I solved this issue by changing the RDP connection to the local IP address instead of the public IP/DNS address.
I connect to my VPN successfully. I'm having problems RDPing into my VM after allowing a firewall rule IP address issued by the VPN
I've setup an Azure P2S VPN successfully and my client is able to connect to a local static IP address, but I'm having problems RDPing into my VM after allowing a firewall rule port 3389 for specific IP addresses
3 answers
Sort by: Newest
-
-
ChaitanyaNaykodi-MSFT 23,031 Reputation points Microsoft Employee
2022-09-28T16:02:28.987+00:00 Hello @azureuser01
Welcome to the Microsoft Q&A forum.
If I have understood the question correctly you have successfully established a VPN connection but are unable to do RDP (port 3389) into your VM.
In such scenarios most likely a NSG present in resource group is blocking this connectivity. You can perform an IP flow verify check and see any NSG is blocking this connectivity. You can follow this documentation here.
Regarding your question above.
When I turn the firewall ON on either machine, I lose the ping connection. Do you have any clue what firewall rules I need to add to keep the ping connection there?
On Windows OS, you can run the command
netsh advfirewall firewall add rule name="ICMP Allow incoming V4 echo request" protocol="icmpv4:8,any" dir=in action=allowto enable V4 ICMP connectivity in the OS firewall.Hope this helps! Please let me know if you have any additional questions. Thank you!
-
 Philippe Levesque 5,691 Reputation points MVP
Philippe Levesque 5,691 Reputation points MVP2022-09-27T18:09:29.543+00:00 Hi, I assume your rule is not triggered if the VPN tunnel is OK.
In your VM you can enable log file to make sure your rule is OK. There; and after go in your RDP's rule and select to log that traffic.
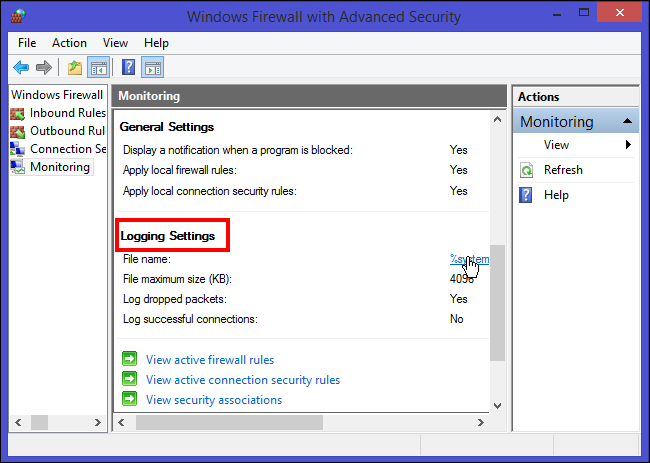
After the log is activated, check inside to make sure the rule is OK, as RDP rule can be made in TCP, UDP, etc..
If you try to connect and nothing got logged make sure the rule is ok inside the Azure portal then, as the traffic is not seen on the VM.