Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
With the external access feature in Teams, you can allow users in your organization to chat and meet with people outside the organization who are using Microsoft as an identity provider. You can configure external access with:
- Other Microsoft 365 organizations (chat and meetings)
- Teams users not managed by an organization (those users with a Microsoft account) (chat only)
- Skype users (chat only)
Users in your organization can accept or block incoming chats from people outside the organization. For details, see Accept or block people outside your org who send you a chat.
People from outside your organization don't have access to your teams, sites, or other Microsoft 365 resources. If you want them to have access to your teams and channels, see Collaborate with guests in a team and Collaborate with external participants in a shared channel.
Note
Your users can add apps when they host meetings or chats with people outside your organization. They can also use apps shared by external users when they join meetings or chats hosted externally. The data policies of the hosting user's organization, and the data sharing practices of any non-Microsoft apps shared by that user's organization, are applied. Learn more about use of apps by people outside your organization.
Related settings
There are other settings in Teams—including guest access and anonymous access—that affect meetings with people outside your organization. For more information, see Plan for meetings with external participants in Microsoft Teams for more information.
The meeting lobby can control how people outside your organization join meetings. For more information, see Control who can bypass the meeting lobby in Microsoft Teams and Configure the Microsoft Teams meeting lobby for sensitive meetings.
Organization settings and user policies for external access
Each external access option has both an organization setting and user policies. The organization settings apply to your entire organization. User policies determine the users who can use the options you configured at the organization level.
Configure the organization settings to specify which types of external meetings and chat you want to allow. Then configure user policies for the users who should have access to these features. Both the organization settings and user policies are turned on by default.
For a user to use external access, both the organization setting and a user policy must allow it.
Use the procedures on the tabs in this article to configure organization settings and user policies.
In this section, you can configure:
- Meetings and chat with trusted Microsoft 365 organizations
- Chat with external Teams users not managed by an organization
- Chat and calls with Skype users
- Block external users
You can also configure these settings by using PowerShell
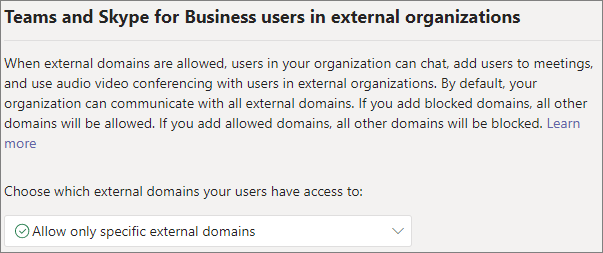
Specify trusted Microsoft 365 organizations
For meetings and chat with other Microsoft 365 organizations, you can specify which domains you want to trust. By default, all external domains are allowed. You can allow or block certain domains in order to define which organizations your organization trusts for external meetings and chat.
In order to chat and meet with people in external domains, the organizations that you trust must also trust your organization, and their users must be enabled for external access. If not, they can't chat with users in your organization and are considered anonymous when joining meetings hosted by your organization. Learn more about meetings with other Microsoft 365 organizations.
You can specify which domains are allowed or which domains are blocked. If you specify blocked domains, all other domains are allowed; if you specify allowed domains, all other domains are blocked. There are four scenarios for configuring trusted organizations:
Allow all external domains: The default setting in Teams, and it lets users in your organization find, call, chat, and set up meetings with people external to your organization in any domain.
In this scenario, your users can communicate with all external domains that are running Teams or Skype for Business so long as the other organization also enabled external access.
Allow only specific external domains: By adding domains to an Allow list, you limit external access to only the allowed domains. Once you set up a list of allowed domains, all other domains are blocked.
Block specific domains: By adding domains to a Block list, you can communicate with all external domains except the domains you blocked. Once you set up a list of blocked domains, all other domains are allowed.
Block all external domains: Prevents users in your organization from finding, calling, chatting, and setting up meetings with people external to your organization in any domain.
Note
People from blocked domains can still join meetings anonymously if anonymous access is allowed. To learn more, see Manage anonymous participant access to Teams meetings.
To allow specific domains, do the following steps:
In the Teams admin center, go to Users > External access.
Next to Teams and Skype for Business users in external organizations, choose Allow only specific external domains.
Select Add external domains.
In the Domain box, type the domain that you want to allow and then select Done.
If you want to allow another domain, enter in another domain.
Select Done.
To block specific domains, do the following steps:
In the Teams admin center, go to Users > External access.
Next to Teams and Skype for Business users in external organizations, choose Block only specific external domains.
Select Block external domains.
In the Domain box, type the domain that you want to allow and then select Done.
If you want to block another domain, enter in another domain.
Select Done.
By default, when you block domains, subdomains aren't blocked. For example, if you block contoso.com, marketing.contoso.com isn't blocked. If you want to block all subdomains, you can use the Set-CsTenantFederationConfiguration PowerShell cmdlet with the -BlockAllSubdomains parameter. For example:
Set-CsTenantFederationConfiguration -BlockAllSubdomains $True
Block federation with Teams trial-only tenants
You can control your organization's external access with Teams trial-only tenants (that don't have any purchased licenses), by using the -ExternalAccessWithTrialTenants setting in PowerShell (at least version 6.4.0 is required).
The default value for this setting is Blocked, but you can override it to Allowed, using the following command:
Set-CsTenantFederationConfiguration -ExternalAccessWithTrialTenants "Allowed"
To block external communication with trial-only tenants, use the following command:
Set-CsTenantFederationConfiguration -ExternalAccessWithTrialTenants "Blocked"
When set to Blocked, users from these trial-only tenants aren't able to search and contact your users via chats, Teams calls, and meetings (using the users' authenticated identities) and your users aren't able to reach users in these trial-only tenants. Users from the trial-only tenant are also removed from existing chats.
Users from trial-only tenants are blocked by default (with no option to override) from external communication with users in other Microsoft 365 cloud environments and with Microsoft Skype for Business server users. Two tenants with only trial subscriptions can federate with each other if the -ExternalAccessWithTrialTenants parameter value is Allowed by both tenants.
Diagnostic Tool
If you're an administrator, you can use the following diagnostic tool to validate if a Teams user can communicate with a Teams user in a trusted organization:
Select Run Tests, which populates the diagnostic in the Microsoft 365 admin center:
In the Run diagnostic pane, enter the Session Initiation Protocol (SIP) Address and the Federated tenant's domain name, and then select Run Tests.
The tests return the best next steps to address any setting or policy configurations that are preventing communication with the external Teams user.
Skype for Business Online
If you want chats and calls to arrive in the user's Skype for Business client, configure your users to be in any mode other than TeamsOnly. For more information, see Understand Microsoft Teams and Skype for Business coexistence and interoperability.
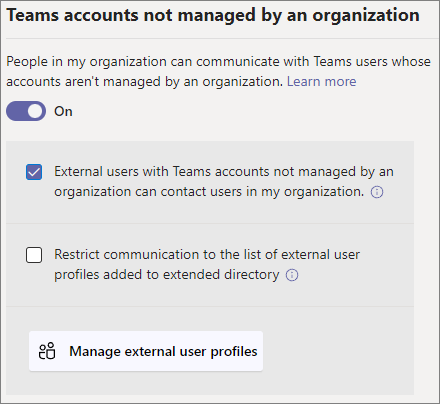
Manage chats and meetings with external Teams users not managed by an organization
You can choose to enable or disable chats and meetings with external unmanaged Teams users (users not managed by an organization, such as Microsoft Teams (free)). If enabled, you can also control if people with unmanaged Teams accounts can start chats and meetings with users in your organization.
Note
Chats and meetings with external unmanaged Teams users isn't available in Microsoft 365 Government Community Cloud (GCC), GCC High, or DOD deployments, or in private cloud environments.
To allow chats and meetings with unmanaged Teams accounts:
- In the Teams admin center, go to Users > External access.
- Turn on the People in my organization can communicate with unmanaged Teams accounts setting.
- If you want to allow external unmanaged Teams users to start the conversation, select the External users with Teams accounts not managed by an organization can contact users in my organization checkbox.
- Select Save.
If External users with Teams accounts not managed by an organization can contact users in my organization is turned off, unmanaged Teams users can't search by email address to find users in your organization. Users in your organization must initiate all communications with unmanaged Teams users.
To prevent chat with unmanaged Teams accounts:
- In the Teams admin center, go to Users > External access.
- Turn off the People in my organization can communicate with unmanaged Teams accounts setting.
- Select Save.
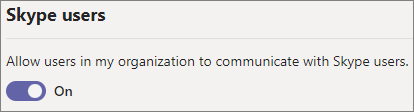
Manage chat and calls with Skype users
Follow these steps to let Teams users in your organization chat with and call Skype users. Teams users can then search for and start a one-on-one text-only conversation or an audio/video call with Skype users and vice versa.
Meetings aren't supported with Skype users. If invited to a meeting, they're considered anonymous when joining.
Note
External communication with Skype users isn't available in GCC, GCC High, or DOD deployments, or in private cloud environments.
To configure chat and calls with Skype users:
In the Teams admin center, go to Users > External access.
Turn the Allow users in my organization to communicate with Skype users setting on or off.
Select Save.
To learn more about the ways that Teams users and Skype users can communicate, including limitations that apply, see Teams and Skype interoperability.
Block external users
You can block specific external users from collaborating with your organization. If a user is added to the blocklist, your organization can't have 1:1 and group chats with these users. If chats already exist before a user is added to the blocklist, the blocked user is removed from the chat. This feature is turned off by default.
To enable and configure blocked users list, do the following steps:
In the Teams admin center, go to Users > External access.
Turn Block specific users from communicating with people in my organization setting on.
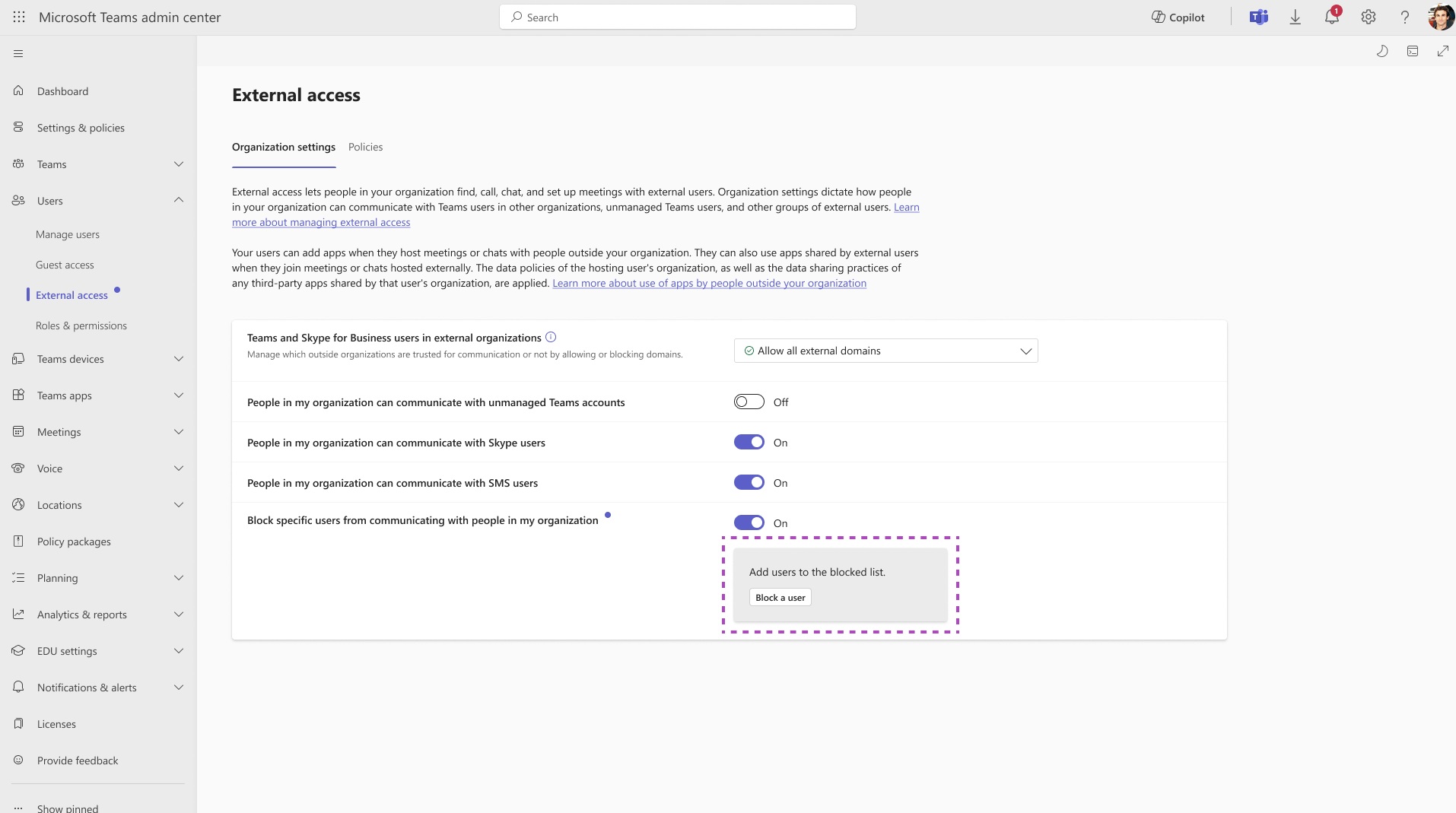
Add users to the blocklist by selecting the Block a user button.
In the User box, type the email address of the user you want to block and then select the Apply button. Select the Cancel button to leave without taking any action. You must type in a valid individual email or a messaging resource identifier (MRI).
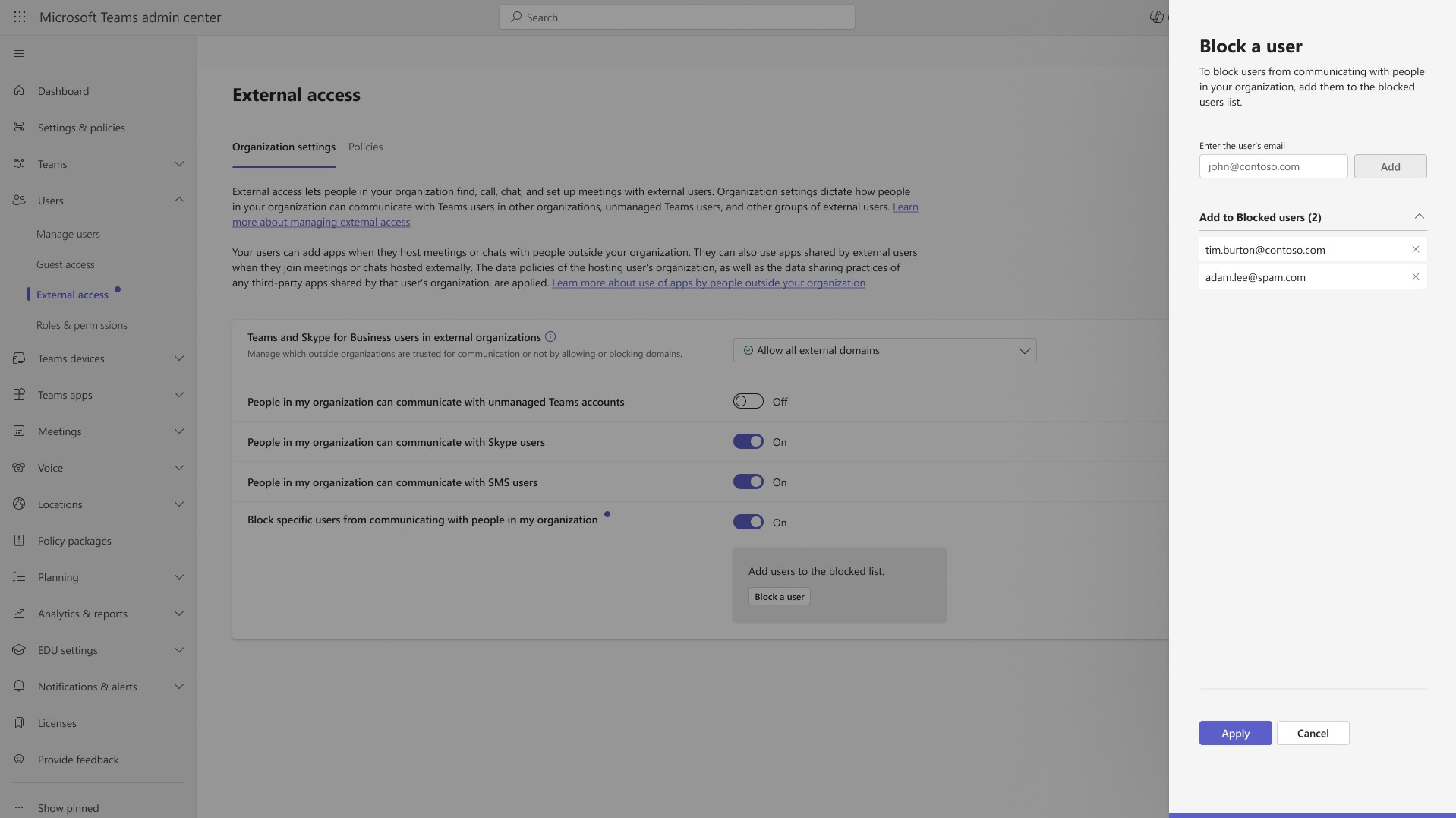
If you want to block another user, select Add users and then the Apply button. A maximum of 200 users can be entered in this list.
Administrators can configure blocked user settings using Set-CsTeamsExternalAccessConfiguration PowerShell cmdlet.
Note
Enabling the Blocked user functionality might generate two audit events - one for the admin setting, and another for any related roster changes that occur when users are blocked.
Allow my security team to manage blocked domains
Note
This feature is currently in Public Preview and corresponds to Message center post MC1133508.
Microsoft Teams Administrators can let Security Administrators manage blocked external domains in the Microsoft Defender for Office security portal. This feature utilizes the Tenant Allow/Block List functionality specifically for Teams. When this feature is on, Security Administrators can view, add, remove blocked external domains. These actions are performed in Microsoft Defender portal and block incoming communications (including chats, meetings, and calls) from the specified domains.
To turn on this feature, do the following steps:
Teams admin center:
- Sign in to the Teams Admin Center at https://admin.teams.microsoft.com.
- In the left navigation, select Users > External Access.
- Turn on Allow my security team to manage blocked domains.
Microsoft Defender portal:
- In the Microsoft Defender portal at https://security.microsoft.com, go to Email & collaboration > Policies & rules > Threat Policies > Rules section > Tenant Allow/Block Lists.
- Select the Teams domains tab.
- Add external domains as needed to block communications.
Prerequisites:
- Microsoft Defender for Office 265 Plan 1 or Plan 2.
- Teams external access tenant setting configured as one of the following options:
- Block only specific external domains
- Allow all external domains
The blocked domain lists in both the Teams admin center and Microsoft Defender security portal are the same.
Configure organization settings by using PowerShell
Trusted organizations can be configured by using the Set-CsTenantFederationConfiguration cmdlet.
The following table shows the cmdlet parameters used for configuring trusted organizations.
| Configuration | Parameter |
|---|---|
| Allow or prevent meetings and chat with other Teams organizations and Skype for Business | -AllowFederatedUsers |
| Specify allowed domains | -AllowedDomains |
| Specify blocked domains | -BlockedDomains |
| Block subdomains | -BlockAllSubdomains |
Chat with Teams users not managed by an organization and Skype users can be configured by using the Set-CsTenantFederationConfiguration cmdlet.
The following table shows the cmdlet parameters used for configuring chat with Skype and unmanaged Teams users.
| Configuration | Parameter |
|---|---|
| Allow or prevent chat with Teams users that aren't managed by an organization | -AllowTeamsConsumer |
| Allow or prevent Teams users not managed by an organization starting conversations | -AllowTeamsConsumerInbound |
| Allow or prevent chat with Skype users | -AllowPublicUsers |
Before you can run these cmdlets, you must be connected to Microsoft Teams PowerShell. For more information, see Manage Teams with Microsoft Teams PowerShell.