Solution ideas
This article describes a solution idea. Your cloud architect can use this guidance to help visualize the major components for a typical implementation of this architecture. Use this article as a starting point to design a well-architected solution that aligns with your workload's specific requirements.
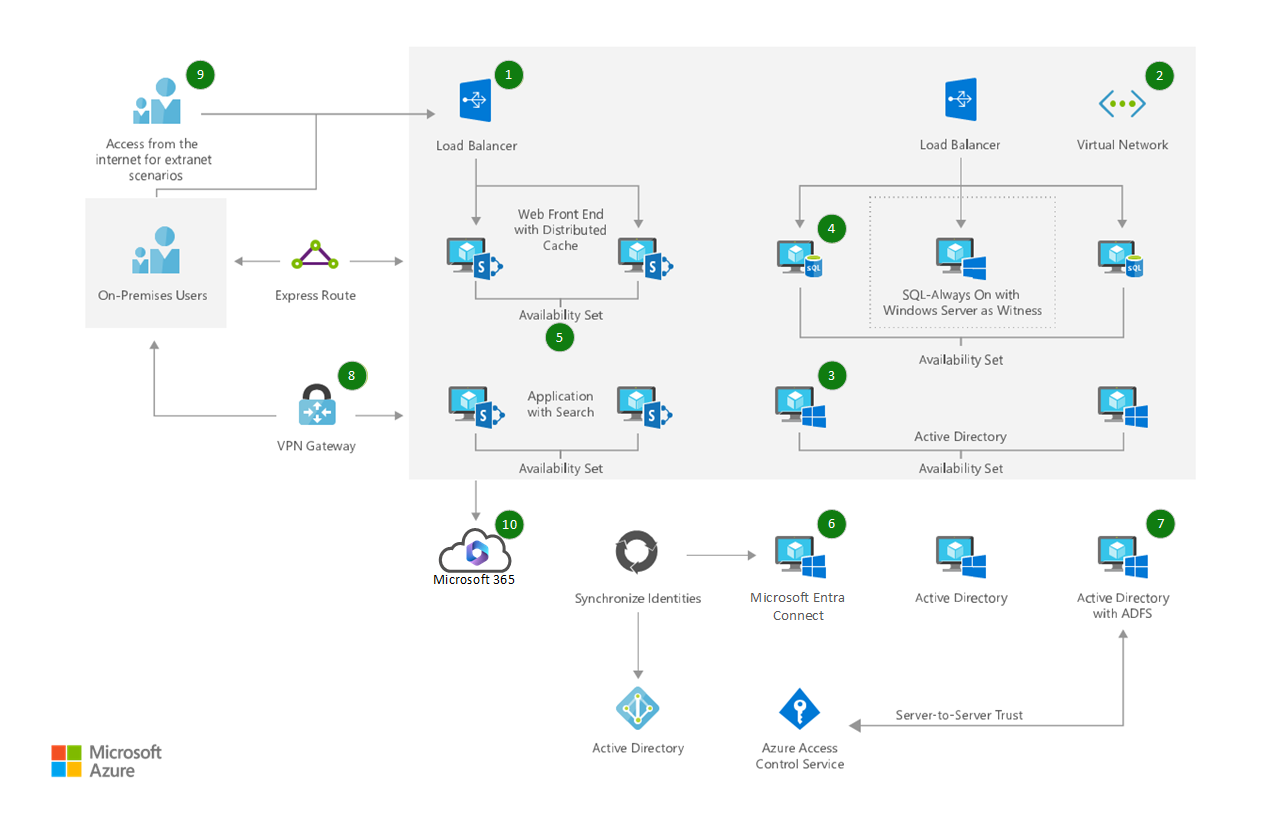
This solution provides a highly available deployment of SharePoint, by using a load-balanced Microsoft Entra instance, a highly available SQL always-on instance, and highly available SharePoint resources.
Potential use cases
This solution addresses the need to deliver a highly available intranet capability, by using the latest and greatest supported platforms.
Architecture
 Download an SVG of this architecture.
Download an SVG of this architecture.
Dataflow
- Create a resource group to host all Azure based infrastructure and services.
- Create a virtual network in Azure.
- Deploy Windows Servers to host Active Directory services for SharePoint, SQL server service accounts, and machine accounts.
- Deploy SQL Server Always-on for high availability (HA) support for the SharePoint farm.
- Deploy the SharePoint Server instances. In this scenario, we use two frontend servers with distributed cache and two applications with search roles. This gives us high availability.
- Install Microsoft Entra Connect on an on-premises server, to synchronize your identities to Microsoft Entra ID.
- Optionally configure Active Directory Federation Services on premises, to support federated authentication to Microsoft 365.
- Deploy ExpressRoute or set up a site-to-site VPN link, for administrative access to the servers that are hosted in Azure VMs.
- Set up and provision external access to the hybrid farm that's hosted in Azure VMs.
- Set up and configure hybrid workloads between Microsoft 365 and the SharePoint farm.
Components
- Azure Resource Group: Container that holds related resources for an Azure solution.
- Virtual Network: Provision private networks, and optionally connect to on-premises datacenters.
- Storage Accounts: Enable durable, highly available, and massively scalable cloud storage.
- Microsoft Entra ID: Synchronize on-premises directories, and enable single sign-on.
- SharePoint Server: Microsoft's collaboration server product.
- Host enterprise SQL Server apps in the cloud.
- Load Balancer: Deliver high availability and network performance to your applications.
- Azure ExpressRoute: Dedicated private network fiber connections to Azure
- VPN Gateway: Establish secure, cross-premises connectivity.
- Microsoft Entra Connect: Synchronize on-premises directories, and enable single sign-on.
- Active Directory Federation Services: Synchronize on-premises directories, and enable single sign-on.
- Hybrid Workloads: Scale between on-premises environments and the cloud.
Next steps
- Azure Resource Group Documentation
- Virtual Network Documentation
- Storage Documentation
- Active Directory Documentation
- SharePoint Server Documentation
- SQL Server Documentation
- Load Balancer Documentation
- ExpressRoute Documentation
- VPN Gateway Documentation
- Microsoft Entra Connect Documentation
- Active Directory Federation Services Documentation
- Hybrid Workloads Documentation