Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Azure Storage is Microsoft's cloud storage solution for modern data storage scenarios. Azure Storage offers highly available, massively scalable, durable, and secure storage for data objects in the cloud. This guide shows how to mount Azure Storage Files as a network share in Windows code (noncontainer) in Azure App Service.
Azure Storage supports Azure Files Shares and Premium Files Shares for App Service. Azure Storage isn't the default storage for App Service. It's billed separately. You can also configure Azure Storage in an ARM template.
The benefits of custom-mounted storage include:
- Configure persistent storage for your App Service app and manage the storage separately.
- Make static content like video and images readily available for your App Service app.
- Write application log files or archive older application logs to Azure File shares.
- Share content across multiple apps or with other Azure services.
The following features are supported for Windows code:
- Secured access to storage accounts with key vault, private endpoints, and service endpoints (when you use virtual network integration).
- Azure Files (read/write).
- Up to five mount points per app.
- Mount Azure Storage file shares using /mounts/<path-name>.
Here are the three options to mount Azure storage to your app:
| Mounting option | Usage |
|---|---|
| Basic | Choose this option when you mount storage by using the Azure portal. You can use the basic option as long as the storage account doesn't use service endpoints, private endpoints, or Azure Key Vault. In this case, the portal gets and stores the access key for you. |
| Access Key | If you plan to mount storage using the Azure CLI, you need to obtain an access key. Choose this option if storage account doesn't use service endpoints, private endpoints, or Azure Key Vault. |
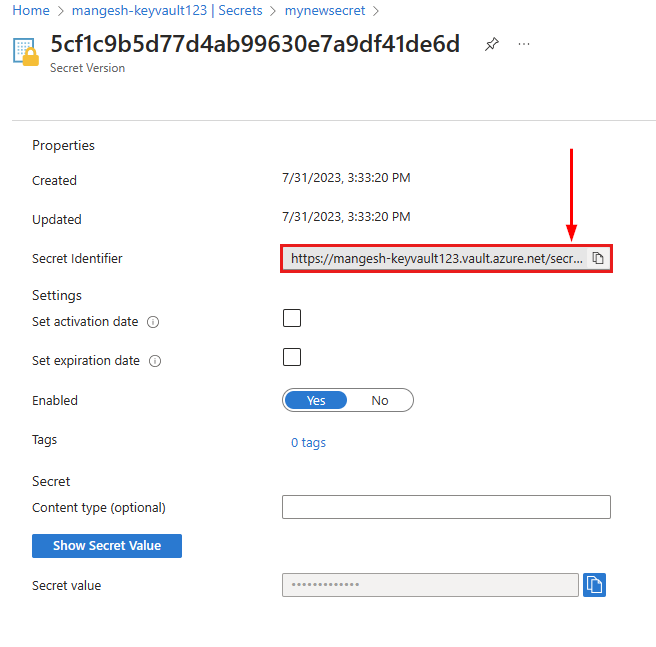
| Key Vault | Also use this option when you plan to mount storage using the Azure CLI, which requires the access key. Choose this option when using Azure Key Vault to securely store and retrieve access keys. Azure Key Vault has the benefits of storing application secrets centrally and securely with the ability to monitor, administer, and integrate with other Azure services like Azure App Service. |
Prerequisites
Limitations
- Storage firewall is supported only through private endpoints and service endpoints when you use virtual network integration.
- Azure blobs aren't supported when you configure Azure storage mounts for Windows code apps deployed to App Service.
- FTP/FTPS access to mounted storage isn't supported. Use Azure Storage Explorer.
- Mapping /mounts, mounts/name1/name2, /, and /mounts/name.ext/ to custom-mounted storage isn't supported. You can only use /mounts/pathname for mounting custom storage to your web app.
- Storage mounts aren't included in backups. Be sure to follow best practices to back up Azure Storage accounts.
- With virtual network integration on your app, the mounted drive uses an RFC1918 IP address and not an IP address from your virtual network.
Prepare for mounting
No extra steps are required because the portal gets and stores the access key for you.
Mount storage to Windows code
In the Azure portal, navigate to the app.
From the left navigation, select Settings > Configuration. Select Path mappings, then New Azure Storage Mount.
Configure the storage mount according to the following table. When finished, select OK.
Setting Description Name Name of the mount configuration. Spaces aren't allowed. Configuration options Select Basic if the storage account doesn't use private endpoints or Azure Key Vault. Otherwise, select Advanced. Storage accounts Azure Storage account. It must contain an Azure Files share. Share name Files share to mount. Storage access Select Key vault reference for Azure Key Vault. Otherwise, select Manual input Access key (Advanced only) Access key for your storage account. Mount path Directory inside your app service that you want to mount. Only /mounts/pathname is supported. Application settings Select the app setting with the Azure Key Vault secret. Deployment slot setting When selected, the storage mount settings also apply to deployment slots.
Note
Adding, editing, or deleting a storage mount causes the app to restart.
Best practices
Azure Storage mounts can be configured as a virtual directory to serve static content. To configure the virtual directory, in the left navigation select Settings > Configuration. Then select Path mappings, then New virtual application or directory. Set the Physical path to the Mount path defined on the Azure Storage mount.
To avoid latency issues, place the app and the Azure Storage account in the same region. If you grant access from App Service IP addresses in the Azure Storage firewall configuration when the app and Azure Storage account are in the same region, these IP restrictions aren't honored.
In the Azure Storage account, avoid regenerating the access key that you use to mount the storage in the app. The storage account contains two keys. Azure App Services stores an Azure storage account key. Use a stepwise approach to ensure that the storage mount remains available to the app during key regeneration. For example, assuming that you used key1 to configure storage mount in your app:
- Regenerate key2.
- In the storage mount configuration, update the access the key to use the regenerated key2.
- Regenerate key1.
If you delete an Azure Storage account, container, or share, remove the corresponding storage mount configuration in the app to avoid possible error scenarios.
The mounted Azure Storage account can be either Standard or Premium performance tier. Based on the app capacity and throughput requirements, choose the appropriate performance tier for the storage account. See the scalability and performance targets for Files.
If your app scales to multiple instances, all the instances connect to the same mounted Azure Storage account. To avoid performance bottlenecks and throughput issues, choose the appropriate performance tier for the storage account.
We don't recommend that you use storage mounts for local databases, such as SQLite, or for any other applications and components that rely on file handles and locks.
If you initiate a storage failover when the storage account is mounted to the app, the mount doesn't connect until the app is restarted or the storage mount is removed and added again.
When virtual network integration is used, ensure app setting,
WEBSITE_CONTENTOVERVNETis set to1and the following ports are open: Azure Files: 80 and 445.The mounted Azure Storage account can be either Standard or Premium performance tier. Based on the app capacity and throughput requirements, choose the appropriate performance tier for the storage account. See the scalability and performance targets for Files.
Next step
Azure Storage is Microsoft's cloud storage solution for modern data storage scenarios. Azure Storage offers highly available, massively scalable, durable, and secure storage for data objects in the cloud. This guide shows how to mount Azure Storage Files as a network share in a Windows container in App Service.
Azure Storage supports Azure Files Shares and Premium Files Shares. Azure Storage isn't the default storage for App Service. It's billed separately. You can also configure Azure Storage in an ARM template.
The benefits of custom-mounted storage include:
- Configure persistent storage for your App Service app and manage the storage separately.
- Make static content like video and images readily available for your App Service app.
- Write application log files or archive older application log to Azure File shares.
- Share content across multiple apps or with other Azure services.
- Mount Azure Storage in a Windows container, including Isolated. For more information, see App Service environment v3.
The following features are supported for Windows containers:
- Secured access to storage accounts with key vault, private endpoints, and service endpoints when you use virtual network integration.
- Azure Files (read/write).
- Up to five mount points per app.
- Drive letter assignments (C: to Z:).
Here are the three options to mount Azure storage to your app:
| Mounting option | Usage |
|---|---|
| Basic | Choose this option when mounting storage using the Azure portal. You can use the basic option as long as the storage account doesn't use service endpoints, private endpoints, or Azure Key Vault. In this case, the portal gets and stores the access key for you. |
| Access Key | If you plan to mount storage using the Azure CLI, you need to obtain an access key. Choose this option if storage account doesn't use service endpoints, private endpoints, or Azure Key Vault. |
| Key Vault | Also use this option when you plan to mount storage using the Azure CLI, which requires the access key. Choose this option when using Azure Key Vault to securely store and retrieve access keys. Azure Key Vault has the benefits of storing application secrets centrally and securely with the ability to monitor, administer, and integrate with other Azure services like Azure App Service. |
Prerequisites
Limitations
- Azure blobs aren't supported.
- Storage firewall is supported only through private endpoints and service endpoints when you use virtual network integration.
- FTP/FTPS access to mounted storage not supported (use Azure Storage Explorer).
- Mapping [C-Z]:\, [C-Z]:\home, /, and /home to custom-mounted storage isn't supported.
- Storage mounts aren't backed up when you back up your app. Be sure to follow best practices to back up the Azure Storage accounts.
- With virtual network integration on your app, the mounted drive uses an RFC1918 IP address and not an IP address from your virtual network.
Prepare for mounting
No extra steps are required because the portal gets and stores the access key for you.
Mount storage to Windows container
In the Azure portal, navigate to the app.
From the left navigation, select Settings > Configuration. Select Path mappings, then New Azure Storage Mount.
Configure the storage mount according to the following table. When finished, select OK.
Setting Description Name Name of the mount configuration. Spaces aren't allowed. Configuration options Select Basic Storage accounts Azure Storage account. It must contain an Azure Files share. Share name Files share to mount. Mount path Directory inside your Windows container that you want to mount. Don't use a root directory ([C-Z]:* or /) or the home directory ([C-Z]:\home* or /home). Deployment slot setting When selected, the storage mount settings also apply to deployment slots.
Note
Adding, editing, or deleting a storage mount causes the app to restart.
Best practices
To avoid latency issues, place the app and the Azure Storage account in the same region. If you grant access from App Service IP addresses in the Azure Storage firewall configuration when the app and Azure Storage account are in the same region, these IP restrictions aren't honored.
In the Azure Storage account, avoid regenerating the access key that you use to mount the storage in the app. The storage account contains two keys. Azure App Services stores an Azure storage account key. Use a stepwise approach to ensure that the storage mount remains available to the app during key regeneration. For example, assuming that you used key1 to configure storage mount in your app:
- Regenerate key2.
- In the storage mount configuration, update the access the key to use the regenerated key2.
- Regenerate key1.
If you delete an Azure Storage account, container, or share, remove the corresponding storage mount configuration in the app to avoid possible error scenarios.
The mounted Azure Storage account can be either Standard or Premium performance tier. Based on the app capacity and throughput requirements, choose the appropriate performance tier for the storage account. See the scalability and performance targets for Files.
If your app scales to multiple instances, all the instances connect to the same mounted Azure Storage account. To avoid performance bottlenecks and throughput issues, choose the appropriate performance tier for the storage account.
We don't recommend that you use storage mounts for local databases, such as SQLite, or for any other applications and components that rely on file handles and locks.
Ensure ports 80 and 445 are open when using Azure Files with virtual network integration.
If you initiate a storage failover when the storage account is mounted to the app, the mount doesn't connect until the app is restarted or the storage mount is removed and added again.
Next step
Note
NFS support is now available for App Service on Linux.
This guide shows how to mount Azure Storage as a network share in a built-in Linux container or a custom Linux container in App Service. Azure Storage is Microsoft's cloud storage solution for modern data storage scenarios. Azure Storage offers highly available, massively scalable, durable, and secure storage for data objects in the cloud. Azure Storage isn't the default storage for App Service. It's billed separately. You can also configure Azure Storage in an ARM template.
The benefits of custom-mounted storage include:
- Configure persistent storage for your App Service app and manage the storage separately.
- Make static content like video and images readily available for your App Service app.
- Write application log files or archive older application log to Azure File shares.
- Share content across multiple apps or with other Azure services.
- Supports Azure Files NFS and Azure Files SMB.
- Supports Azure Blobs (read-only).
- Supports up to five mount points per app.
The limitations of custom-mounted storage include:
- Storage firewall is supported only through service endpoints and private endpoints when you use virtual network integration.
- FTP/FTPS access to custom-mounted storage isn't supported. Use Azure Storage Explorer.
- Storage account shared access keys are the only means of authentication that are supported. Entra ID and RBAC Roles aren't supported.
- Azure CLI, Azure PowerShell, and Azure SDK support is in preview.
- Mapping / or /home to custom-mounted storage isn't supported.
- Don't map the storage mount to /tmp or its subdirectories. This action can cause a time-out during app startup.
- Azure Storage isn't supported with Docker Compose scenarios.
- Storage mounts aren't included in backups. Be sure to follow best practices to back up the Azure Storage accounts.
- NFS support is only available for App Service on Linux. NFS isn't supported for Windows code and Windows containers. The web app and storage account need to be configured on the same virtual network for NFS. The storage account used for file share should have Premium performance tier and File storage as the Account Kind. Azure Key Vault isn't applicable when using the NFS protocol.
- With virtual network integration on your app, the mounted drive uses an RFC1918 IP address and not an IP address from your virtual network.
Mounting options
You need to mount the storage to the app. Here are three mounting options for Azure storage:
| Mounting option | Usage |
|---|---|
| Basic | Choose this option to mount storage using the Azure portal. You can use the basic option as long as the storage account doesn't use service endpoints, private endpoints, or Azure Key Vault. In this case, the portal gets and stores the access key for you. |
| Access Key | If you plan to mount storage using the Azure CLI, you need to obtain an access key. Choose this option if storage account doesn't use service endpoints, private endpoints, or Azure Key Vault. |
| Key Vault | Also use this option when you plan to mount storage using the Azure CLI, which requires the access key. Choose this option when you use Azure Key Vault to securely store and retrieve access keys. Azure Key Vault has the benefits of storing application secrets centrally and securely with the ability to monitor, administer, and integrate with other Azure services like Azure App Service. |
Prerequisites
- An existing App Service on Linux app.
- An Azure Storage account.
- An Azure file share and directory.
Prepare for mounting
No extra steps are required because the portal gets and stores the access key for you.
Mount storage to Linux container
The way that you mount storage depends on your storage access option and whether you use the portal or the Azure CLI.
In the Azure portal, navigate to the app.
From the left navigation, select Settings > Configuration. Select Path mappings, then New Azure Storage Mount.
Configure the storage mount according to the following table. When finished, select OK.
Setting Description Name Name of the mount configuration. Spaces aren't allowed. Configuration options Select Basic if the storage account doesn't use service endpoints, private endpoints, or Azure Key Vault. Otherwise, select Advanced. Storage accounts Azure Storage account. Storage type Select the type based on the storage you want to mount. Azure Blobs only supports read-only access. Storage container or Share name Files share or Blobs container to mount. Mount path Directory inside the Linux container to mount to Azure Storage. Don't use / or /home. Deployment slot setting When checked, the storage mount settings also apply to deployment slots.
Note
Adding, editing, or deleting a storage mount causes the app to restart.
Validate the mounted storage
To validate that the Azure Storage is mounted successfully for the app:
Open an SSH session into the container.
In the SSH terminal, execute the following command:
df –hCheck if the storage share is mounted. If it's not present, there's an issue with mounting the storage share.
Check latency or general reachability of the storage mount with the following command:
tcpping Storageaccount.file.core.windows.net
Best practices
Performance
To avoid latency issues, place the app and the Azure Storage account in the same region. If you grant access from App Service IP addresses in the Azure Storage firewall configuration when the app and Azure Storage account are in the same region, then these IP restrictions aren't honored.
The mounted Azure Storage account can be either Standard or Premium performance tier. Based on the app capacity and throughput requirements, choose the appropriate performance tier for the storage account. See the scalability and performance targets that correspond to the storage type: Files and Blobs.
If your app scales to multiple instances, all the instances connect to the same mounted Azure Storage account. To avoid performance bottlenecks and throughput issues, choose the appropriate performance tier for the storage account.
Security
In the Azure Storage account, avoid regenerating the access key that you use to mount the storage in the app. The storage account contains two keys. Azure App Services stores an Azure storage account key. Use a stepwise approach to ensure that the storage mount remains available to the app during key regeneration. For example, assuming that you used key1 to configure storage mount in your app:
- Regenerate key2.
- In the storage mount configuration, update the access the key to use the regenerated key2.
- Regenerate key1.
Configuration
- If you need to use a real time file system, where you expect changes to alter, add, or remove files quickly, use Azure Files as the storage type when you mount storage. When files are static and you don't expect them to change, use Azure Blob.
Troubleshooting
- The mount directory in the custom container should be empty. Any content stored at this path is deleted when the Azure Storage is mounted, if you specify a directory under /home, for example. If you migrate files for an existing app, make a backup of the app and its content before you begin.
- If you delete an Azure Storage account, container, or share, remove the corresponding storage mount configuration in the app to avoid possible error scenarios.
- We don't recommend that you use storage mounts for local databases, such as SQLite, or for any other applications and components that rely on file handles and locks.
- Ensure the following ports are open when using virtual network integration: Azure Files: 80 and 445. Azure Blobs: 80 and 443.
- If you initiate a storage failover when the storage account is mounted to the app, the mount doesn't connect until the app is restarted or the storage mount is removed and added again.