Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this quickstart, you'll enable Microsoft Sentinel and install a solution from the content hub. Then, you'll set up a data connector to start ingesting data into Microsoft Sentinel.
Microsoft Sentinel comes with many data connectors for Microsoft products such as the Microsoft Defender XDR service-to-service connector. You can also enable built-in connectors for non-Microsoft products such as Syslog or Common Event Format (CEF). For this quickstart, you'll use the Azure Activity data connector that's available in the Azure Activity solution for Microsoft Sentinel.
To onboard to Microsoft Sentinel by using the API, see the latest supported version of Sentinel Onboarding States.
Prerequisites
Active Azure Subscription. If you don't have one, create a free account before you begin.
Permissions:
To enable Microsoft Sentinel, you need contributor permissions to the subscription in which the Microsoft Sentinel workspace resides.
To use Microsoft Sentinel, you need either Microsoft Sentinel Contributor or Microsoft Sentinel Reader permissions on the resource group that the workspace belongs to.
To install or manage solutions in the content hub, you need the Microsoft Sentinel Contributor role on the resource group that the workspace belongs to.
If you are a new Microsoft Sentinel customer and have permissions of a subscription Owner or a User access administrator, your workspace is automatically onboarded to the Defender portal. Users of such workspaces use Microsoft Sentinel in the Defender portal only.
Microsoft Sentinel is a paid service. Review the pricing options and the Microsoft Sentinel pricing page.
Before deploying Microsoft Sentinel to a production environment, review the predeployment activities and prerequisites for deploying Microsoft Sentinel.
Create a Log Analytics workspace
Microsoft Sentinel must be added to a workspace. If you already have a Log Analytics workspace, skip to adding Microsoft Sentinel to your Log Analytics workspace. If you don't already have a Log Analytics workspace, you can create one using the instructions below or, for a more detailed explanation, go to Create a Log Analytics workspace. For more information about Log Analytics workspaces, see Designing your Azure Monitor Logs deployment.
You may have a default of 30 days retention in the Log Analytics workspace used for Microsoft Sentinel. To make sure that you can use all Microsoft Sentinel functionality and features, raise the retention to 90 days. Configure data retention and archive policies in Azure Monitor Logs.
Sign in to the Azure portal.
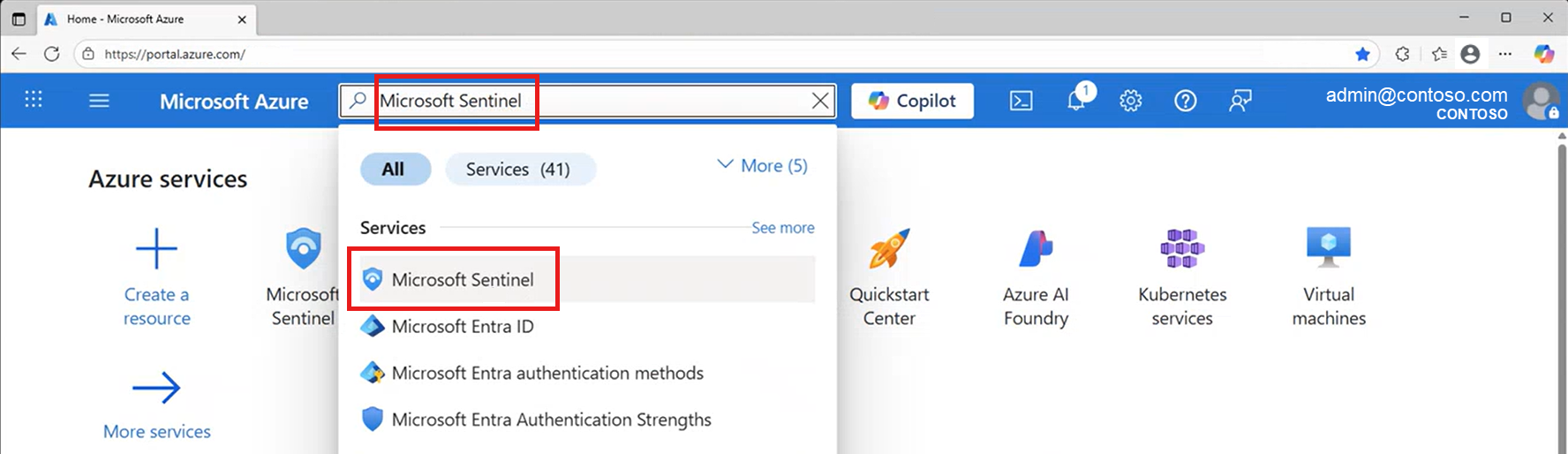
Search for and select Microsoft Sentinel.
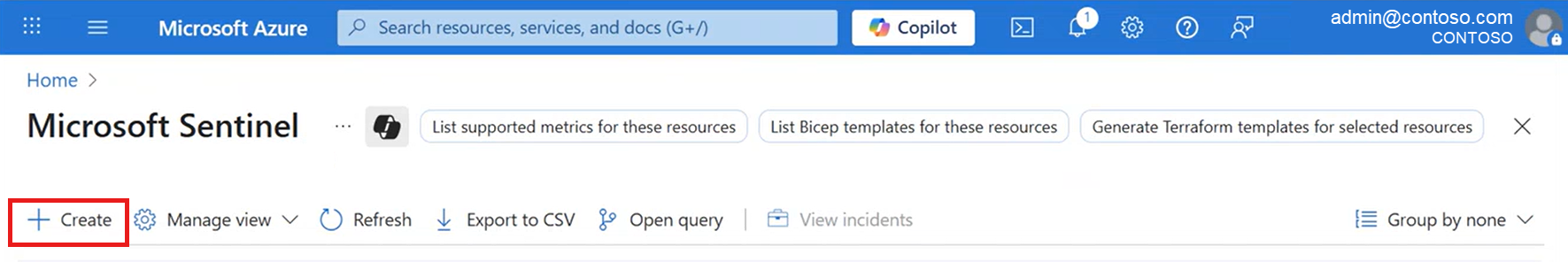
Select Create.
Select Create a new workspace.
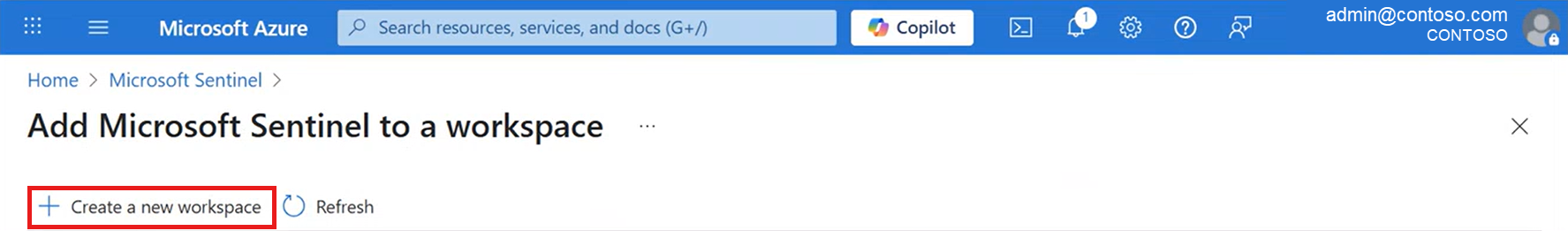
Under Subscription > Resource group, select Create new. Enter a name for your resource group and select OK.
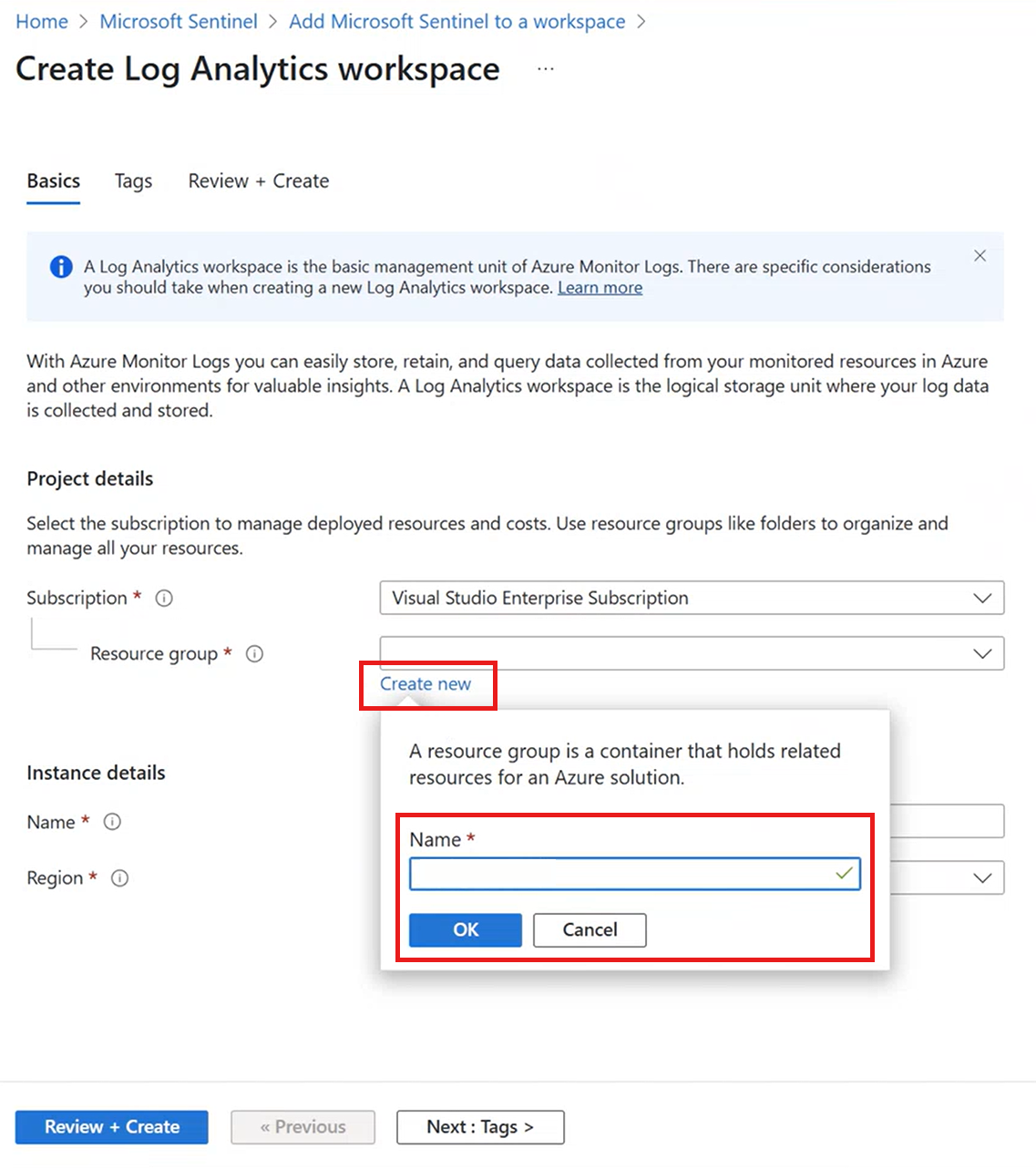
Give the workspace a name and select a region, then select Review + Create. (See which regions Log Analytics is available in.)
After validation has passed, select Create. Wait until your deployment is complete.
Add Microsoft Sentinel to your Log Analytics workspace
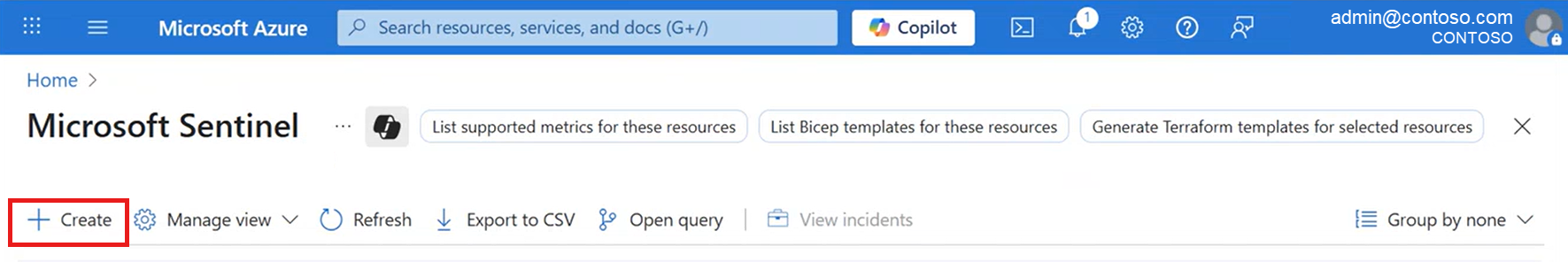
From the Azure portal, search for and select Microsoft Sentinel.
Select Create.
Select the workspace you want to use and select Add. You can run Microsoft Sentinel on more than one workspace, but data is isolated to a single workspace.
- The default workspaces created by Microsoft Defender for Cloud aren't shown in the list. You can't install Microsoft Sentinel on these workspaces.
- Once deployed on a workspace, Microsoft Sentinel doesn't support moving that workspace to another resource group or subscription.
Note
If your workspace isn't automatically onboarded to the Defender portal, we recommend onboarding for a unified experience in managing security operations (SecOps) across both Microsoft Sentinel and other Microsoft security services. For more information, see Onboard Microsoft Sentinel to the Defender portal.
If your workspace is automatically onboarded, or if you decide to onboard your workspace now, you can continue the procedures in this article from the Defender portal. If this is your first time using the Defender portal, there will be a delay of a few minutes while the process completes.
Access Microsoft Sentinel in the Defender portal
To access Microsoft Sentinel in the Defender portal:
Sign into the Defender portal.
The first time you access the Defender portal, it'll take some time to provision your tenant.
Once provisioned, you'll see Microsoft Sentinel available in the navigation pane, with Microsoft Sentinel nodes nested within. For example:

Scroll down in the navigation pane, and select Settings > Microsoft Sentinel > Workspaces to view the workspaces onboarded to the Defender portal and available to you.
The Defender portal supports multiple workspaces, with one workspace acting as the primary workspace per tenant. For more information, see Multiple Microsoft Sentinel workspaces in the Defender portal and Microsoft Defender multitenant management.
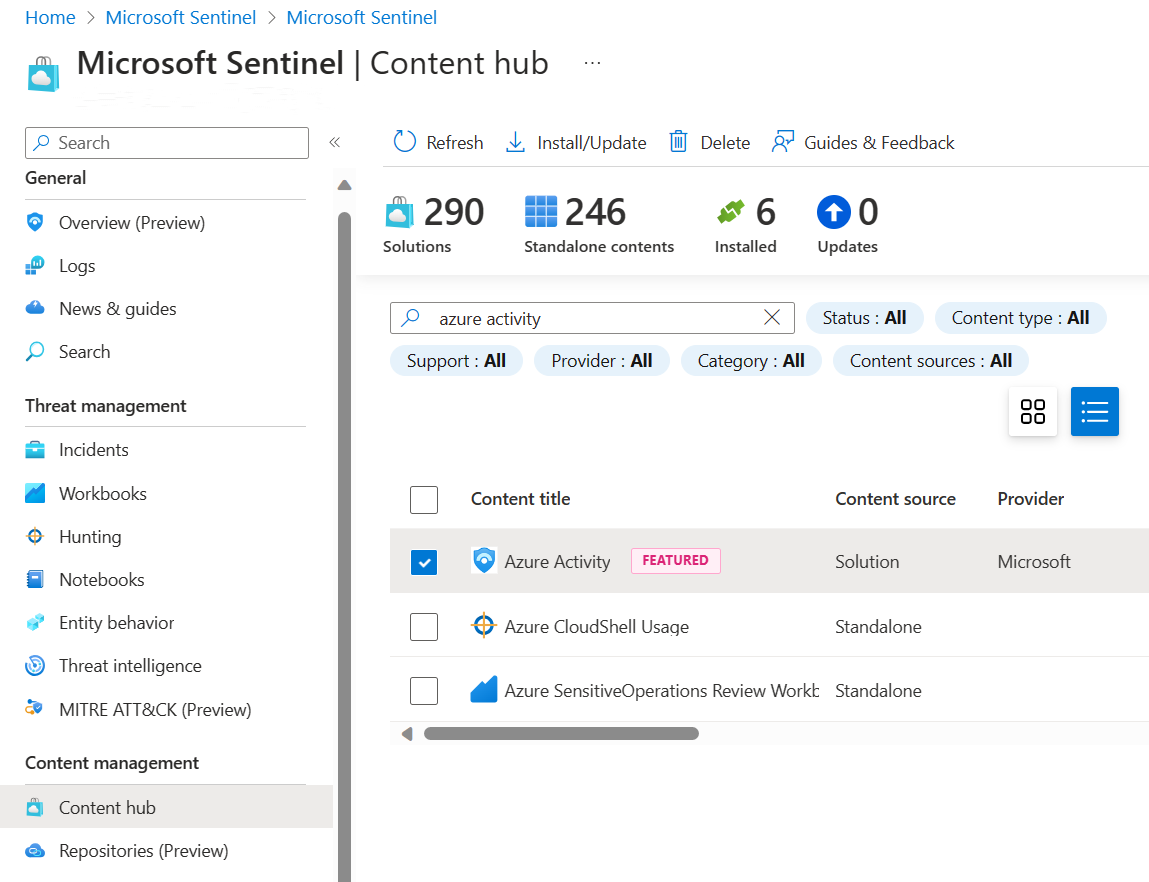
Install a solution from the content hub
The content hub in Microsoft Sentinel is the centralized location to discover and manage out-of-the-box content including data connectors. For this quickstart, install the solution for Azure Activity.
In Microsoft Sentinel, browse to the Content hub page, and find and select the Azure Activity solution.
On the solution details pane on the side, select Install.
Set up the data connector
Microsoft Sentinel ingests data from services and apps by connecting to the service and forwarding the events and logs to Microsoft Sentinel. For this quickstart, install the data connector to forward data for Azure Activity to Microsoft Sentinel.
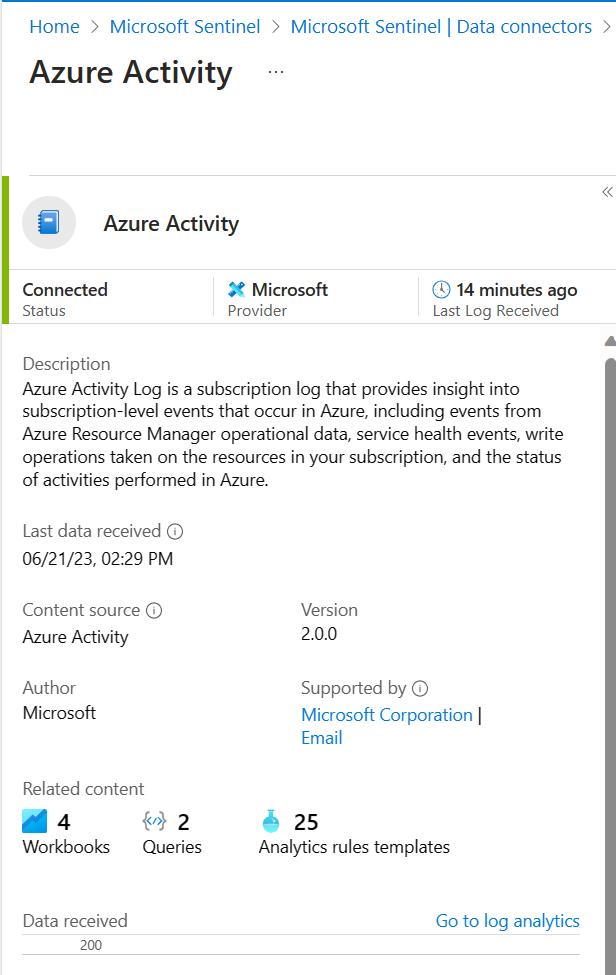
In Microsoft Sentinel, select Configuration > Data connectors and search for and select the Azure Activity data connector.
In the connector details pane, select Open connector page. Use the instructions on the Azure Activity connector page to set up the data connector.
Select Launch Azure Policy Assignment Wizard.
On the Basics tab, set the Scope to the subscription and resource group that has activity to send to Microsoft Sentinel. For example, select the subscription that contains your Microsoft Sentinel instance.
Select the Parameters tab, and set the Primary Log Analytics workspace. This should be the workspace where Microsoft Sentinel is installed.
Select Review + create and Create.
Generate activity data
Let's generate some activity data by enabling a rule that was included in the Azure Activity solution for Microsoft Sentinel. This step also shows you how to manage content in the content hub.
In Microsoft Sentinel, select Content hub and search for and select Suspicious Resource deployment rule template in the Azure Activity solution.
In the details pane, select Create rule to create a new rule using the Analytics rule wizard.
In the Analytics rule wizard - Create a new Scheduled rule page, change the Status to Enabled.
On this tab and all other tabs in the wizard, leave the default values as they are.
On the Review and create tab, select Create.
View data ingested into Microsoft Sentinel
Now that you've enabled the Azure Activity data connector and generated some activity data let's view the activity data added to the workspace.
In Microsoft Sentinel, select Configuration > Data connectors and search for and select the Azure Activity data connector.
In the connector details pane, select Open connector page.
Review the Status of the data connector. It should be Connected.
Select a tab to continue, depending on which portal you're using:
Select Go to log analytics to open the Advanced hunting page.
On the top of the pane, next to the New query tab, select the + to add a new query tab.
Run the following query to view the activity date ingested into the workspace:
AzureActivity
For example:

Next steps
In this quickstart, you enabled Microsoft Sentinel and installed a solution from the content hub. Then, you set up a data connector to start ingesting data into Microsoft Sentinel. You also verified that data is being ingested by viewing the data in the workspace.
If you're a new customer who's been automatically onboarded to the Defender portal, your users will access Microsoft Sentinel in the Defender portal only. As you use the Microsoft Sentinel documentation, make sure to select the Defender portal version of the documentation.
- To visualize the data you've collected by using the dashboards and workbooks, see Visualize collected data.
- To detect threats by using analytics rules, see Tutorial: Detect threats by using analytics rules in Microsoft Sentinel.