Implement Azure Policy with Azure DevOps release pipelines
Azure DevOps Services
Learn how to enforce compliance policies on your Azure resources before and after deployment with Azure Pipelines. Azure Pipelines lets you build, test, and deploy with continuous integration (CI) and continuous delivery (CD) using Azure DevOps. One scenario for adding Azure Policy to a pipeline is when you want to ensure that resources are deployed only to authorized regions and are configured to send diagnostics logs to Azure Log Analytics.
You can use either the classic pipeline or YAML pipeline processes to implement Azure Policy in your CI/CD pipelines.
For more information, see What is Azure Pipelines? and Create your first pipeline.
Prepare
Create an Azure Policy in the Azure portal. There are several predefined sample policies that can be applied to a management group, subscription, and resource group.
In Azure DevOps, create a release pipeline that contains at least one stage, or open an existing release pipeline.
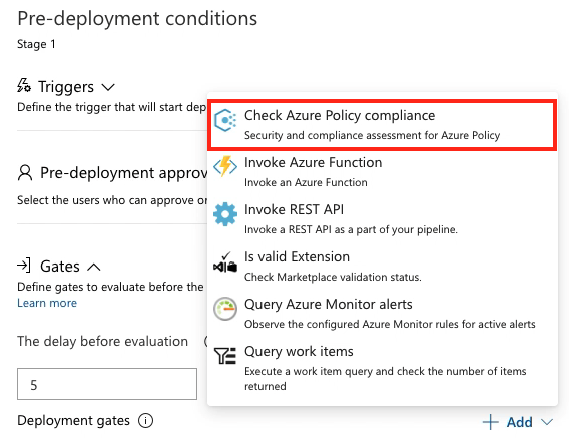
Add a pre- or post-deployment condition that includes the Check Azure Policy compliance task as a gate. More details.
If you're using a YAML pipeline definition, then use the AzurePolicyCheckGate@0 Azure Pipelines task.
Validate for any violation(s) during a release
Note
Use the AzurePolicyCheckGate task to check for policy compliance in YAML. This task can only be used as a gate and not in a build or a release pipeline.
Navigate to your team project in Azure DevOps.
In the Pipelines section, open the Releases page and create a new release.
Choose the In progress link in the release view to open the live logs page.
When the release is in progress and attempts to perform an action disallowed by the defined policy, the deployment is marked as Failed. The error message contains a link to view the policy violations.
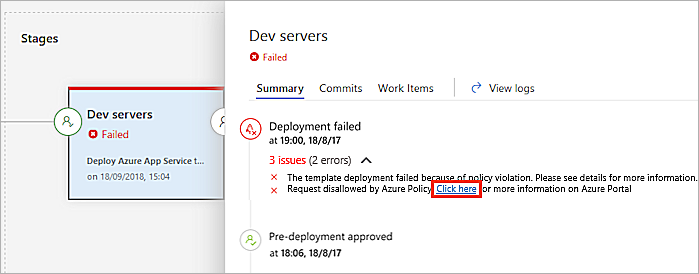
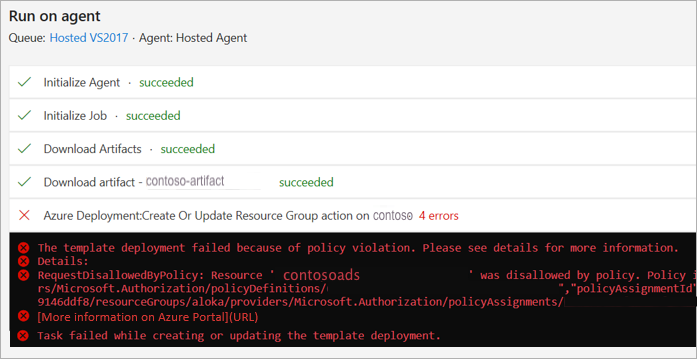
An error message is written to the logs and displayed in the stage status panel in the releases page of Azure Pipelines.
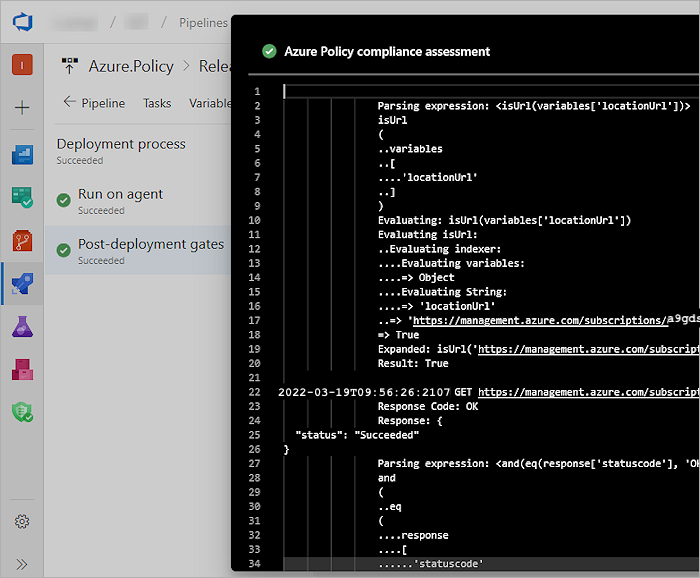
When the policy compliance gate passes the release, a Succeeded status is displayed.
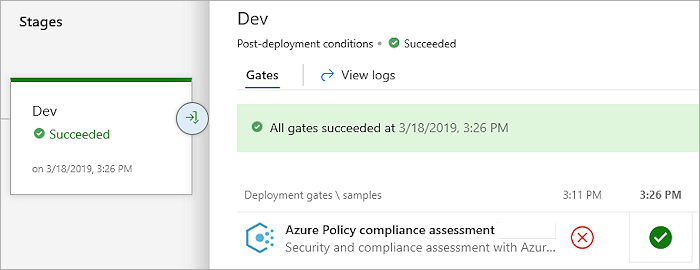
Choose the successful deployment to view the detailed logs.
Next steps
To learn more about the structures of policy definitions, look at this article:
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for