Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Microsoft Defender for Cloud provides vulnerability assessment for your Azure SQL databases. Vulnerability assessment scans your databases for software vulnerabilities and provides a list of findings. You can use the findings to remediate software vulnerabilities and disable findings.
Prerequisites
Make sure that you know whether you're using the express or classic configurations before you continue.
To see which configuration you're using:
- In the Azure portal, open the specific resource in Azure SQL Database, SQL Managed Instance Database, or Azure Synapse.
- Under the Security heading, select Defender for Cloud.
- In the Enablement Status, select Configure to open the Microsoft Defender for SQL settings pane for either the entire server or managed instance.
If the vulnerability settings show the option to configure a storage account, you're using the classic configuration. If not, you're using the express configuration.
Find vulnerabilities in your Azure SQL databases
Permissions
One of the following permissions is required to see vulnerability assessment results in the Microsoft Defender for Cloud recommendation SQL databases should have vulnerability findings resolved:
- Security Admin
- Security Reader
The following permissions are required to changes vulnerability assessment settings:
- SQL Security Manager
If you're receiving any automated emails with links to scan results the following permissions are required to access the links about scan results or to view scan results at the resource-level:
- SQL Security Manager
Data residency
SQL vulnerability assessment queries the SQL server using publicly available queries under Defender for Cloud recommendations for SQL vulnerability assessment, and stores the query results. SQL vulnerability assessment data is stored in the location of the logical server it's configured on. For example, if the user enabled vulnerability assessment on a logical server in West Europe, the results will be stored in West Europe. This data will be collected only if the SQL vulnerability assessment solution is configured on the logical server.
On-demand vulnerability scans
You can run SQL vulnerability assessment scans on-demand:
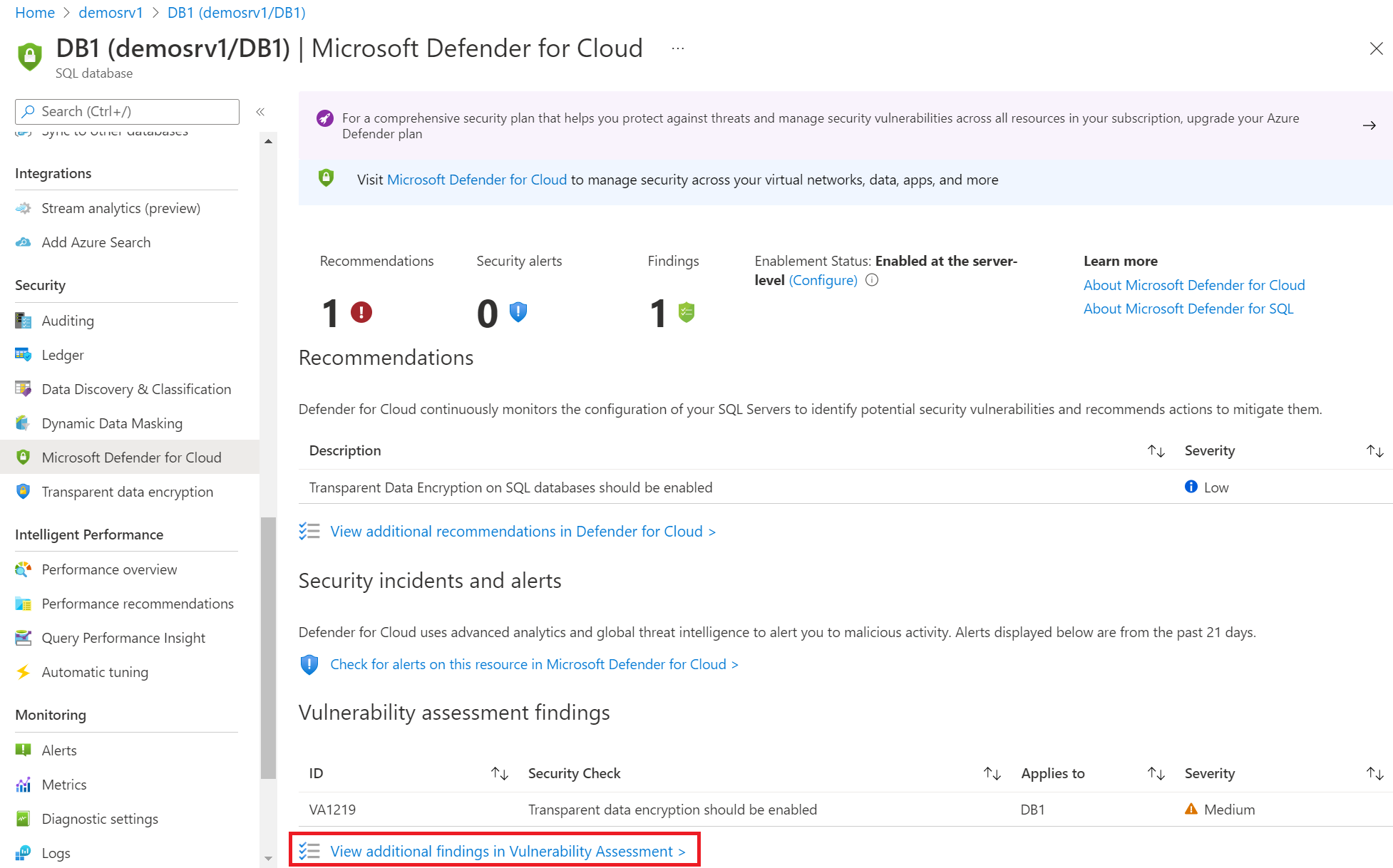
From the resource's Defender for Cloud page, select View additional findings in Vulnerability Assessment to access the scan results from previous scans.
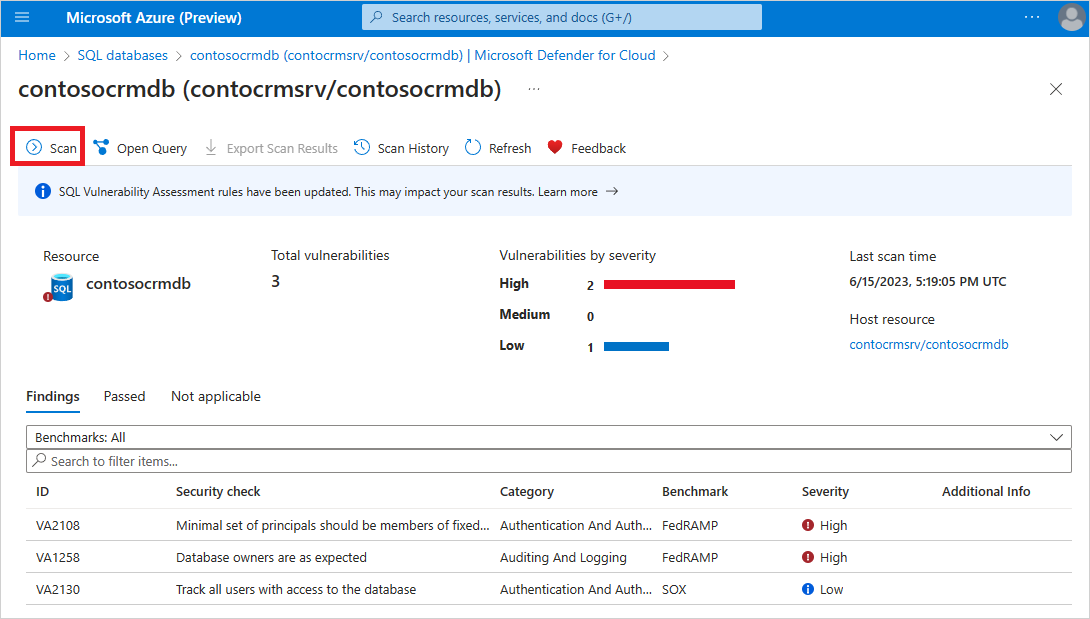
To run an on-demand scan to scan your database for vulnerabilities, select Scan from the toolbar:
Note
The scan is lightweight and safe. It takes a few seconds to run and is entirely read-only. It doesn't make any changes to your database.
Remediate vulnerabilities
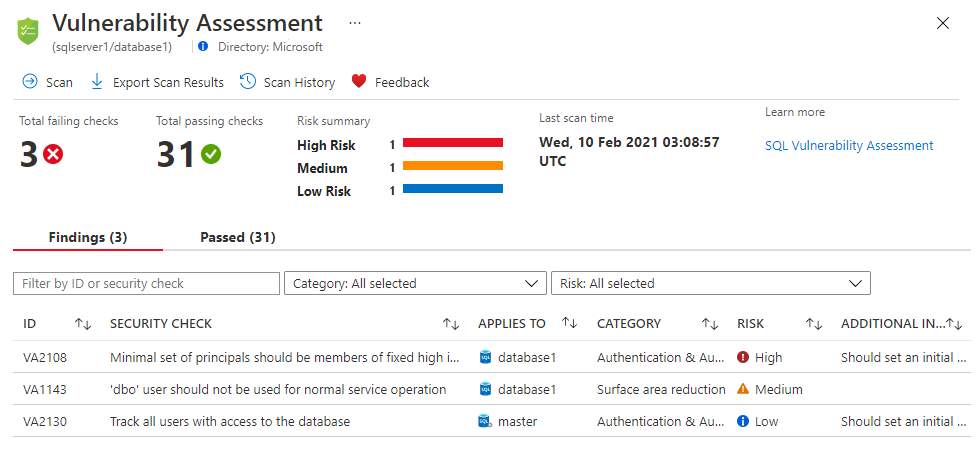
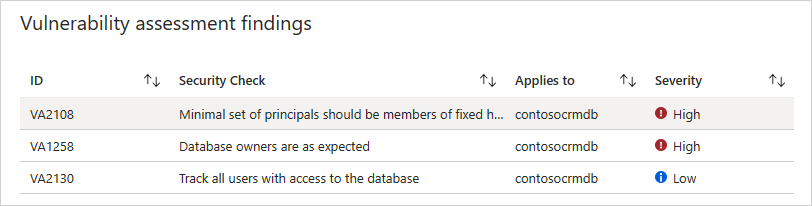
When a vulnerability scan completes, the report is displayed in the Azure portal. The report presents:
- An overview of your security state
- The number of issues that were found
- A summary by severity of the risks
- A list of the findings for further investigations
To remediate the vulnerabilities discovered:
Review your results and determine which of the report's findings are true security issues for your environment.
Select each failed result to understand its impact and why the security check failed.
Tip
The findings details page includes actionable remediation information explaining how to resolve the issue.
As you review your assessment results, you can mark specific results as being an acceptable baseline in your environment. A baseline is essentially a customization of how the results are reported. In subsequent scans, results that match the baseline are considered as passes. After you've established your baseline security state, vulnerability assessment only reports on deviations from the baseline. In this way, you can focus your attention on the relevant issues.
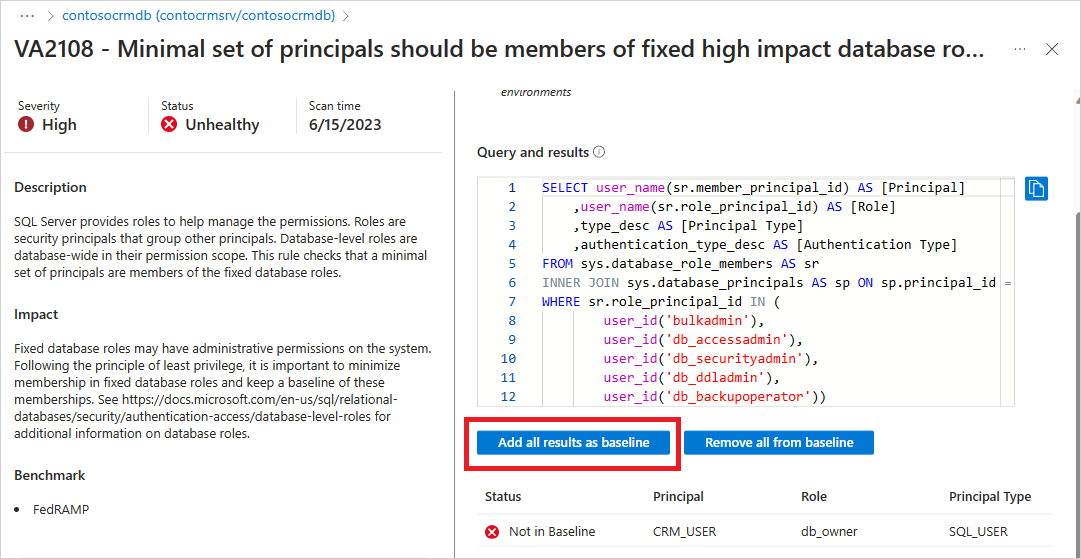
Any findings you've added to the baseline will now appear as Passed with an indication that they've passed because of the baseline changes. There's no need to run another scan for the baseline to take effect.

Your vulnerability assessment scans can now be used to ensure that your database maintains a high level of security, and that your organizational policies are met.
Next steps
- Learn more about Microsoft Defender for Azure SQL.
- Learn more about data discovery and classification.
- Learn more about storing vulnerability assessment scan results in a storage account accessible behind firewalls and VNets.