Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
This article describes some of the best practices for using Microsoft Entra role-based access control (Microsoft Entra RBAC). These best practices are derived from our experience with Microsoft Entra RBAC and the experiences of customers like yourself. We encourage you to also read our detailed security guidance at Securing privileged access for hybrid and cloud deployments in Microsoft Entra ID.
1. Apply principle of least privilege
When planning your access control strategy, it's a best practice to manage to least privilege. Least privilege means you grant your administrators exactly the permission they need to do their job. There are three aspects to consider when you assign a role to your administrators: a specific set of permissions, over a specific scope, for a specific period of time. Avoid assigning broader roles at broader scopes even if it initially seems more convenient to do so. By limiting roles and scopes, you limit what resources are at risk if the security principal is ever compromised. Microsoft Entra RBAC supports over 65 built-in roles. There are Microsoft Entra roles to manage directory objects like users, groups, and applications, and also to manage Microsoft 365 services like Exchange, SharePoint, and Intune. To better understand Microsoft Entra built-in roles, see Understand roles in Microsoft Entra ID. If there isn't a built-in role that meets your need, you can create your own custom roles.
Finding the right roles
Follow these steps to help you find the right role.
Sign in to the Microsoft Entra admin center.
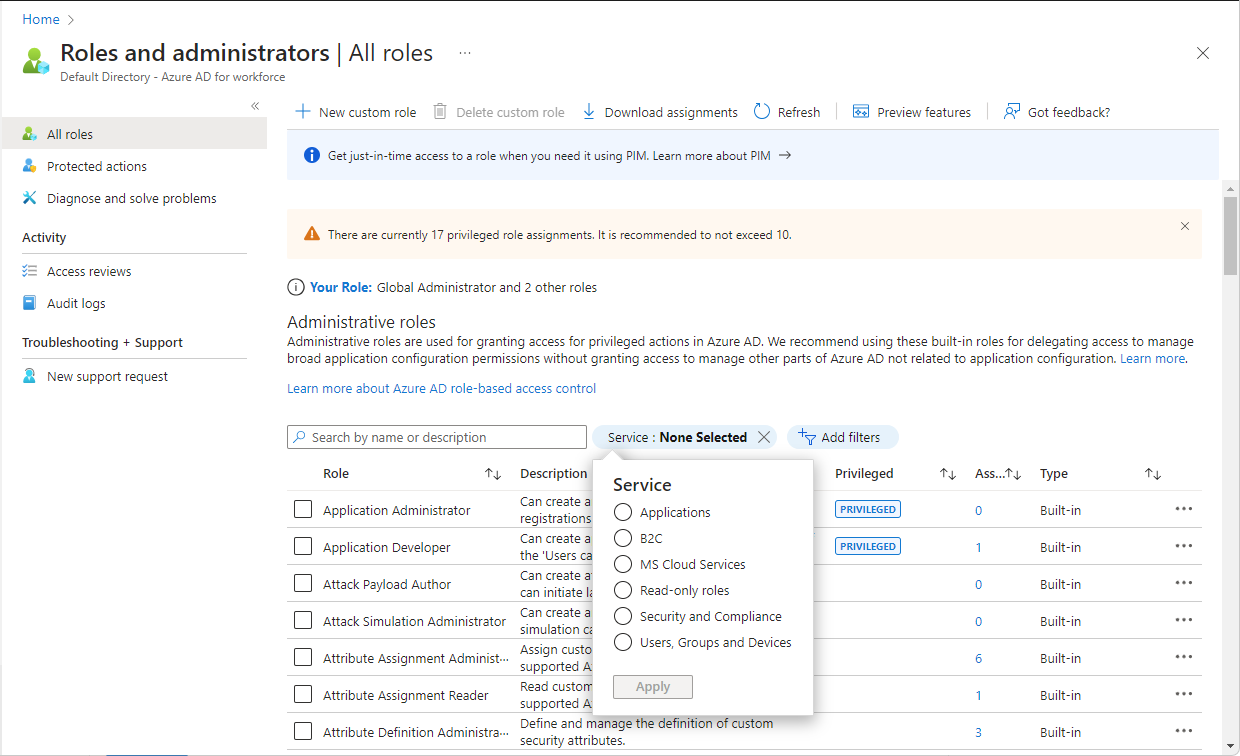
Navigate to Entra ID > Roles & admins > All roles.
Use the Service filter to narrow down the list of roles.
Refer to the Microsoft Entra built-in roles documentation. Permissions associated with each role are listed together for better readability. To understand the structure and meaning of role permissions, see How to understand role permissions.
Refer to the Least privileged role by task documentation.
2. Use Privileged Identity Management to grant just-in-time access
One of the principles of least privilege is that access should be granted only when required. Microsoft Entra Privileged Identity Management (PIM) lets you grant just-in-time access to your administrators. Microsoft recommends that you use PIM in Microsoft Entra ID. Using PIM, a user can be made eligible for a Microsoft Entra role where they can then activate the role for a limited time when needed. Privileged access is automatically removed when the timeframe expires. You can also configure PIM settings to require approval, receive notification emails when someone activates their role assignment, or other role settings. Notifications provide an alert when new users are added to highly privileged roles. For more information, see Configure Microsoft Entra role settings in Privileged Identity Management.
3. Turn on multifactor authentication for all your administrator accounts
Based on our studies, your account is 99.9% less likely to be compromised if you use multifactor authentication (MFA).
You can enable MFA on Microsoft Entra roles using two methods:
- Role settings in Privileged Identity Management
- Conditional Access
4. Configure recurring access reviews to revoke unneeded permissions over time
Access reviews enable organizations to review administrator's access regularly to make sure only the right people have continued access. Regular auditing your administrators is crucial because of following reasons:
- A malicious actor can compromise an account.
- People move teams within a company. If there's no auditing, they can amass unnecessary access over time.
Microsoft recommends that you use access reviews to find and remove role assignments that are no longer needed. This helps you reduce the risk of unauthorized or excessive access and maintain your compliance standards.
For information about access reviews for roles, see Create an access review of Azure resource and Microsoft Entra roles in PIM. For information about access reviews of groups that are assigned roles, see Create an access review of groups and applications in Microsoft Entra ID.
5. Limit the number of Global Administrators to less than 5
As a best practice, Microsoft recommends that you assign the Global Administrator role to fewer than five people in your organization. Global Administrators essentially have unrestricted access, and it is in your best interest to keep the attack surface low. As stated previously, all of these accounts should be protected with multifactor authentication.
If you have 5 or more privileged Global Administrator role assignments, a Global Administrators alert card is displayed on the Microsoft Entra Overview page to help you monitor Global Administrator role assignments.
By default, when a user signs up for a Microsoft cloud service, a Microsoft Entra tenant is created and the user is assigned the Global Administrators role. Users who are assigned the Global Administrator role can read and modify almost every administrative setting in your Microsoft Entra organization. With a few exceptions, Global Administrators can also read and modify all configuration settings in your Microsoft 365 organization. Global Administrators also have the ability to elevate their access to read data.
Microsoft recommends that organizations have two cloud-only emergency access accounts permanently assigned the Global Administrator role. These accounts are highly privileged and aren't assigned to specific individuals. The accounts are limited to emergency or "break glass" scenarios where normal accounts can't be used or all other administrators are accidentally locked out. These accounts should be created following the emergency access account recommendations.
6. Limit the number of privileged role assignments to less than 10
Some roles include privileged permissions, such as the ability to update credentials. Since these roles can potentially lead to elevation of privilege, you should limit the use of these privileged role assignments to fewer than 10 in your organization. If you exceed 10 privileged role assignments, a warning is displayed on the Roles and administrators page.
You can identify roles, permissions, and role assignments that are privileged by looking for the PRIVILEGED label. For more information, see Privileged roles and permissions in Microsoft Entra ID.
7. Use groups for Microsoft Entra role assignments and delegate the role assignment
If you have an external governance system that takes advantage of groups, then you should consider assigning roles to Microsoft Entra groups, instead of individual users. You can also manage role-assignable groups in PIM to ensure that there are no standing owners or members in these privileged groups. For more information, see Privileged Identity Management (PIM) for Groups.
You can assign an owner to role-assignable groups. That owner decides who is added to or removed from the group, so indirectly, decides who gets the role assignment. In this way, a Privileged Role Administrator can delegate role management on a per-role basis by using groups. For more information, see Use Microsoft Entra groups to manage role assignments.
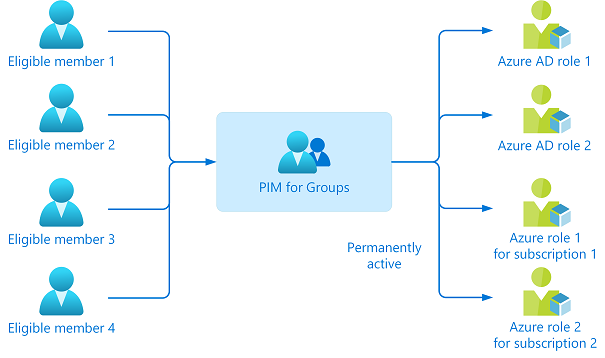
8. Activate multiple roles at once using PIM for Groups
It might be the case that an individual has five or six eligible assignments to Microsoft Entra roles through PIM. They'll have to activate each role individually, which can reduce productivity. Worse still, they can also have tens or hundreds of Azure resources assigned to them, which aggravates the problem.
In this case, you should use Privileged Identity Management (PIM) for Groups. Create a PIM for Groups and grant it permanent access to multiple roles (Microsoft Entra ID and/or Azure). Make that user an eligible member or owner of this group. With just one activation, they'll have access to all the linked resources.
9. Use cloud native accounts for Microsoft Entra roles
Avoid using on-premises synced accounts for Microsoft Entra role assignments. If your on-premises account is compromised, it can compromise your Microsoft Entra resources as well.