This article addresses frequently asked questions about how Microsoft Entra certificate-based authentication (CBA) works. Keep checking back for updated content.
Why don't I see an option to sign in to Microsoft Entra ID by using certificates after I enter my username?
An administrator needs to enable CBA for the tenant to make the sign-in with certificate option available for users. For more information, see Step 3: Configure authentication binding policy.
Where can I get more diagnostic information after a user sign-in failed?
On the error page, click More Details for more information to help your tenant admin. The tenant admin can check the Sign-ins report to investigate further. For example, if a user certificate is revoked and is part of a Certificate Revocation List, then authentication fails correctly. To get more diagnostic information, check the Sign-ins report.
How can an administrator enable Microsoft Entra CBA?
- Sign in to the Microsoft Entra admin center as at least an Authentication Policy Administrator.
- Browse to Protection > Authentication methods > Policies.
- Select policy: Certificate-based Authentication.
- On the Enable and Target tab, select the Enable toggle to enable certificate-based authentication.
Is Microsoft Entra CBA a free feature?
Certificate-based authentication is a free feature. Every edition of Microsoft Entra ID includes Microsoft Entra CBA. For more information about features in each Microsoft Entra edition, see Microsoft Entra pricing.
Does Microsoft Entra CBA support Alternate ID as the username instead of userPrincipalName?
No, sign-in using a non-UPN value, such as an alternate email, isn't supported now.
Can I have more than one CRL Distribution Point (CDP) for a Certificate Authority (CA)?
No, only one CDP is supported per CA.
Can I have non-http URLs for CDP?
No, CDP supports only HTTP URLs.
How do I find the CRL for a Certificate Authority or how do I troubleshoot the error AADSTS2205015: The Certificate Revocation List (CRL) failed signature validation?
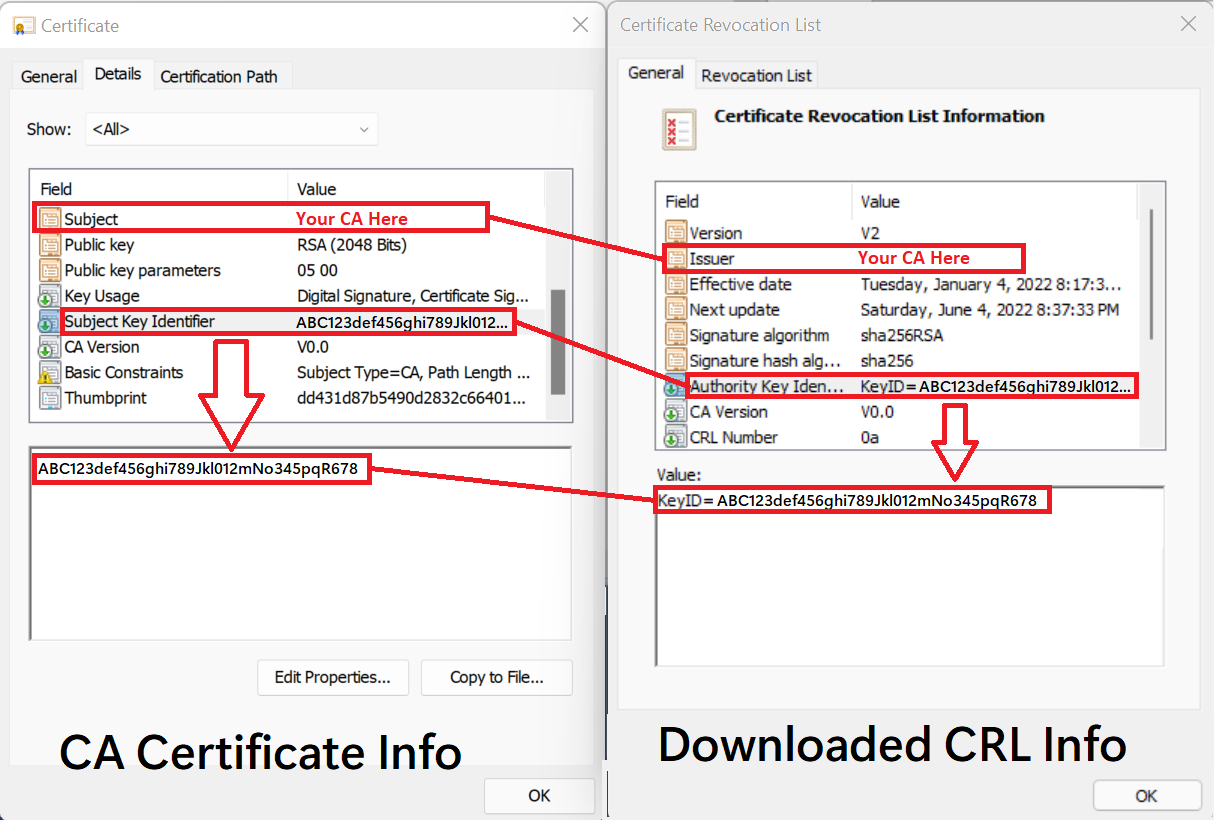
Please download the CRL and compare the CA certificate and the CRL information to validate the crlDistributionPoint value is valid for the CA you want to add. You can configure the CRL to the corresponding CA by matching CA's Issuer SKI to the AKI of the CRL (CA Issuer SKI == CRL AKI) The following table and graphic show how to map information from the CA certificate to the attributes of the downloaded CRL.
| CA Certificate Info | = | Downloaded CRL Info |
|---|---|---|
| Subject | = | Issuer |
| Subject Key Identifier | = | Authority Key Identifier (KeyID) |
How do I validate the Certificate Authority configuration?
It's important to ensure that the Certificate Authority configuration in the trust store result is Microsoft Entra ID ability to both validate the certificate authority trust chain and successfully acquire the certificate revocation list (CRL) from the configured certificate authority CRL distribution point (CDP). To assist with this task, it's recommended to install the MSIdentity Tools PowerShell module and run Test-MsIdCBATrustStoreConfiguration. This PowerShell cmdlet will review the Entra tenant certificate authority configuration and surface errors/warnings for common mis-configuration issues.
How do I turn certificate revocation checking on or off for a particular CA?
We highly recommend against disabling certificate revocation list (CRL) checking as you won't be able to revoke certificates. However, if you need to investigate issues with CRL checking, you can update a trusted CA and set the crlDistributionPoint attribute to """.
Use the Set-AzureADTrustedCertificateAuthority cmdlet:
$c=Get-AzureADTrustedCertificateAuthority
$c[0]. crlDistributionPoint=""
Set-AzureADTrustedCertificateAuthority -CertificateAuthorityInformation $c[0]
Is there a limit for CRL size?
The following CRL size limits apply:
- Interactive sign in download limit: 20 MB (Azure Global includes GCC), 45 MB for (Azure US government, includes GCC High, Dept. of Defense)
- Service download limit: 65 MB (Azure Global includes GCC), 150 MB for (Azure US government, includes GCC High, Dept. of Defense)
When a CRL download fails, the following message appears:
"The Certificate Revocation List (CRL) downloaded from {uri} has exceeded the maximum allowed size ({size} bytes) for CRLs in Microsoft Entra ID. Try again in few minutes. If the issue persists, contact your tenant administrators."
Download remains in the background with higher limits.
We're reviewing the impact of these limits and have plans to remove them.
I see a valid Certificate Revocation List (CRL) endpoint set, but why don't I see any CRL revocation?
- Make sure the CRL distribution point is set to a valid HTTP URL.
- Make sure the CRL distribution point is accessible via an internet-facing URL.
- Make sure the CRL sizes are within limits.
How do I instantly revoke a certificate?
Follow the steps to manually revoke a certificate.
Will the changes to the Authentication methods policy take effect immediately?
The policy is cached. After a policy update, it might take up to an hour for the changes to take effect.
Why do I see the certificate-based authentication option after it fails?
The Authentication method policy always shows all available authentication methods to the user so they can retry sign-in using any method they prefer. Microsoft Entra ID doesn't hide available methods based on success or failure of a sign-in.
Why does certificate-based auth (CBA) loops once it fails?
The browser caches the certificate after the certificate picker appears. If the user retries, the cached certificate is used automatically. The user should close the browser, and reopen a new session to try CBA again.
Why doesn't proof up for registering other auth methods come up when I use single factor certificates?
A user is considered capable for MFA when the user is in scope for Certificate-based authentication in the Authentication methods policy. This policy requirement means a user can't use proof up as part of their authentication to register other available methods.
How can I use single-factor certificates to complete MFA?
We have support for single factor CBA to get MFA. CBA SF + passwordless phone sign-in (PSI) and CBA SF + FIDO2 are the two supported combinations to get MFA using single factor certificates. MFA with single factor certificates
CertificateUserIds update fails with value already there. How can an admin query all the user objects with the same value?
Tenant admins can run MS Graph queries to find all the users with a given certificateUserId value. More information can be found at CertificateUserIds graph queries
GET all user objects that have the value 'bob@contoso.com' value in certificateUserIds:
GET https://graph.microsoft.com/v1.0/users?$filter=certificateUserIds/any(x:x eq 'bob@contoso.com')
After a CRL endpoint is configured, end users aren't able to sign in and they see the following diagnostic message: ```http AADSTS500173: Unable to download CRL. Invalid status code Forbidden from CRL distribution point errorCode: 500173 ```
This is commonly seen when a firewall rule setting blocks access to the CRL endpoint.
Can Microsoft Entra CBA be used on SurfaceHub?
Yes. This works out of the box for most smart card / smart card reader combinations. If the smart card / smart card reader combination requires additional drivers these must be installed prior to using the smart card / smart card reader combination on the surface hub.
Next steps
If your question isn't answered here, see the following related topics: