Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
This article lists sample use cases for Microsoft Sentinel playbooks, as well as sample playbooks and recommended playbook templates.
Recommended playbook use cases
We recommend starting with Microsoft Sentinel playbooks for the following SOC scenarios, for which we provide ready-made playbook templates out-of-the-box.
Enrichment: Collect and attach data to an incident to make smarter decisions
If your Microsoft Sentinel incident is created from an alert and analytics rule that generates IP address entities, configure the incident to trigger an automation rule to run a playbook and gather more information.
Configure your playbook with the following steps:
Start the playbook when the incident is created. The entities represented in the incident are stored in the incident trigger's dynamic fields.
For each IP address, configure the playbook to query an external Threat Intelligence provider, such as Virus Total, to retrieve more data.
Add the returned data and insights as comments of the incident to enrich your investigation.
Bi-directional sync for Microsoft Sentinel incidents with other ticketing systems
To sync your Microsoft Sentinel incident data with a ticketing system, such as ServiceNow:
Create an automation rule for all incident creation.
Attach a playbook that's triggered when a new incident is created.
Configure the playbook to create a new ticket in ServiceNow using the ServiceNow connector.
Make sure that your teams can easily jump from the ServiceNow ticket back to your Microsoft Sentinel incident by configuring the playbook to include the incident name, important fields, and a URL to the Microsoft Sentinel incident in the ServiceNow ticket.
Orchestration: Control the incidents queue from your SOC chat platform
If your Microsoft Sentinel incident is created from an alert and analytics rule that generates username and IP address entities, configure the incident to trigger an automation rule to run a playbook and contact your team over your standard communications channels.
Configure your playbook with the following steps:
Start the playbook when the incident is created. The entities represented in the incident are stored in the incident trigger's dynamic fields.
Configure the playbook to send a message to your security operations communications channel, such as in Microsoft Teams or Slack to make sure your security analysts are aware of the incident.
Configure the playbook to send all the information in the alert by email to your senior network admin and security admin. The email message includes Block and Ignore user option buttons.
Configure the playbook to wait until a response is received from the admins, then continue to run.
If the admins select Block, configure the playbook to send a command to the firewall to block the IP address in the alert, and another to Microsoft Entra ID to disable the user.
Response to threats immediately with minimal human dependencies
This section provides two examples, responding to threats of a compromised user and a compromised machine.
In case of a compromised user, such as discovered by Microsoft Entra ID Protection:
Start your playbook when a new Microsoft Sentinel incident is created.
For each user entity in the incident that's suspected as compromised, configure the playbook to:
Send a Teams message to the user, requesting confirmation that the user took the suspicious action.
Check with Microsoft Entra ID Protection to confirm the user's status as compromised. Microsoft Entra ID Protection labels the user as risky, and apply any enforcement policy already configured - for example, to require the user to use MFA when next signing in.
Note
This particular Microsoft Entra action does not initiate any enforcement activity on the user, nor does it initiate any configuration of enforcement policy. It only tells Microsoft Entra ID Protection to apply any already defined policies as appropriate. Any enforcement depends entirely on the appropriate policies being defined in Microsoft Entra ID Protection.
In case of a compromised machine, such as discovered by Microsoft Defender for Endpoint:
Start your playbook when a new Microsoft Sentinel incident is created.
Configure your playbook with the Entities - Get Hosts action to parse the suspicious machines that are included in the incident entities.
Configure your playbook to issue a command to Microsoft Defender for Endpoint to isolate the machines in the alert.
Respond manually during an investigation or while hunting without leaving context
Use the entity trigger to take immediate action on individual threat actors you discover during an investigation, one at a time, right from within your investigation. This option is also available in the threat hunting context, unconnected to any particular incident.
Select an entity in context and perform actions on it right there, saving time and reducing complexity.
Playbooks with entity triggers support actions such as:
- Blocking a compromised user.
- Blocking traffic from a malicious IP address in your firewall.
- Isolating a compromised host on your network.
- Adding an IP address to a safe/unsafe address watchlist, or to your external configuration management database (CMDB).
- Getting a file hash report from an external threat intelligence source and adding it to an incident as a comment.
Recommended playbook templates
This section lists recommended playbooks, and other similar playbooks are available to you in the Content hub, or in the Microsoft Sentinel GitHub repository.
Notification playbook templates
Notification playbooks are triggered when an alert or incident is created and send a notification to a configured destination:
| Playbook | Folder in GitHub repository |
Solution in Content hub/ Azure Marketplace |
|---|---|---|
| Post a message in a Microsoft Teams channel | Post-Message-Teams | Sentinel SOAR Essentials Solution |
| Send an Outlook email notification | Send-basic-email | Sentinel SOAR Essentials Solution |
| Post a message in a Slack channel | Post-Message-Slack | Sentinel SOAR Essentials Solution |
| Send Microsoft Teams adaptive card on incident creation | Send-Teams-adaptive-card-on-incident-creation | Sentinel SOAR Essentials Solution |
Blocking playbook templates
Blocking playbooks are triggered when an alert or incident is created, gather entity information like the account, IP address, and host, and blocks them from further actions:
| Playbook | Folder in GitHub repository |
Solution in Content hub/ Azure Marketplace |
|---|---|---|
| Block an IP address in Azure Firewall | AzureFirewall-BlockIP-addNewRule | Azure Firewall Solution for Sentinel |
| Block a Microsoft Entra user | Block-AADUser | Microsoft Entra solution |
| Reset a Microsoft Entra user password | Reset-AADUserPassword | Microsoft Entra solution |
| Isolate or unisolate device using Microsoft Defender for Endpoint |
Isolate-MDEMachine Unisolate-MDEMachine |
Microsoft Defender for Endpoint solution |
Create, update, or close playbook templates
Create, update, or close playbooks can create, update, or close incidents in Microsoft Sentinel, Microsoft 365 security services, or other ticketing systems:
| Playbook | Folder in GitHub repository |
Solution in Content hub/ Azure Marketplace |
|---|---|---|
| Create an incident using Microsoft Forms | CreateIncident-MicrosoftForms | Sentinel SOAR Essentials solution |
| Relate alerts to incidents | relateAlertsToIncident-basedOnIP | Sentinel SOAR Essentials solution |
| Create a Service Now incident | Create-ServiceNow-record | ServiceNow solution |
Commonly used playbook configurations
This section provides sample screenshots for commonly used playbook configurations, including updating an incident, using incident details, adding comments to an incident, or disabling a user.
Update an incident
This section provides sample screenshots of how you might use a playbook to update an incident based on a new incident or alert.
Update an incident based on a new incident (incident trigger):

Update an incident based on a new alert (alert trigger):

Use incident details in your flow
This section provides sample screenshots of how you might use your playbook to use incident details elsewhere in your flow:
Send incident details by mail, using a playbook triggered by a new incident:
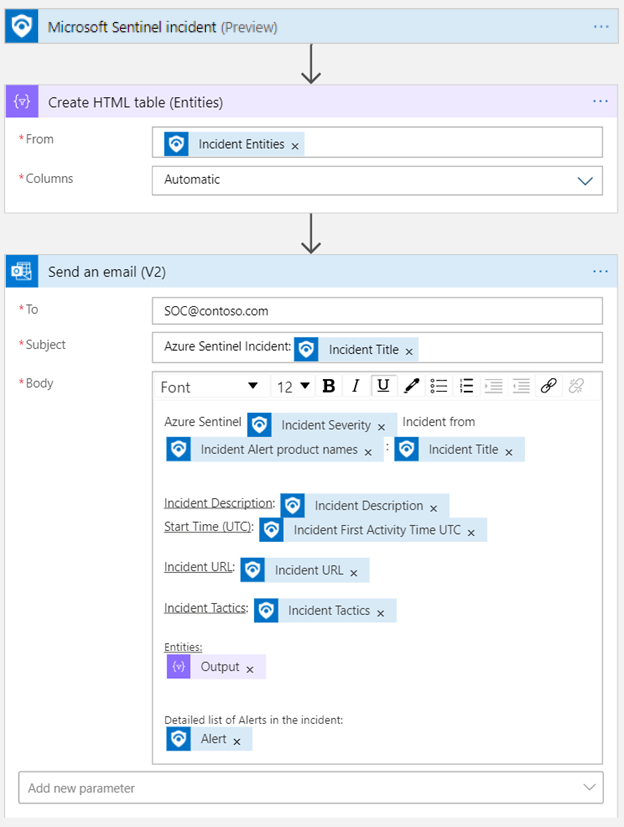
Send incident details by mail, using a playbook triggered by a new alert:

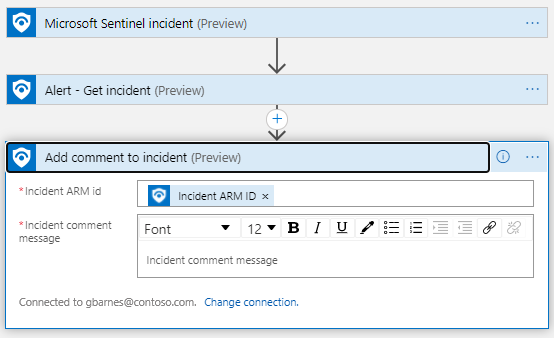
Add a comment to an incident
This section provides sample screenshots of how you might use your playbook to add comments to an incident:
Add a comment to an incident, using a playbook triggered by a new incident:

Add a comment to an incident, using a playbook triggered by a new alert:
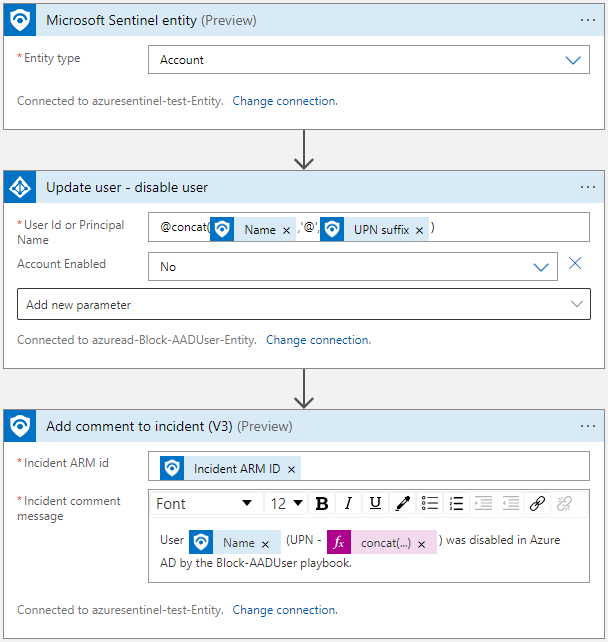
Disable a user
The following screenshot shows an example of how you might use your playbook to disable a user account, based on a Microsoft Sentinel entity trigger: