Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Applies to:
Azure SQL Database
Azure SQL Managed Instance
This article guides you through creating an Azure Policy that would enforce Microsoft Entra-only authentication when users create an Azure SQL Managed Instance, or a logical server for Azure SQL Database. To learn more about Microsoft Entra-only authentication during resource creation, see Create server with Microsoft Entra-only authentication enabled in Azure SQL.
Note
Although Azure Active Directory (Azure AD) has been renamed to Microsoft Entra ID, Microsoft Entra-only and Azure AD-only authentication are used interchangeably in this article.
In this article, you learn how to:
- Create an Azure Policy that enforces logical server or managed instance creation with Microsoft Entra-only authentication enabled
- Check Azure Policy compliance
Prerequisite
- Have permissions to manage Azure Policy. For more information, see Azure RBAC permissions in Azure Policy.
Create an Azure Policy
Start off by creating an Azure Policy enforcing SQL Database or SQL Managed Instance provisioning with Microsoft Entra-only authentication enabled.
Go to the Azure portal.
Search for the service Policy.
Under the Authoring settings, select Definitions.
In the Search box, search for Microsoft Entra-only authentication.
There are a few built-in policies available to enforce Microsoft Entra-only authentication. Look for the one available for your service:
- Azure SQL Database should have Microsoft Entra-only Authentication enabled
- Azure SQL Managed Instance should have Microsoft Entra-only Authentication enabled
Select the policy name for your service. In this example, we'll use Azure SQL Database. Select Azure SQL Database should have Microsoft Entra-only authentication enabled.
Select Assign policy in the new menu.
Note
The JSON script in the menu shows the built-in policy definition that can be used as a template to build a custom Azure Policy for SQL Database. The default is set to
Audit.In the Basics tab, add a Scope by using the selector (...) on the side of the box.
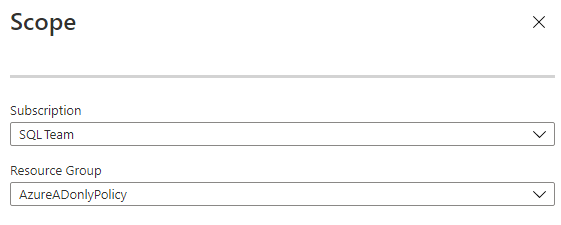
In the Scope pane, select your Subscription from the dropdown list menu, and select a Resource Group for this policy. Once you're done, use the Select button to save the selection.
Note
If you don't select a resource group, the policy applies to the whole subscription.
Once you're back on the Basics tab, customize the Assignment name and provide an optional Description. Make sure the Policy enforcement is Enabled.
Go over to the Parameters tab. Unselect the option Only show parameters that require input.
Under Effect, select Deny. This setting prevents creating a logical server without Microsoft Entra-only authentication enabled.
In the Non-compliance messages tab, you can customize the policy message that displays if a violation of the policy has occurred. The message will let users know what policy was enforced during server creation.
Select Review + create. Review the policy and select the Create button.
Note
It can take some time for the newly created policy to be enforced.
Check policy compliance
You can check the Compliance setting under the Policy service to see the compliance state.
Search for the assignment name that you have given earlier to the policy.
Once the logical server is created with Microsoft Entra-only authentication, the policy report will increase the counter under the Resources by compliance state visual. You'll be able to see which resources are compliant, or noncompliant.
If the resource group that the policy was chosen to cover contains already created servers, the policy report will indicate those resources that are compliant and noncompliant.
Note
Updating the compliance report can take some time. Changes related to resource creation or Microsoft Entra-only authentication settings aren't reported immediately.
Provision a server
You can then try to provision a logical server or managed instance in the resource group that you assigned the Azure Policy. If Microsoft Entra-only authentication is enabled during server creation, the provision will succeed. When Microsoft Entra-only authentication isn't enabled, the provision will fail.
For more information, see Create server with Microsoft Entra-only authentication enabled in Azure SQL.


