在補救頁面上選取建立補救工作。 最後,選取 檢閱 + 建立 以檢閱政策指派,然後選取 建立 來建立指派。
產生的政策指派會定期執行,建立後可能不會立即執行。
另請參閱
![建立私人端點區段 [基本] 區段的螢幕快照](media/storage-sync-files-networking-endpoints/create-storage-sync-private-endpoint-1.png)