Configure a managed identity for a dev center
This guide explains how to add and configure a managed identity for your Azure Deployment Environments dev center to enable secure deployment for development teams.
Azure Deployment Environments uses managed identities to give development teams self-serve deployment capabilities without giving them access to the subscriptions in which Azure resources are created. A managed identity adds elevated-privileges capabilities and secure authentication to any service that supports Microsoft Entra authentication.
The managed identity attached to a dev center should be assigned both the Contributor role and the User Access Administrator role in the deployment subscriptions for each environment type. When an environment deployment is requested, the service grants appropriate permissions to the deployment identities that are set up for the environment type to deploy on behalf of the user. The managed identity attached to a dev center also is used to add to a catalog and access environment definitions in the catalog.
Add a managed identity
In Azure Deployment Environments, you can choose between two types of managed identities:
- System-assigned identity: A system-assigned identity is tied either to your dev center or to the project environment type. A system-assigned identity is deleted when the attached resource is deleted. A dev center or a project environment type can have only one system-assigned identity.
- User-assigned identity: A user-assigned identity is a standalone Azure resource that you can assign to your dev center or to a project environment type. For Azure Deployment Environments, a dev center or a project environment type can have only one user-assigned identity.
As a security best practice, if you choose to use user-assigned identities, use different identities for your project and for your dev center. Project identities should have more limited access to resources compared to a dev center.
Note
In Azure Deployment Environments, if you add both a system-assigned identity and a user-assigned identity, only the user-assigned identity is used.
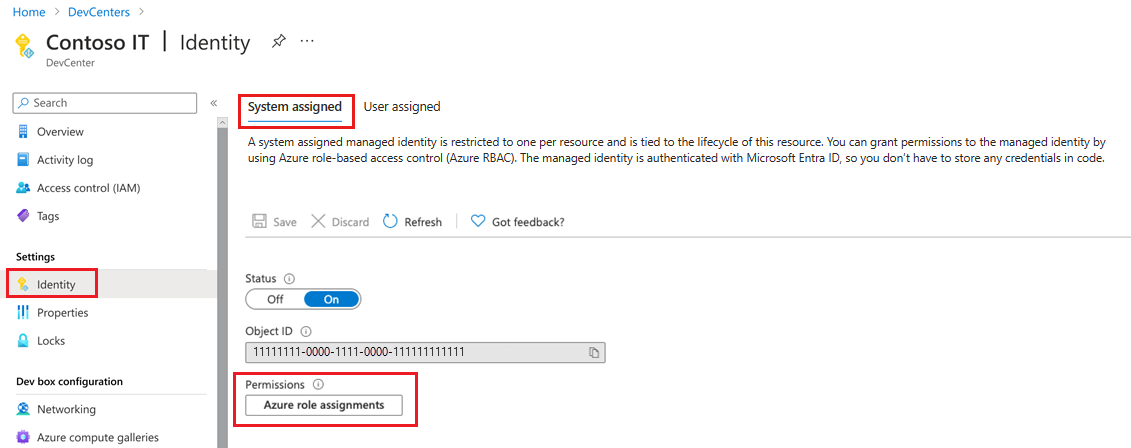
Add a system-assigned managed identity
Sign in to the Azure portal and go to Azure Deployment Environments.
On Dev centers, select your dev center.
On the left menu under Settings, select Identity.
Under System assigned, set Status to On.
Select Save.
In the Enable system assigned managed identity dialog, select Yes.
Add a user-assigned managed identity
Sign in to the Azure portal and go to Azure Deployment Environments.
On Dev centers, select your dev center.
On the left menu under Settings, select Identity.
Under User assigned, select Add to attach an existing identity.
On Add user assigned managed identity, enter or select the following information:
- On Subscription, select the subscription in which the identity exists.
- On User assigned managed identities, select an existing identity.
- Select Add.
Assign a subscription role assignment
The identity attached to the dev center should be assigned the Contributor and User Access Administrator roles for all the deployment subscriptions and the Reader role for all subscriptions that contain the relevant project. When a user creates or deploys an environment, the service grants appropriate access to the deployment identity that's attached to the project environment type. The deployment identity uses the access to perform deployments on behalf of the user. You can use the managed identity to empower developers to create environments without granting them access to the subscription.
Add a role assignment to a system-assigned managed identity
In the Azure portal, navigate to your dev center in Azure Deployment Environments.
On the left menu under Settings, select Identity.
Under System assigned > Permissions, select Azure role assignments.
To give Contributor access to the subscription, select Add role assignment (Preview), enter or select the following information, and then select Save:
Name Value Scope Subscription Subscription Select the subscription in which to use the managed identity. Role Contributor To give User Access Administrator access to the subscription, select Add role assignment (Preview), enter or select the following information, and then select Save:
Name Value Scope Subscription Subscription Select the subscription in which to use the managed identity. Role User Access Administrator
Add a role assignment to a user-assigned managed identity
In the Azure portal, navigate to your dev center.
On the left menu under Settings, select Identity.
Under User assigned, select the identity.
On the left menu, select Azure role assignments.
To give Contributor access to the subscription, select Add role assignment (Preview), enter or select the following information, and then select Save:
Name Value Scope Subscription Subscription Select the subscription in which to use the managed identity. Role Contributor To give User Access Administrator access to the subscription, select Add role assignment (Preview), enter or select the following information, and then select Save:
Name Value Scope Subscription Subscription Select the subscription in which to use the managed identity. Role User Access Administrator
Grant the managed identity access to the key vault secret
You can set up your key vault to use either a key vault access policy or Azure role-based access control.
Note
Before you can add a repository as a catalog, you must grant the managed identity access to the key vault secret that contains the repository's personal access token.
Key vault access policy
If the key vault is configured to use a key vault access policy:
In the Azure portal, go to the key vault that contains the secret with the personal access token.
On the left menu, select Access policies, and then select Create.
On Create an access policy, enter or select the following information:
- On the Permissions tab, under Secret permissions, select the Get checkbox, and then select Next.
- On the Principal tab, select the identity that's attached to the dev center.
- Select Review + create, and then select Create.
Azure role-based access control
If the key vault is configured to use Azure role-based access control:
In the Azure portal, go to the key vault that contains the secret with the personal access token.
On the left menu, select Access control (IAM).
Select the identity, and in the left menu, select Azure role assignments.
Select Add role assignment, and then enter or select the following information:
- For Scope, select the key vault.
- For Subscription, select the subscription that contains the key vault.
- For Resource, select the key vault.
- For Role, select Key Vault Secrets User.
- Select Save.
Related content
Feedback
Kommer snart: I hele 2024 udfaser vi GitHub-problemer som feedbackmekanisme for indhold og erstatter det med et nyt feedbacksystem. Du kan få flere oplysninger under: https://aka.ms/ContentUserFeedback.
Indsend og få vist feedback om