Events
Apr 9, 3 p.m. - Apr 10, 12 p.m.
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register NowThis browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
This article describes the steps that you'll take in both ServiceNow and Microsoft Entra ID to configure automatic user provisioning. When Microsoft Entra ID is configured, it automatically provisions and deprovisions users and groups to ServiceNow by using the Microsoft Entra provisioning service.
For more information on the Microsoft Entra automatic user provisioning service, see Automate user provisioning and deprovisioning to SaaS applications with Microsoft Entra ID.
Note
This integration is also available to use from Microsoft Entra US Government Cloud environment. You can find this application in the Microsoft Entra US Government Cloud Application Gallery and configure it in the same way as you do from public cloud.
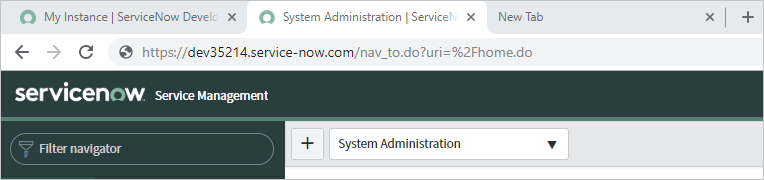
Identify your ServiceNow instance name. You can find the instance name in the URL that you use to access ServiceNow. In the following example, the instance name is dev35214.
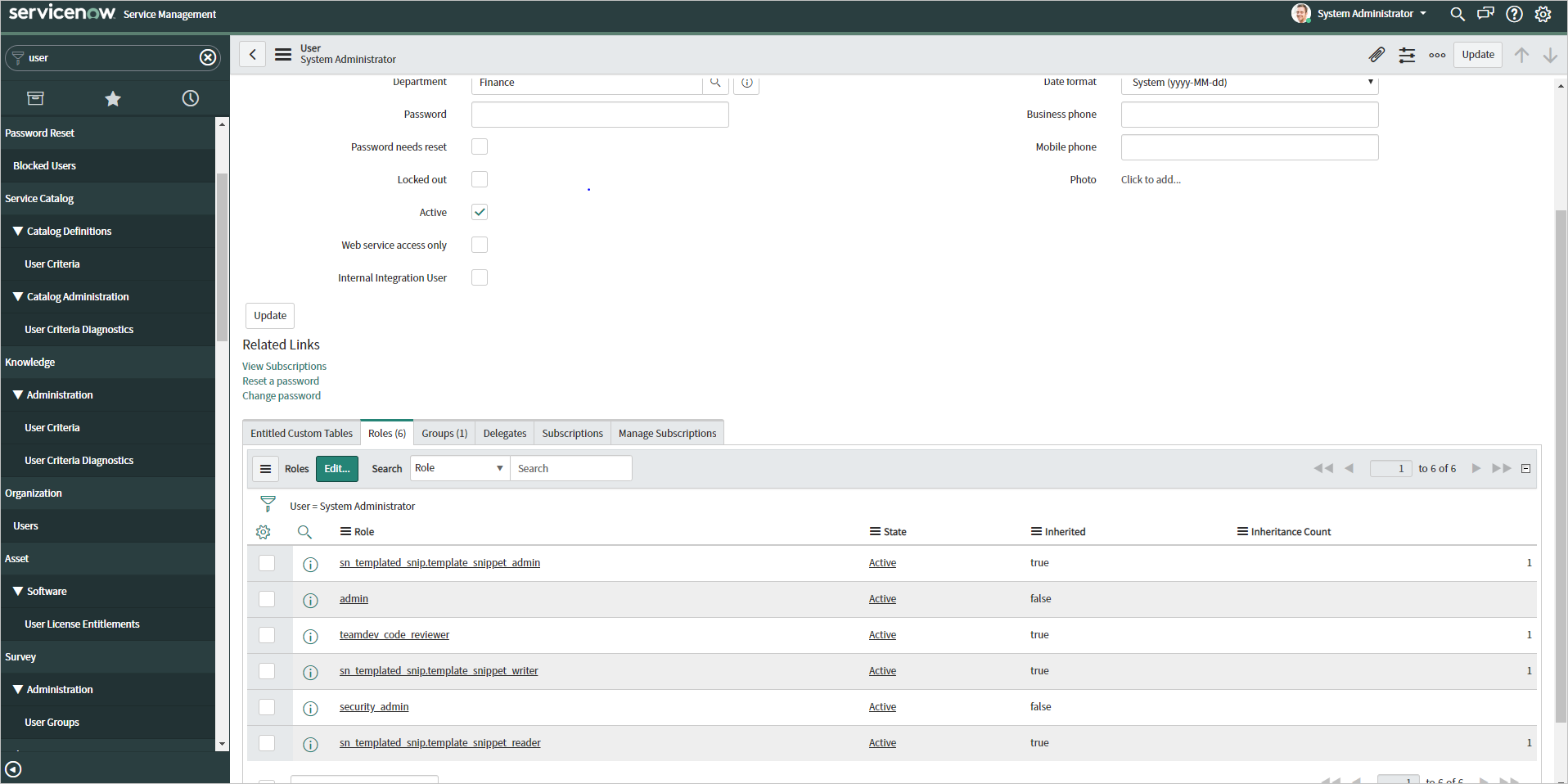
Obtain credentials for an admin in ServiceNow. Go to the user profile in ServiceNow and verify that the user has the admin role.
Add ServiceNow from the Microsoft Entra application gallery to start managing provisioning to ServiceNow. If you previously set up ServiceNow for single sign-on (SSO), you can use the same application. However, we recommend that you create a separate app when you're testing the integration. Learn more about adding an application from the gallery.
The Microsoft Entra provisioning service allows you to scope who will be provisioned based on assignment to the application, or based on attributes of the user or group. If you choose to scope who will be provisioned to your app based on assignment, you can use the steps to assign users and groups to the application. If you choose to scope who will be provisioned based solely on attributes of the user or group, you can use a scoping filter.
Keep the following tips in mind:
When you're assigning users and groups to ServiceNow, you must select a role other than Default Access. Users with the Default Access role are excluded from provisioning and will be marked as not effectively entitled in the provisioning logs. If the only role available on the application is the Default Access role, you can update the application manifest to add more roles.
If you need additional roles, you can update the application manifest to add new roles.
This section guides you through the steps to configure the Microsoft Entra provisioning service to create, update, and disable users and groups in TestApp. You can base the configuration on user and group assignments in Microsoft Entra ID.
To configure automatic user provisioning for ServiceNow in Microsoft Entra ID:
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
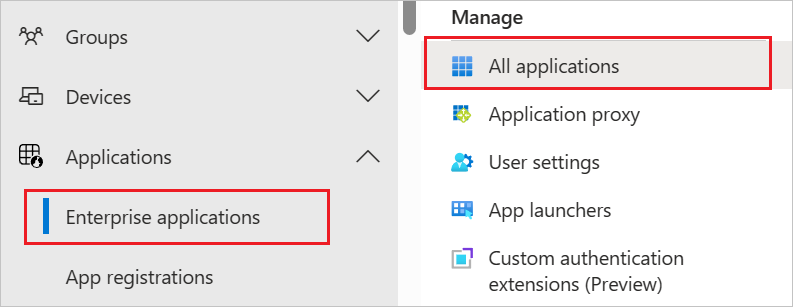
Browse to Identity > Applications > Enterprise applications.
In the list of applications, select ServiceNow.
Select the Provisioning tab.
Set Provisioning Mode to Automatic.
In the Admin Credentials section, enter your ServiceNow admin credentials and username. Select Test Connection to ensure that Microsoft Entra ID can connect to ServiceNow. If the connection fails, ensure that your ServiceNow account has admin permissions and try again.
In the Notification Email box, enter the email address of a person or group that should receive the provisioning error notifications. Then select the Send an email notification when a failure occurs check box.
Select Save.
In the Mappings section, select Synchronize Microsoft Entra users to ServiceNow.
Review the user attributes that are synchronized from Microsoft Entra ID to ServiceNow in the Attribute-Mapping section. The attributes selected as Matching properties are used to match the user accounts in ServiceNow for update operations.
If you choose to change the matching target attribute, you'll need to ensure that the ServiceNow API supports filtering users based on that attribute.
Select the Save button to commit any changes.
In the Mappings section, select Synchronize Microsoft Entra groups to ServiceNow.
Review the group attributes that are synchronized from Microsoft Entra ID to ServiceNow in the Attribute-Mapping section. The attributes selected as Matching properties are used to match the groups in ServiceNow for update operations. Select the Save button to commit any changes.
To configure scoping filters, see the instructions in the Scoping filter article.
To enable the Microsoft Entra provisioning service for ServiceNow, change Provisioning Status to On in the Settings section.
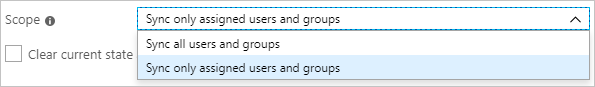
Define the users and groups that you want to provision to ServiceNow by choosing the desired values in Scope in the Settings section.
When you're ready to provision, select Save.
This operation starts the initial synchronization cycle of all users and groups defined in Scope in the Settings section. The initial cycle takes longer to perform than subsequent cycles. Subsequent cycles occur about every 40 minutes, as long as the Microsoft Entra provisioning service is running.
After you've configured provisioning, use the following resources to monitor your deployment:
When you're provisioning certain attributes (such as Department and Location) in ServiceNow, the values must already exist in a reference table in ServiceNow. If they don't, you'll get an InvalidLookupReference error.
For example, you might have two locations (Seattle, Los Angeles) and three departments (Sales, Finance, Marketing) in a certain table in ServiceNow. If you try to provision a user whose department is "Sales" and whose location is "Seattle," that user will be provisioned successfully. If you try to provision a user whose department is "Sales" and whose location is "LA," the user won't be provisioned. The location "LA" must be added to the reference table in ServiceNow, or the user attribute in Microsoft Entra ID must be updated to match the format in ServiceNow.
If you get an EntryJoiningPropertyValueIsMissing error, review your attribute mappings to identify the matching attribute. This value must be present on the user or group you're trying to provision.
To understand any requirements or limitations (for example, the format to specify a country code for a user), review the ServiceNow SOAP API.
Provisioning requests are sent by default to https://{your-instance-name}.service-now.com/{table-name}. If you need a custom tenant URL, you can provide the entire URL as the instance name.
The ServiceNowInstanceInvalid error indicates a problem communicating with the ServiceNow instance. Here's the text of the error:
Details: Your ServiceNow instance name appears to be invalid. Please provide a current ServiceNow administrative user name and password along with the name of a valid ServiceNow instance.
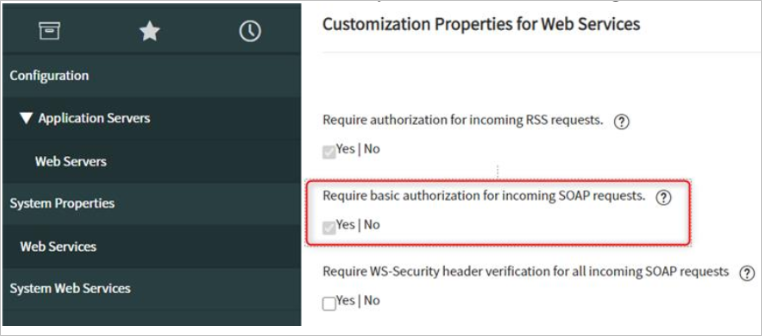
If you're having test connection problems, try selecting No for the following settings in ServiceNow:
System Security > High security settings > Require basic authentication for incoming SCHEMA requests
System Properties > Web Services > Require basic authorization for incoming SOAP requests
If you still can't resolve your problem, contact ServiceNow support, and ask them to turn on SOAP debugging to help troubleshoot.
The Microsoft Entra provisioning service currently operates under particular IP ranges. If necessary, you can restrict other IP ranges and add these particular IP ranges to the allowlist of your application. That technique will allow traffic flow from the Microsoft Entra provisioning service to your application.
Self-hosted ServiceNow instances aren't supported.
When an update to the active attribute in ServiceNow is provisioned, the attribute locked_out is also updated accordingly, even if locked_out is not mapped in the Azure provisioning service.
Events
Apr 9, 3 p.m. - Apr 10, 12 p.m.
Code the Future with AI and connect with Java peers and experts at JDConf 2025.
Register NowTraining
Learning path
Solution Architect: Design Microsoft Power Platform solutions - Training
Learn how a solution architect designs solutions.
Certification
Microsoft Certified: Identity and Access Administrator Associate - Certifications
Demonstrate the features of Microsoft Entra ID to modernize identity solutions, implement hybrid solutions, and implement identity governance.
Documentation
Microsoft Entra single sign-on (SSO) integration with ServiceNow - Microsoft Entra ID
Learn how to configure single sign-on between Microsoft Entra ID and ServiceNow.
Learn how to use scoping filters to define attribute-based rules that determine which users or groups are provisioned in Microsoft Entra ID.
Learn about attribute mappings for Software as a Service (SaaS) apps in Microsoft Entra Application Provisioning. Learn what attributes are and how you can modify them to address your business needs.