Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
By using Microsoft Entra authentication context, you can enforce more stringent access conditions when users access SharePoint sites.
Use authentication contexts to connect an Microsoft Entra Conditional Access policy to a SharePoint site. You can apply policies directly to the site or apply them through a sensitivity label.
You can't apply this capability to the root site in SharePoint (for example, https://contoso.sharepoint.com).
Before you begin
Review the SharePoint Advanced Management prerequisites.
In addition, you need one of the following licenses:
- Microsoft 365 E5/A5 Compliance
- Microsoft 365 E5 Information Protection and Governance
Limitations
Some apps don't work with authentication contexts. Test apps on a site with authentication context enabled before broadly deploying this feature.
The following apps and scenarios don't work with authentication contexts:
- Older versions of Office apps (see the list of supported versions)
- SharePoint mobile apps (iOS and Android)
- Viva Engage
- You can't add the OneNote app to a channel if the associated SharePoint site has an authentication context.
- Teams channel meeting recording upload fails on sites with an authentication context.
- SharePoint folder renaming in Teams fails if the site has an authentication context.
- Teams webinar scheduling fails if OneDrive has an authentication context.
- The OneDrive sync app won't sync sites with an authentication context.
- Associating an authentication context to the enterprise application catalog site collection isn't supported.
- The "Visualize SharePoint List in Power BI" feature doesn't currently support authentication context.
- Outlook on Windows, Mac, Android, and iOS don't support communication with SharePoint sites protected by an Authentication Context.
- The multiple-file download feature currently doesn't function when both the authentication context and 'Use Conditional Access App Control' in session control are enabled in the conditional access policy.
- The multiple-file download feature won't work if an authentication context is set directly on a SharePoint site without an active Conditional Access policy using that context, or if the policy exists but is disabled.
- The file copy and move feature between different regions (cross-geo) currently doesn't function when an authentication context is applied to the destination site.
- Exporting to Excel as an Excel Web Query (IQY) doesn't currently support authentication context.
Set up an authentication context
To set up an authentication context for labeled sites, complete these basic steps:
Add an authentication context in Microsoft Entra ID.
Create a Conditional Access policy that applies to that authentication context and has the conditions and access controls that you want to use.
Do one of the following steps:
Set a sensitivity label to apply the authentication context to labeled sites.
Apply the authentication context directly to a site.
In this article, you see the example of requiring guests to agree to a terms of use before gaining access to a sensitive SharePoint site. You can also use any of the other conditional access conditions and access controls that you might need for your organization.
Add an authentication context
First, add an authentication context in Microsoft Entra ID.
To add an authentication context:
In Microsoft Entra Conditional Access, under Manage, select Authentication context.
Select New authentication context.
Type a name and description, and select the Publish to apps check box.
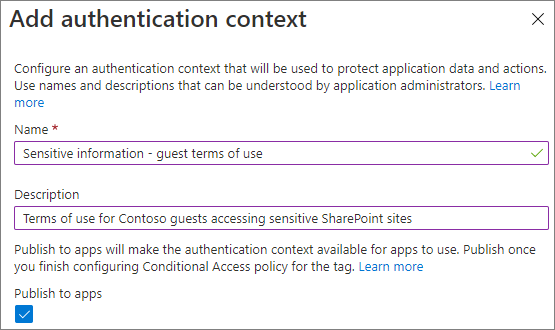
Select Save.
Create a Conditional Access policy
Next, create a Conditional Access policy that applies to that authentication context and requires guests to agree to terms of use as a condition of access.
To create a Conditional Access policy:
In Microsoft Entra Conditional Access, select New policy.
Enter a name for the policy.
On the Users and groups tab, choose the Select users and groups option, and then select the Guest or external users check box.
Choose B2B collaboration guest users from the dropdown.
On the Cloud apps or actions tab, under Select what this policy applies to, choose Authentication context, and select the check box for the authentication context that you created.

On the Grant tab, select the check box for the terms of use that you want to use, and then select Select.
Choose if you want to enable the policy, and then select Create.
Apply the authentication context directly to a site
You can directly apply an authentication context to a SharePoint site by using the Set-SPOSite PowerShell cmdlet.
Note
This capability requires a Microsoft 365 E5 or Microsoft SharePoint Advanced Management license.
In the following example, you apply the authentication context you created earlier to a site called "research."
Set-SPOSite -Identity https://contoso.sharepoint.com/sites/research -ConditionalAccessPolicy AuthenticationContext -AuthenticationContextName "Sensitive information - guest terms of use"
Set a sensitivity label to apply the authentication context to labeled sites
If you want to use a sensitivity label to apply the authentication context, update a sensitivity label (or create a new one) to use the authentication context.
Note
Sensitivity labels require Microsoft 365 E5 or Microsoft 365 E3 plus the Advanced Compliance license.
To update a sensitivity label
In the Microsoft Purview portal, on the Information protection tab, select the label that you want to update and then select Edit label.
Select Next until you are on the Define protection settings for groups and sites page.
Ensure that the External sharing and Conditional Access settings check box is selected, and then select Next.
On the Define external sharing and device access settings page, select the Use Microsoft Entra Conditional Access to protect labeled SharePoint sites check box.
Select the Choose an existing authentication context option.
In the dropdown list, choose the authentication context that you want to use.
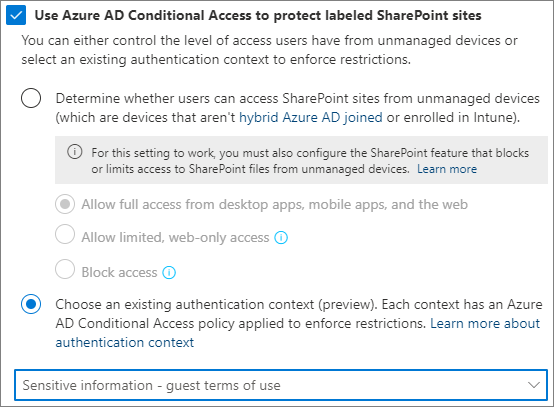
Select Next until you are on the Review your settings and finish page, and then select Save label.
After you update the label, guests accessing a SharePoint site (or the Files tab in a team) with that label must agree to the terms of use before gaining access to that site.
Block background apps
If you set authentication context on a site, admins can choose to prevent background apps from accessing that site for the apps assigned with that authentication context in a Conditional Access policy. You can configure a Conditional Access policy such that a specific authentication context can be assigned to chosen application principals (non-Microsoft applications). You need to explicitly turn on this feature by using the following cmdlet. You should have at least one Conditional Access policy with an application principal configured.
Set-SPOTenant -BlockAppAccessWithAuthenticationContext $false/$true (default false)
Third-party app integration
Third-party apps that use sites with authentication context attached need to be able to handle claims challenge. See Developer guide to Conditional Access authentication context.
See also
Conditional Access: Cloud apps, actions, and authentication context
