Privileged Identity Management supports Azure Resource Manager (ARM) API commands to manage Azure resource roles, as documented in the PIM ARM API reference. For the permissions required to use the PIM API, see Understand the Privileged Identity Management APIs.
To activate an eligible Azure role assignment and gain activated access, use the Role Assignment Schedule Requests - Create REST API to create a new request and specify the security principal, role definition, requestType = SelfActivate and scope. To call this API, you must have an eligible role assignment on the scope.
Use a GUID tool to generate a unique identifier that will be used for the role assignment identifier. The identifier has the format: 00000000-0000-0000-0000-000000000000.
Replace {roleAssignmentScheduleRequestName} in the below PUT request with the GUID identifier of the role assignment.
For more details on managing eligible roles for Azure resources, see this PIM ARM API tutorial.
The following is a sample HTTP request to activate an eligible assignment for an Azure role.
Request
PUT https://management.azure.com/providers/Microsoft.Subscription/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Authorization/roleAssignmentScheduleRequests/{roleAssignmentScheduleRequestName}?api-version=2020-10-01
Request body
{
"properties": {
"principalId": "aaaaaaaa-bbbb-cccc-1111-222222222222",
"roleDefinitionId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Authorization/roleDefinitions/c8d4ff99-41c3-41a8-9f60-21dfdad59608",
"requestType": "SelfActivate",
"linkedRoleEligibilityScheduleId": "b1477448-2cc6-4ceb-93b4-54a202a89413",
"scheduleInfo": {
"startDateTime": "2020-09-09T21:35:27.91Z",
"expiration": {
"type": "AfterDuration",
"endDateTime": null,
"duration": "PT8H"
}
},
"condition": "@Resource[Microsoft.Storage/storageAccounts/blobServices/containers:ContainerName] StringEqualsIgnoreCase 'foo_storage_container'",
"conditionVersion": "1.0"
}
}
Response
Status code: 201
{
"properties": {
"targetRoleAssignmentScheduleId": "c9e264ff-3133-4776-a81a-ebc7c33c8ec6",
"targetRoleAssignmentScheduleInstanceId": null,
"scope": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e",
"roleDefinitionId": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Authorization/roleDefinitions/c8d4ff99-41c3-41a8-9f60-21dfdad59608",
"principalId": "aaaaaaaa-bbbb-cccc-1111-222222222222",
"principalType": "User",
"requestType": "SelfActivate",
"status": "Provisioned",
"approvalId": null,
"scheduleInfo": {
"startDateTime": "2020-09-09T21:35:27.91Z",
"expiration": {
"type": "AfterDuration",
"endDateTime": null,
"duration": "PT8H"
}
},
"ticketInfo": {
"ticketNumber": null,
"ticketSystem": null
},
"justification": null,
"requestorId": "a3bb8764-cb92-4276-9d2a-ca1e895e55ea",
"createdOn": "2020-09-09T21:35:27.91Z",
"condition": "@Resource[Microsoft.Storage/storageAccounts/blobServices/containers:ContainerName] StringEqualsIgnoreCase 'foo_storage_container'",
"conditionVersion": "1.0",
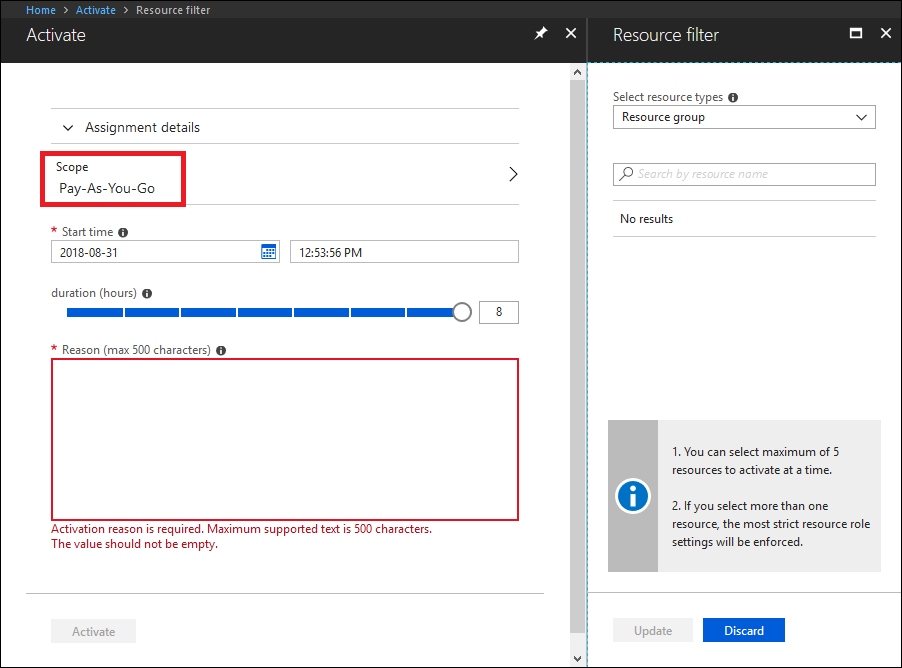
"expandedProperties": {
"scope": {
"id": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e",
"displayName": "Pay-As-You-Go",
"type": "subscription"
},
"roleDefinition": {
"id": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Authorization/roleDefinitions/c8d4ff99-41c3-41a8-9f60-21dfdad59608",
"displayName": "Contributor",
"type": "BuiltInRole"
},
"principal": {
"id": "a3bb8764-cb92-4276-9d2a-ca1e895e55ea",
"displayName": "User Account",
"email": "user@my-tenant.com",
"type": "User"
}
}
},
"name": "fea7a502-9a96-4806-a26f-eee560e52045",
"id": "/subscriptions/aaaa0a0a-bb1b-cc2c-dd3d-eeeeee4e4e4e/providers/Microsoft.Authorization/RoleAssignmentScheduleRequests/fea7a502-9a96-4806-a26f-eee560e52045",
"type": "Microsoft.Authorization/RoleAssignmentScheduleRequests"
}