Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Restricted site access control helps prevent oversharing by designating access of SharePoint sites and its content to users in a specific group. Users not in the specified group can't access the site or its content, even if they had prior permissions or a shared link. You can apply this policy on Microsoft 365 group-connected, Teams-connected, and nongroup connected sites by using Microsoft 365 groups or Microsoft Entra security groups.
Site access restriction policies take effect when a user attempts to open a site or access a file. Users with direct permissions to the file can still view files in search results. However, they can't access the files if they're not part of the specified group.
Restricting site access through group membership can minimize the risk of oversharing content. For insights into data sharing, see Data access governance reports.
What do you need to restrict site access?
See Prerequisites for SharePoint Advanced Management.
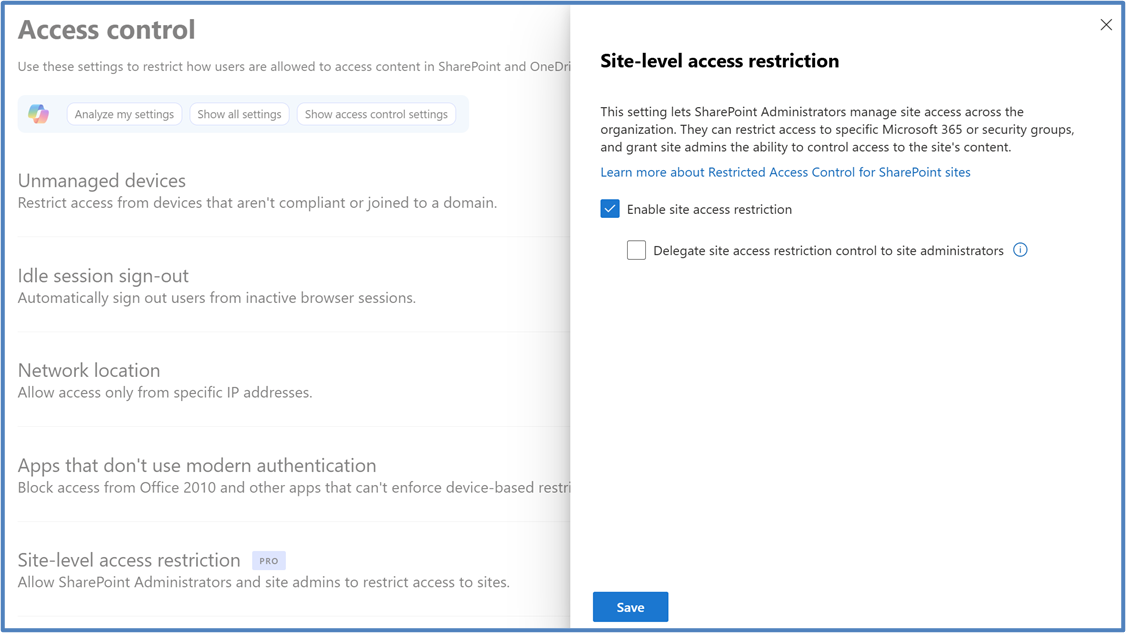
Enable site-level access restriction for your organization
You must enable site-level access restriction for your organization before you can configure it for individual sites. You can also delegate site access restriction control to all the site admins of your organization.
To enable site-level access restriction for your organization in the SharePoint admin center, follow these steps:
Expand Policies and select Access control.
Select Site-level access restriction.
Select Allow access restriction and then select Save.
To enable site-level access restriction for your organization using PowerShell, run the following command:
Set-SPOTenant -EnableRestrictedAccessControl $true
It might take up to one hour for the command to take effect.
Delegate Management of Restricted Access Control to Site Admins
As a SharePoint administrator, you can also delegate management of Restricted Access Control to site administrators. If they update the policy, they need to provide appropriate justification on why the policy is being updated.
By default, the delegation is turned off. If you decide to enable it, run the following command:
Set-SPOTenant -DelegateRestrictedAccessControlManagement $true
Once the Restricted Access Control is delegated to all the site admins, they can manage the policy.
Check status of delegate management of restricted access control to site admins
To check the delegation status, run the following command:
Get-SPOTenant | Select-Object DelegateRestrictedAccessControlManagement
Note
For Microsoft 365 Multi-Geo users, run this command separately for each desired geo-location.
Restrict access to all SharePoint sites using Microsoft 365 group or Microsoft Entra security groups
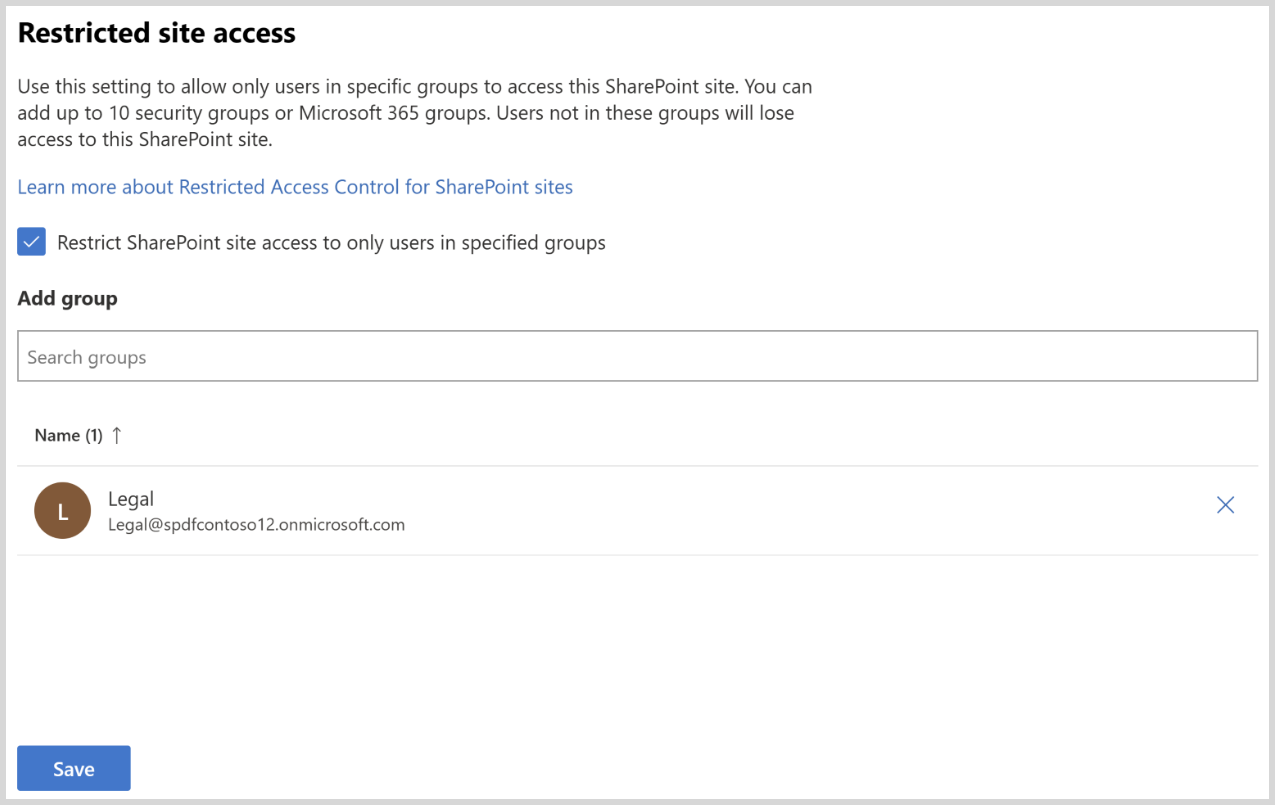
You can restrict access to a SharePoint site by specifying Microsoft Entra security groups or Microsoft 365 groups as the Restricted Access Control group. The control group should include the users who are allowed access to the site and its content.
For a site, you can configure up to 10 Microsoft Entra security groups or Microsoft 365 groups. Once you apply the policy, users in the specified group who have access permission to the content are granted access.
Important
Adding people to the Restricted Access Control group (Microsoft Entra security group or Microsoft 365 group) doesn't automatically give the users access permission to the site or the content. For a user to access the content protected by this policy, the user needs both the site or content access permission and be a member of the Restricted Access Control group.
Note
You can also use dynamic security groups as a Restricted Access Control group if you want to base group membership on user properties.
Manage site access for a site
To manage site access for a site, follow these steps:
In SharePoint admin center, expand Sites and select Active sites.
Select the site you want to manage. The site details panel appears.
In the Settings tab, select Edit in the Restricted site access section.
Select the Restrict SharePoint site access to only users in specified groups check box.
Add or remove your security groups or Microsoft 365 groups and select Save.
To apply site access restriction to the site, you must add at least one group to the site access restriction policy.
For a group connected site, the Microsoft 365 group connected to the site is the default Restricted Access Control group. You can choose to keep this group and add more Microsoft 365 or Microsoft Entra Security groups as Restricted Access Control group.
Note
There's a tag labeled as Default group marked against the Microsoft 365 group connected to the site as shown in the previous image.
To manage site access restriction for a SharePoint site by using PowerShell, use the following commands:
| Action | PowerShell command |
|---|---|
| Enable site access restriction | Set-SPOSite -Identity <siteurl> -RestrictedAccessControl $true |
| Add group | Set-SPOSite -Identity <siteurl> -AddRestrictedAccessControlGroups <comma separated group GUIDS> |
| Edit group | Set-SPOSite -Identity <siteurl> -RestrictedAccessControlGroups <comma separated group GUIDS> |
| View group | Get-SPOSite -Identity <siteurl> | Select RestrictedAccessControl, RestrictedAccessControlGroups |
| Remove group | Set-SPOSite -Identity <siteurl> -RemoveRestrictedAccessControlGroups <comma separated group GUIDS> |
| Reset site access restriction | Set-SPOSite -Identity <siteurl> -ClearRestrictedAccessControl |
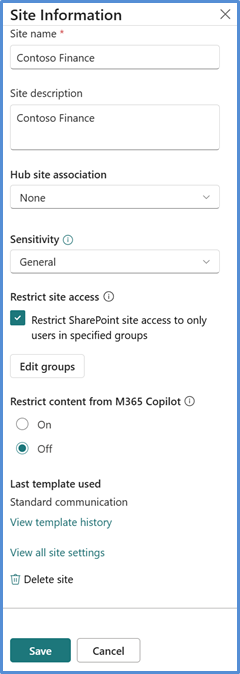
Site admin experience
After you delegate the site access restriction control to site admins, they can configure the site access restriction setting at the Site Information panel.
To restrict access to a SharePoint site:
- Limit who can access a site by using Microsoft Entra security groups or Microsoft 365 groups.
- Add the groups that contain the users who should have access.
- Add up to 10 groups for each site.
- When you save the site access restriction setting configuration, only users in those groups and users who already have permission to the content can access the site.
- Provide justification whenever you update the site access restriction setting.
Site owner experience
After you apply the policy to the site, the Site access panel displays the policy status and all configured control groups for site owners, in addition to the Site Information and Permissions panels.
Shared and private channel sites
Shared and private channel sites are separate from the Microsoft 365 group-connected site that standard channels use. Because shared and private channel sites aren't connected to the Microsoft 365 group, site access restriction policies applied to the team don't affect them. You must enable site access restriction for each shared or private channel site separately as nongroup connected sites.
For shared channel sites, only internal users in the resource tenant are subject to site access restriction. External channel participants are excluded from site access restriction policy and only evaluated per the site's existing site permissions.
Important
Adding people to the security group or Microsoft 365 group doesn't give users access to the channel in Teams. Add or remove the same users of the Teams channel in Teams and the security group or Microsoft 365 group, so users have access to both Teams and SharePoint sites.
Auditing
The Microsoft Purview portal provides audit events that help you monitor site access restriction activities. The system logs audit events for the following activities:
- Applying site access restriction for a site
- Removing site access restriction for a site
- Changing site access restriction groups for a site
- Site admin's justification for updating site access restriction
Reporting
Restricted site access policy insights
As an IT administrator, you can view the following reports to gain more insight about SharePoint sites protected with restricted site access policy:
- Sites protected by restricted site access policy (RACProtectedSites)
- Details of access denials due to restricted site access policy (ActionsBlockedByPolicy)
Reports are currently unavailable for Gallatin, even if you have the required licenses.
Note
It can take a few hours to generate each report.
Sites protected by restricted site access policy report
Run the following commands in SharePoint PowerShell to generate, view, and download the reports:
| Action | PowerShell command | Description |
|---|---|---|
| Generate report | Start-SPORestrictedAccessForSitesInsights -RACProtectedSites |
Generates a list of sites protected by restricted site access policy |
| View report | Get-SPORestrictedAccessForSitesInsights -RACProtectedSites -ReportId <Report GUID> |
The report shows the top 100 sites with the highest page views that are protected by the policy. |
| Download report | Get-SPORestrictedAccessForSitesInsights -RACProtectedSites -ReportId <Report GUID> -Action Download |
Run this command as an administrator. The downloaded report is located on the path where the command was run. |
| Percentage of site protected with restricted site access report | Get-SPORestrictedAccessForSitesInsights -RACProtectedSites -ReportId <Report GUID> -InsightsSummary |
This report shows the percentage of sites that are protected by the policy out of the total number of sites |
Access denials due to restricted site access policy report
Run the following commands to create, fetch, and view report for access denials due to restricted site access reports:
| Action | PowerShell command | Description |
|---|---|---|
| Create access denials report | Start-SPORestrictedAccessForSitesInsights -ActionsBlockedByPolicy |
Creates a new report for fetching access denial details |
| Fetch access denials report status | Get-SPORestrictedAccessForSitesInsights -ActionsBlockedByPolicy |
Fetches the status of the generated report. |
| Latest access denials in the past 28 days | Get-SPORestrictedAccessForSitesInsights -ActionsBlockedByPolicy -ReportId <Report ID> -Content AllDenials |
Gets a list of the most recent 100 access denials that occurred in the past 28 days |
| View list of top users who were denied access | Get-SPORestrictedAccessForSitesInsights -ActionsBlockedByPolicy -ReportId <Report ID> -Content TopUsers |
Gets a list of the top 100 users who received the most access denials |
| View list of top sites that received the most access denials | Get-SPORestrictedAccessForSitesInsights -ActionsBlockedByPolicy -ReportId <Report ID> -Content TopSites |
Gets a list of the top 100 sites that had the most access denials |
| Distribution of access denials across different types of sites | Get-SPORestrictedAccessForSitesInsights -ActionsBlockedByPolicy -ReportId <Report ID> -Content SiteDistribution |
Shows the distribution of access denials across different types of sites |
Note
To view up to 10,000 denials, you must download the reports. Run the download command as an administrator. The downloaded reports are located on the path where you run the command.
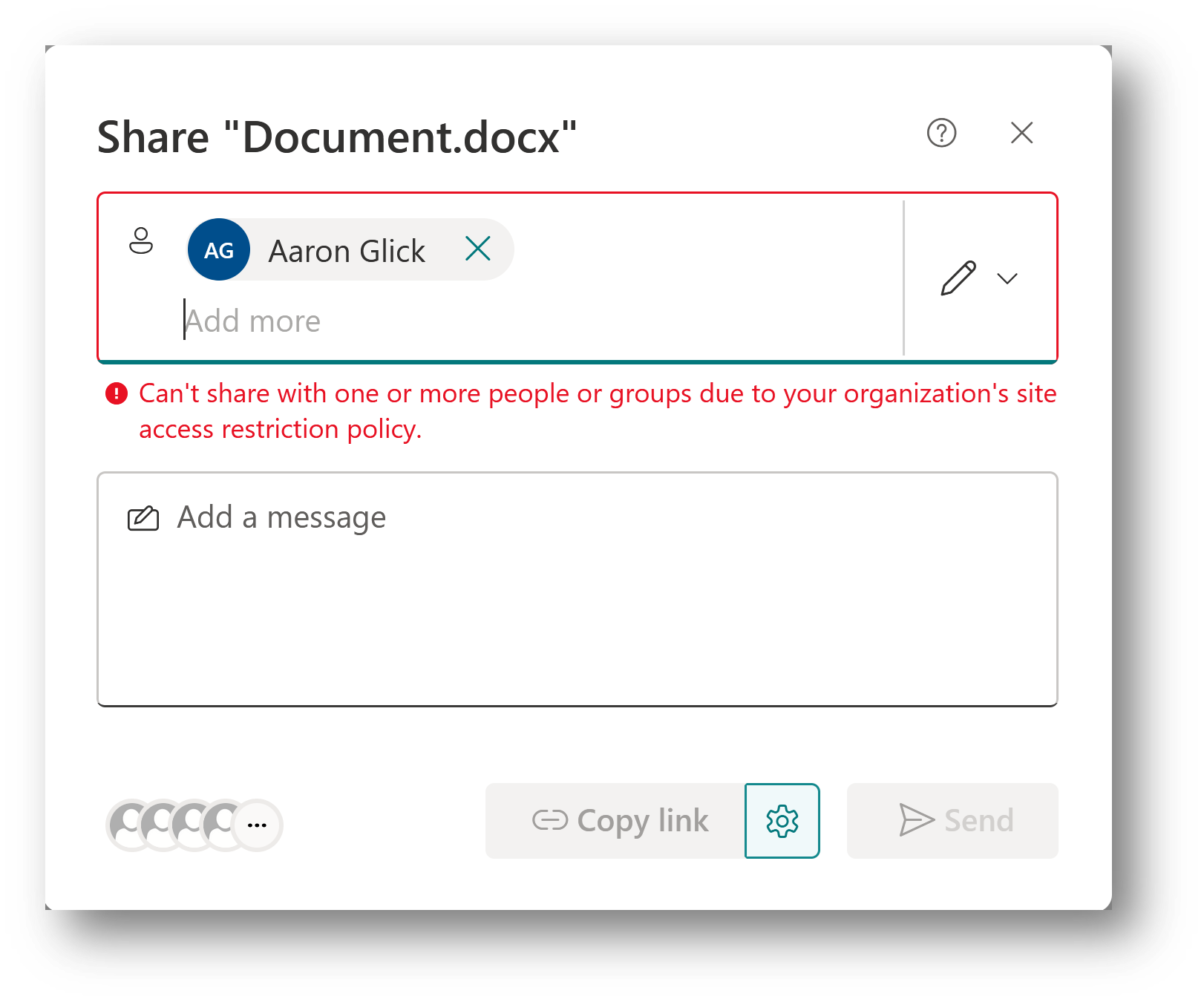
Sharing of site and content with users outside of Restricted Access Control Groups (opt-in capability)
By default, sharing SharePoint sites and their content doesn't follow the restricted site access policy. The SharePoint administrator can choose to restrict sharing of a site and its content with users who aren't members of the Restricted Access Control group.
To restrict the sharing capability to users outside of the Restricted Access Control group, run the following PowerShell command in SharePoint Online Management Shell as an administrator:
Set-SPOTenant -AllowSharingOutsideRestrictedAccessControlGroups $false
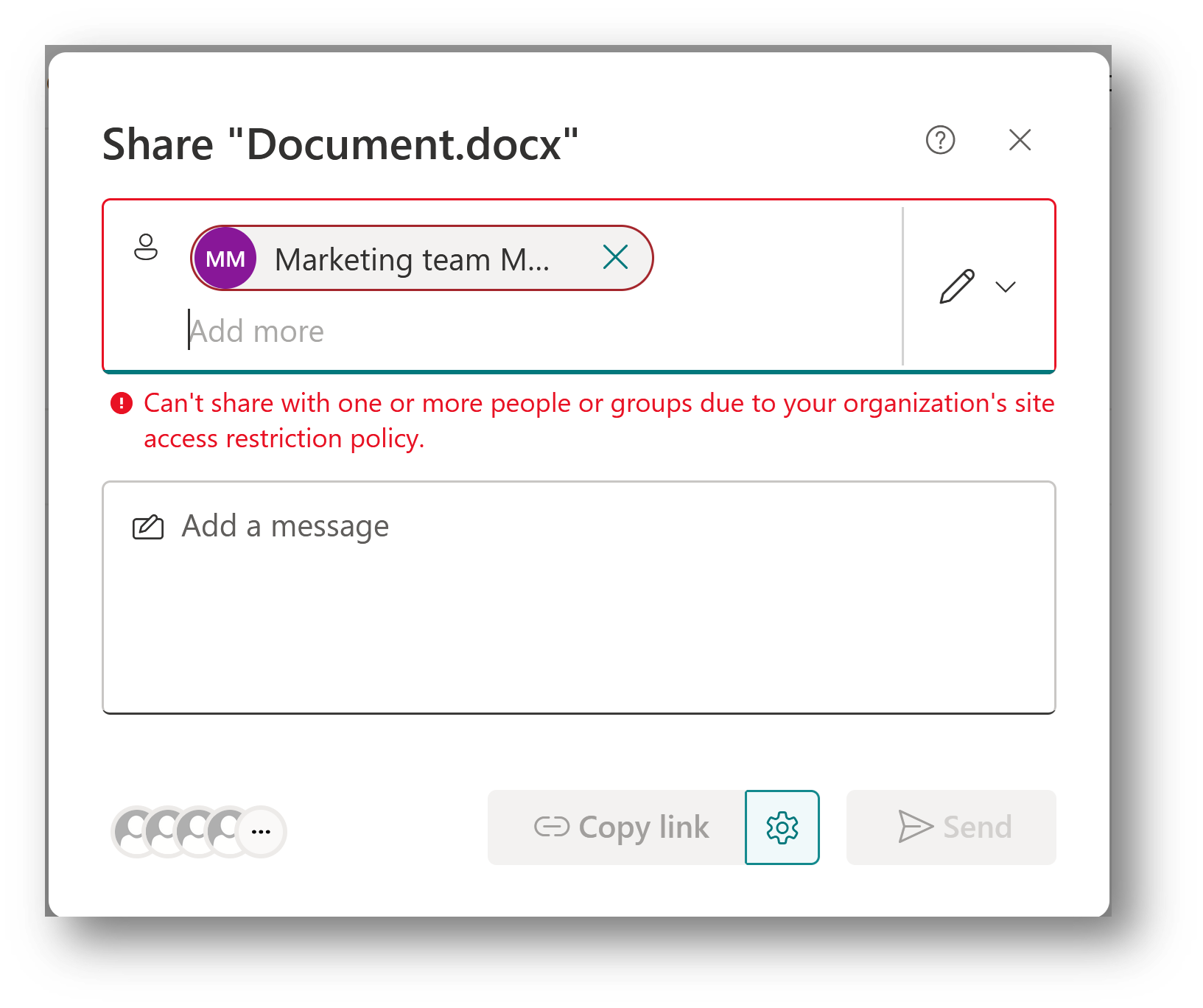
Sharing with users
When you apply the sharing restriction, it blocks sharing for users who aren't members of the Restricted Access Control group.
Sharing with groups
Sharing is allowed with Microsoft Entra Security or Microsoft 365 groups that are part of the Restricted Access Control groups list. Sharing isn't allowed with all other groups, including Everyone except external users or SharePoint groups.
Note
Sharing of a site and its content is now allowed for the nested security groups that are part of the Restricted Access Control groups.
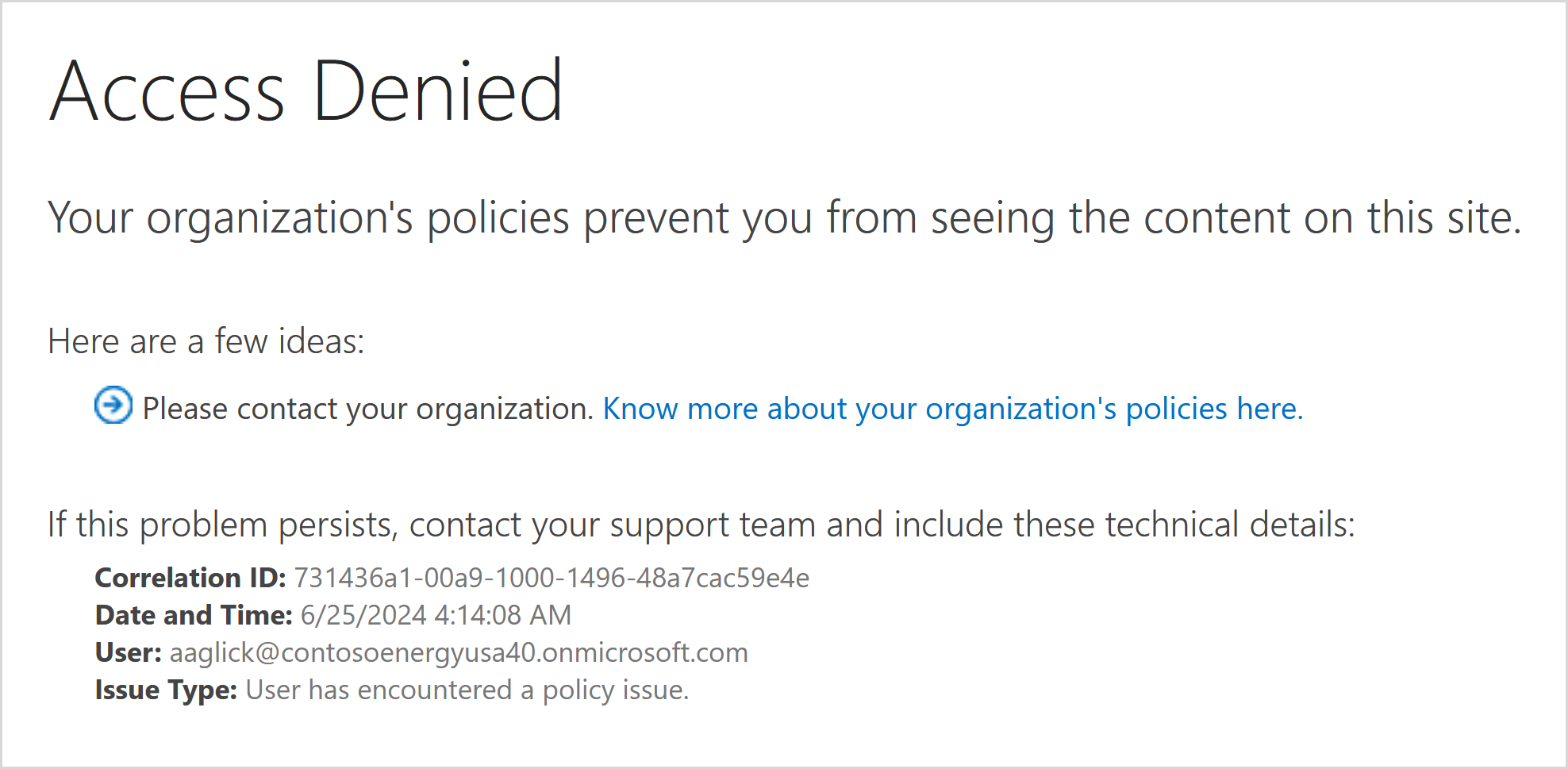
Configure the Learn more link for access denial error page (opt-in capability)
Configure the Learn more link to inform users who are denied access to a SharePoint site due to the restricted site access control policy. By customizing this error link, you can provide more information and guidance to your users.
Note
The Learn more link is a tenant-level setting that applies to all sites with the Restricted Access Control policy enabled.
To configure the link, run the following command in SharePoint PowerShell:
Set-SPOTenant -RestrictedAccessControlForSitesErrorHelpLink "<Learn more URL>"
To fetch the value of the link, run the following command:
Get-SPOTenant | select RestrictedAccessControlForSitesErrorHelpLink
The configured Learn more link launches when the user selects the Know more about your organization's policies here link.