Ok, I don't have any machine accounts listed here so they may have been manually added. I'd probably look for and delete from the parent level.
--please don't forget to upvote and Accept as answer if the reply is helpful--
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Hello. I finally replaced my 2012 DCs with 2019. One of the 2012 DCs was a VM. I'm seeing this VM's account listed in the ACL of many SRV records. These are the records in DNS-Forward Lookup Zones-[our doman name]... in the _tcp and _udp folders. How do I clean up the ACL on all these records?
Ok, I don't have any machine accounts listed here so they may have been manually added. I'd probably look for and delete from the parent level.
--please don't forget to upvote and Accept as answer if the reply is helpful--
Just checking if there's any progress or updates?
--please don't forget to upvote and Accept as answer if the reply is helpful--
Hello LimitlessTechnology. Thanks for this powershell method. These commands do not find anything because I don't have any records of the old dns server. What I have is records of the new dns servers but within those records in the ACL is the machine account of one of the retired DCs. It is listed (under the Security tab) as RetiredDCName$ with Write and Special permissions ticked.
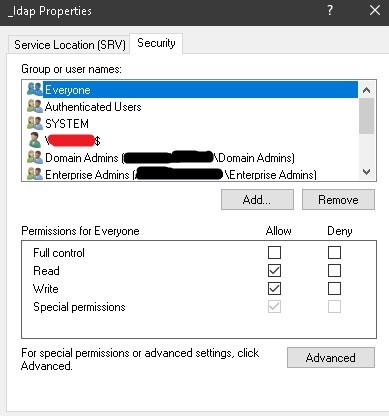
Here is an example. This is the just the _ldap properties but this DC is in the ACL of all the SRV records under the domain. The Machine account crossed off in red is one of the old DCs. A DC that was removed successfully with the Remove Roles & Features.