Tutorial: Enable application gateway ingress controller add-on for an existing AKS cluster with an existing application gateway
You can use Azure CLI or portal to enable the application gateway ingress controller (AGIC) add-on for an existing Azure Kubernetes Services (AKS) cluster. In this tutorial, you'll learn how to use AGIC add-on to expose your Kubernetes application in an existing AKS cluster through an existing application gateway deployed in separate virtual networks. You'll start by creating an AKS cluster in one virtual network and an application gateway in a separate virtual network to simulate existing resources. You'll then enable the AGIC add-on, peer the two virtual networks together, and deploy a sample application that will be exposed through the application gateway using the AGIC add-on. If you're enabling the AGIC add-on for an existing application gateway and existing AKS cluster in the same virtual network, then you can skip the peering step below. The add-on provides a much faster way of deploying AGIC for your AKS cluster than through Helm and also offers a fully managed experience.
In this tutorial, you learn how to:
- Create a resource group
- Create a new AKS cluster
- Create a new application gateway
- Enable the AGIC add-on in the existing AKS cluster through Azure CLI
- Enable the AGIC add-on in the existing AKS cluster through Azure portal
- Peer the application gateway virtual network with the AKS cluster virtual network
- Deploy a sample application using AGIC for ingress on the AKS cluster
- Check that the application is reachable through application gateway
If you don't have an Azure subscription, create an Azure free account before you begin.
Prerequisites
Use the Bash environment in Azure Cloud Shell. For more information, see Quickstart for Bash in Azure Cloud Shell.
If you prefer to run CLI reference commands locally, install the Azure CLI. If you're running on Windows or macOS, consider running Azure CLI in a Docker container. For more information, see How to run the Azure CLI in a Docker container.
If you're using a local installation, sign in to the Azure CLI by using the az login command. To finish the authentication process, follow the steps displayed in your terminal. For other sign-in options, see Sign in with the Azure CLI.
When you're prompted, install the Azure CLI extension on first use. For more information about extensions, see Use extensions with the Azure CLI.
Run az version to find the version and dependent libraries that are installed. To upgrade to the latest version, run az upgrade.
Create a resource group
In Azure, you allocate related resources to a resource group. Create a resource group by using az group create. The following example creates a resource group named myResourceGroup in the East US location (region):
az group create --name myResourceGroup --location eastus
Deploy a new AKS cluster
You'll now deploy a new AKS cluster, to simulate having an existing AKS cluster that you want to enable the AGIC add-on for.
In the following example, you'll be deploying a new AKS cluster named myCluster using Azure CNI and Managed Identities in the resource group you created, myResourceGroup.
az aks create --name myCluster --resource-group myResourceGroup --network-plugin azure --enable-managed-identity --generate-ssh-keys
To configure more parameters for the above command, see az aks create.
Note
A node resource group will be created with the name MC_resource-group-name_cluster-name_location.
Deploy a new application gateway
You'll now deploy a new application gateway, to simulate having an existing application gateway that you want to use to load balance traffic to your AKS cluster, myCluster. The name of the application gateway will be myApplicationGateway, but you'll need to first create a public IP resource, named myPublicIp, and a new virtual network called myVnet with address space 10.0.0.0/16, and a subnet with address space 10.0.0.0/24 called mySubnet, and deploy your application gateway in mySubnet using myPublicIp.
Caution
When you use an AKS cluster and application gateway in separate virtual networks, the address spaces of the two virtual networks must not overlap. The default address space that an AKS cluster deploys in is 10.224.0.0/12.
az network public-ip create --name myPublicIp --resource-group myResourceGroup --allocation-method Static --sku Standard
az network vnet create --name myVnet --resource-group myResourceGroup --address-prefix 10.0.0.0/16 --subnet-name mySubnet --subnet-prefix 10.0.0.0/24
az network application-gateway create --name myApplicationGateway --resource-group myResourceGroup --sku Standard_v2 --public-ip-address myPublicIp --vnet-name myVnet --subnet mySubnet --priority 100
Note
The application gateway ingress controller (AGIC) add-on only supports application gateway v2 SKUs (Standard and WAF), and not the application gateway v1 SKUs.
Enable the AGIC add-on in existing AKS cluster through Azure CLI
If you'd like to continue using Azure CLI, you can continue to enable the AGIC add-on in the AKS cluster you created, myCluster, and specify the AGIC add-on to use the existing application gateway you created, myApplicationGateway.
appgwId=$(az network application-gateway show --name myApplicationGateway --resource-group myResourceGroup -o tsv --query "id")
az aks enable-addons --name myCluster --resource-group myResourceGroup --addon ingress-appgw --appgw-id $appgwId
Enable the AGIC add-on in existing AKS cluster through Azure portal
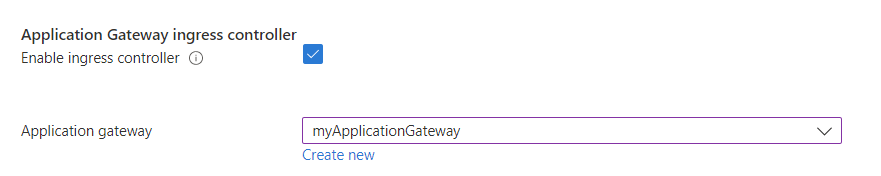
If you'd like to use Azure portal to enable AGIC add-on, go to (https://aka.ms/azure/portal/aks/agic) and navigate to your AKS cluster through the portal link. Select the Networking menu item under Settings. From there, go to the Virtual network integration tab within your AKS cluster. You'll see an Application gateway ingress controller section, which allows you to enable and disable the ingress controller add-on. Select the Manage button, then the checkbox next to Enable ingress controller. Select the application gateway you created, myApplicationGateway and then select Save.
Important
If you use an application gateway in a different resource group than the AKS cluster resource group, the managed identity ingressapplicationgateway-{AKSNAME} that is created must have Network Contributor and Reader roles set in the application gateway resource group.
Peer the two virtual networks together
Since you deployed the AKS cluster in its own virtual network and the Application gateway in another virtual network, you'll need to peer the two virtual networks together in order for traffic to flow from the Application gateway to the pods in the cluster. Peering the two virtual networks requires running the Azure CLI command two separate times, to ensure that the connection is bi-directional. The first command will create a peering connection from the Application gateway virtual network to the AKS virtual network; the second command will create a peering connection in the other direction.
nodeResourceGroup=$(az aks show --name myCluster --resource-group myResourceGroup -o tsv --query "nodeResourceGroup")
aksVnetName=$(az network vnet list --resource-group $nodeResourceGroup -o tsv --query "[0].name")
aksVnetId=$(az network vnet show --name $aksVnetName --resource-group $nodeResourceGroup -o tsv --query "id")
az network vnet peering create --name AppGWtoAKSVnetPeering --resource-group myResourceGroup --vnet-name myVnet --remote-vnet $aksVnetId --allow-vnet-access
appGWVnetId=$(az network vnet show --name myVnet --resource-group myResourceGroup -o tsv --query "id")
az network vnet peering create --name AKStoAppGWVnetPeering --resource-group $nodeResourceGroup --vnet-name $aksVnetName --remote-vnet $appGWVnetId --allow-vnet-access
Note
In the "Deploy a new AKS cluster" step above we created AKS with Azure CNI, in case you have an existing AKS cluster using Kubenet mode you need to update the route table to help the packets destined for a POD IP reach the node which is hosting the pod. A simple way to achieve this is by associating the same route table created by AKS to the Application Gateway's subnet.
Deploy a sample application using AGIC
You'll now deploy a sample application to the AKS cluster you created that will use the AGIC add-on for Ingress and connect the application gateway to the AKS cluster. First, you'll get credentials to the AKS cluster you deployed by running the az aks get-credentials command.
az aks get-credentials --name myCluster --resource-group myResourceGroup
Once you have the credentials to the cluster you created, run the following command to set up a sample application that uses AGIC for Ingress to the cluster. AGIC will update the application gateway you set up earlier with corresponding routing rules to the new sample application you deployed.
kubectl apply -f https://raw.githubusercontent.com/Azure/application-gateway-kubernetes-ingress/master/docs/examples/aspnetapp.yaml
Check that the application is reachable
Now that the application gateway is set up to serve traffic to the AKS cluster, let's verify that your application is reachable. You'll first get the IP address of the Ingress.
kubectl get ingress
Check that the sample application you created is up and running by either visiting the IP address of the application gateway that you got from running the above command or check with curl. It may take application gateway a minute to get the update, so if the application gateway is still in an "Updating" state on Azure portal, then let it finish before trying to reach the IP address.
Clean up resources
When no longer needed, delete all resources created in this tutorial by deleting myResourceGroup and MC_myResourceGroup_myCluster_eastus resource groups:
az group delete --name myResourceGroup
az group delete --name MC_myResourceGroup_myCluster_eastus
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for
