Describe Microsoft Defender for Office 365
Microsoft Defender for Office 365 is a seamless integration into your Office 365 subscription that provides protection against threats, like phishing and malware that arrive in email links (URLs), attachments, or collaboration tools like SharePoint, Teams, and Outlook. Defender for Office 365 provides real-time views of threats. It also provides investigation, hunting, and remediation capabilities to help security teams identify, prioritize, investigate, and respond to threats.
Microsoft Defender for Office 365 safeguards organizations against malicious threats by providing admins and security operations (sec ops) teams a wide range of capabilities.
- Preset security policies: Preset security policies allow you to apply protection features to users based on Microsoft recommended settings. A use case for preset security policies is during installation. Installation by preset can set up everything for you and is the recommended setup because it automates the roll-out of a secure environment.
- Threat protection policies: Define threat protection policies to set the appropriate level of protection for your organization.
- Reports: View real-time reports to monitor Microsoft Defender for Office 365 performance in your organization.
- Threat investigation and response capabilities: Use leading-edge tools to investigate, understand, simulate, and prevent threats.
- Automated investigation and response capabilities: Save time and effort investigating and mitigating threats.
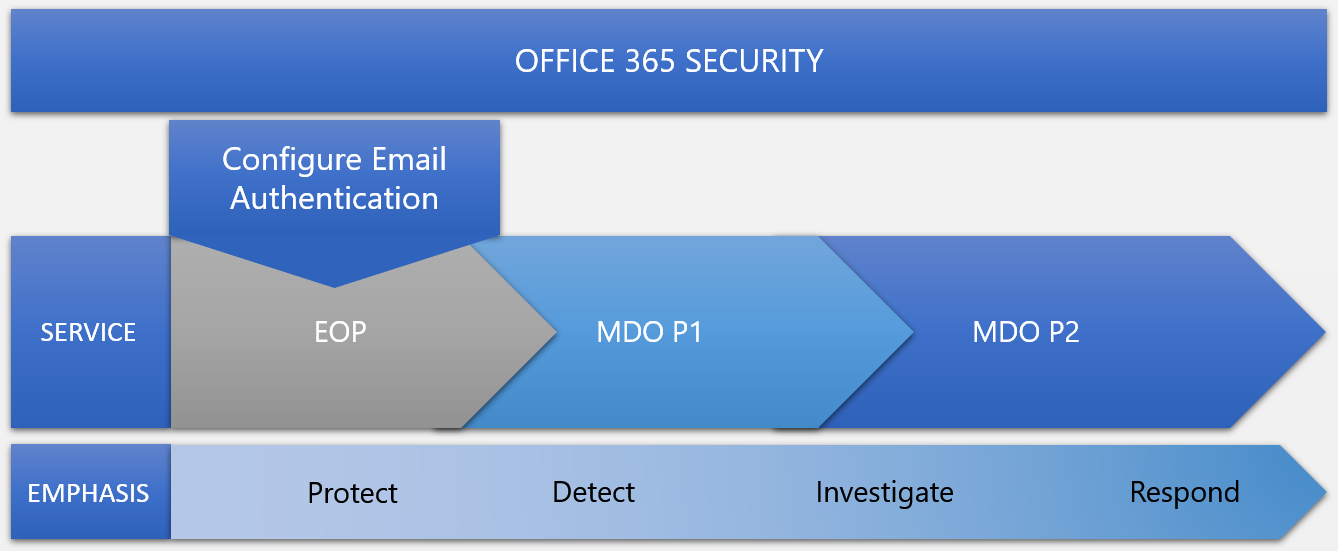
Microsoft Defender for Office 365 is available in two plans: Microsoft Defender for Office 365 Plan 1 and Plan 2. The security services of Defender for Office 365 are built on the core protections offered by Exchange Online Protection (EOP), which helps prevent broad, volume-based, known attacks and is present in any subscription where Exchange Online mailboxes can be found. Microsoft Defender for Office 365 P1 contains EOP in it plus protects email and collaboration from zero-day malware, phish, and business email compromise. Defender for Office 365 P2 contains P1 and EOP and adds post-breach investigation, hunting, response, automation, and training simulation. The structure is cumulative.
For a complete listing of the features in each plan, see the Microsoft Defender for Office 365 security product overview document that is linked in summary and resources unit of this module.