Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Starting on March 31, 2026, Azure Kubernetes Service (AKS) no longer supports default outbound access for virtual machines (VMs). New AKS clusters that use the AKS-managed virtual network option will place cluster subnets into private subnets by default (defaultOutboundAccess = false). This setting doesn't impact AKS-managed cluster traffic, which uses explicitly configured outbound paths. It might affect unsupported scenarios, such as deploying other resources into the same subnet. Clusters using BYO VNets are unaffected by this change. In supported configurations, no action is required. For more information on this retirement, see the Azure Updates retirement announcement. To stay informed on announcements and updates, follow the AKS release notes.
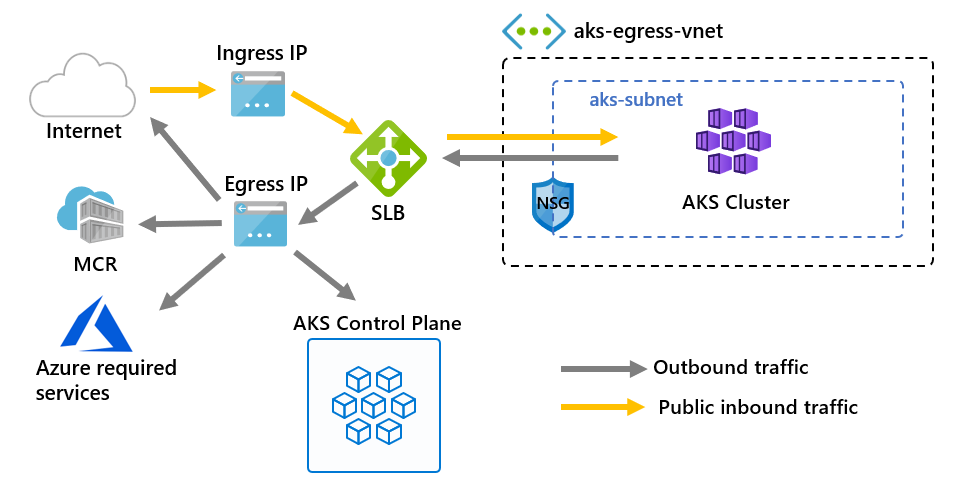
You can customize egress for an AKS cluster to fit specific scenarios. By default, AKS creates a Standard Load Balancer to be set up and used for egress. However, the default setup may not meet the requirements of all scenarios if public IPs are disallowed or extra hops are required for egress.
This article covers the various types of outbound connectivity that are available in AKS clusters.
Note
You can now update the outboundType after cluster creation.
Important
In nonprivate clusters, API server cluster traffic is routed and processed through the clusters outbound type. To prevent API server traffic from being processed as public traffic, consider using a private cluster, or check out the API Server VNet Integration feature.
Limitations
- Setting
outboundTyperequires AKS clusters with avm-set-typeofVirtualMachineScaleSetsandload-balancer-skuofStandard.
Outbound types in AKS
You can configure an AKS cluster using the following outbound types: load balancer, NAT gateway, or user-defined routes. The outbound type impacts only the egress traffic of your cluster. For more information, see setting up ingress controllers.
Outbound type: Load Balancer
The load balancer is used for egress through an AKS-assigned public IP. An outbound type of loadBalancer supports Kubernetes services of type loadBalancer, which expect egress out of the load balancer created by the AKS resource provider.
If loadBalancer is set, AKS automatically completes the following configuration:
- A public IP address is created for cluster egress.
- The public IP address is assigned to the load balancer resource.
- Backend pools for the load balancer are set up for agent nodes in the cluster.
For more information, see using a standard load balancer in AKS.
Outbound type: NAT Gateway
If managedNATGatewayV2 (Preview), managedNATGateway or userAssignedNATGateway are selected for outboundType, AKS relies on Azure Networking NAT gateway for cluster egress.
- Select
managedNATGatewayV2ormanagedNATGatewaywhen using managed virtual networks. AKS provisions a StandardV2 NAT gateway withmanagedNATGatewayV2and a Standard NAT gateway withmanagedNATGatewayand attaches it to the cluster subnet. StandardV2 NAT gateway is recommended because it's zone-redundant by default and offers higher bandwidth and throughput. For information see, StandardV2 NAT Gateway. - Select
userAssignedNATGatewaywhen using bring-your-own virtual networking. This option requires that you have a NAT gateway created before cluster creation. Both Standard and StandardV2 NAT Gateways are supported.
Important
The managedNATGatewayV2 outbound type is currently in PREVIEW.
See the Supplemental Terms of Use for Microsoft Azure Previews for legal terms that apply to Azure features that are in beta, preview, or otherwise not yet released into general availability.
For more information, see using NAT gateway with AKS.
Outbound type: User-Defined Routes
Note
The userDefinedRouting outbound type is an advanced networking scenario and requires proper network configuration.
If userDefinedRouting is set, AKS doesn't automatically configure egress paths. The egress setup is completed by you.
You must deploy the AKS cluster into an existing virtual network with a subnet that is configured. Since you're not using a standard load balancer (SLB) architecture, you must establish explicit egress. This architecture requires explicitly sending egress traffic to an appliance like a firewall, gateway, proxy or to allow NAT to be done by a public IP assigned to the standard load balancer or appliance.
For more information, see configuring cluster egress via user-defined routing.
Outbound type: none
Important
The none outbound type is only available with Network Isolated Cluster and requires careful planning to ensure the cluster operates as expected without unintended dependencies on external services. For fully isolated clusters, see isolated cluster considerations.
If none is set, AKS won't automatically configure egress paths. This option is similar to userDefinedRouting but does not require a default route as part of validation.
The none outbound type is supported in both bring-your-own (BYO) virtual network scenarios and managed VNet scenarios. However, you must ensure that the AKS cluster is deployed into a network environment where explicit egress paths are defined if needed. For BYO VNet scenarios, the cluster must be deployed into an existing virtual network with a subnet that is already configured. Since AKS doesn't create a standard load balancer or any egress infrastructure, you must establish explicit egress paths if needed. Egress options can include routing traffic to a firewall, proxy, gateway, or other custom network configurations.
Outbound type: block (Preview)
Important
The block outbound type is only available with Network Isolated Cluster and requires careful planning to ensure no unintended network dependencies exist. For fully isolated clusters, see isolated cluster considerations.
If block is set, AKS configures network rules to actively block all egress traffic from the cluster. This option is useful for highly secure environments where outbound connectivity must be restricted.
When using block:
- AKS ensures that no public internet traffic can leave the cluster through network security group (NSG) rules. VNet traffic isn't affected.
- You must explicitly allow any required egress traffic through extra network configurations.
The block option provides another level of network isolation but requires careful planning to avoid breaking workloads or dependencies.
Updating outboundType after cluster creation
Changing the outbound type after cluster creation deploys or removes resources as required to put the cluster into the new egress configuration.
The following tables show the supported migration paths between outbound types for managed and BYO virtual networks. Each row shows whether the outbound type can be migrated to the types listed across the top. "Supported" means migration is possible, while "Not Supported" or "N/A" means it isn't.
Supported migration paths for managed VNet
| From|To | loadBalancer |
managedNATGatewayV2 |
managedNATGateway |
none |
block |
|---|---|---|---|---|---|
loadBalancer |
N/A | Supported | Supported | Supported | Supported |
managedNATGatewayV2 |
Not Supported | N/A | Not Supported | Not Supported | Not Supported |
managedNATGateway |
Not Supported | Supported | N/A | Supported | Supported |
none |
Supported | Supported | Supported | N/A | Supported |
block |
Supported | Supported | Supported | Supported | N/A |
Supported migration paths for BYO VNet
| From|To | loadBalancer |
userAssignedNATGateway |
userDefinedRouting |
none |
block |
|---|---|---|---|---|---|
loadBalancer |
N/A | Supported | Supported | Supported | Not Supported |
userAssignedNATGateway |
Supported | N/A | Supported | Supported | Not Supported |
userDefinedRouting |
Supported | Supported | N/A | Supported | Not Supported |
none |
Supported | Supported | Supported | N/A | Not Supported |
Warning
Migrating the outbound type to managedNATGatewayV2 userAssignedNATGateway or userDefinedRouting will change the outbound public IP addresses of the cluster.
If Authorized IP ranges is enabled, ensure new outbound IP range is appended to authorized IP range.
Warning
Changing the outbound type on a cluster is disruptive to network connectivity and results in a change of the cluster's egress IP address. It involves downtime and impact to existing connections. If any firewall rules are configured to restrict traffic from the cluster, you need to update them to match the new egress IP address.
Update cluster to use a new outbound type
Note
You must use a version >= 2.56 of Azure CLI to migrate outbound type. Use az upgrade to update to the latest version of Azure CLI.
Update the outbound configuration of your cluster using the az aks update command.
Update cluster from loadBalancer to managedNATGatewayV2
az aks update --resource-group <resourceGroup> --name <clusterName> --outbound-type managedNATGatewayV2 --nat-gateway-managed-outbound-ipv6-count <number of managed outbound ipv6>
Important
The managedNATGatewayV2 outbound type is currently in PREVIEW.
See the Supplemental Terms of Use for Microsoft Azure Previews for legal terms that apply to Azure features that are in beta, preview, or otherwise not yet released into general availability. For more information, see using NAT gateway with AKS.
Update cluster from managedNATGateway to loadBalancer
az aks update --resource-group <resourceGroup> --name <clusterName> \
--outbound-type loadBalancer \
< --load-balancer-managed-outbound-ip-count <number of managed outbound ip> | --load-balancer-outbound-ips <outbound ip ids> | --load-balancer-outbound-ip-prefixes <outbound ip prefix ids> >
Warning
Don't reuse an IP address that is already in use in prior outbound configurations.
Update cluster from managedNATGateway to userDefinedRouting
Add route 0.0.0.0/0 default route table. Please see Customize cluster egress with a user-defined routing table in Azure Kubernetes Service (AKS)
az aks update --resource-group <resourceGroup> --name <clusterName> --outbound-type userDefinedRouting
Update cluster from loadBalancer to userAssignedNATGateway in BYO VNet scenario
Associate NAT gateway with subnet where the workload is associated with. Refer to Create a managed or user-assigned NAT gateway
az aks update --resource-group <resourceGroup> --name <clusterName> --outbound-type userAssignedNATGateway