Hi @JS Arya
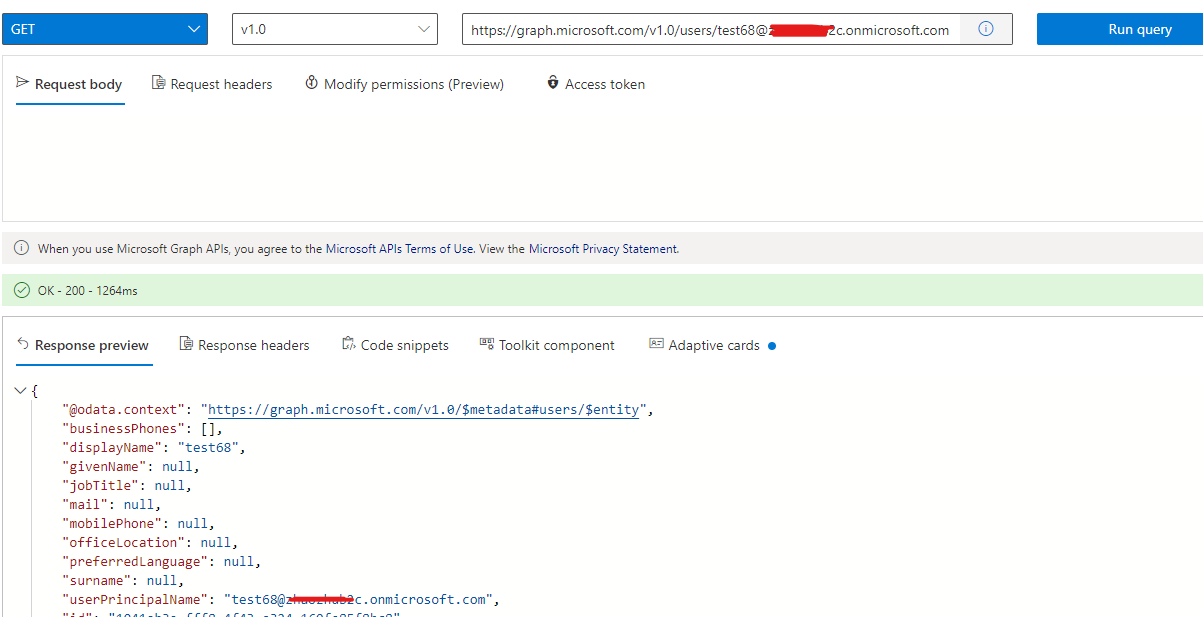
Only Directory.AccessAsUser.All delegated permissions can change user passwords, refer to the api documentation.
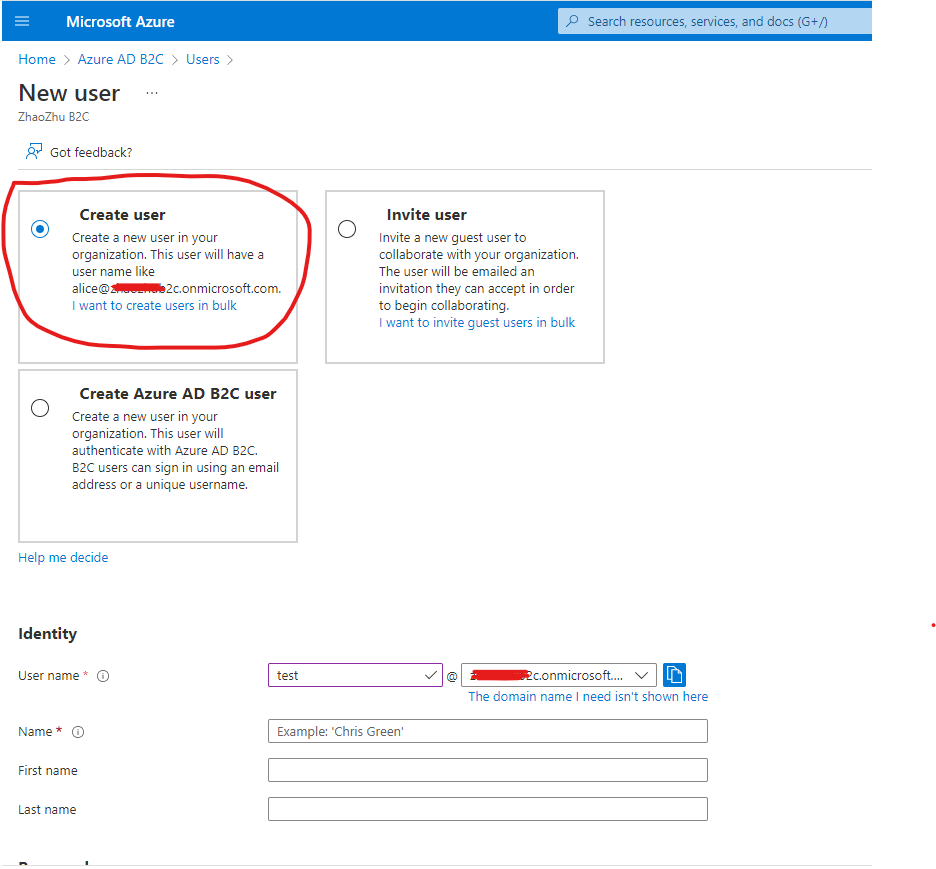
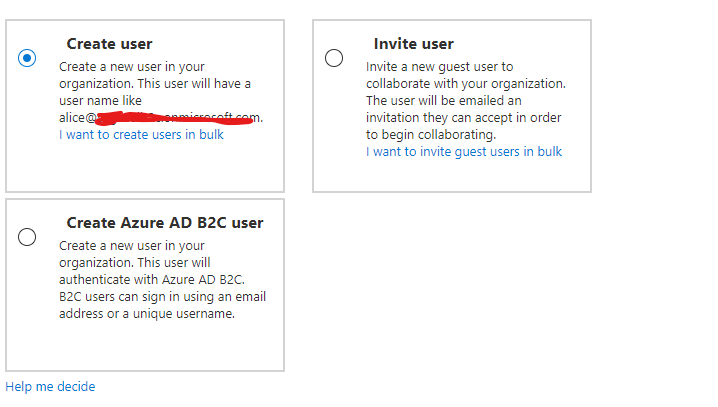
By the way, since Azure AD B2C's token does not yet support calling graph api, you need to use the Azure AD based authentication flow to authenticate your B2C user and get the token.
E.g. auth code flow or ROPC flow.
using Microsoft.Graph;
using Azure.Identity;
namespace test1
{
class Program
{
static async System.Threading.Tasks.Task Main(string[] args)
{
var scopes = new[] { "Directory.AccessAsUser.All" };
// Multi-tenant apps can use "common",
// single-tenant apps must use the tenant ID from the Azure portal
var tenantId = "b2c tenant id";
// Value from app registration
var clientId = "b2c app client id";
// using Azure.Identity;
var options = new TokenCredentialOptions
{
AuthorityHost = AzureAuthorityHosts.AzurePublicCloud
};
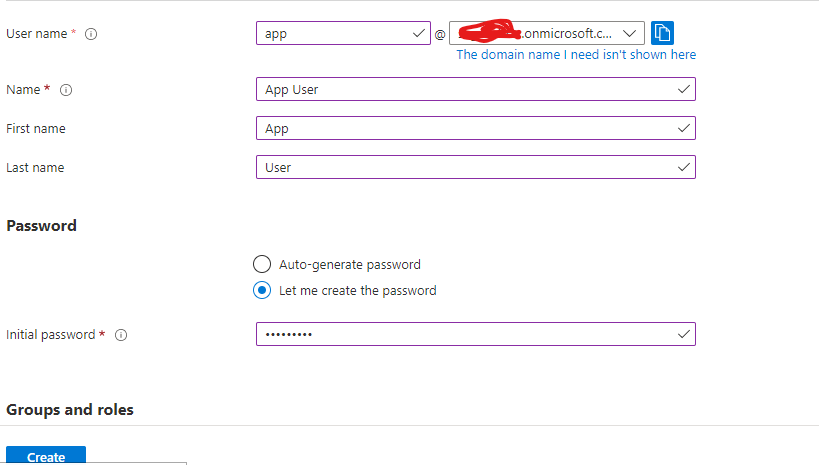
var userName = "b2c user name";
var password = "password";
// https://learn.microsoft.com/dotnet/api/azure.identity.usernamepasswordcredential
var userNamePasswordCredential = new UsernamePasswordCredential(
userName, password, tenantId, clientId, options);
var graphClient = new GraphServiceClient(userNamePasswordCredential, scopes);
var user = new User
{
PasswordProfile = new PasswordProfile
{
ForceChangePasswordNextSignIn = false,
Password = "xWwvJ]6NMw+bWH-d"
}
};
await graphClient.Users["user id"]
.Request()
.UpdateAsync(user);
}
}
}
If the answer is helpful, please click "Accept Answer" and kindly upvote it. If you have extra questions about this answer, please click "Comment".
Note: Please follow the steps in our documentation to enable e-mail notifications if you want to receive the related email notification for this thread.