Automate the rotation of a secret for resources that have two sets of authentication credentials
The best way to authenticate to Azure services is by using a managed identity, but there are some scenarios where that isn't an option. In those cases, access keys or passwords are used. You should rotate access keys and passwords frequently.
This tutorial shows how to automate the periodic rotation of secrets for databases and services that use two sets of authentication credentials. Specifically, this tutorial shows how to rotate Azure Storage account keys stored in Azure Key Vault as secrets. You'll use a function triggered by Azure Event Grid notification.
Note
For Storage account services, using Microsoft Entra ID to authorize requests is recommended. For more information, see Authorize access to blobs using Microsoft Entra ID. There are services that require storage account connection strings with access keys. For that scenario, we recommend this solution.
Here's the rotation solution described in this tutorial:

In this solution, Azure Key Vault stores storage account individual access keys as versions of the same secret, alternating between the primary and secondary key in subsequent versions. When one access key is stored in the latest version of the secret, the alternate key is regenerated and added to Key Vault as the new latest version of the secret. The solution provides the application's entire rotation cycle to refresh to the newest regenerated key.
- Thirty days before the expiration date of a secret, Key Vault publishes the near expiry event to Event Grid.
- Event Grid checks the event subscriptions and uses HTTP POST to call the function app endpoint that's subscribed to the event.
- The function app identifies the alternate key (not the latest one) and calls the storage account to regenerate it.
- The function app adds the new regenerated key to Azure Key Vault as the new version of the secret.
- An Azure subscription. Create one for free.
- Azure Cloud Shell. This tutorial is using portal Cloud Shell with PowerShell env
- Azure Key Vault.
- Two Azure storage accounts.
Note
Rotation of shared storage account key revokes account level shared access signature (SAS) generated based on that key. After storage account key rotation, you must regenerate account-level SAS tokens to avoid disruptions to applications.
You can use this deployment link if you don't have an existing key vault and existing storage accounts:
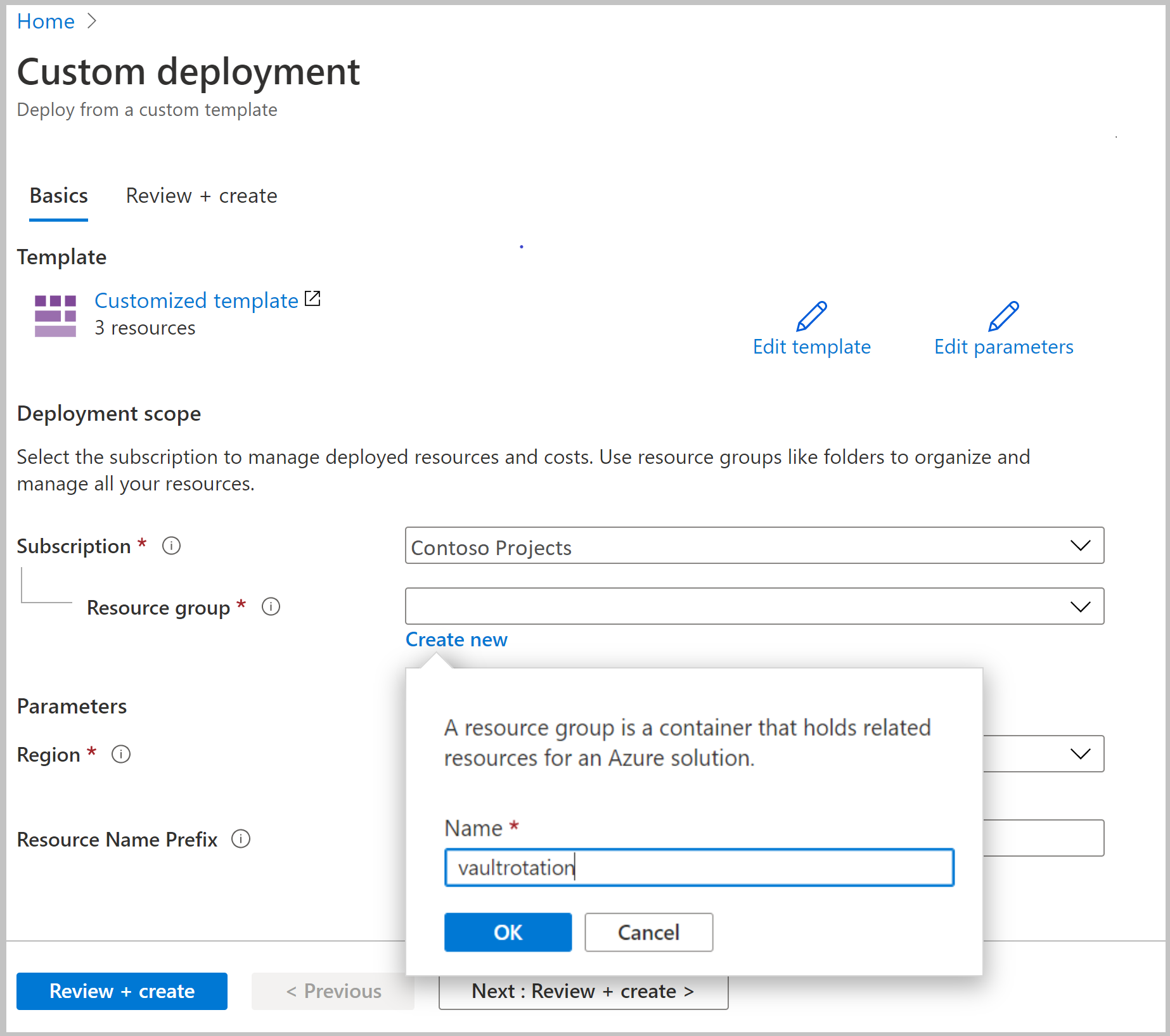
Under Resource group, select Create new. Name the group vault rotation and then select OK.
Select Review + create.
Select Create.
You'll now have a key vault and two storage accounts. You can verify this setup in the Azure CLI or Azure PowerShell by running this command:
az resource list -o table -g vaultrotation
The result will look something like this output:
Name ResourceGroup Location Type Status
----------------------- -------------------- ---------- --------------------------------- --------
vaultrotation-kv vaultrotation westus Microsoft.KeyVault/vaults
vaultrotationstorage vaultrotation westus Microsoft.Storage/storageAccounts
vaultrotationstorage2 vaultrotation westus Microsoft.Storage/storageAccounts
Next, you'll create a function app with a system-managed identity, in addition to other required components. You'll also deploy the rotation function for the storage account keys.
The function app rotation function requires the following components and configuration:
- An Azure App Service plan
- A storage account to manage function app triggers
- An access policy to access secrets in Key Vault
- The Storage Account Key Operator Service role assigned to the function app so it can access storage account access keys
- A key rotation function with an event trigger and an HTTP trigger (on-demand rotation)
- An Event Grid event subscription for the SecretNearExpiry event
Select the Azure template deployment link:
In the Resource group list, select vaultrotation.
In the Storage Account RG box, enter the name of the resource group in which your storage account is located. Keep the default value [resourceGroup().name] if your storage account is already located in the same resource group where you'll deploy the key rotation function.
In the Storage Account Name box, enter the name of the storage account that contains the access keys to rotate. Keep the default value [concat(resourceGroup().name, 'storage')] if you use storage account created in Prerequisites.
In the Key Vault RG box, enter the name of resource group in which your key vault is located. Keep the default value [resourceGroup().name] if your key vault already exists in the same resource group where you'll deploy the key rotation function.
In the Key Vault Name box, enter the name of the key vault. Keep the default value [concat(resourceGroup().name, '-kv')] if you use key vault created in Prerequisites.
In the App Service Plan Type box, select hosting plan. Premium Plan is needed only when your key vault is behind firewall.
In the Function App Name box, enter the name of the function app.
In the Secret Name box, enter the name of the secret where you'll store access keys.
In the Repo URL box, enter the GitHub location of the function code. In this tutorial, you can use https://github.com/Azure-Samples/KeyVault-Rotation-StorageAccountKey-PowerShell.git .
Select Review + create.
Select Create.

After you complete the preceding steps, you'll have a storage account, a server farm, a function app, and Application Insights. When the deployment is complete, you'll see this page:

Note
If you encounter a failure, you can select Redeploy to finish the deployment of the components.
You can find deployment templates and code for the rotation function in Azure Samples.
First, set your access policy to grant manage secrets permissions to your user principal:
az keyvault set-policy --upn <email-address-of-user> --name vaultrotation-kv --secret-permissions set delete get list
You can now create a new secret with a storage account access key as its value. You'll also need the storage account resource ID, secret validity period, and key ID to add to the secret so the rotation function can regenerate the key in the storage account.
Determine the storage account resource ID. You can find this value in the id property.
az storage account show -n vaultrotationstorage
List the storage account access keys so you can get the key values:
az storage account keys list -n vaultrotationstorage
Add secret to key vault with validity period for 60 days, storage account resource ID, and for demonstration purpose to trigger rotation immediately set expiration date to tomorrow. Run this command, using your retrieved values for key1Value and storageAccountResourceId:
tomorrowDate=$(date -u -d "+1 day" +"%Y-%m-%dT%H:%M:%SZ")
az keyvault secret set --name storageKey --vault-name vaultrotation-kv --value <key1Value> --tags "CredentialId=key1" "ProviderAddress=<storageAccountResourceId>" "ValidityPeriodDays=60" --expires $tomorrowDate
This secret will trigger SecretNearExpiry event within several minutes. This event will in turn trigger the function to rotate the secret with expiration set to 60 days. In that configuration, 'SecretNearExpiry' event would be triggered every 30 days (30 days before expiry) and rotation function will alternate rotation between key1 and key2.
You can verify that access keys have regenerated by retrieving the storage account key and the Key Vault secret and compare them.
Use this command to get the secret information:
az keyvault secret show --vault-name vaultrotation-kv --name storageKey
Notice that CredentialId is updated to the alternate keyName and that value is regenerated:

Retrieve the access keys to compare the values:
az storage account keys list -n vaultrotationstorage
Notice that value of the key is same as secret in key vault:

You can reuse the same function app to rotate keys for multiple storage accounts.
To add storage account keys to an existing function for rotation, you need:
- The Storage Account Key Operator Service role assigned to function app so it can access storage account access keys.
- An Event Grid event subscription for the SecretNearExpiry event.
Select the Azure template deployment link:
In the Resource group list, select vaultrotation.
In the Storage Account RG box, enter the name of the resource group in which your storage account is located. Keep the default value [resourceGroup().name] if your storage account is already located in the same resource group where you'll deploy the key rotation function.
In the Storage Account Name box, enter the name of the storage account that contains the access keys to rotate.
In the Key Vault RG box, enter the name of resource group in which your key vault is located. Keep the default value [resourceGroup().name] if your key vault already exists in the same resource group where you'll deploy the key rotation function.
In the Key Vault Name box, enter the name of the key vault.
In the Function App Name box, enter the name of the function app.
In the Secret Name box, enter the name of the secret where you'll store access keys.
Select Review + create.
Select Create.

Determine the storage account resource ID. You can find this value in the id property.
az storage account show -n vaultrotationstorage2
List the storage account access keys so you can get the key2 value:
az storage account keys list -n vaultrotationstorage2
Add secret to key vault with validity period for 60 days, storage account resource ID, and for demonstration purpose to trigger rotation immediately set expiration date to tomorrow. Run this command, using your retrieved values for key2Value and storageAccountResourceId:
tomorrowDate=$(date -u -d "+1 day" +"%Y-%m-%dT%H:%M:%SZ")
az keyvault secret set --name storageKey2 --vault-name vaultrotation-kv --value <key2Value> --tags "CredentialId=key2" "ProviderAddress=<storageAccountResourceId>" "ValidityPeriodDays=60" --expires $tomorrowDate
Use this command to get the secret information:
az keyvault secret show --vault-name vaultrotation-kv --name storageKey2
Notice that CredentialId is updated to the alternate keyName and that value is regenerated:

Retrieve the access keys to compare the values:
az storage account keys list -n vaultrotationstorage
Notice that value of the key is same as secret in key vault:

You can disable rotation of a secret simply by deleting the Event Grid subscription for that secret. Use the Azure PowerShell Remove-AzEventGridSubscription cmdlet or Azure CLI az event grid event--subscription delete command.
Rotation functions template for two sets of credentials and several ready to use functions:
Note
These rotation functions are created by a member of the community and not by Microsoft. Community functions are not supported under any Microsoft support program or service, and are made available AS IS without warranty of any kind.
