@Oleg Tserkovnyuk
I'm glad that you were able to resolve your issue and thank you for posting your solution so that others experiencing the same thing can easily reference this! Since the Microsoft Q&A community has a policy that "The question author cannot accept their own answer. They can only accept answers by others", I'll repost your solution in case you'd like to "Accept" the answer.
Issue:
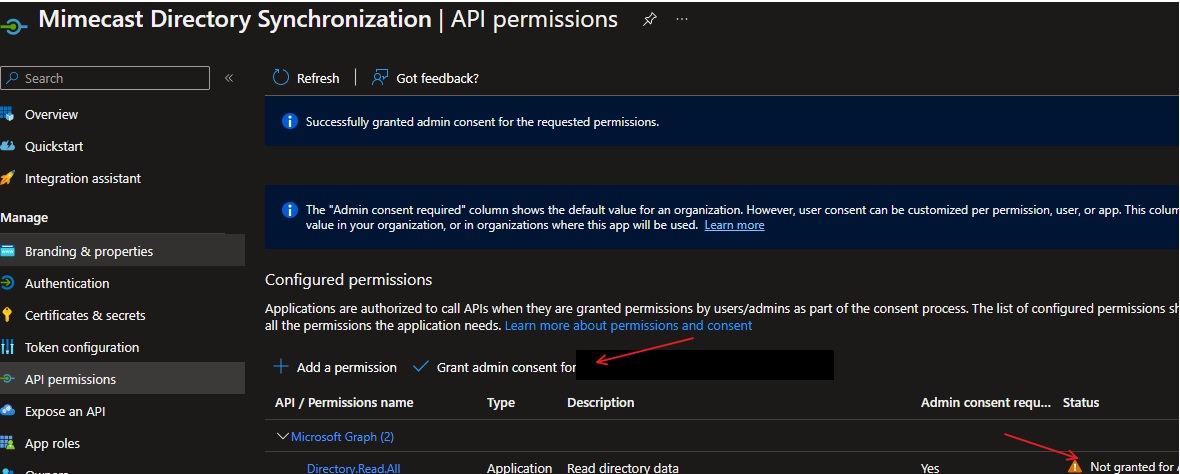
- Using PowerShell and the Graph API you created a new app registration.
- When Granting Admin Consent for API Permissions for your tenant, this required going through the Azure Portal UI.
- You're looking for a way to automate granting admin consent using PowerShell and haven't found a way to do this for API permissions. Solution:
Using the below PowerShell Script, you were able to resolve your issue. $AppServicePrincipalId = (Get-AzureADServicePrincipal -all $true | Where-Object { $.DisplayName -eq $AppDisplayName }).ObjectId
$MSGraphServicePrincipalObjectId = (Get-AzureADServicePrincipal -all $true | Where-Object { $.DisplayName -eq 'Microsoft Graph' }).ObjectId
# Microsoft Graph permissions IDs https://learn.microsoft.com/en-us/graph/permissions-reference
$AppRolesId = ((Invoke-MgGraphRequest -Uri "/v1.0/servicePrincipals?$filter=displayName eq 'Microsoft Graph'&$select=id,displayName,appId,appRoles" -Method GET).value.appRoles)
$UserReadAll = ($AppRolesId | Where-Object { $_.value -eq 'User.Read.All' }).id$param = @{ "PrincipalId" = "$AppServicePrincipalId" "ResourceId" = "$MSGraphServicePrincipalObjectId" "AppRoleId" = "$UserReadAll" } New-MgServicePrincipalAppRoleAssignment -ServicePrincipalId "$MSGraphServicePrincipalObjectId" -BodyParameter $param
If you have any other questions, please let me know.
Thank you again for your time and patience throughout this issue.
Please remember to "Accept Answer" if any answer/reply helped, so that others in the community facing similar issues can easily find the solution.