A couple things to look at with your scenario as we're also going through the transition from all our computers being joined to an on premise AD to strictly AAD joined or some that are hybrid joined.
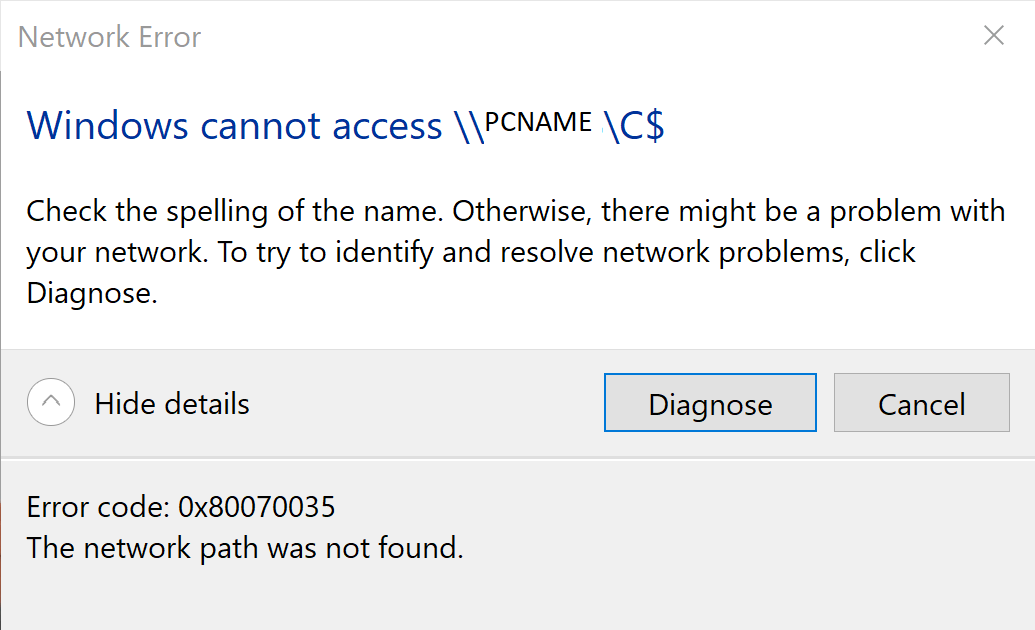
First, if you were disabling the Windows firewall on your on premise joined computers via AD group policy, specifically when they were on the domain's network, this isn't the case with AAD joined computers. Even though the AAD joined computers are sitting on the same network as your on premise domain, they are not pulling those same AD group policies, at least not without some further configuration. So access to the admin share on that PC is probably being blocked by the Windows firewall.
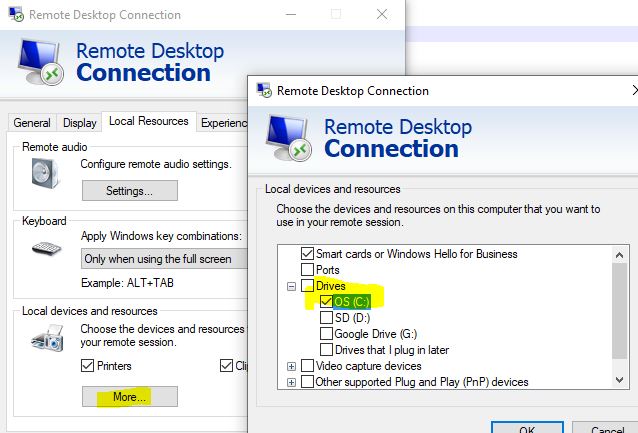
Second, if you get past that network error, the next error you'll probably run into is authenticating to the AAD computer if you're trying to access it from a hybrid joined or other non-AAD joined device. Typically when you try and access one AD joined computer's admin sharer (c$) from another AD joined computer, Windows authentication takes place behind the scenes seamlessly. But in this case, the AAD computer won't be able to authenticate due to it not recognizing the username format "username@keyman .com" like a typical AD joined computer would. So instead you'll need to authenticate using the format "azuread\username@keyman .com" (assuming you have everything setup to sync between your on premise AD and AAD via the Azure AD connect client.)
Hope this help you out. (I found this post as we are trying to copy files to AAD joined computers when they're not on our network, rather sitting on the internet at home or at a coffee shop. We need to replace a config. file and are trying find a way to push that out to all our AAD computers when they don't have access to a local file share within our datacenter. Your situation is a bit easier since they reside on your network.)