Hello @Mr Edge ,
Thank you for posting your query on Microsoft Q&A.
From the given description I could understand that you are looking to have one user with to be linked with different federated accounts.
We could not have 2 identical local accounts with same IDP however we could have 1 account linked to a federated account and similar account linked to different federation service (Example U1@jaswant .COM could be signed up as a local user, as a FB user and as a Gmail user with same UPN), via custom policy.
With Azure AD B2C an account can have multiple identities, local (username and password) or social/enterprise identity (such as Facebook or AAD). For more information, see User profile attributes This Azure AD B2C sample demonstrates how to link and unlink existing Azure AD B2C account to a social identity.
The following diagram illustrates the linking flow:
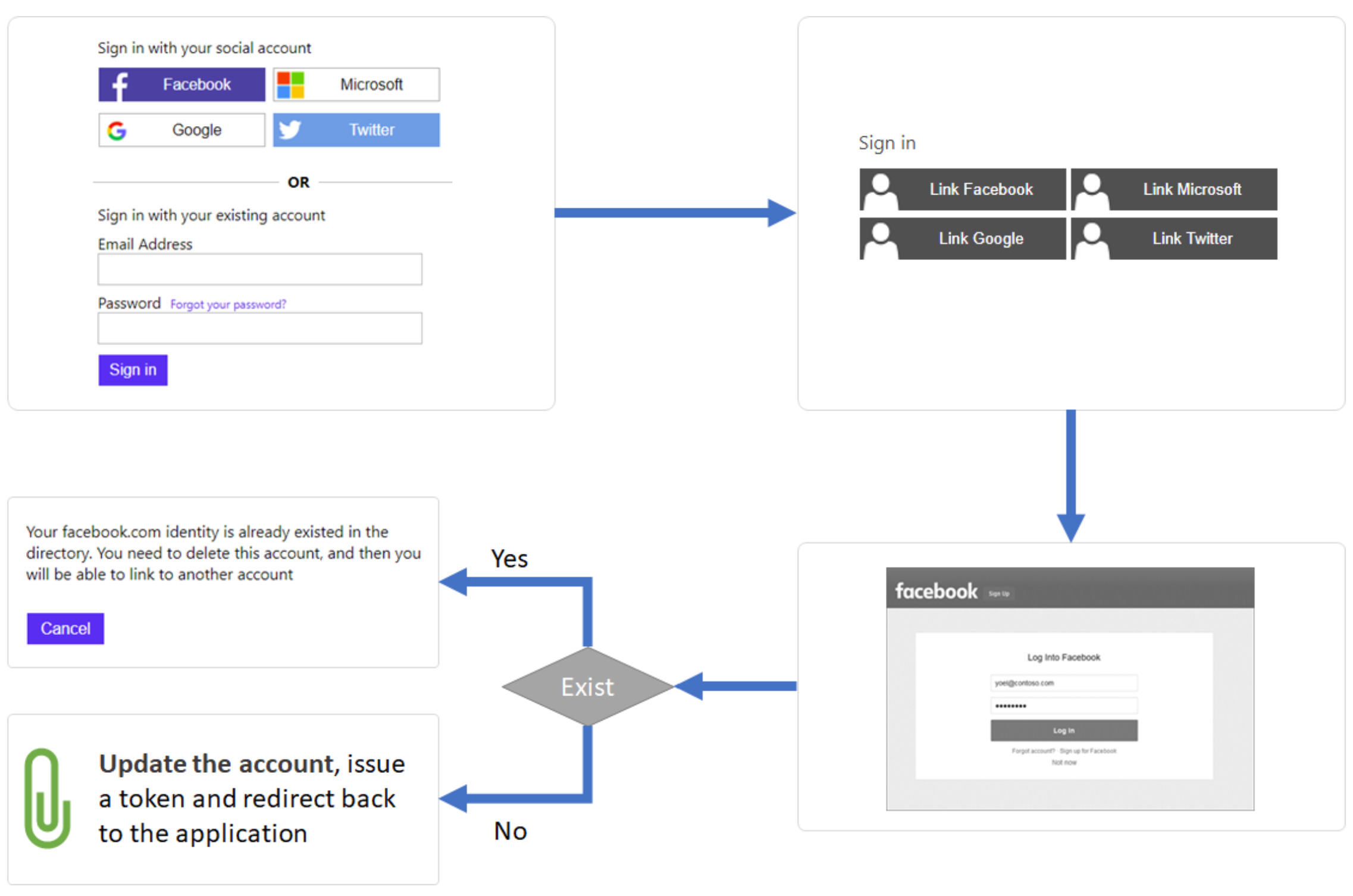
- To link a local or federated account to another federated identity, user fist sign-in (with a local or federated account).
- The policy reads the account form the directory and checks the value of the userIdentities attribute. The policy extracts the names of the issuer to a string collection. Based on this string collection, the policy show/hide the technical profile. For example:
- If the collection is empty, user will see the four options to link with: Facebook, Microsoft, Google, and Twitter. While hiding the unlink with Facebook, Microsoft, Google, and Twitter.
- After user linked a Facebook account, on the next time user execute the link policy, the user will see link: Microsoft, Google, and Twitter, and unlink Facebook.
- When user clicks on:
- One of the link federated account buttons, which takes the user to the identity provider to complete the sign-in. The policy tries to find such an account in the directory. If found, the policy displays an error message "You facebook.com identity already exists...". If not found, the policy adds the new federated identity to the userIdenitites collection and update the account.
- One of the unlink federated account buttons, which takes the user to the federated identity provider to complete the sign-in. After user complete the sign-in with the selected identity provider, the policy removed that issuer from the userIdenitites collection and update the account.
- Azure AD B2C issues an access token.
Please refer to https://github.com/azure-ad-b2c/samples/tree/master/policies/account-linkage-unified for custom policy sample and let me know if you have any further queries.
Thanks,
Akshay Kaushik
Please "Accept the answer", "Upvote" and rate your experience if the suggestion works as per your business need. This will help us and others in the community as well.