本文說明如何透過調整特定適用於身分識別的 Microsoft Defender 警示的門檻來設定誤報數量。
部分身份辯護警示依賴 學習期 來建立模式輪廓,並區分合法與可疑活動。 每個警示在偵測邏輯中也包含特定條件,幫助區分合法與可疑活動,例如警示閾值及熱門活動的過濾。
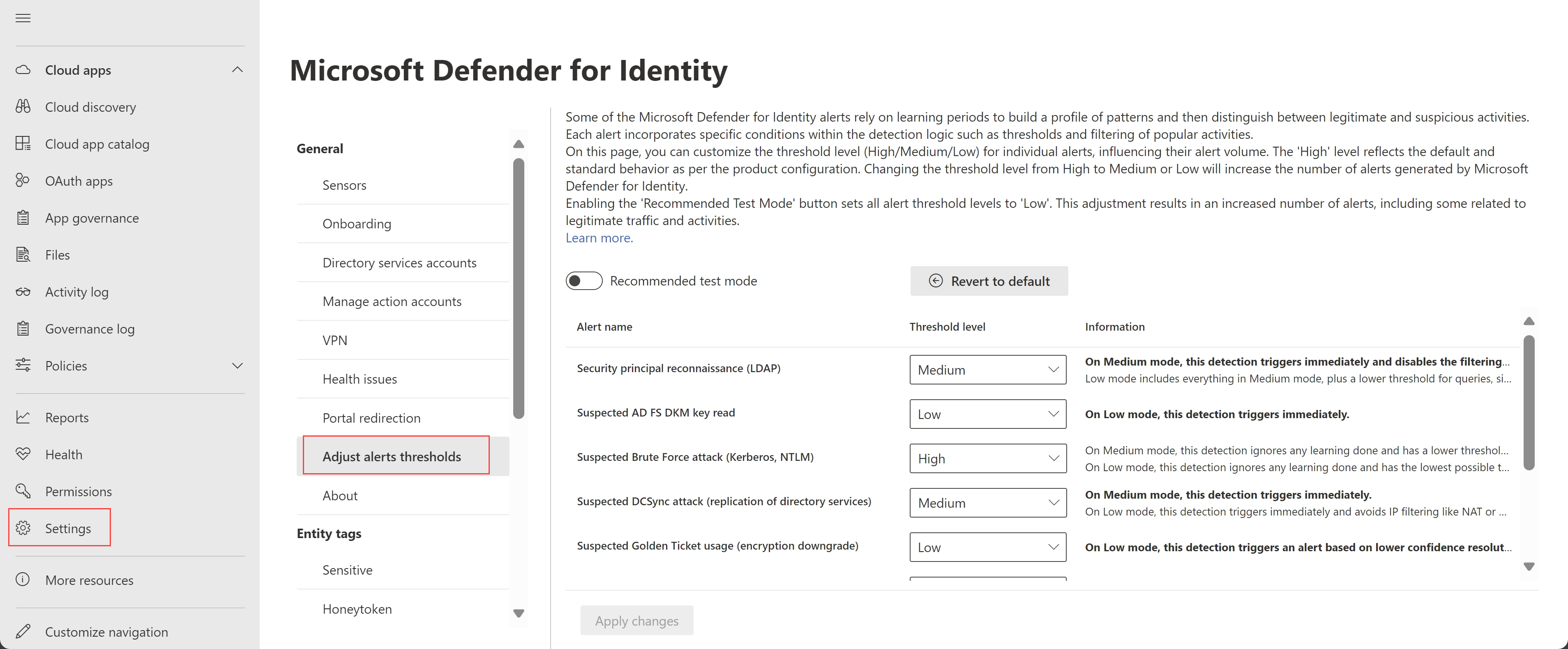
使用 「調整警報閾值」 頁面,自訂特定警報的閾值等級,以影響警報音量。 例如,如果你正在進行全面測試,可能會想降低警示門檻,以觸發盡可能多的警示。
如果選擇「 推薦測試模式 」選項,或將閾值設定為 中 等或 低,無論警示學習期是否已結束,警報都會立即觸發。
注意事項
調整警報閾值頁面之前稱為「進階設定」。
必要條件
要在 Microsoft Defender 全面偵測回應 查看 Adjusts 警示閾值頁面,至少需要以安全檢視器身份存取。
要在 「調整警報閾值 」頁面進行變更,至少需要以 安全管理員身份取得存取權限。
定義警示閾值
我們建議在仔細考慮後,才將警報閾值從預設 (高) 更改。
例如,如果您使用 NAT 或 VPN,我們建議您仔細考慮任何相關偵測變更,包括 疑似 DCSync 攻擊 (目錄服務複製) 及 疑似身份盜用 偵測。
為了定義你的警示閾值:
在 Microsoft Defender 全面偵測回應中,請點到設定>身份>調整警示閾值。
找到你想調整警報閾值的警示,並選擇你想套用的門檻等級。
- 高 為預設值,並套用標準閾值以減少誤判率。
- 中 等與 低 門檻會增加 Defender for Identity 產生的警示數量。
當您選擇 中 等或 低時, 資訊 欄會以粗體顯示細節,幫助您了解變更如何影響警示行為。
選擇 「套用變更 」以儲存變更。
選擇 還原為預設 ,然後套 用變更 ,將所有警報重置為預設閾值 (高) 。 回復預設是不可逆的,且對閾值等級所做的任何更改都會消失。
切換到推薦測試模式
推薦測試模式選項旨在幫助您了解所有 Defender for Identity 的警示,包括與合法流量及活動相關的,讓您能有效率地全面評估 Defender for Identity。
如果你最近部署了 Defender for Identity 並想測試它,請選擇 「推薦測試模式 」選項,將所有警示閾值切換為 低 ,並增加觸發的警示數量。
當選擇 「推薦測試模式 」選項時,閾值等級為唯讀。
注意事項
測試模式的時間限制為最長60天。 開啟推薦測試模式時,必須指定結束時間。 只要測試模式開啟,所選結束時間會顯示在切換開關旁。
測試結束後,關閉推薦測試模式選項,回到之前的設定。 選擇 「套用變更 」以儲存變更。
支援的閾值配置偵測
下表說明支持調整閾值水平的偵測類型,包括 中 度與 低 閾值的影響。
標示為 N/A 的格子表示該閾值等級不支援偵測。
| 偵測 | 中 | 低 |
|---|---|---|
| LDAP (安全主體偵察) | 當此偵測設定為 中等時,會立即觸發警報,無需等待學習期,並且會關閉環境中熱門查詢的過濾功能。 | 當設定為 低時,所有 中等閾 值的支援都適用,查詢、單一範圍列舉等則有較低的門檻。 |
| 敏感群體的可疑新增 | 不適用 | 當偵測設為 低時,會避開滑動視窗,並忽略先前的學習結果。 |
| 疑似AD FS DKM鑰匙讀取 | 不適用 | 當偵測設為 低時,會立即觸發,無需等待學習期。 |
| 疑似暴力攻擊 (Kerberos,NTLM) | 當設定為 Medium 時,這個偵測會忽略任何已知的學習,且密碼失敗的門檻較低。 | 當偵測為 低時,會忽略任何已知的學習,並設定密碼失敗的最低門檻。 |
| 疑似 DCSync 攻擊 (目錄服務複製) | 當設定為 中等時,此偵測會立即觸發,無需等待學習期。 | 當設定為 低時,這個偵測會立即觸發,無需等待學習期,並避免像 NAT 或 VPN 這樣的 IP 過濾。 |
| 疑似金票使用 (偽造授權資料) | 不適用 | 當偵測設為 低時,會立即觸發,無需等待學習期。 |
| 疑似金票使用 (加密降級) | 不適用 | 當偵測設定為 低時,會根據裝置的置信度解析度較低觸發警示。 |
| 疑似身份盜用 (轉票) | 不適用 | 當設定為 低時,這個偵測會立即觸發,無需等待學習期,並避免像 NAT 或 VPN 這樣的 IP 過濾。 |
| SAMR) (使用者與群組成員偵察 | 當設定為 中等時,此偵測會立即觸發,無需等待學習期。 | 當偵測設為 低時,會立即觸發,並包含較低的警示門檻。 |
欲了解更多資訊,請參閱 適用於身分識別的 Microsoft Defender 中的安全警示。
下一步
欲了解更多資訊,請參閱 Microsoft Defender 全面偵測回應中的 Defender for Identity 安全警示。