Web sign-in for Windows
Starting in Windows 11, version 22H2 with KB5030310, you can enable a web-based sign-in experience on Microsoft Entra joined devices. This feature is called Web sign-in, and it unlocks new sign-in options and capabilities.
Web sign-in is a credential provider, and it was initially introduced in Windows 10 with support for Temporary Access Pass (TAP) only. With the release of Windows 11, the supported scenarios and capabilities of Web sign-in are expanded.
For example, you can sign in with the Microsoft Authenticator app or with a SAML-P federated identity.
This article describes how to configure Web sign-in and the supported key scenarios.
System requirements
Here are the prerequisites for using Web sign-in:
- Windows 11, version 22H2 with 5030310, or later
- Microsoft Entra joined
- Internet connectivity, as the authentication is done over the Internet
Important
Web sign-in is not supported for Microsoft Entra hybrid joined or domain joined devices.
Windows edition and licensing requirements
The following table lists the Windows editions that support Web sign-in:
| Windows Pro | Windows Enterprise | Windows Pro Education/SE | Windows Education |
|---|---|---|---|
| Yes | Yes | Yes | Yes |
Web sign-in license entitlements are granted by the following licenses:
| Windows Pro/Pro Education/SE | Windows Enterprise E3 | Windows Enterprise E5 | Windows Education A3 | Windows Education A5 |
|---|---|---|---|---|
| Yes | Yes | Yes | Yes | Yes |
For more information about Windows licensing, see Windows licensing overview.
Configure web sign-in
To use web sign-in, your devices must be configured with different policies. Review the following instructions to configure your devices using either Microsoft Intune or a provisioning package (PPKG).
Note
Web sign-in uses a system-managed local account called WsiAccount. The account is created automatically when you enable Web sign-in, and it's not displayed in the user selection list. Every time a user uses the Web sign-in credential provider, the WsiAccount account is enabled. After the user signs in, the account is disabled.
To configure devices with Microsoft Intune, create a Settings catalog policy and use the following settings:
| Category | Setting name | Value |
|---|---|---|
| Authentication | Enable Web Sign In | Enabled |
| Authentication | Configure Web Sign In Allowed Urls | This setting is optional, and it contains a list of domains required for sign in, for example: - idp.example.com- example.com |
| Authentication | Configure Webcam Access Domain Names | This setting is optional, and it should be configured if you need to use the webcam during the sign-in process. Specify the list of domains that are allowed to use the webcam during the sign-in process, for example: example.com |
Assign the policy to a group that contains as members the devices or users that you want to configure.
Alternatively, you can configure devices using a custom policy with the following settings:
| OMA-URI | More information |
|---|---|
./Vendor/MSFT/Policy/Config/Authentication/EnableWebSignIn |
EnableWebSignIn |
./Vendor/MSFT/Policy/Config/Authentication/ConfigureWebSignInAllowedUrls |
ConfigureWebSignInAllowedUrls |
./Vendor/MSFT/Policy/Config/Authentication/ConfigureWebCamAccessDomainNames |
ConfigureWebcamAccessDomainNames |
User experiences
Once the devices are configured, a new sign-in experience becomes available, as indicated by the presence of the Web sign-in credential provider
in the Windows lock screen.
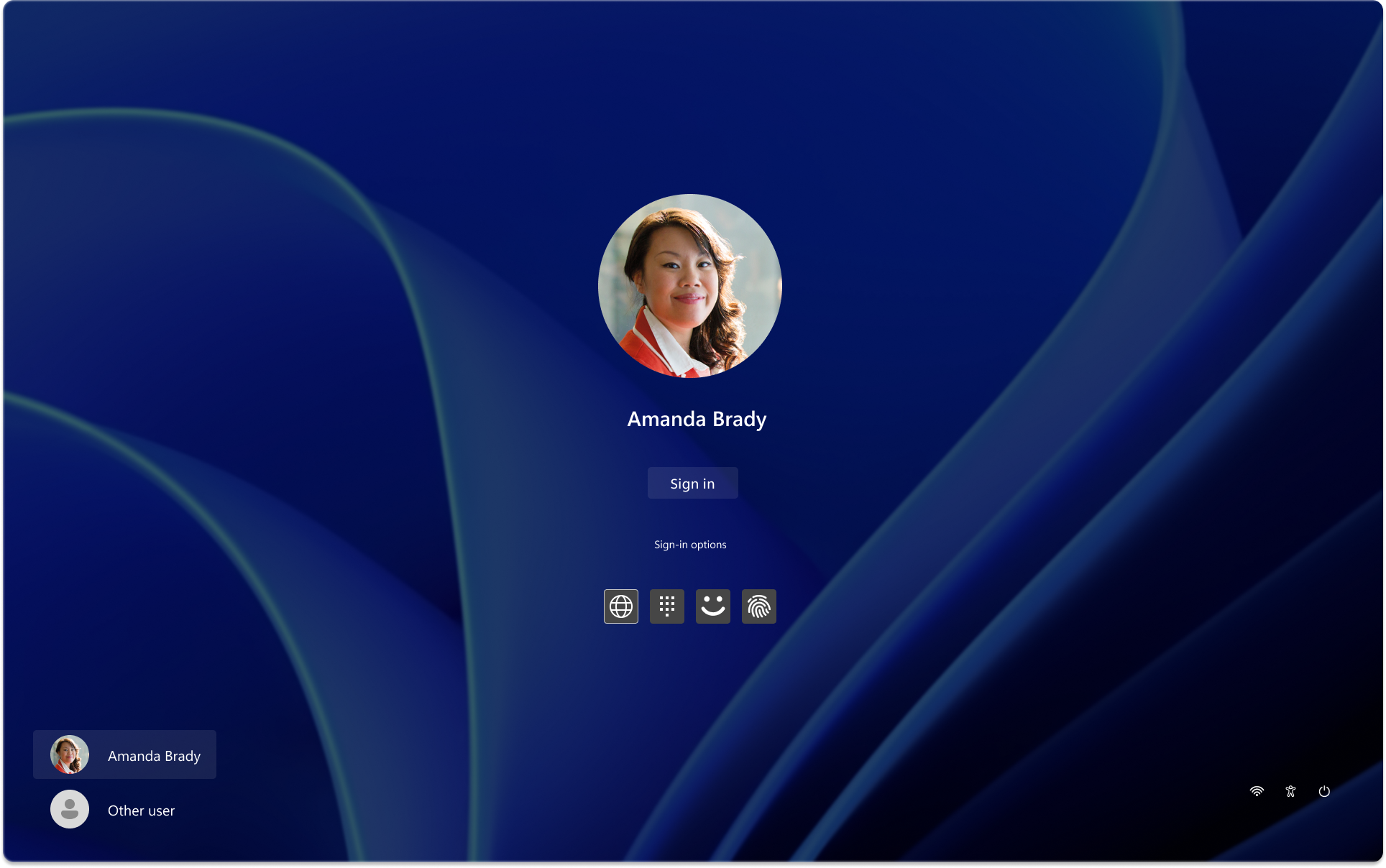
Here's a list of key scenarios supported by Web sign-in, and a brief animation showing the user experience. Select the thumbnail to start the animation.
Passwordless sign-in
Users can sign in to Windows passwordless, even before enrolling in Windows Hello for Business. For example, by using the Microsoft Authenticator app as a sign-in method.
Tip
When used in conjuction with Windows Hello for Business passwordless, you can hide the password credential provider from the lock screen as well as in-session authentication scenarios. This enables a truly passwordless Windows experience.
To learn more:
- Enable passwordless sign-in with Microsoft Authenticator
- Passwordless authentication options for Microsoft Entra ID
- Windows passwordless experience
Windows Hello for Business PIN reset
The Windows Hello PIN reset flow is seamless and more robust than in previous versions.
For more information, see PIN reset.
Temporary Access Pass (TAP)
A Temporary Access Pass (TAP) is a time-limited passcode granted by an administrator to a user. Users can sign in with a TAP using the Web sign-in credential provider. For example:
- to onboard Windows Hello for Business or a FIDO2 security key
- if lost or forgotten FIDO2 security key and unknown password
For more information, see Use a Temporary Access Pass.
Federated authentication
If the Microsoft Entra tenant is federated with a non-Microsoft SAML-P identity provider (IdP), federated users can sign using the Web sign-in credential provider.
Tip
To improve the user experience for federated identities:
- Enable Windows Hello for Business. Once the user signs in, the user can enroll in Windows Hello for Business and then use it to sign in to the device
- Configure the preferred Microsoft Entra tenant name feature, which allows users to select the domain name during the sign-in process. The users are then automatically redirected to the identity provider sign-in page
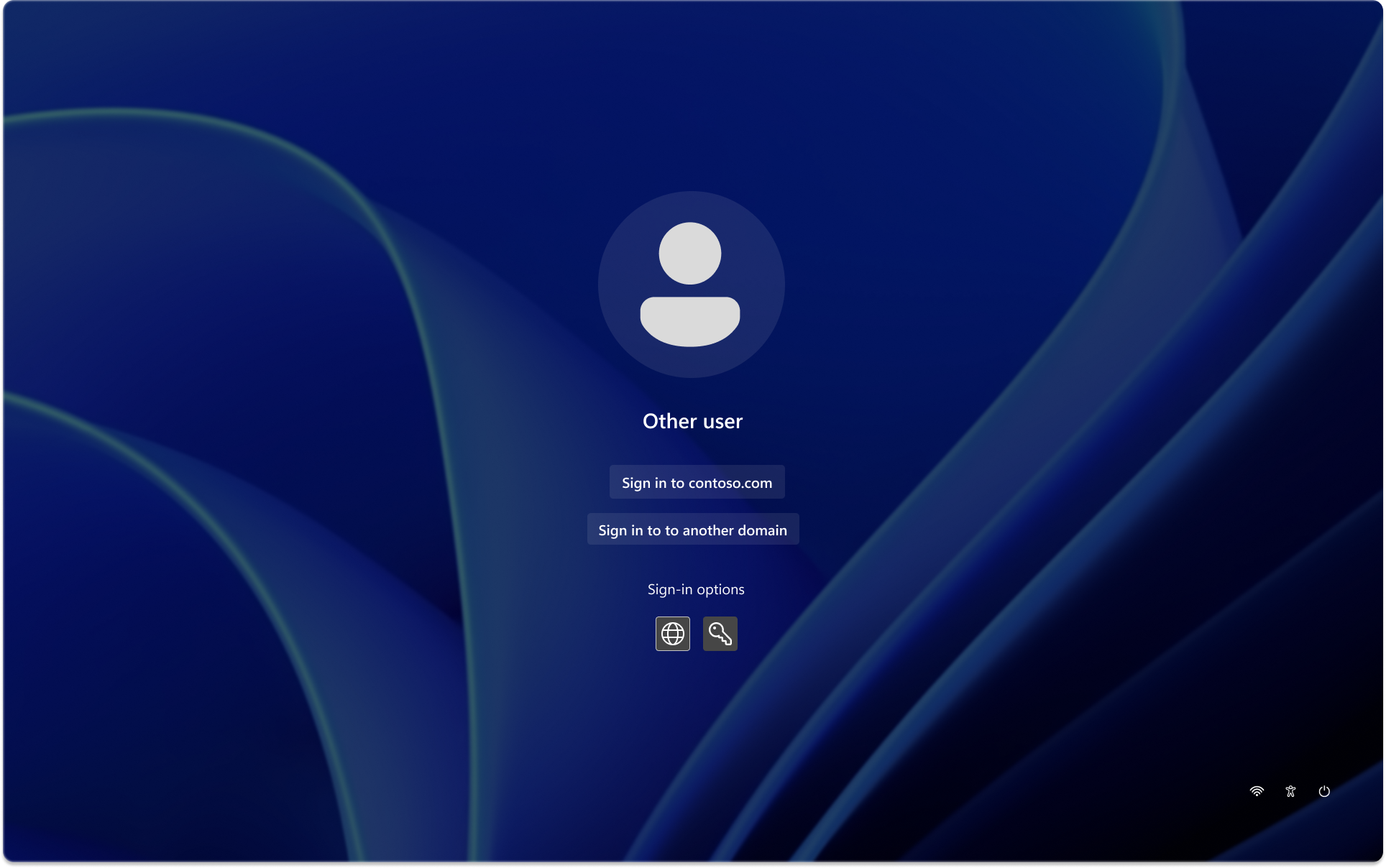
For more information about preferred tenant name, see Authentication CSP - PreferredAadTenantDomainName.
Important considerations
Here's a list of important considerations to keep in mind when configuring or using Web sign-in:
- Cached credentials aren't supported with Web sign-in. If the device is offline, the user can't use the Web sign-in credential provider to sign in
- After sign out, the user isn't displayed in the user selection list
- Once enabled, the Web sign-in credential provider is the default credential provider for new users signing in to the device. To change the default credential provider, you can use the DefaultCredentialProvider ADMX-backed policy
- The user can exit the Web sign-in flow by pressing Ctrl+Alt+Delete to get back to the Windows lock screen
Known issues
- If you attempt to sign in while the device is offline, you get the following message: It doesn't look like you're connected to the Internet. Check your connection and try again. Selecting the Back to sign-in option doesn't bring you back to the lock screen. As a workaround, you can press Ctrl+Alt+Delete to get back to the lock screen.
 Provide feedback
Provide feedback
To provide feedback for web sign-in, open Feedback Hub and use the category Security and Privacy > Passwordless experience.
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for