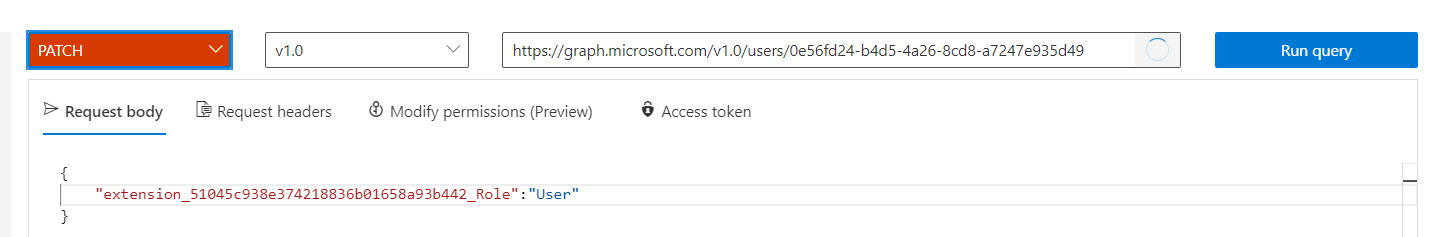
Regarding Microsoft graph-Explorer:
I have several B2C tenants. How do I tell graph-explorer which B2C tenant I want to use?
When I run my 4-2-B2C, I can log in with my gmail account. However, when I log in via the graph-explorer, it does not accept this account...
When I log into graph-explorer with my hotmail account and get a list of users, it does not see any of the other accounts that I can use to log into 4-2-B2C with. (I only see one account and that is the hotmail account). This is probably because I don't know how to tell the Microsoft graph explorer the tenant that 4-2-B2C is using.
The same is true with the Graph API: how do I specify the tenant?