Access an app in Azure Spring Apps in a virtual network
Note
Azure Spring Apps is the new name for the Azure Spring Cloud service. Although the service has a new name, you'll see the old name in some places for a while as we work to update assets such as screenshots, videos, and diagrams.
This article applies to: ✔️ Basic/Standard ✔️ Enterprise
This article explains how to access an endpoint for your application in a private network.
When you assign an endpoint on an application in an Azure Spring Apps service instance deployed in your virtual network, the endpoint uses a private fully qualified domain name (FQDN). The domain is only accessible in the private network. Apps and services use the application endpoint. They include the Test Endpoint described in the View apps and deployments section of Set up a staging environment in Azure Spring Apps. Log streaming, described in Stream Azure Spring Apps app logs in real-time, also works only within the private network.
Prerequisites
- An Azure subscription. If you don't have a subscription, create a free account before you begin.
- (Optional) Azure CLI version 2.45.0 or higher.
- An existing application in an Azure Spring Apps service instance deployed to a virtual network. For more information, see Deploy Azure Spring Apps in a virtual network.
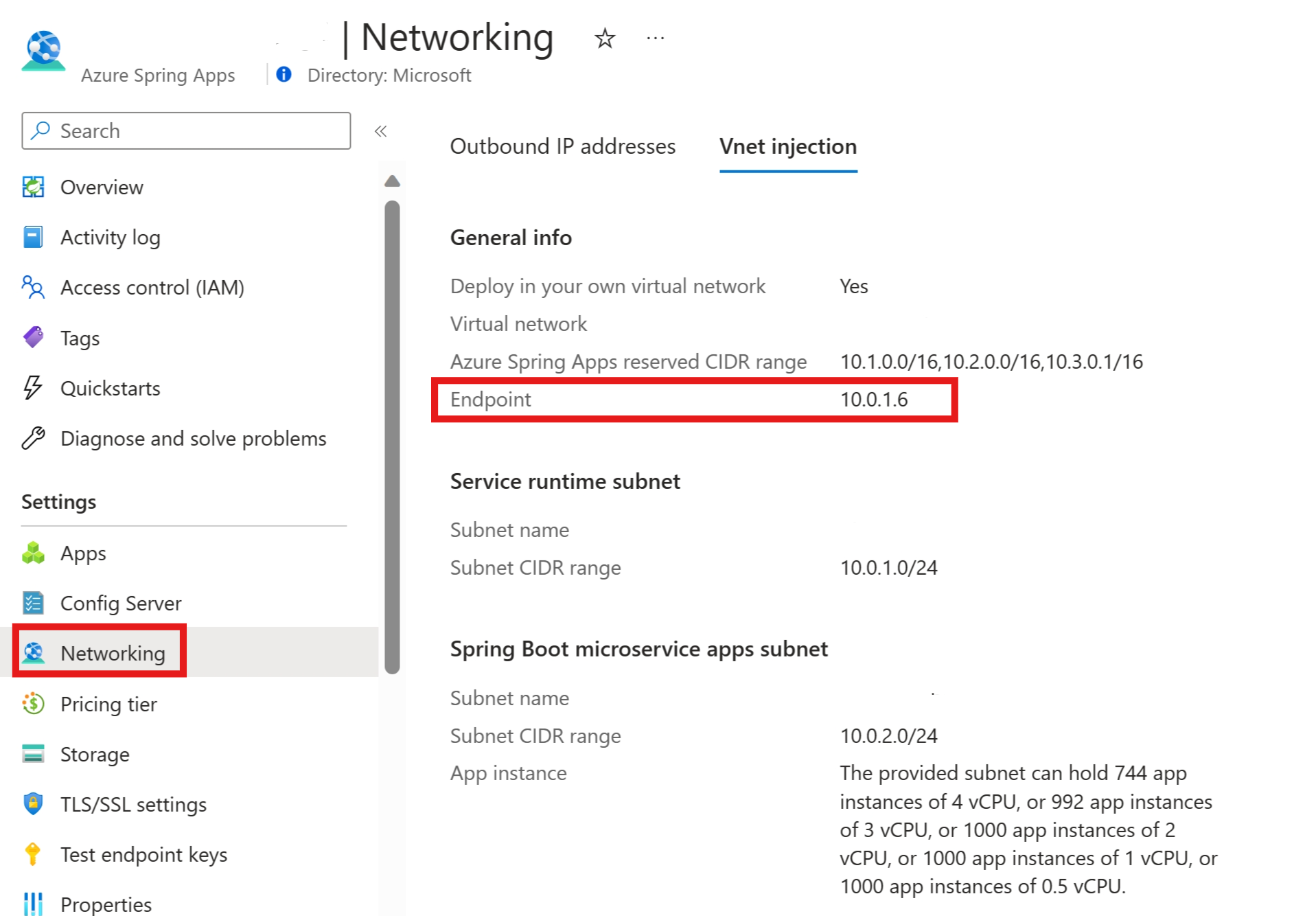
Find the IP for your application
Use the following steps to find the IP address for your application.
Add a DNS for the IP
If you have your own DNS solution for your virtual network, like Active Directory Domain Controller, Infoblox, or another, you need to point the domain *.private.azuremicroservices.io to the IP address. Otherwise, use the following instructions to create an Azure Private DNS Zone in your subscription to translate/resolve the private fully qualified domain name (FQDN) to its IP address.
Note
If you're using Microsoft Azure operated by 21Vianet, be sure to replace private.azuremicroservices.io with private.microservices.azure.cn in this article. For more information, see the Check Endpoints in Azure section of the Azure China developer guide.
Create a private DNS zone
Use the following steps to create a private DNS zone for an application in the private network:
Open the Azure portal. Using the search box, search for Private DNS zones. Select Private DNS zones from the search results.
On the Private DNS zones page, select Add.
Fill out the form on the Create Private DNS zone page. Enter private.azuremicroservices.io as the Name of the zone.
Select Review + Create.
Select Create.
It might take a few minutes to create the zone.
Link the virtual network
To link the private DNS zone to the virtual network, you need to create a virtual network link.
Use the following steps to link the private DNS zone you created to the virtual network holding your Azure Spring Apps service:
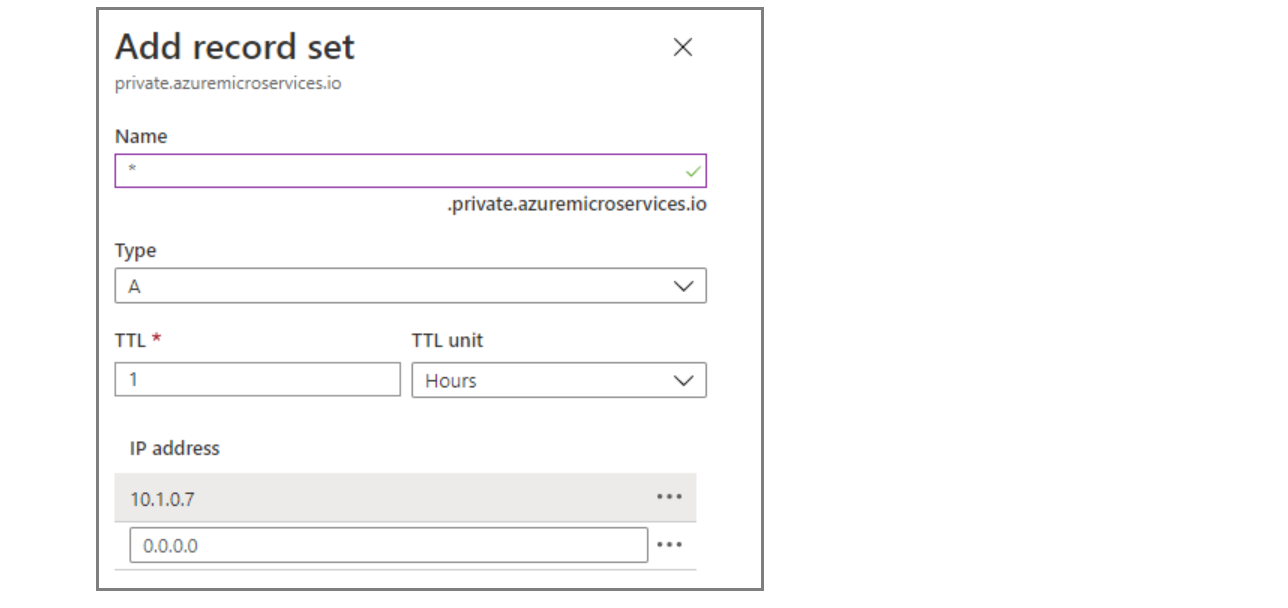
Create DNS record
You must create an "A" type record in the private DNS zone.
Use the following steps to use the private DNS zone to translate/resolve DNS.
Select the private DNS zone resource you created - for example, private.azuremicroservices.io.
Select Record set.
In Add record set, enter or select the following information:
Setting Value Name Enter *. Type Select A. TTL Enter 1. TTL unit Select Hours. IP address Enter the IP address. The following screenshot uses the IP address 10.1.0.7. Select OK.
Assign a private FQDN for your application
You can assign a private FQDN for your application after you deploy Azure Spring Apps in a virtual network. For more information, see Deploy Azure Spring Apps in a virtual network.
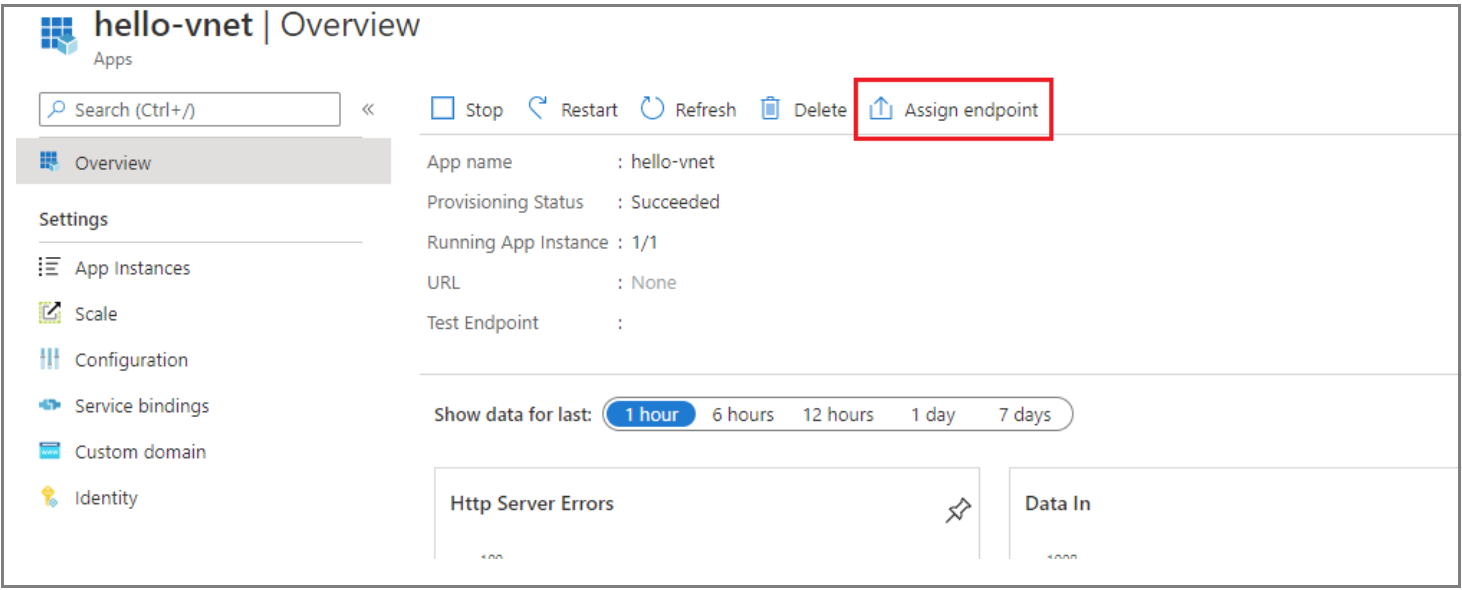
Use the following steps to assign a private FQDN:
Select the Azure Spring Apps service instance deployed in your virtual network, and open the Apps tab.
Select the application to open the Overview page.
Select Assign Endpoint to assign a private FQDN to your application. Assigning an FQDN can take a few minutes.
The assigned private FQDN (labeled URL) is now available. You can only access the URL within the private network, but not on the internet.
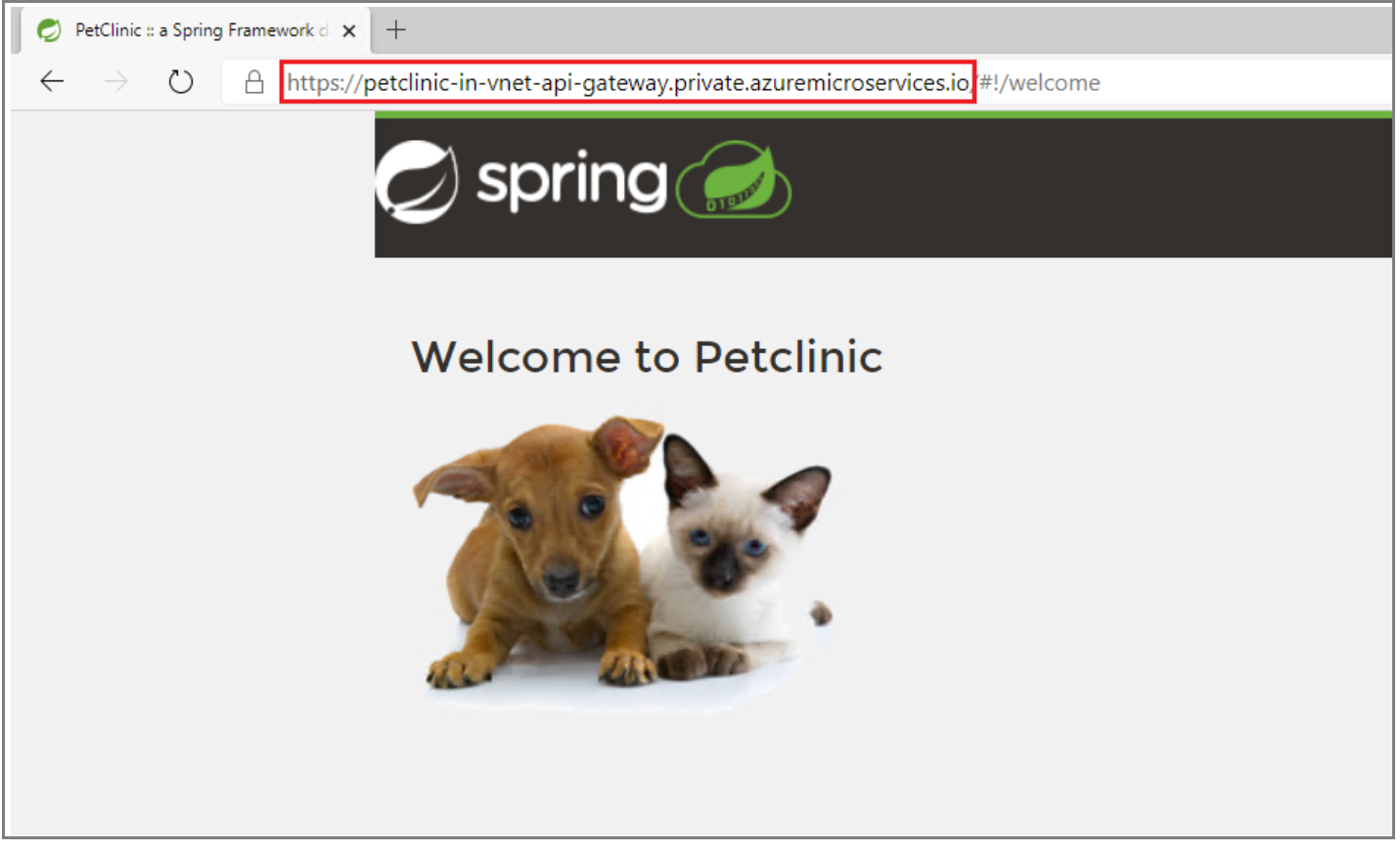
Access the application's private FQDN
After the assignment, you can access the application's private FQDN in the private network. For example, you can create a jumpbox machine in the same virtual network or in a peered virtual network. Then, on that jumpbox or virtual machine, you can access the private FQDN.
Clean up resources
If you plan to continue working with subsequent articles, you might want to leave these resources in place. When you no longer need them, delete the resource group, which deletes the resources in the resource group. To delete the resource group by using the Azure CLI, use the following command:
az group delete --name $RESOURCE_GROUP
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for