Hi @Anonymous ,
Glad to know that you have self-resolved the question and thanks for sharing it. This would be of great help for other community users who might be looking for similar information.
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Permission error when running Add-AzureADGroupMember in an Azure PowerShell RunBook:
Error occurred while executing AddGroupMember
Code: Authorization_RequestDenied
Message: Insufficient privileges to complete the operation.
Running Set-AzureADUser does not produce an error, but also doesn't alter the JobTitle attribute.
Editing Exchange related attributes like default email address and additional email addresses are successful.
This Azure Automation account uses a Certificate and an Azure RunAsAccount. The RunAsAccount has the Role "Contributor" assigned.
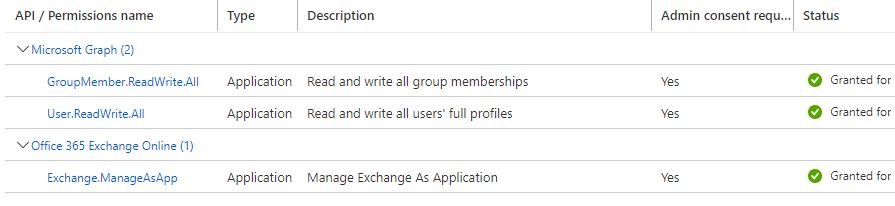
Permission granted via App Registration API are seen in this image:
What API permissions are needed to permit Add-AzureADGroupMember and set Set-AzureADUser to be successful?

Hi @Anonymous ,
Glad to know that you have self-resolved the question and thanks for sharing it. This would be of great help for other community users who might be looking for similar information.
Created custom Azure Roles using the built in Azure Role templates:
# enable Groups Administrator from template
Enable-AzureADDirectoryRole -RoleTemplateId "fdd7a751-b60b-444a-984c-02652fe8fa1c"
Add-AzureADDirectoryRoleMember -ObjectId (Get-AzureADDirectoryRole | where-object {$_.DisplayName -eq "Groups Administrator"}).Objectid -RefObjectId $servicePrincipalObjectId
# enable User Administrator from template
Enable-AzureADDirectoryRole -RoleTemplateId "fe930be7-5e62-47db-91af-98c3a49a38b1"
Add-AzureADDirectoryRoleMember -ObjectId (Get-AzureADDirectoryRole | where-object {$_.DisplayName -eq "User Administrator"}).Objectid -RefObjectId $servicePrincipalObjectId
Additionally we removed the API permissions "GroupMember.ReadWrite.All" and "User.ReadWrite.All" (seen in the image above) and the RunBook can still edit Azure users and Azure groups.
This resolved the problem and with the minimal permissions we need.
Tested assignment of Global Administrator Role to the RunAsAccount via
Add-AzureADDirectoryRoleMember -ObjectId (Get-AzureADDirectoryRole | where-object {$_.DisplayName -eq "Global Administrator"}).Objectid -RefObjectId $servicePrincipalObjectId
and it permits the RunBook to make changes to the Azure user and Azure group.
This is unacceptable as a solution because of granting too much permission.