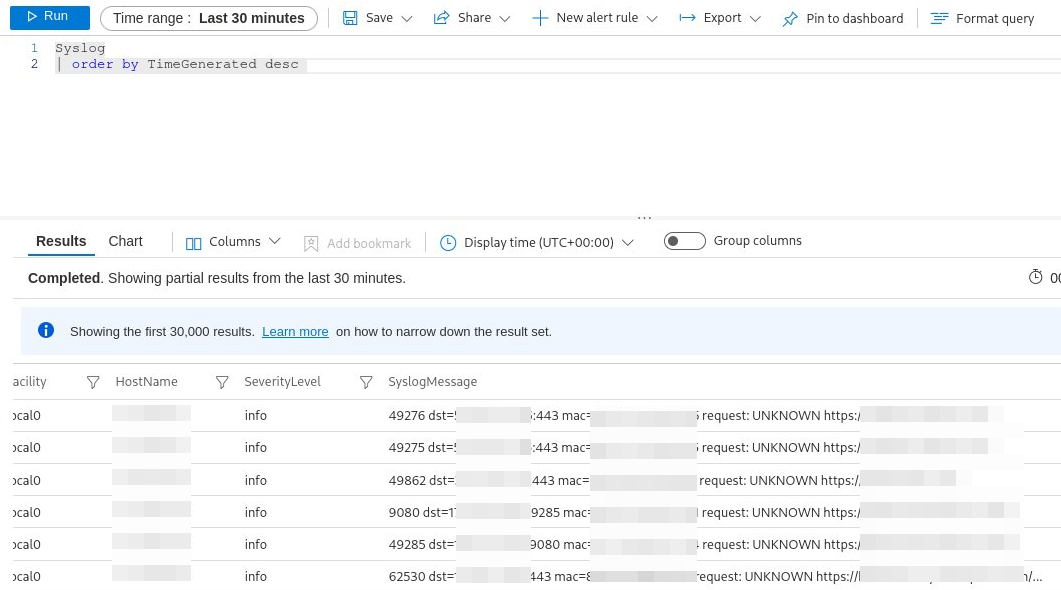
The preview connector is based on Syslog so avoid using CEF in this case. The data might be correct, just not displayed in the way you expect. Is it possible that that lead-in data is displayed in another column(s) in log analytics? Check the column picker for missing columns/data
.
Sentinel/LogAnalytics receives only partial syslog messages
Hi MS-Community,
I am having trouble getting the Meraki Logs into Sentinel.
My setup looks like the following:
- A fresh Debian 9 Image (recommended operating system for Linux)
- Executing the onboard_agent.sh
- Modifying rsyslog to listen on 514 (UDP & TCP)
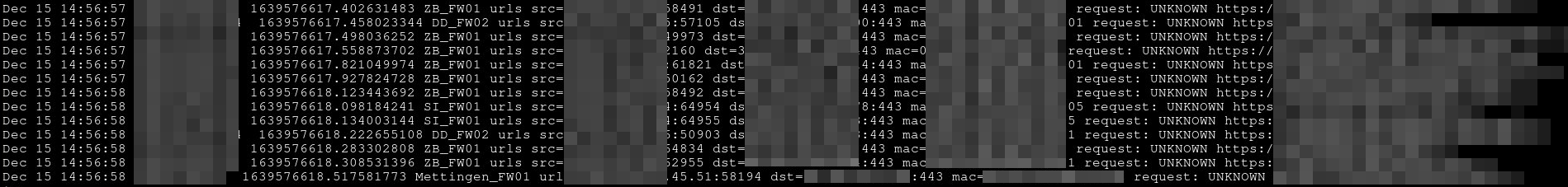
The problem is that I actually receive messages, but not the entire log entry. In the screenshot below you can see the correct string from syslog:
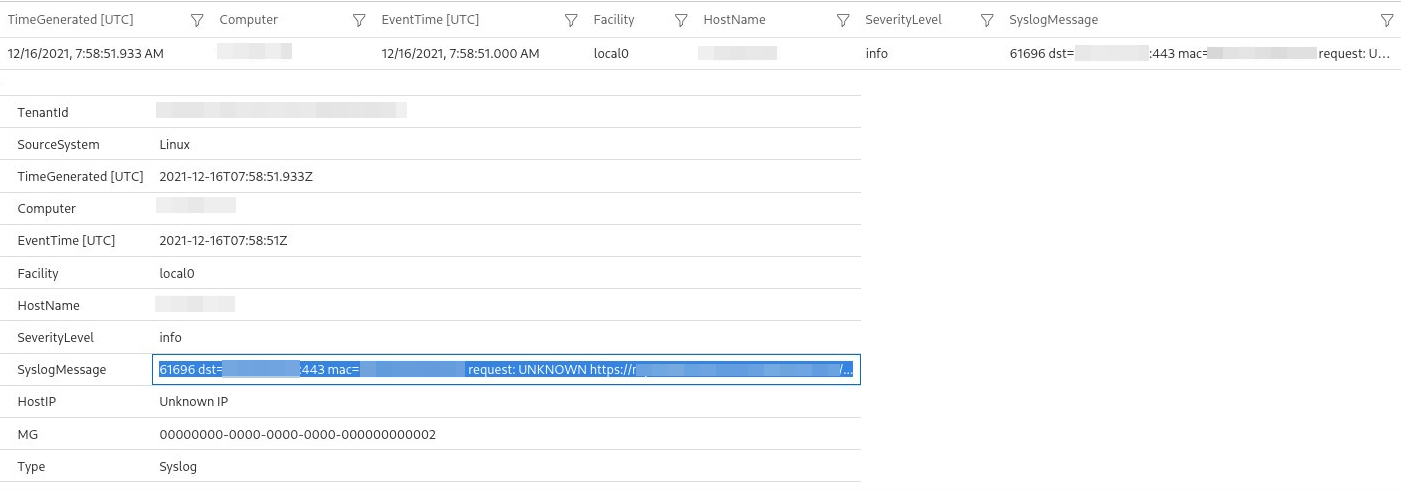
And this is what ends up in Sentinel:
If you check the log lines you can see that the agent is only transmitting the part after the first colon. I am pretty sure I have a miss-configuration with CEF and normal Syslog messages but I simply cannot put my finger on it.
Any help would be very appreciated!
Thanks in advantage.
2 answers
Sort by: Most helpful
-
 Andrew Blumhardt 9,576 Reputation points Microsoft Employee
Andrew Blumhardt 9,576 Reputation points Microsoft Employee2021-12-15T15:11:42.997+00:00 -
lmatt 11 Reputation points
2021-12-20T15:31:51.92+00:00 So I wrote a simple Relay, which "sits" between Syslog and MS-Agend. It has the simple task to forward from port A to B and replace all colons in the syslog message with an underscore or minus character.
Now it works and I can see the correct messages in the sentinel portal.1640013874.755653224 DD_FW02 urls src=xxx.xx.x.xxx-57874 dst=xx.xx.xxx.xx-443 mac=xx-xx-xx-xx-xx-xx request- UNKNOWN https-//teams.events.data.microsoft.com/...
This feels like a bug. I deployed and reinstalled the system numerous times by now.
I followed the deployment guides by the letter. Still same issues every time.