Hi @Geethanjali ,
Thanks for reaching out.
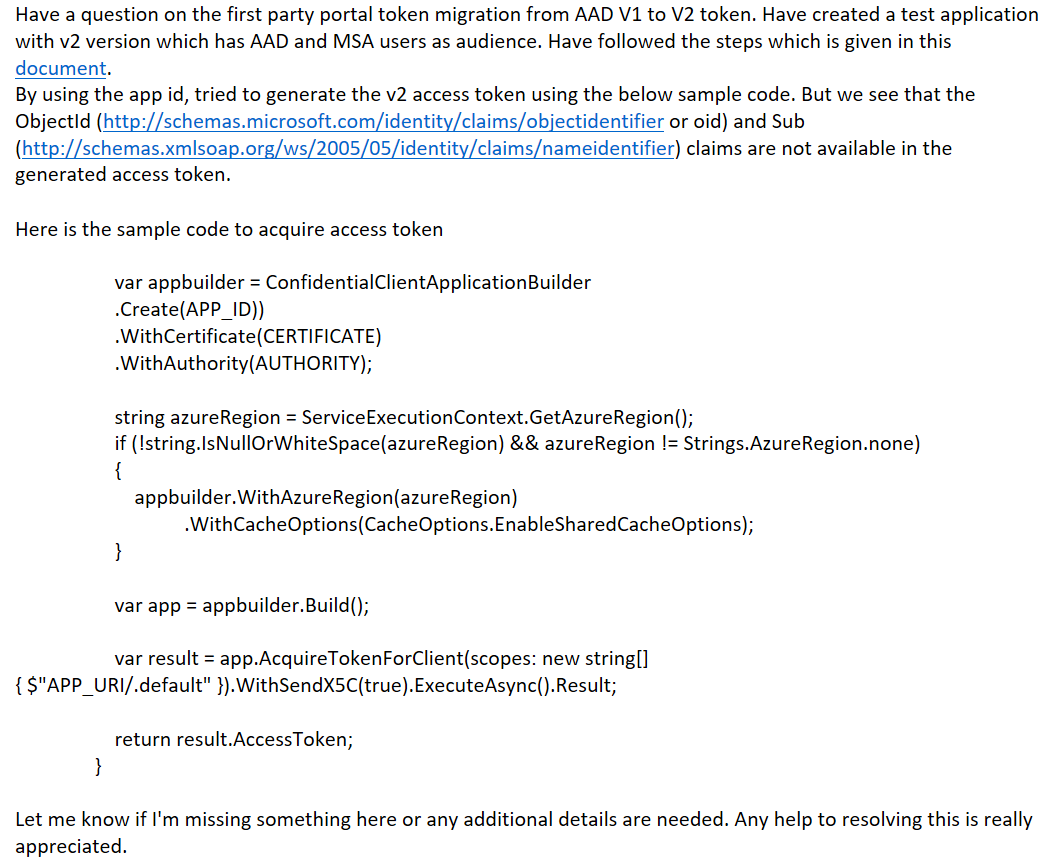
I understand that for first party application, you are not able to get oid and sub claim in access token.
As this is first party application and when you are signing in with MSA account, MSA pass through the user and does not add as guest user object in the tenant.
Since there is no object ID of User, so no OID claim returning in the token.
Alternatively, OID and sub claims will be null and not returned in the token, if the user logs in into a tenant where the apps are not provisioned, and its service principal is missing in that tenant.
Hope this will help.
Please remember to "Accept Answer" if answer helped you.
Thanks,
Shweta