Defender for Cloud collects data from your Azure virtual machines (VMs), Virtual Machine Scale Sets, IaaS containers, and non-Azure computers (including on-premises machines) to monitor for security vulnerabilities and threats. The Log Analytics agent collects data, which reads various security-related configurations and event logs from the machine and copies the data to your workspace for analysis.
Data collection
How do I enable data collection?
Data collection is automatically turned on when you enable a Defender plan that requires a monitoring component.
What happens when data collection is enabled?
When automatic provisioning is enabled, Defender for Cloud uses the Log Analytics agent on all supported Azure VMs and any new ones that are created. Automatic provisioning is recommended but manual agent installation is also available. Learn how to install the Log Analytics agent extension.
The agent enables the process creation event 4688 and the CommandLine field inside event 4688. New processes created on the VM get recorded by the EventLog and monitored by Defender for Cloud's detection services. For more information on the details recorded for each new process, see description fields in 4688. The agent also collects the 4688 events created on the VM and stores them in search.
The agent also enables data collection for Adaptive application controls, Defender for Cloud configures a local AppLocker policy in Audit mode to allow all applications. This policy causes AppLocker to generate events, which are then collected and used by Defender for Cloud. It's important to note that this policy isn't configured on any machines on which there's already a configured AppLocker policy.
When Defender for Cloud detects suspicious activity on the VM, the customer receives an email notification if security contact information has been provided. An alert is also visible in Defender for Cloud's security alerts dashboard.
Agents
What is the Log Analytics agent?
To monitor for security vulnerabilities and threats, Microsoft Defender for Cloud depends on the Log Analytics Agent - this agent is the same used by the Azure Monitor service.
The agent is sometimes referred to as the Microsoft Monitoring Agent (or "MMA").
The agent collects various security-related configuration details and event logs from connected machines, and then copies the data to your Log Analytics workspace for further analysis. Examples of such data are: operating system type and version, operating system logs (Windows event logs), running processes, machine name, IP addresses, and logged in user.
Ensure your machines are running one of the supported operating systems for the agent as described on the following pages:
Learn more about the data collected by the Log Analytics agent.
What qualifies a VM for automatic provisioning of the Log Analytics agent installation?
Windows or Linux IaaS VMs qualify if:
- The Log Analytics agent extension isn't currently installed on the VM.
- The VM is in running state.
- The Windows or Linux Azure Virtual Machine Agent is installed.
- The VM isn't used as an appliance such as web application firewall or next generation firewall.
What security events does Log Analytics agent collect?
For a full list of the security events collected by the agent, see What event types are stored for the "Common" and "Minimal" security events settings?.
Important
For some services, such as Azure Firewall, logging for a resource that produces numerous logs can consume storage in your Log Analytics workspace. Make sure you use verbose logging only when necessary.
What if the Log Analytics agent was already installed as an extension on the VM?
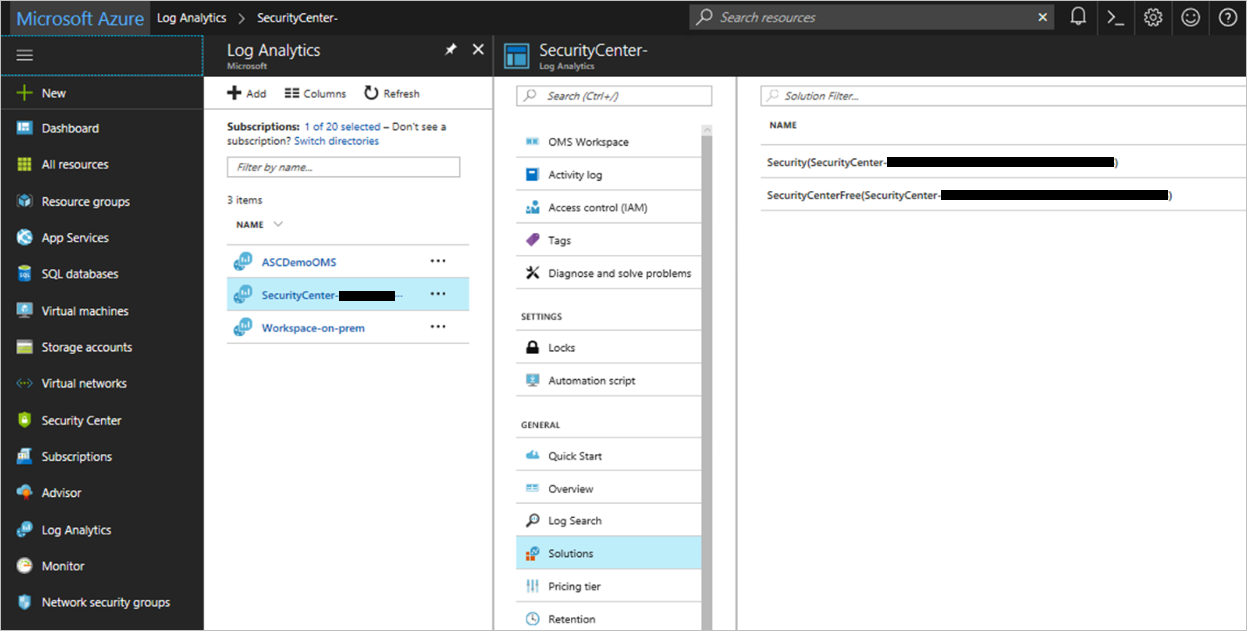
When the Monitoring Agent is installed as an extension, the extension configuration allows reporting to only a single workspace. Defender for Cloud doesn't override existing connections to user workspaces. Defender for Cloud stores security data from a VM in a workspace that is already connected when the "Security" or "SecurityCenterFree" solution is installed on it. Defender for Cloud might upgrade the extension version to the latest version in this process.
For more information, see Automatic provisioning in cases of a pre-existing agent installation.
What if a Log Analytics agent is directly installed on the machine but not as an extension (Direct Agent)?
If the Log Analytics agent is installed directly on the VM (not as an Azure extension), Defender for Cloud installs the Log Analytics agent extension, and might upgrade the Log Analytics agent to the latest version.
The agent installed continues to report to its already configured workspaces, and reports to the workspace configured in Defender for Cloud. (Multi-homing is supported on Windows machines.)
For custom user workspaces, you need to install the "Security" or "SecurityCenterFree" solution on it so that Defender for Cloud can process events from VMs and computers reporting to that workspace.
For Linux machines, agent multi-homing isn't yet supported. If an existing agent installation is detected, Defender for Cloud doesn't automatically uses an agent or change the machine's configuration.
For existing machines on subscriptions onboarded to Defender for Cloud before March 17 2019, agent multi-homing isn't yet supported. If an existing agent installation is detected, Defender for Cloud doesn't automatically use an agent or change the machine's configuration. For these machines, see the "Resolve monitoring agent health issues on your machines" recommendation to resolve the agent installation issues on these machines
For more information, see the next section What happens if a System Center Operations Manager or OMS direct agent is already installed on my VM?
What if a System Center Operations Manager agent is already installed on my VM?
Defender for Cloud implements an Azure Policy that doesn't allow the Log Analytics agent to be installed while the System Center Operations Manager Agent in installed on the machine. Both the agents have the ability to multi-home and report to the System Center Operations Manager and the Log Analytics workspace. The Operations Manager agent and Log Analytics agent share common run-time libraries. Note - If version 2012 of the Operations Manager agent is installed, don't turn on automatic provisioning (manageability capabilities can be lost when the Operations Manager server is also version 2012).
What is the effect of removing these extensions?
If you remove the Microsoft Monitoring Extension, Defender for Cloud isn't able to collect security data from the VM and some security recommendations and alerts are unavailable. Within 24 hours, Defender for Cloud determines that the VM is missing the extension and reinstalls the extension.
How do I stop the automatic agent installation and workspace creation?
Deploying extensions with Defender for Cloud is highly recommended in order to get security alerts and recommendations about system updates, OS vulnerabilities, and endpoint protection. Turning off extensions limits these alerts and recommendations. However, you can disable automatic provisioning for a specific agent or extension:
To disable automatic provisioning for a specific agent or extension:
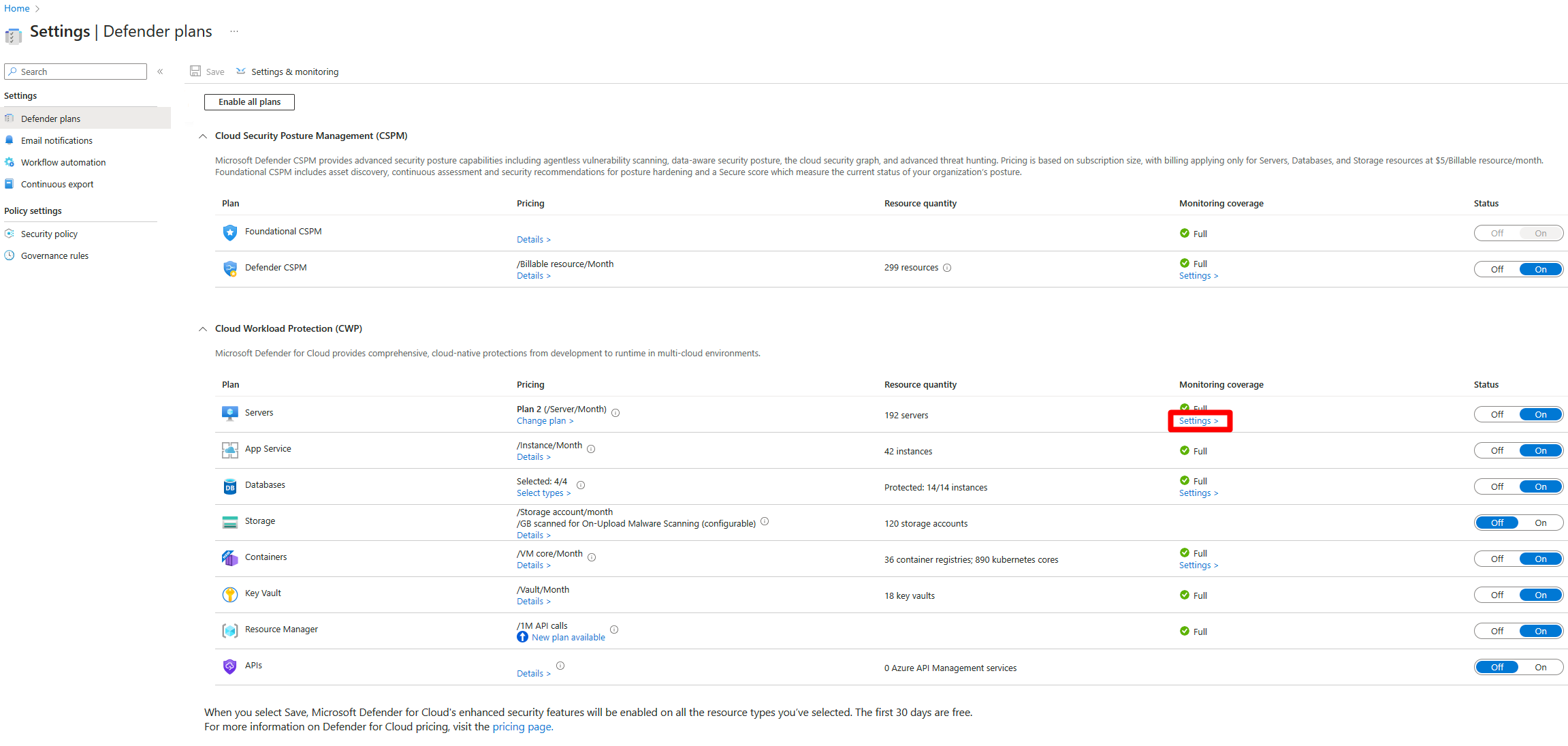
From the Azure portal, open Defender for Cloud and select Environment settings.
Select the relevant subscription.
In the Monitoring coverage column of the Defender for Server plan, select Settings.
Turn off the extension you want to stop being automatically provisioned.
Select Save.
Should I opt out of the automatic agent installation and workspace creation?
Note
Be sure to review sections What are the implications of opting out? and recommended steps when opting out if you choose to opt out of automatic provisioning.
You might want to opt out of automatic provisioning if these scenarios apply to you:
Automatic agent installation by Defender for Cloud applies to the entire subscription. You can't apply automatic installation to a subset of VMs. If there are critical VMs that can't be installed with the Log Analytics agent, then you should opt out of automatic provisioning.
Installation of the Log Analytics agent extension updates the agent's version. This applies to a direct agent and a System Center Operations Manager agent (in the latter, the Operations Manager and Log Analytics agent share common runtime libraries - which is updated in the process). If the installed Operations Manager agent is version 2012 and is upgraded, manageability capabilities can be lost when the Operations Manager server is also version 2012. Consider opting out of automatic provisioning if the installed Operations Manager agent is version 2012.
If you want to avoid creation of multiple workspaces per subscription and you have your own custom workspace within the subscription, then you have two options:
You can opt out of automatic provisioning. After migration, set the default workspace settings as described in How can I use my existing Log Analytics workspace?
Or, you can allow the migration to complete, the Log Analytics agent to be installed on the VMs, and the VMs connected to the created workspace. Then, select your own custom workspace by setting the default workspace setting with opting in to reconfiguring the already installed agents. For more information, see How can I use my existing Log Analytics workspace?
What are the implications of opting out of automatic provisioning?
When migration is complete, Defender for Cloud can't collect security data from the VM and some security recommendations and alerts are unavailable. If you opt out, install the Log Analytics agent manually. See recommended steps when opting out.
What are the recommended steps when opting out of automatic provisioning?
Manually install the Log Analytics agent extension so Defender for Cloud can collect security data from your VMs and provide recommendations and alerts. See agent installation for Windows VM or agent installation for Linux VM for guidance on installation.
You can connect the agent to any existing custom workspace or Defender for Cloud created workspace. If a custom workspace doesn't have the "Security" or "SecurityCenterFree" solutions enabled, you need to apply a solution. To apply, select the custom workspace and apply a pricing tier via the Environment settings > Defender plans page.
Defender for Cloud enables the correct solution on the workspace based on the selected options.
How do I remove OMS extensions installed by Defender for Cloud?
You can manually remove the Log Analytics agent but it isn't recommended. Removing OMS extensions limits Defender for Cloud's recommendations and alerts.
Note
If data collection is enabled, Defender for Cloud will reinstall the agent after you remove it. You must disable data collection before manually removing the agent. See How do I stop the automatic agent installation and workspace creation? for instructions on disabling data collection.
To manually remove the agent:
In the portal, open Log Analytics.
On the Log Analytics page, select a workspace:
Select the VMs that you don't want to monitor and select Disconnect.
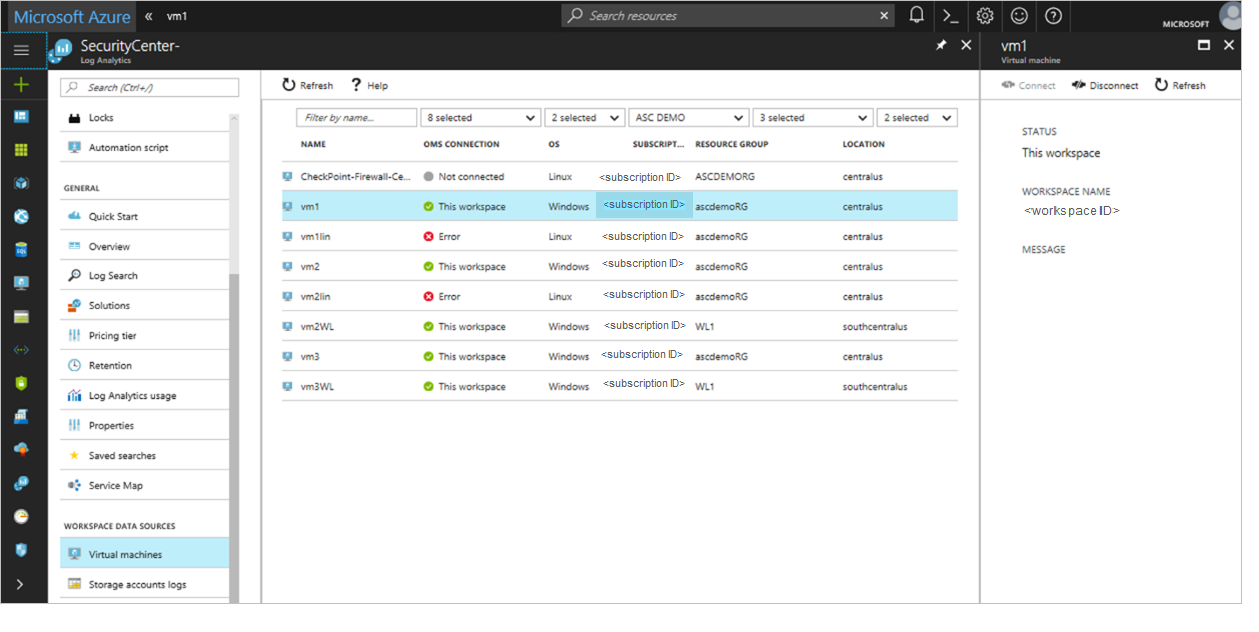
Note
If a Linux VM already has a non-extension OMS agent, removing the extension removes the agent as well and you have to reinstall it.
Will Defender for Cloud work using an OMS gateway?
Yes. Microsoft Defender for Cloud uses Azure Monitor to collect data from Azure VMs and servers, using the Log Analytics agent. To collect the data, each VM and server must connect to the Internet using HTTPS. The connection can be direct, using a proxy, or through the OMS Gateway.
Does the Log Analytics agent affect the performance of my servers?
The agent consumes a nominal amount of system resources and should have little effect on the performance. For more information on performance effect and the agent and extension, see the planning and operations guide.
Agentless
Which data is collected from snapshots?
Agentless scanning collects data similar to the data an agent collects to perform the same analysis. Raw data, PIIs or sensitive business data isn't collected, and only metadata results are sent to Defender for Cloud.
What are the costs related to agentless scanning?
Agentless scanning is included in Defender Cloud Security Posture Management (CSPM) and Defender for Servers P2 plans. No other costs incur to Defender for Cloud when enabling it.
Note
AWS charges for retention of disk snapshots. The Defender for Cloud scanning process actively tries to minimize the period during which a snapshot is stored in your account (typically up to a few minutes). AWS might charge an overhead cost for the disk snapshots storage. Check with AWS to see what costs apply to you.
How can I track AWS costs incurred for the disk snapshots created by Defender for Cloud agentless scanning?
Disk snapshots are created with the CreatedBy tag key, and the Microsoft Defender for Cloud tag value. The CreatedBy tag tracks who created the resource.
You need to activate the tags in the Billing and Cost Management console. It can take up to 24 hours for tags to activate.
Once you have activated the tags, AWS generates a cost allocation report as a comma-separated value (.CSV file) with your usage and cost grouped by your active tags.
Workspaces
Am I billed for Azure Monitor logs on the workspaces created by Defender for Cloud?
There's a 500-MB free data ingestion for each workspace. It's calculated per node, per reported workspace, per day, and available for every workspace that has a 'Security' or 'AntiMalware' solution installed. You're charged for any data ingested over the 500-MB limit.
Workspaces created by Defender for Cloud, while configured for Azure Monitor logs per node billing, don't incur Azure Monitor logs charges. Defender for Cloud billing is always based on your Defender for Cloud security policy and the solutions installed on a workspace:
Enhanced security off – Defender for Cloud enables the "SecurityCenterFree" solution on the default workspace. There are no charges when there are no Defender plans enabled.
All Microsoft Defender for Cloud plans enabled – Defender for Cloud enables the "Security" solution on the default workspace.
For pricing details in your local currency or region, see the pricing page.
Note
The log analytics pricing tier of workspaces created by Defender for Cloud doesn't affect Defender for Cloud billing.
Note
This article was recently updated to use the term Azure Monitor logs instead of Log Analytics. Log data is still stored in a Log Analytics workspace and is still collected and analyzed by the same Log Analytics service. We are updating the terminology to better reflect the role of logs in Azure Monitor. See Azure Monitor terminology changes for details.
Where is the default Log Analytics workspace created?
The location of the default workspace depends on your Azure region:
- For VMs in the United States and Brazil, the workspace location is the United States
- For VMs in Canada, the workspace location is Canada
- For VMs in Europe, the workspace location is Europe
- For VMs in the UK, the workspace location is the UK
- For VMs in East Asia and Southeast Asia, the workspace location is Asia
- For VMs in Korea, the workspace location is Korea
- For VMs in India, the workspace location is India
- For VMs in Japan, the workspace location is Japan
- For VMs in China, the workspace location is China
- For VMs in Australia, the workspace location is Australia
Can I delete the default workspaces created by Defender for Cloud?
Deleting the default workspace isn't recommended. Defender for Cloud uses the default workspaces to store security data from your VMs. If you delete a workspace, Defender for Cloud is unable to collect this data and some security recommendations and alerts are unavailable.
To recover, remove the Log Analytics agent on the VMs connected to the deleted workspace. Defender for Cloud reinstalls the agent and creates new default workspaces.
How can I use my existing Log Analytics workspace?
You can select an existing Log Analytics workspace to store data collected by Defender for Cloud. To use your existing Log Analytics workspace:
- The workspace must be associated with your selected Azure subscription.
- At a minimum, you must have read permissions to access the workspace.
Note
To get security alerts from that agent, make sure that the Log Analytics agent and the machine on which the agent is running both report to a Log Analytics workspace in the same tenant.
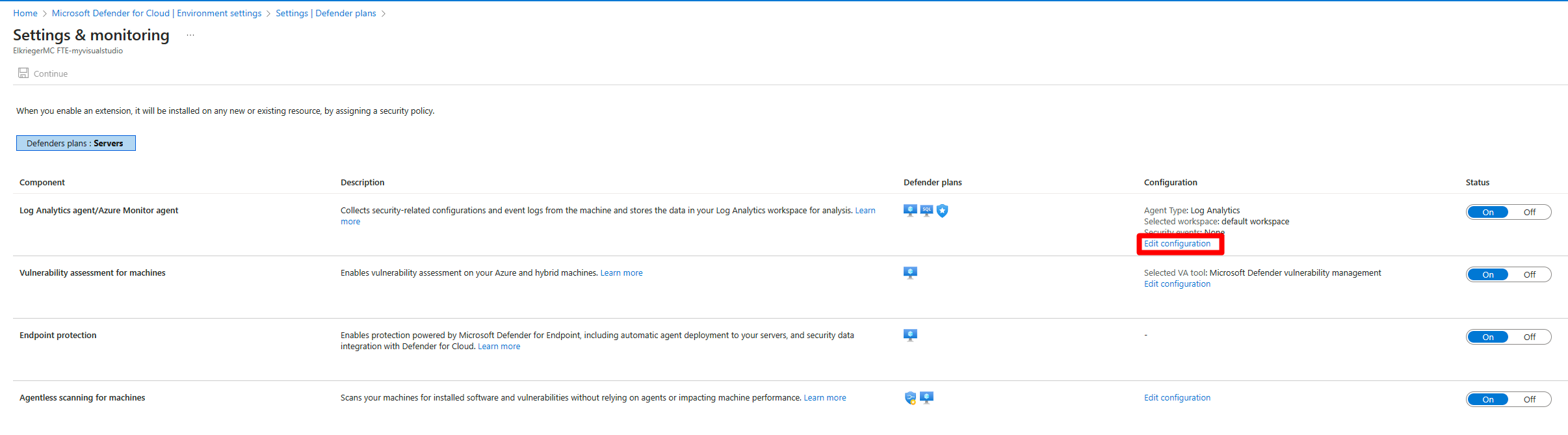
To select an existing Log Analytics workspace:
From Defender for Cloud's menu, open Environment settings.
Select the relevant subscription.
In the Monitoring coverage column of the Defender for Server plan, select Settings.
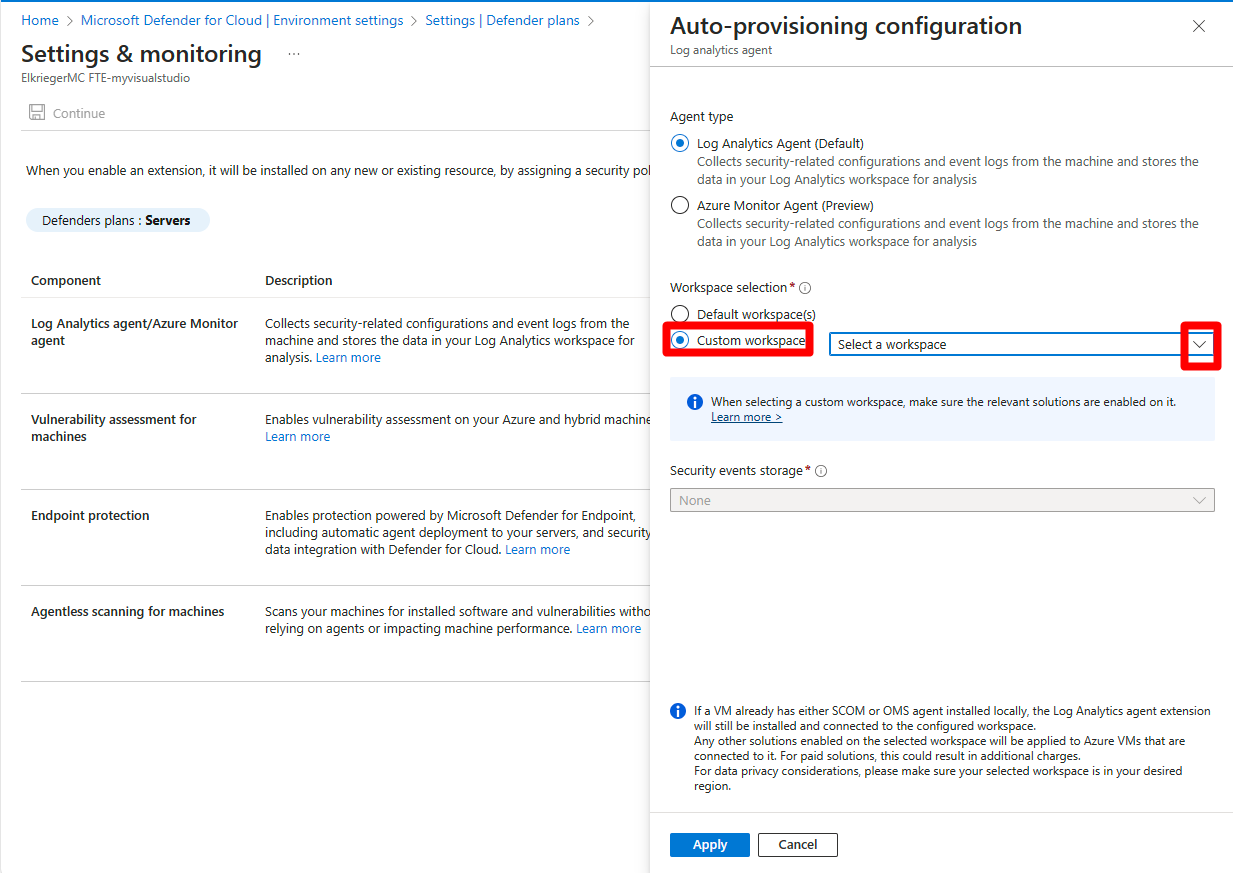
For the Log Analytics agent, select Edit configuration.
Select Custom workspace and select your existing workspace.
Tip
The list only includes workspaces to which you have access and which are in your Azure subscription.
Select Apply.
Select Continue.
Select Save and confirm that you want to reconfigure monitored VMs.
Important
This choice is only relevant if you're changing the configuration from the default workspace to a custom workspace. If you're changing the setting from one custom workspace to another or from a custom workspace to the default workspace, the change isn't being applied to existing machines.
- Select No if you want the new workspace settings to apply on new VMs only. The new workspace settings only apply to new agent installations; newly discovered VMs that don't have the Log Analytics agent installed.
- Select Yes if you want the new workspace settings to apply on all VMs. In addition, every VM connected to a Defender for Cloud created workspace is reconnected to the new target workspace.
Note
If you select Yes, don't delete any workspaces created by Defender for Cloud until all VMs have been reconnected to the new target workspace. This operation fails if a workspace is deleted too early.
Does Defender for Cloud override any existing connections between VMs and workspaces?
If a VM already has the Log Analytics agent installed as an Azure extension, Defender for Cloud doesn't override the existing workspace connection. Instead, Defender for Cloud uses the existing workspace. The VM is protected if the "Security" or "SecurityCenterFree" solution has been installed on the workspace to which it's reporting.
A Defender for Cloud solution is installed on the workspace selected in the Data Collection screen if not present already, and the solution is applied only to the relevant VMs. When you add a solution, it's automatically deployed by default to all Windows and Linux agents connected to your Log Analytics workspace. Solution Targeting allows you to apply a scope to your solutions.
Tip
If the Log Analytics agent is installed directly on the VM (not as an Azure extension), Defender for Cloud doesn't install the Log Analytics agent, and security monitoring is limited.
Does Defender for Cloud install solutions on my existing Log Analytics workspaces? What are the billing implications?
When Defender for Cloud identifies that a VM is already connected to a workspace you created, Defender for Cloud enables solutions on this workspace according to your pricing configuration. The solutions are applied only to the relevant resources, via solution targeting, so the billing remains the same.
No Defender plans are enabled – Defender for Cloud installs the "SecurityCenterFree" solution on the workspace and you aren't billed for it.
Enable all Microsoft Defender plans – Defender for Cloud installs the 'Security' solution on the workspace.
I already have workspaces in my environment, can I use them to collect security data?
If a VM already has the Log Analytics agent installed as an Azure extension, Defender for Cloud uses the existing connected workspace. A Defender for Cloud solution is installed on the workspace if not present already, and the solution is applied only to the relevant VMs via solution targeting.
When Defender for Cloud installs the Log Analytics agent on VMs, it uses the default workspaces created by Defender for Cloud if it's not pointed to an existing workspace.
I already have security solution on my workspaces. What are the billing implications?
The Security & Audit solution is used to enable Microsoft Defender for Servers. If the Security & Audit solution is already installed on a workspace, Defender for Cloud uses the existing solution. There's no change in billing.