Getting started with the Azure Multi-Factor Authentication Server

This page covers a new installation of the server and setting it up with on-premises Active Directory. If you already have the MFA server installed and are looking to upgrade, see Upgrade to the latest Azure Multi-Factor Authentication Server. If you're looking for information on installing just the web service, see Deploying the Azure Multi-Factor Authentication Server Mobile App Web Service.
Important
In September 2022, Microsoft announced deprecation of Azure Multi-Factor Authentication Server. Beginning September 30, 2024, Azure Multi-Factor Authentication Server deployments will no longer service multifactor authentication requests, which could cause authentications to fail for your organization. To ensure uninterrupted authentication services and to remain in a supported state, organizations should migrate their users’ authentication data to the cloud-based Microsoft Entra multifactor authentication service by using the latest Migration Utility included in the most recent Azure Multi-Factor Authentication Server update. For more information, see Azure Multi-Factor Authentication Server Migration.
To get started with cloud-based MFA, see Tutorial: Secure user sign-in events with Azure multifactor authentication.
Plan your deployment
Before you download the Azure Multi-Factor Authentication Server, think about what your load and high availability requirements are. Use this information to decide how and where to deploy.
A good guideline for the amount of memory you need is the number of users you expect to authenticate regularly.
| Users | RAM |
|---|---|
| 1-10,000 | 4 GB |
| 10,001-50,000 | 8 GB |
| 50,001-100,000 | 12 GB |
| 100,000-200,001 | 16 GB |
| 200,001+ | 32 GB |
Do you need to set up multiple servers for high availability or load balancing? There are many ways to set up this configuration with Azure Multi-Factor Authentication Server. When you install your first Azure Multi-Factor Authentication Server, it becomes the master. Any other servers become subordinate, and automatically synchronize users and configuration with the master. Then, you can configure one primary server and have the rest act as backup, or you can set up load balancing among all the servers.
When a master Azure Multi-Factor Authentication Server goes offline, the subordinate servers can still process two-step verification requests. However, you can't add new users and existing users can't update their settings until the master is back online or a subordinate gets promoted.
Prepare your environment
Make sure the server that you're using for Azure multifactor authentication meets the following requirements.
| Azure Multi-Factor Authentication Server Requirements | Description |
|---|---|
| Hardware | |
| Software | |
| Permissions | Domain Administrator or Enterprise Administrator account to register with Active Directory |
1If Azure Multi-Factor Authentication Server fails to activate on an Azure virtual machine (VM) that runs Windows Server 2019 or later, try using an earlier version of Windows Server.
Azure Multi-Factor Authentication Server Components
There are three web components that make up Azure Multi-Factor Authentication Server:
- Web Service SDK - Enables communication with the other components and is installed on the Azure Multi-Factor Authentication Server application server
- User portal - An Internet Information Services (IIS) website that allows users to enroll in Microsoft Entra multifactor authentication and maintain their accounts.
- Mobile App Web Service - Enables using a mobile app like the Microsoft Authenticator app for two-step verification.
All three components can be installed on the same server if the server is internet-facing. If breaking up the components, the Web Service SDK is installed on the Microsoft Entra multifactor authentication application server and the User portal and Mobile App Web Service are installed on an internet-facing server.
Azure Multi-Factor Authentication Server firewall requirements
Each MFA server must be able to communicate on port 443 outbound to the following addresses:
If outbound firewalls are restricted on port 443, open the following IP address ranges:
| IP Subnet | Netmask | IP Range |
|---|---|---|
| 134.170.116.0/25 | 255.255.255.128 | 134.170.116.1 – 134.170.116.126 |
| 134.170.165.0/25 | 255.255.255.128 | 134.170.165.1 – 134.170.165.126 |
| 70.37.154.128/25 | 255.255.255.128 | 70.37.154.129 – 70.37.154.254 |
| 52.251.8.48/28 | 255.255.255.240 | 52.251.8.48 - 52.251.8.63 |
| 52.247.73.160/28 | 255.255.255.240 | 52.247.73.160 - 52.247.73.175 |
| 52.159.5.240/28 | 255.255.255.240 | 52.159.5.240 - 52.159.5.255 |
| 52.159.7.16/28 | 255.255.255.240 | 52.159.7.16 - 52.159.7.31 |
| 52.250.84.176/28 | 255.255.255.240 | 52.250.84.176 - 52.250.84.191 |
| 52.250.85.96/28 | 255.255.255.240 | 52.250.85.96 - 52.250.85.111 |
If you aren't using the Event Confirmation feature, and your users aren't using mobile apps to verify from devices on the corporate network, you only need the following ranges:
| IP Subnet | Netmask | IP Range |
|---|---|---|
| 134.170.116.72/29 | 255.255.255.248 | 134.170.116.72 – 134.170.116.79 |
| 134.170.165.72/29 | 255.255.255.248 | 134.170.165.72 – 134.170.165.79 |
| 70.37.154.200/29 | 255.255.255.248 | 70.37.154.201 – 70.37.154.206 |
| 52.251.8.48/28 | 255.255.255.240 | 52.251.8.48 - 52.251.8.63 |
| 52.247.73.160/28 | 255.255.255.240 | 52.247.73.160 - 52.247.73.175 |
| 52.159.5.240/28 | 255.255.255.240 | 52.159.5.240 - 52.159.5.255 |
| 52.159.7.16/28 | 255.255.255.240 | 52.159.7.16 - 52.159.7.31 |
| 52.250.84.176/28 | 255.255.255.240 | 52.250.84.176 - 52.250.84.191 |
| 52.250.85.96/28 | 255.255.255.240 | 52.250.85.96 - 52.250.85.111 |
Download the MFA Server
Tip
Steps in this article might vary slightly based on the portal you start from.
Follow these steps to download the Azure Multi-Factor Authentication Server:
Important
In September 2022, Microsoft announced deprecation of Azure Multi-Factor Authentication Server. Beginning September 30, 2024, Azure Multi-Factor Authentication Server deployments will no longer service multifactor authentication requests, which could cause authentications to fail for your organization. To ensure uninterrupted authentication services and to remain in a supported state, organizations should migrate their users’ authentication data to the cloud-based Microsoft Entra multifactor authentication service by using the latest Migration Utility included in the most recent Azure Multi-Factor Authentication Server update. For more information, see Azure Multi-Factor Authentication Server Migration.
To get started with cloud-based MFA, see Tutorial: Secure user sign-in events with Azure multifactor authentication.
Existing customers that activated MFA Server before July 1, 2019 can download the latest version, future updates, and generate activation credentials as usual. The following steps only work if you were an existing MFA Server customer.
-
Sign in to the Microsoft Entra admin center as a Global Administrator.
Browse to Protection > Multifactor authentication > Server settings.
Select Download and follow the instructions on the download page to save the installer.
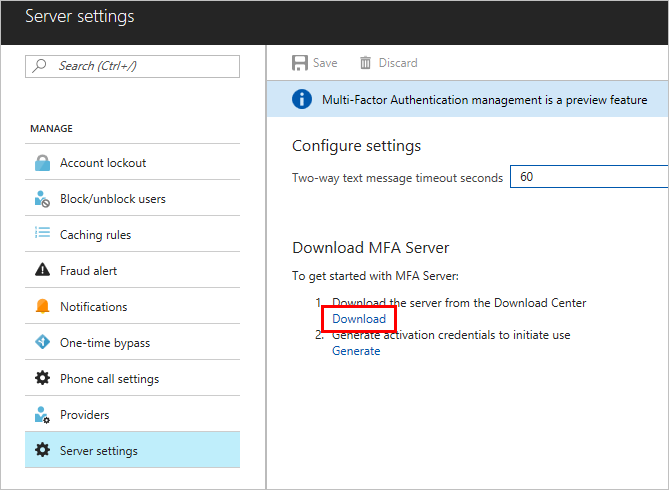
Keep this page open as we'll refer to it after you run the installer.
Install and configure the MFA Server
Now that you have downloaded the server you can install and configure it. Be sure that the server you install it on meets requirements listed in the planning section.
- Double-click the executable.
- On the Select Installation Folder screen, make sure that the folder is correct and click Next. The following libraries are installed:
- When the installation finishes, select Finish. The configuration wizard starts.
- Back on the page that you downloaded the server from, click the Generate Activation Credentials button. Copy this information into the Azure Multi-Factor Authentication Server in the boxes provided and click Activate.
Note
A Global Administrator is needed to manage this feature.
Send users an email
To ease rollout, allow MFA Server to communicate with your users. MFA Server can send an email to inform them that they have been enrolled for two-step verification.
The email you send should be determined by how you configure your users for two-step verification. For example, if you can import phone numbers from the company directory, the email should include the default phone numbers so that users know what to expect. If you don't import phone numbers, or your users are going to use the mobile app, send them an email that directs them to complete their account enrollment. Include a hyperlink to the Azure multifactor authentication User portal in the email.
The content of the email also varies depending on the method of verification that has been set for the user (phone call, SMS, or mobile app). For example, if the user is required to use a PIN when they authenticate, the email tells them what their initial PIN has been set to. Users are required to change their PIN during their first verification.
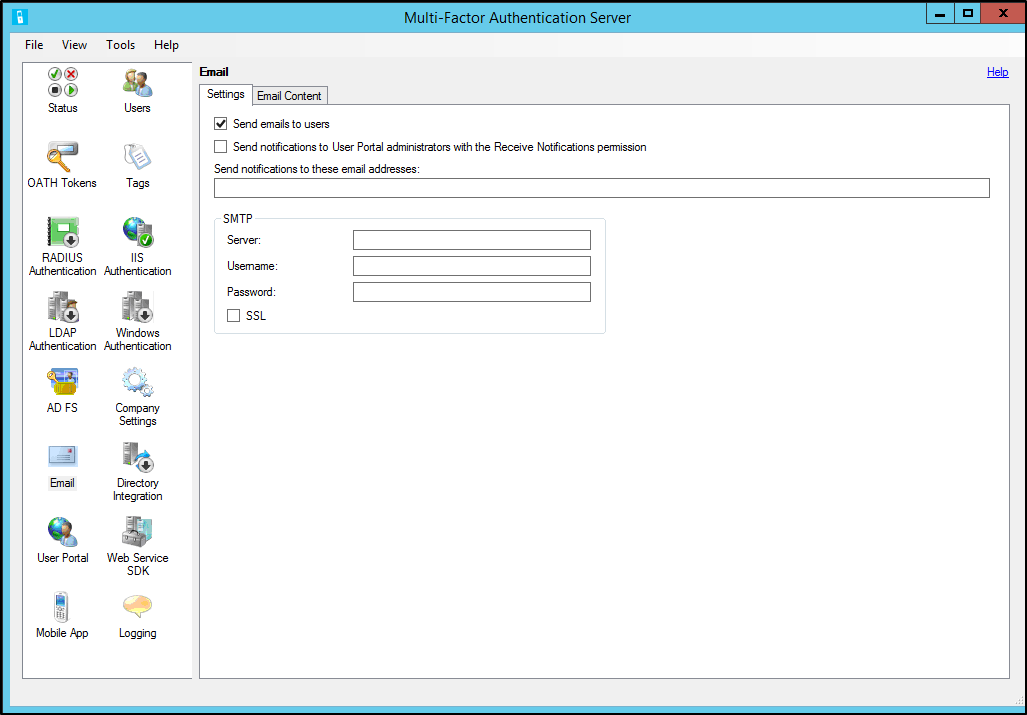
Configure email and email templates
Click the email icon on the left to set up the settings for sending these emails. This page is where you can enter the Simple Mail Transfer Protocol (SMTP) information of your mail server and send email by checking the Send emails to users check box.
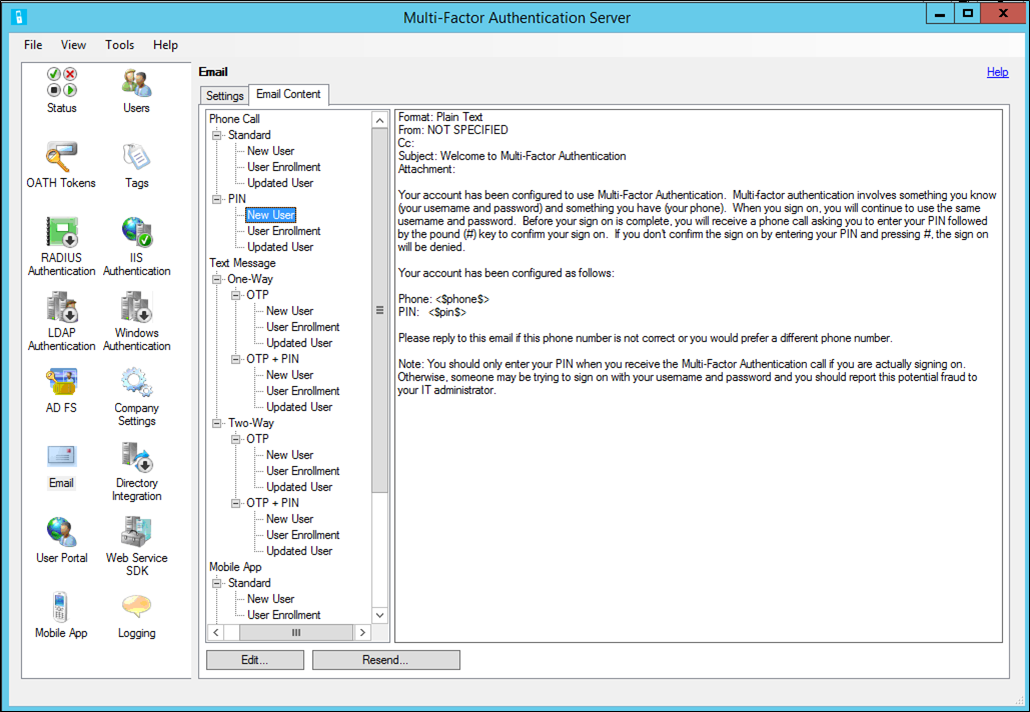
On the Email Content tab, you can see the email templates that are available to choose from. Depending on how you have configured your users to perform two-step verification, choose the template that best suits you.
Import users from Active Directory
Now that the server is installed you want to add users. You can choose to create them manually, import users from Active Directory, or configure automated synchronization with Active Directory.
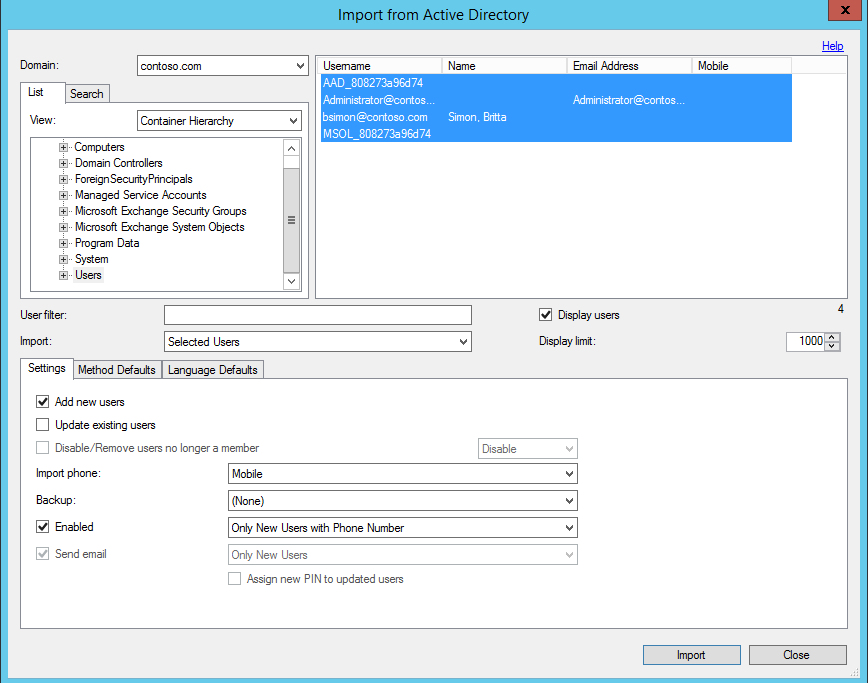
Manual import from Active Directory
In the Azure Multi-Factor Authentication Server, on the left, select Users.
At the bottom, select Import from Active Directory.
Now you can either search for individual users or search the Windows Server Active Directory for organizational units (OUs) with users in them. In this case, we specify the users OU.
Highlight all the users on the right and click Import. You should receive a pop-up telling you that you were successful. Close the import window.
Automated synchronization with Active Directory
- In the Azure Multi-Factor Authentication Server, on the left, select Directory Integration.
- Navigate to the Synchronization tab.
- At the bottom, choose Add
- In the Add Synchronization Item box that appears choose the Domain, OU or security group, Settings, Method Defaults, and Language Defaults for this synchronization task and click Add.
- Check the box labeled Enable synchronization with Active Directory and choose a Synchronization interval between one minute and 24 hours.
How the Azure Multi-Factor Authentication Server handles user data
When you use the Multi-Factor Authentication Server on-premises, a user's data is stored in the on-premises servers. No persistent user data is stored in the cloud. When the user performs a two-step verification, the MFA Server sends data to the Microsoft Entra multifactor authentication cloud service to perform the verification. When these authentication requests are sent to the cloud service, the following fields are sent in the request and logs so that they're available in the customer's authentication/usage reports. Some of the fields are optional so they can be enabled or disabled within the Multi-Factor Authentication Server. The communication from the MFA Server to the MFA cloud service uses SSL/TLS over port 443 outbound. These fields are:
- Unique ID - either username or internal MFA server ID
- First and last name (optional)
- Email address (optional)
- Phone number - when doing a voice call or SMS authentication
- Device token - when doing mobile app authentication
- Authentication mode
- Authentication result
- MFA Server name
- MFA Server IP
- Client IP – if available
In addition to the fields above, the verification result (success/denial) and reason for any denials is also stored with the authentication data and available through the authentication/usage reports.
Important
Starting in March of 2019 the phone call options will not be available to MFA Server users in free/trial Microsoft Entra tenants. SMS messages are not impacted by this change. Phone call will continue to be available to users in paid Microsoft Entra tenants. This change only impacts free/trial Microsoft Entra tenants.
Back up and restore Azure Multi-Factor Authentication Server
Making sure that you have a good backup is an important step to take with any system.
To back up Azure Multi-Factor Authentication Server, ensure that you have a copy of the C:\Program Files\Multi-Factor Authentication Server\Data folder including the PhoneFactor.pfdata file.
In case a restore is needed complete the following steps:
- Reinstall Azure Multi-Factor Authentication Server on a new server.
- Activate the new Azure Multi-Factor Authentication Server.
- Stop the MultiFactorAuth service.
- Overwrite the PhoneFactor.pfdata with the backed-up copy.
- Start the MultiFactorAuth service.
The new server is now up and running with the original backed-up configuration and user data.
Managing the TLS/SSL Protocols and Cipher Suites
Once you have upgraded to or installed MFA Server version 8.x or higher, it's recommended that older and weaker cipher suites be disabled or removed unless required by your organization. Information on how to complete this task can be found in the article Managing SSL/TLS Protocols and Cipher Suites for Active Directory Federation Services (AD FS).
Next steps
- Set up and configure the User portal for user self-service.
- Set up and configure the Azure Multi-Factor Authentication Server with Active Directory Federation Service, RADIUS Authentication, or Lightweight Directory Access Protocol (LDAP) Authentication.
- Set up and configure Remote Desktop Gateway and Azure Multi-Factor Authentication Server using RADIUS.
- Deploy the Azure Multi-Factor Authentication Server Mobile App Web Service.
- Advanced scenarios with Azure multifactor authentication and third-party VPNs.