@Anonymous , Thanks for posting in Q&A.
For your questions, here are my answers for your reference:
Q1: What will happen to my existing policies if I configure the "Security Baseline for Windows 10 and later" and "Microsoft Defender for Endpoint Baseline"?
A1: In General, many of the settings you can configure for devices can be managed by different features in Intune. When you use multiple methods or instances of the same method to configure the same setting, ensure your different methods either agree or aren't deployed to the same devices, otherwise they will conflict. Say in other words, if you use device configuration, please don't use endpoint security.
Here is a link with some details for your reference:
https://learn.microsoft.com/en-us/mem/intune/protect/endpoint-security#avoid-policy-conflicts
Q2: From a management perspective, should I prefer Intune to determine this baseline or the Endpoint security?
A2: In fact, Intune is a cloud-based endpoint management solution. It manages user access and simplifies app and device management across your many devices, including mobile devices, desktop computers, and virtual endpoints, and endpoint security is just one feature available in Intune. Endpoint security policies are intended to assist you in focusing on the security of your devices while also reducing risk. If you want to deploy such policies in a batch, Intune is a good option.
Q3: If at a certain point the Cxo’s want to move to another AV/protection suite, should I leave the baselines at Intune?
A3: Based as I know, currently, the integrated AV is Microsoft Defender. If you want to move to another AV. You can let it there as not configured.
Q4: Do I need to see Endpoint security as a standalone defender version, or does it link up with the other Defender programs?
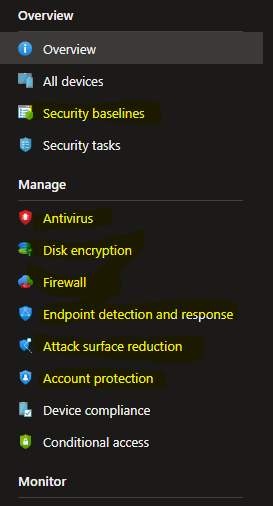
A4: In fact, the Endpoint security node in Intune is used to configure device security and to manage security tasks for devices when those devices are at risk, it is not a defender version. You can use endpoint security to do the following:
• Review the status of all your managed devices.
• Deploy security baselines that establish best practice security configurations for devices.
• Manage security configurations on devices through tightly focused policies.
• Establish device and user requirements through compliance policy.
• Integrate Intune with your Microsoft Defender for Endpoint team.
For more information about Endpoint Security, you can refer to this link:
https://learn.microsoft.com/en-us/mem/intune/protect/endpoint-security
Hope the above information can help you.
If the answer is helpful, please click "Accept Answer" and kindly upvote it. If you have extra questions about this answer, please click "Comment".
Note: Please follow the steps in our documentation to enable e-mail notifications if you want to receive the related email notification for this thread.