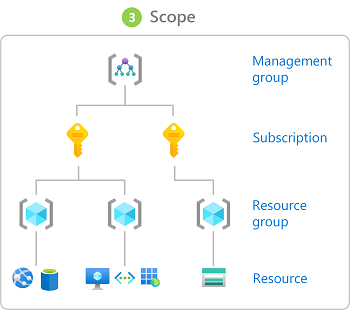
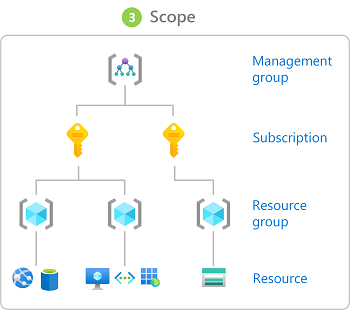
I m looking for the best security practise of using cloud admin accounts. We have privileged users as the subscription owners, contributors at the subscription level, resource group and resource level. Other privileged RBAC roles are key vault, storage accounts, SQL Paas services, Azure data factory contributors
To what level in the scope a cloud admin account is required to manage all the privileged access. Is it safe to assign privileged access to O365 accounts . On the other side, we need to create more than 5 admin accounts which is more than the microsoft recommended (5 roles)
we dont have the privileged access management implemented yet due to which we have to rely to security of the cloud admin account which is MFA, and continuous monitoring of admin activities.
Any advice or recommendations is highly appreciated
Ref - https://learn.microsoft.com/en-us/azure/active-directory/roles/security-planning
Ensure separate user accounts and mail forwarding for Global Administrator accounts
Personal email accounts are regularly phished by cyber attackers, a risk that makes personal email addresses unacceptable for Global Administrator accounts. To help separate internet risks from administrative privileges, create dedicated accounts for each user with administrative privileges.
Be sure to create separate accounts for users to do Global Administrator tasks.
Make sure that your Global Administrators don't accidentally open emails or run programs with their administrator accounts.
Be sure those accounts have their email forwarded to a working mailbox.
Global Administrator (and other privileged groups) accounts should be cloud-only accounts with no ties to on-premises Active Directory.