Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Azure Policy is a service in Azure that you use to create, assign, and manage policies. These policies enforce different rules and effects over your resources, so those resources stay compliant with your corporate standards and service level agreements.
This article introduces built-in policies (preview) for Azure SignalR Service. Use these policies to audit new and existing SignalR resources for compliance.
There are no charges for using Azure Policy.
Built-in policy definitions
The following built-in policy definitions are specific to Azure SignalR Service:
| Name (Azure portal) |
Description | Effect(s) | Version (GitHub) |
|---|---|---|---|
| Azure SignalR Service should disable public network access | To improve the security of Azure SignalR Service resource, ensure that it isn't exposed to the public internet and can only be accessed from a private endpoint. Disable the public network access property as described in https://aka.ms/asrs/networkacls. This option disables access from any public address space outside the Azure IP range, and denies all logins that match IP or virtual network-based firewall rules. This reduces data leakage risks. | Audit, Deny, Disabled | 1.2.0 |
| Azure SignalR Service should enable diagnostic logs | Audit enabling of diagnostic logs. This enables you to recreate activity trails to use for investigation purposes; when a security incident occurs or when your network is compromised | AuditIfNotExists, Disabled | 1.0.0 |
| Azure SignalR Service should have local authentication methods disabled | Disabling local authentication methods improves security by ensuring that Azure SignalR Service exclusively require Azure Active Directory identities for authentication. | Audit, Deny, Disabled | 1.0.0 |
| Azure SignalR Service should use a Private Link enabled SKU | Azure Private Link lets you connect your virtual network to Azure services without a public IP address at the source or destination which protect your resources against public data leakage risks. The policy limits you to Private Link enabled SKUs for Azure SignalR Service. Learn more about private link at: https://aka.ms/asrs/privatelink. | Audit, Deny, Disabled | 1.0.0 |
| Azure SignalR Service should use private link | Azure Private Link lets you connect your virtual network to Azure services without a public IP address at the source or destination. The private link platform handles the connectivity between the consumer and services over the Azure backbone network. By mapping private endpoints to your Azure SignalR Service resource instead of the entire service, you'll reduce your data leakage risks. Learn more about private links at: https://aka.ms/asrs/privatelink. | Audit, Disabled | 1.0.0 |
| Configure Azure SignalR Service to disable local authentication | Disable local authentication methods so that your Azure SignalR Service exclusively requires Azure Active Directory identities for authentication. | Modify, Disabled | 1.0.0 |
| Configure private endpoints to Azure SignalR Service | Private endpoints connect your virtual network to Azure services without a public IP address at the source or destination. By mapping private endpoints to Azure SignalR Service resources, you can reduce data leakage risks. Learn more at https://aka.ms/asrs/privatelink. | DeployIfNotExists, Disabled | 1.0.0 |
| Deploy - Configure private DNS zones for private endpoints connect to Azure SignalR Service | Use private DNS zones to override the DNS resolution for a private endpoint. A private DNS zone links to your virtual network to resolve to Azure SignalR Service resource. Learn more at: https://aka.ms/asrs/privatelink. | DeployIfNotExists, Disabled | 1.0.0 |
| Modify Azure SignalR Service resources to disable public network access | To improve the security of Azure SignalR Service resource, ensure that it isn't exposed to the public internet and can only be accessed from a private endpoint. Disable the public network access property as described in https://aka.ms/asrs/networkacls. This option disables access from any public address space outside the Azure IP range, and denies all logins that match IP or virtual network-based firewall rules. This reduces data leakage risks. | Modify, Disabled | 1.2.0 |
Assign policy definitions
- Assign policy definitions using the Azure portal, Azure CLI, a Resource Manager template, or the Azure Policy SDKs.
- Scope a policy assignment to a resource group, a subscription, or an Azure management group. SignalR policy assignments apply to existing and new SignalR resources within the scope.
- Enable or disable policy enforcement at any time.
Note
After you assign or update a policy, it takes some time for the assignment to be applied to resources in the defined scope. See information about policy evaluation triggers.
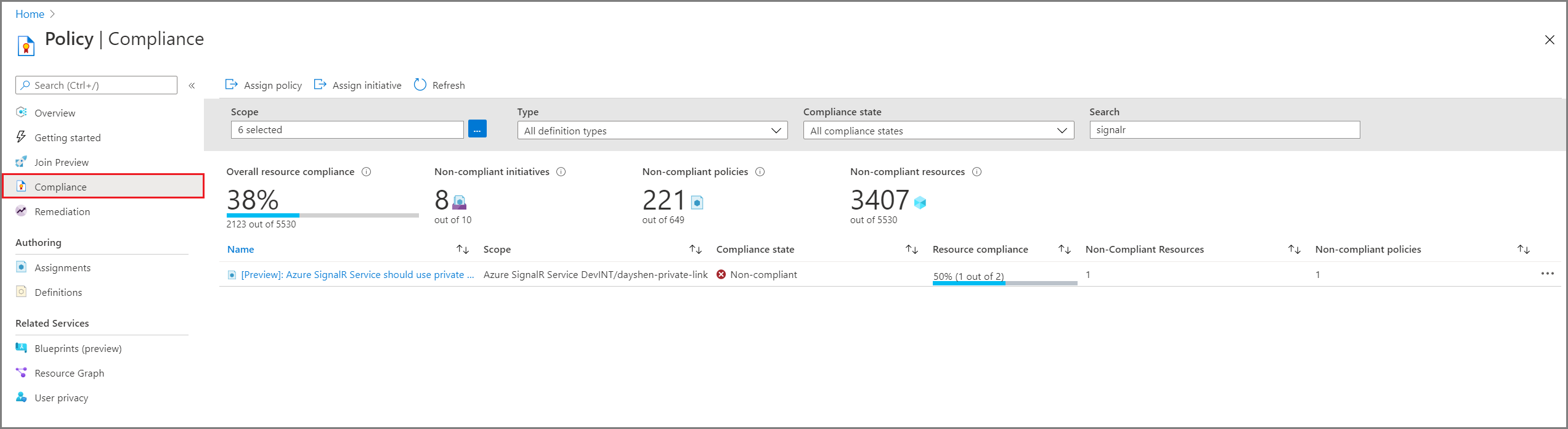
Review policy compliance
Access compliance information generated by your policy assignments using the Azure portal, Azure command-line tools, or the Azure Policy SDKs. For details, see Get compliance data of Azure resources.
When a resource is non-compliant, there are many possible reasons. To determine the reason or to find the change responsible, see Determine non-compliance.
Policy compliance in the portal:
Select All services, and search for Policy.
Select Compliance.
Use the filters to limit compliance states or to search for policies
Select a policy to review aggregate compliance details and events. If desired, then select a specific SignalR for resource compliance.
Policy compliance in the Azure CLI
You can also use the Azure CLI to get compliance data. For example, use the az policy assignment list command in the CLI to get the policy IDs of the Azure SignalR Service policies that are applied:
az policy assignment list --query "[?contains(displayName,'SignalR')].{name:displayName, ID:id}" --output table
Sample output:
Name ID
------------------------------------------------------------------------------------- --------------------------------------------------------------------------------------------------------------------------------
[Preview]: Azure SignalR Service should use private links /subscriptions/<subscriptionId>/resourceGroups/<resourceGroup>/providers/Microsoft.Authorization/policyAssignments/<assignmentId>
Then run az policy state list to return the JSON-formatted compliance state for all resources under a specific resource group:
az policy state list --g <resourceGroup>
Or run az policy state list to return the JSON-formatted compliance state of a specific SignalR resource:
az policy state list \
--resource /subscriptions/<subscriptionId>/resourceGroups/<resourceGroup>/providers/Microsoft.SignalRService/SignalR/<resourceName> \
--namespace Microsoft.SignalRService \
--resource-group <resourceGroup>
Next steps
Learn more about Azure Policy definitions and effects
Create a custom policy definition
Learn more about governance capabilities in Azure