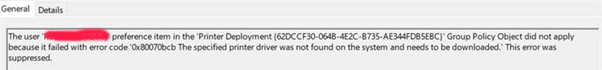
We experience exactly the same behaviour. I've spent one full day and I think this is a bug in how Microsoft fixed PrintNightmare vulnerability and printer deployment via Deployed Printer Connection GPO.
I'm dumping all test information here in case someone needs it. The tests where performed on Windows Server 2019 print server and Windows 10 clients with latest 2021-12 CU installed, though I don't think OS version matters that much.
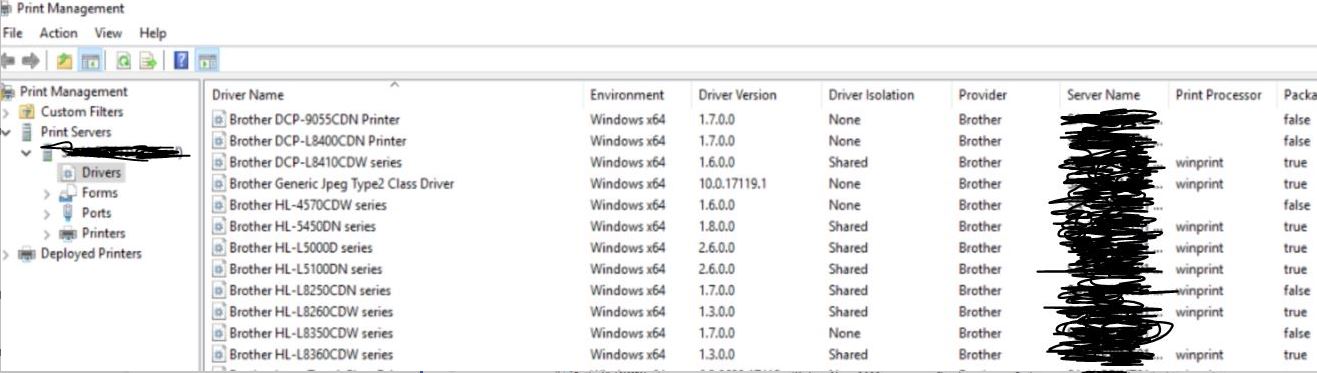
First thing you need to understand is that the behaviour and how GPO settings described in this MS article https://support.microsoft.com/en-us/topic/kb5005652-manage-new-point-and-print-default-driver-installation-behavior-cve-2021-34481-873642bf-2634-49c5-a23b-6d8e9a302872 work depends on the type of the driver.
If you are using only V4 drivers there are three possible solutions (choose only one of them):
Solution 1
a) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Only use Package Point and Print to Enabled.
b) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Package Point and Print - Approved Servers to Enabled and specify FQDN of your print server.
c) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Limit print driver installation to Administrators to Disabled.
This will allow to deploy printers via Deployed Printer Connection GPO targeting User Scope. I didn't find any information if this also enables PrintNightmare vulnerability. Here https://support.microsoft.com/en-us/topic/kb5005010-restricting-installation-of-new-printer-drivers-after-applying-the-july-6-2021-updates-31b91c02-05bc-4ada-a7ea-183b129578a7 Microsoft says that CVE-2021-34527 is only present if Point and Print Restrictions GPO is used and nothing about Package Point and Print. Even if it is, the vulnerability should be limited only to the attack vector coming from the FQDN specified earlier. Also, vulnerability should only be exploitable when attacker uses V3 packaged drivers, and not package-unaware drivers.
Solution 2
Use GPP instead of Deployed Printer Connection GPO to deploy printers. This will allow to deploy V4 printers without any other GPO/registry changes.
Solution 3
Change your Deployed Printer Connection GPO to use Computer Configuration instead of User Configuration and apply it to Computers OU instead of Users OU. This again will allow you to deploy V4 printers without any other GPO/registry changes.
If you are using V3 packaged drivers there is only one solution:
Solution 1
a) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Only use Package Point and Print to Enabled.
b) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Package Point and Print - Approved Servers to Enabled and specify FQDN of your print server.
c) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Limit print driver installation to Administrators to Disabled.
This will allow to deploy printers via Deployed Printer Connection GPO targeting User Scope. Again, it is unclear if this enables PrintNightmare vulnerability, but even if it's so, the vulnerability should be limited only to the attack vector coming from the FQDN specified earlier. Also, vulnerability should only be exploitable when attacker uses V3 packaged drivers, and not package-unaware drivers.
If you are using very old V3 package-unaware drivers the solution is a little bit different:
Solution 1
a) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Package Point and Print - Approved Servers to Enabled and specify FQDN of your print server.
b) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Point and Print Restrictions to Enabled, enable User can only point and print from these servers and specify FQDN of your print server. Also, don't forget set Security Prompts to your liking.
c) Set Computer Configuration -> Policies -> Administrative Templates -> Printers -> Limit print driver installation to Administrators to Disabled.
This will allow to deploy printers via Deployed Printer Connection GPO targeting User Scope, but if you choose to disable Security Prompts in step b) it also enables PrintNightmare vulnerability. Vulnerability can be exploited when using both V3 packaged and package-unaware drivers. It is limited to the attack vector coming from the FQDN specified earlier though. If Security Prompts are enabled vulnerability cannot be exploited.
Since I'm using only V4 drivers and I think it's a bug, I went with first Solution 1 and will wait until MS hopefully comes up with another fix.
Hope this helps.
P.S. I encourage everyone to have Feedback Hub ticket filled regarding this issue. Maybe our voices will be heard at some point.