Oh also, the AKS load balancer that shows up has two public IPs on it, so I don't know how to point the gateway to the AKS load balancer at all really.
TLS end to end with Azure Kubernetes services and an application gateway
We are having some major problems getting TLS end to end with AKS. Here is how things are supposed to go:
Internet --> Application Gateway (WAF enabled) --> AKS load balancer --> pods
The problem is that one of the tools we use in AKS is istio. When traffic reaches istio, it is unencrypted. Further, we can't get the traffic to flow through the gateway to AKS, we have to take the App Gateway out of the picture. If we do this, istio receives encrypted traffic. Now I have a set of ideas which may be correct, but I was hoping the community here could give a hand.
2 answers
Sort by: Most helpful
-
-
 prmanhas-MSFT 17,901 Reputation points Microsoft Employee
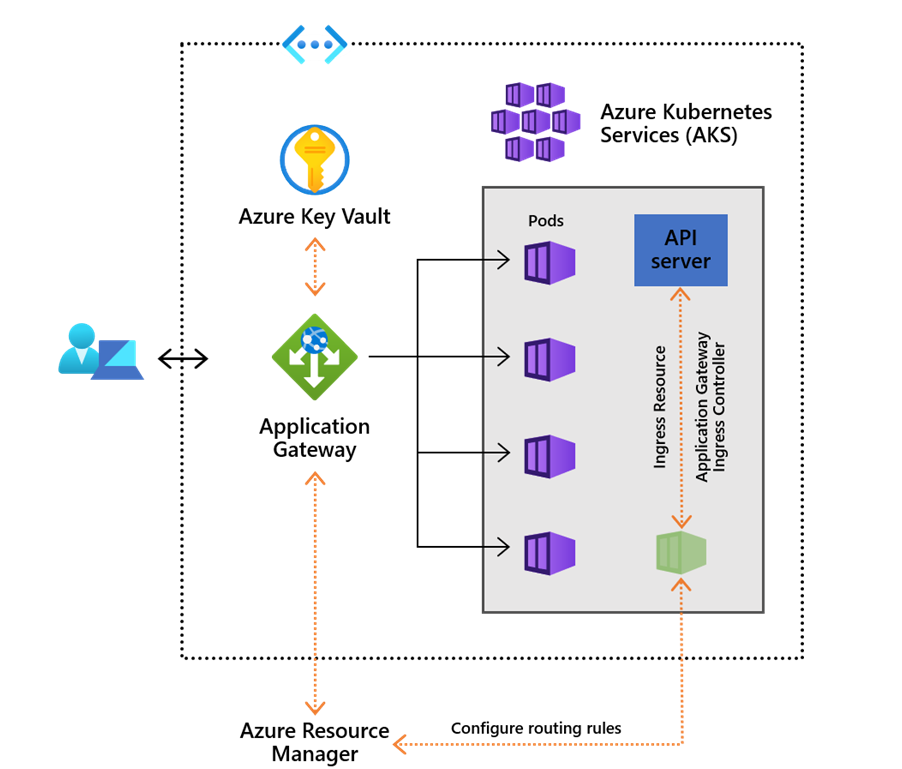
prmanhas-MSFT 17,901 Reputation points Microsoft Employee2020-10-21T07:55:22.34+00:00 @Duane Wolford Application Gateway Ingress Controller runs in its own pod on the customer’s AKS. Ingress Controller monitors a subset of Kubernetes’ resources for changes. The state of the AKS cluster is translated to Application Gateway specific configuration and applied to the Azure Resource Manager. The continuous re-configuration of Application Gateway ensures uninterrupted flow of traffic to AKS’ services. The diagram below illustrates the flow of state and configuration changes from the Kubernetes API, via Application Gateway Ingress Controller, to Resource Manager and then Application Gateway:
Hope it helps!!!
Do let me know in case of any more queries.
If the suggested response helped you resolve your issue, do click on "Mark as Answer" and "Up-Vote" for the answer that helped you for benefit of the community.