
Did you also give the AADConnect account:
Replicate Directory Changes
Replicate Directory Changes All
at the root for the Password Hash Sync requirement?
If you add the account to Domain Admins as a test, I assume it works yes?
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
Hello,
We currently installed Azure AD Sync connect and everything seems to be synching well except for a 8344 "Insufficient access rights to perform the operation". We did a custom install where it only syncs a specific OU / group.
-We are doing only PW Hash Synchronization
-Users are getting their pws synced for the few that we are doing, pw changes, take effect too,
-During AD Forest account we selected create a new ad account
-We used users are represented only once across all directories
-Let azure manage the source anchor was selected
Again all the passwords are synching good but when I open Synchronization service manager I get the above error. When I click on the user error I see it has a change under "ms-ds-consistencyGuid" which I believe is the change it is having issue writing back to our active directory. Is there an easy way to fix this?
EDIT:
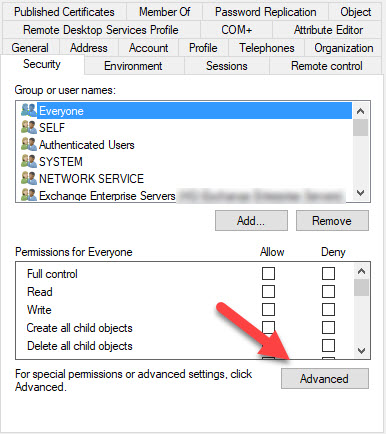
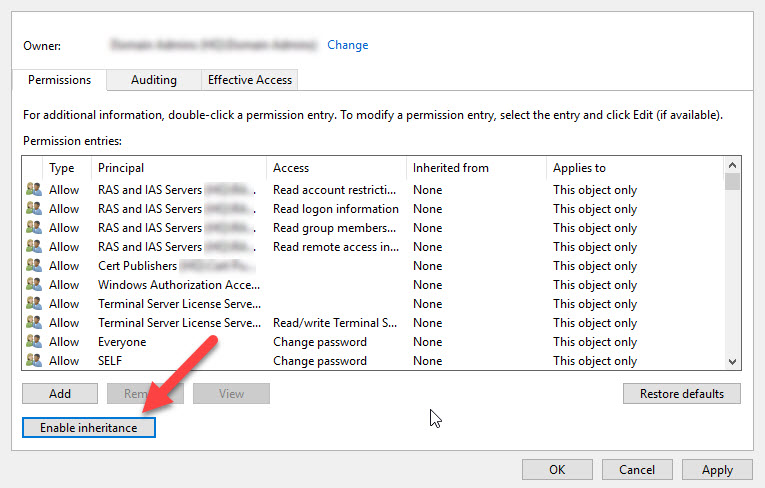
Finally it is fixed! After I started checking the security permissions for the root domain I noticed the OU for our users didn't have the security permissions for the MSOL service account at all.
The users OU had inheritance disabled. After I enabled inheritance for that particular OU, the permissions instantly appeared for the service account and the problem was fixed.


Did you also give the AADConnect account:
Replicate Directory Changes
Replicate Directory Changes All
at the root for the Password Hash Sync requirement?
If you add the account to Domain Admins as a test, I assume it works yes?

Check the security inheritance on the user.
If that isnt the issue did you enable writeback permission if you enabled SSPR?
Did you enable any other options?
Note that group filtering is not supported except for pilot testing.
Finally it is fixed! After I started checking the security permissions for the root domain I noticed the OU for our users didn't have the MSOL at all.
The users OU had inheritance disabled. After I enabled inheritance for that particular OU the problem is fixed.
Dear all,
We have created a new article in regards to this topic.
For more details, please see below:
I hope you will find this useful.
Kind regards,
Carmen

I would use the built-in functionality in AADConnect Powershell:
Set-ADSyncMsDsConsistencyGuidPermissions -ADConnectorAccountName <String> -ADConnectorAccountDomain <String> [-SkipAdminSdHolders]
[<CommonParameters>]