Poznámka:
Přístup k této stránce vyžaduje autorizaci. Můžete se zkusit přihlásit nebo změnit adresáře.
Přístup k této stránce vyžaduje autorizaci. Můžete zkusit změnit adresáře.
Active Directory Federation Services (AD FS) 2019 přidává funkce pro přizpůsobení hlaviček odpovědí zabezpečení HTTP odesílaných službou AD FS. Tyto nástroje pomáhají správcům chránit před běžnými ohroženími zabezpečení a umožňují jim využívat nejnovější vylepšení mechanismů ochrany na základě prohlížeče. Tato funkce pochází z úvodu dvou nových rutin: Get-AdfsResponseHeaders a Set-AdfsResponseHeaders.
Note
Funkce přizpůsobení hlaviček odpovědí zabezpečení HTTP (s výjimkou hlaviček CORS) pomocí rutin: Get-AdfsResponseHeaders a Set-AdfsResponseHeaders byla backportována do služby AD FS 2016. Do služby AD FS 2016 můžete přidat funkce instalací KB4493473 a KB4507459.
Tento článek popisuje běžně používané hlavičky odpovědí zabezpečení, které ukazují, jak přizpůsobit hlavičky odeslané službou AD FS 2019.
Note
Článek předpokládá, že jste nainstalovali službu AD FS 2019.
Scenarios
Následující scénáře ukazují, že správci potřebují přizpůsobit hlavičky zabezpečení.
- Správce povolil http Strict-Transport-Security (HSTS) k ochraně uživatelů, kteří můžou přistupovat k webové aplikaci pomocí HTTP z veřejného přístupového bodu Wi-Fi, který může být hacknut. HSTS vynucuje všechna připojení pomocí šifrování HTTPS. Chtěli by dále posílit zabezpečení povolením HSTS pro subdomény.
- Správce nakonfiguroval hlavičku odpovědi X-Frame-Options tak, aby chránil webové stránky před kliknutím. X-Frame-Options zabraňuje vykreslení jakékoli webové stránky v prvku iFrame. Kvůli novému obchodnímu požadavku na zobrazení dat (v prvku iFrame) z aplikace s jiným původem (doménou) ale musí přizpůsobit hodnotu hlavičky.
- Správce povolil X-XSS-Protection k sanitizaci a blokování stránky, pokud prohlížeč detekuje útoky křížového skriptování. X-XSS-Protection zabraňuje útokům křížového skriptování. Musí ale přizpůsobit záhlaví, aby se stránka mohla načíst po sanitizaci.
- Správce musí povolit sdílení prostředků mezi zdroji (CORS) a musí nastavit zdroj (doménu) ve službě AD FS tak, aby jedna stránková aplikace mohla přistupovat k webovému rozhraní API s jinou doménou.
- Správce povolil hlavičku CSP (Content Security Policy), aby zabránil útokům prostřednictvím skriptování mezi weby a injektáži dat tím, že zakáže všechny požadavky napříč doménou. Vzhledem k novému obchodnímu požadavku ale musí přizpůsobit hlavičku, aby webová stránka mohla načítat obrázky z libovolného původu a omezit média na důvěryhodné poskytovatele.
Hlavičky zabezpečení odpovědi HTTP
Služba AD FS obsahuje hlavičky odpovědí v odchozí odpovědi HTTP odeslané ve webovém prohlížeči. Záhlaví můžete zobrazit pomocí Get-AdfsResponseHeaders rutiny, jak je znázorněno na následujícím snímku obrazovky.
Atribut ResponseHeaders na snímku obrazovky identifikuje hlavičky zabezpečení zahrnuté službou AD FS v každé odpovědi HTTP. Služba AD FS odesílá hlavičky odpovědi pouze v případě, že je vlastnost ResponseHeadersEnabled nastavená na True (výchozí hodnota). Hodnotu lze nastavit na False, aby se zabránilo tomu, že služba AD FS zahrne jakékoli hlavičky zabezpečení v odpovědi HTTP. Toto nastavení se ale nedoporučuje.
ResponseHeadersFalse můžete nastavit pomocí následujícího příkazu:
Set-AdfsResponseHeaders -EnableResponseHeaders $false
StriktníTransport-Security HTTP (HSTS)
HTTP Strict-Transport-Security (HSTS) je mechanismus bezpečnostní politiky webu, který pomáhá zmírnit útoky na downgrade protokolu a krádež cookies pro služby, které mají koncové body HTTP i HTTPS. Umožňuje webovým serverům deklarovat, že webové prohlížeče nebo jiné agenty dodržující požadavky na uživatele by s nimi měly pracovat pouze pomocí protokolu HTTPS a nikdy přes protokol HTTP.
Všechny koncové body služby AD FS pro provoz ověřování webu se otevírají výhradně přes PROTOKOL HTTPS. Díky tomu služba AD FS účinně snižuje hrozby, které poskytuje mechanismus zásad zabezpečení striktního přenosu HTTP. Ve výchozím nastavení není možné snížit na HTTP, protože v HTTP nejsou žádní posluchači. Hlavičku lze přizpůsobit nastavením následujících parametrů:
- max-věk=<doba vypršení>. Doba vypršení platnosti (v sekundách) určuje, jak dlouho má být web přístupný pouze pomocí protokolu HTTPS. Výchozí a doporučená hodnota je 31536000 sekund (jeden rok).
- includeSubDomains. Tento parametr je volitelný. Pokud je zadáno, pravidlo HSTS platí i pro všechny subdomény.
Přizpůsobení HSTS
Ve výchozím nastavení je hlavička povolená a max-age je nastavená na jeden rok. Správci ale můžou upravit max-age (nedoporučuje se snížit maximální věk) nebo povolit HSTS pro subdomény prostřednictvím rutiny Set-AdfsResponseHeaders .
Set-AdfsResponseHeaders -SetHeaderName "Strict-Transport-Security" -SetHeaderValue "max-age=<seconds>; includeSubDomains"
Example:
Set-AdfsResponseHeaders -SetHeaderName "Strict-Transport-Security" -SetHeaderValue "max-age=31536000; includeSubDomains"
Ve výchozím nastavení je hlavička zahrnuta do atributu ResponseHeaders ; Správci ale mohou hlavičku odebrat prostřednictvím rutiny Set-AdfsResponseHeaders .
Set-AdfsResponseHeaders -RemoveHeaders "Strict-Transport-Security"
X-Frame-Options
Služba AD FS ve výchozím nastavení neumožňuje externím aplikacím při interaktivním přihlašování používat elementy iFrame. Tato konfigurace zabraňuje určitému stylu útoků phishing. Neinteraktivní přihlášení lze provést prostřednictvím prvku iFrame díky dříve zavedenému zabezpečení na úrovni relace.
V některých výjimečných případech ale můžete důvěřovat konkrétní aplikaci, která vyžaduje interaktivní přihlašovací stránku služby AD FS podporující prvek iFrame. Hlavička X-Frame-Options se používá k tomuto účelu.
Tato hlavička odpovědi zabezpečení HTTP slouží ke komunikaci s prohlížečem, jestli může vykreslit stránku v <rámci nebo>< prvku iframe>. Záhlaví lze nastavit na jednu z následujících hodnot:
- deny. Stránka v rámci se nezobrazuje. Tato konfigurace je výchozí a doporučené nastavení.
- sameorigin. Stránka se zobrazí pouze v rámci, pokud je původ stejný jako původ webové stránky. Možnost není užitečná, pokud nejsou všichni předkové také ve stejném původu.
-
povolit z <určeného původu>. Stránka se zobrazí jenom v rámci, pokud zdroj (například
https://www.".com) odpovídá konkrétnímu původu v záhlaví. Některé prohlížeče tuto možnost nemusí podporovat.
PřizpůsobeníFrame-Options X
Ve výchozím nastavení je záhlaví nastaveno na odepření; Správci ale můžou hodnotu upravit prostřednictvím rutiny Set-AdfsResponseHeaders .
Set-AdfsResponseHeaders -SetHeaderName "X-Frame-Options" -SetHeaderValue "<deny/sameorigin/allow-from<specified origin>>"
Example:
Set-AdfsResponseHeaders -SetHeaderName "X-Frame-Options" -SetHeaderValue "allow-from https://www.example.com"
Ve výchozím nastavení je hlavička zahrnuta do atributu ResponseHeaders ; Správci ale mohou hlavičku odebrat prostřednictvím rutiny Set-AdfsResponseHeaders .
Set-AdfsResponseHeaders -RemoveHeaders "X-Frame-Options"
X-XSS-Protection
Tato hlavička odpovědi zabezpečení HTTP slouží k zastavení načítání webových stránek, když prohlížeče detekují útoky na skriptování mezi weby (XSS). Tento přístup se označuje jako filtrování XSS. Záhlaví lze nastavit na jednu z následujících hodnot:
- 0 zakáže filtrování XSS. Nedoporučuje se.
- 1 umožňuje filtrování XSS. Pokud se zjistí útok XSS, prohlížeč stránku sanituje.
- 1; mode=block umožňuje filtrování XSS. Pokud se zjistí útok XSS, prohlížeč zabrání vykreslení stránky. Toto nastavení je výchozí a doporučené nastavení.
PřizpůsobeníXSS-Protection X
Ve výchozím nastavení je záhlaví nastaveno na hodnotu 1; mode=block;. Správci ale můžou hodnotu upravit prostřednictvím rutiny Set-AdfsResponseHeaders .
Set-AdfsResponseHeaders -SetHeaderName "X-XSS-Protection" -SetHeaderValue "<0/1/1; mode=block/1; report=<reporting-uri>>"
Example:
Set-AdfsResponseHeaders -SetHeaderName "X-XSS-Protection" -SetHeaderValue "1"
Ve výchozím nastavení je hlavička zahrnuta do atributu ResponseHeaders ; Správci ale můžou hlavičku odebrat prostřednictvím rutiny Set-AdfsResponseHeaders .
Set-AdfsResponseHeaders -RemoveHeaders "X-XSS-Protection"
Hlavičky pro sdílení prostředků mezi doménami (CORS)
Zabezpečení webového prohlížeče brání webové stránce v provádění požadavků mezi zdroji iniciovaných ze skriptů. Můžete ale chtít získat přístup k prostředkům v jiných zdrojích (doménách). Cross-Origin Resource Sharing (CORS) je standard W3C, který umožňuje serveru uvolnit politiku stejný původ. Pomocí CORS může server explicitně povolit některé požadavky mezi zdroji a zároveň odmítnout jiné.
Pokud chcete lépe porozumět požadavku CORS, následující scénář vás provede instancí, ve které jedna stránková aplikace (SPA) potřebuje volat webové rozhraní API s jinou doménou. Dále vezměte v úvahu, že na AD FS 2019 jsou nakonfigurovány SPA i rozhraní API a CORS je povolen. Služba AD FS dokáže identifikovat hlavičky CORS v požadavku HTTP, ověřit hodnoty hlaviček a zahrnout do odpovědi odpovídající hlavičky CORS. Podrobnosti o povolení a konfiguraci CORS ve službě AD FS 2019 najdete v části Přizpůsobení CORS. Následující ukázkový tok vás provede scénářem:
Uživatel přistupuje ke SPA prostřednictvím klientského prohlížeče a je přesměrován na koncový bod ověřování služby AD FS k ověření. Vzhledem k tomu, že SPA je nakonfigurována pro implicitní tok udělení, požadavek po úspěšném ověření vrátí do prohlížeče token Access a ID.
Po ověření uživatele vytvoří front-end JavaScript zahrnutý ve spa žádost o přístup k webovému rozhraní API. Požadavek se přesměruje do služby AD FS s následujícími hlavičkami:
- Možnosti – popisuje možnosti komunikace pro cílový prostředek.
- Origin – zahrnuje původ webového rozhraní API.
- Řízení přístupu –Request-Method – identifikuje metodu HTTP (například DELETE), která se má použít při skutečném požadavku.
- Řízení přístupu –Request-Headers – identifikuje hlavičky HTTP, které se mají použít při skutečném požadavku.
Note
Požadavek CORS se podobá standardnímu požadavku HTTP. Přítomnost hlavičky původu ale signalizuje, že příchozí požadavek souvisí s CORS.
Služba AD FS ověřuje, že zdroj webového rozhraní API zahrnutý v hlavičce je uvedený v důvěryhodných zdrojích nakonfigurovaných ve službě AD FS. Další informace o tom, jak upravit důvěryhodné zdroje, najdete v tématu Přizpůsobení CORS. Služba AD FS pak odpoví následujícími hlavičkami:
- Řízení přístupu –Allow-Origin – hodnota stejná jako v hlavičce Origin.
- Řízení přístupu –Allow-Method – hodnota stejná jako v hlavičce Access-Control-Request-Method.
- Řízení přístupu -Allow-Headers - hodnota stejná jako v záhlaví Access-Control-Request-Headers.
Prohlížeč odešle skutečný požadavek včetně následujících hlaviček:
- Metoda HTTP (například DELETE).
- Origin – zahrnuje původ webového rozhraní API.
- Všechny hlavičky zahrnuté v hlavičce odpovědi Access-Control-Allow-Headers.
Po ověření služba AD FS žádost schválí zahrnutím domény webového rozhraní API (origin) do hlavičky odpovědi řízení přístupuAllow-Origin.
Zahrnutí hlavičky Řízení přístupu –Allow-Origin umožňuje prohlížeči volat požadované rozhraní API.
Přizpůsobení CORS
Ve výchozím nastavení není funkce CORS povolená; Správci ale můžou funkci povolit prostřednictvím rutiny Set-AdfsResponseHeaders .
Set-AdfsResponseHeaders -EnableCORS $true
Po povolení můžou správci vytvořit výčet seznamu důvěryhodných zdrojů pomocí stejné rutiny. Například následující příkaz povolí CORS žádosti z původů https://example1.com a https://example1.com.
Set-AdfsResponseHeaders -CORSTrustedOrigins https://example1.com,https://example2.com
Note
Správci můžou povolit žádosti CORS z jakéhokoli původu tak, že do seznamu důvěryhodných zdrojů zahrne "*", i když se tento přístup nedoporučuje kvůli ohrožením zabezpečení a pokud se rozhodnete, zobrazí se zpráva s upozorněním.
Zásady zabezpečení obsahu (CSP)
Tato hlavička odpovědi zabezpečení HTTP slouží k zabránění cross-site scriptingu, clickjackingu a dalším útokům prostřednictvím injektáže dat tím, že brání prohlížečům neúmyslně spouštět škodlivý obsah. Prohlížeče, které nepodporují zásady zabezpečení obsahu (CSP), ignorují hlavičky odpovědí CSP.
Přizpůsobení CSP
Přizpůsobení hlavičky CSP zahrnuje úpravu zásad zabezpečení, která definuje prostředky, které prohlížeč může načíst pro webovou stránku. Výchozí zásady zabezpečení jsou:
Content-Security-Policy: default-src 'self' 'unsafe-inline' 'unsafe-eval'; img-src 'self' data:;
Direktiva default-src se používá k úpravě direktiv -src bez explicitního výpisu jednotlivých direktiv. Například v následujícím příkladu je zásada 1 stejná jako zásada 2.
Zásady 1
Set-AdfsResponseHeaders -SetHeaderName "Content-Security-Policy" -SetHeaderValue "default-src 'self'"
Zásady 2
Set-AdfsResponseHeaders -SetHeaderName "Content-Security-Policy" -SetHeaderValue "script-src 'self'; img-src 'self'; font-src 'self';
frame-src 'self'; manifest-src 'self'; media-src 'self';"
Pokud je direktiva explicitně uvedena, zadaná hodnota přepíše hodnotu zadanou pro default-src. V následujícím příkladu přebírá img-src hodnotu jako *(což umožňuje načtení obrázků z jakéhokoli zdroje), zatímco jiné direktivy -src přebírají hodnotu jako self (omezení na stejný původ jako webová stránka).
Set-AdfsResponseHeaders -SetHeaderName "Content-Security-Policy" -SetHeaderValue "default-src 'self'; img-src *"
Pro zásady default-src je možné definovat následující zdroje:
- "self" – určení tohoto zdroje omezuje původ obsahu, aby byl načten z původu webové stránky.
- 'unsafe-inline' – zadání tohoto atributu v zásadách umožňuje používat vložený JavaScript a CSS.
- "'unsafe-eval' – určení tohoto zdroje v zásadách umožňuje použití mechanismů převodu textu na JavaScript, jakým je eval."
- „žádný“ – zadáním tohoto zdroje omezíte, aby se obsah načetl z jakéhokoli původu.
- data: – specifikace dat: Identifikátory URI umožňují tvůrcům obsahu vkládat malé soubory přímo do dokumentů. Nedoporučuje se používat.
Note
Služba AD FS používá v procesu ověřování JavaScript, a tak zahrnutím zdrojů 'unsafe-inline' a 'unsafe-eval' do výchozí zásady povoluje JavaScript.
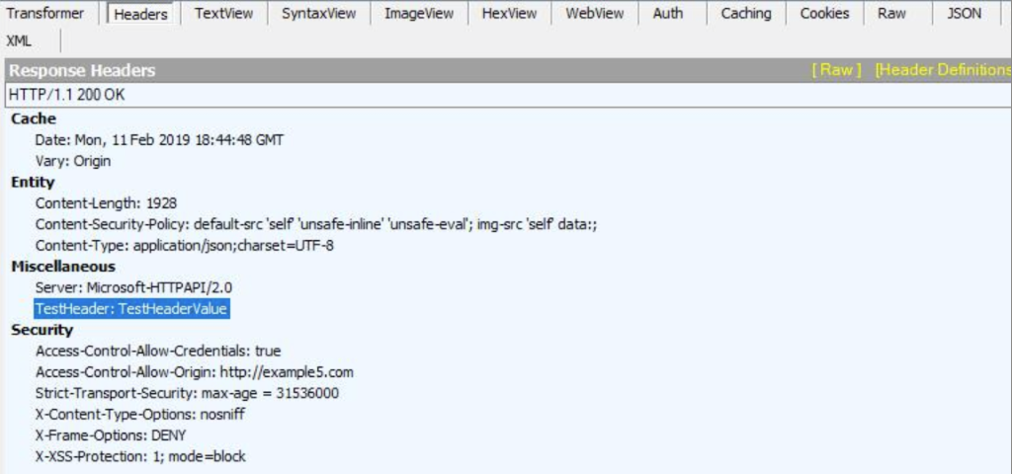
Vlastní hlavičky
Kromě dříve uvedených hlaviček odpovědí zabezpečení (HSTS, CSP, X-Frame-Options, X-XSS-Protection a CORS) umožňuje služba AD FS 2019 nastavit nová záhlaví.
Jako příklad můžete nastavit novou hlavičku TestHeader a TestHeaderValue jako hodnotu.
Set-AdfsResponseHeaders -SetHeaderName "TestHeader" -SetHeaderValue "TestHeaderValue"
Po nastavení se nová hlavička odešle v odpovědi služby AD FS, jak je znázorněno v následujícím fragmentu kódu Fiddleru:
Kompatibilita webového prohlížeče
Pomocí následující tabulky a odkazů určete, které webové prohlížeče jsou kompatibilní s jednotlivými hlavičkami odpovědi zabezpečení.
| Hlavičky odpovědi zabezpečení HTTP | Kompatibilita prohlížeče |
|---|---|
| StriktníTransport-Security HTTP (HSTS) | Kompatibilita prohlížeče HSTS |
| X-Frame-Options | Kompatibilita prohlížečeFrame-Options X |
| X-XSS-Protection | Kompatibilita prohlížečeXSS-Protection X |
| Sdílení prostředků mezi zdroji (CORS) | Kompatibilita prohlížeče CORS |
| Zásady zabezpečení obsahu (CSP) | Kompatibilita prohlížeče CSP |
