HTTP with Microsoft Entra ID (preauthorized)
Use the HTTP connector to fetch resources from various Web services, authenticated by Microsoft Entra ID, or from an on-premise web service.
This connector is available in the following products and regions:
| Service | Class | Regions |
|---|---|---|
| Logic Apps | Standard | All Logic Apps regions except the following: - US Department of Defense (DoD) |
| Power Automate | Premium | All Power Automate regions |
| Power Apps | Premium | All Power Apps regions |
| Contact | |
|---|---|
| Name | Microsoft |
| URL | Microsoft LogicApps Support Microsoft Power Automate Support Microsoft Power Apps Support |
| Connector Metadata | |
|---|---|
| Publisher | Microsoft |
Note
The HTTP with Microsoft Entra ID (preauthorized) connector enables users to submit requests to any HTTP endpoint that supports Entra ID authentication. As part of our ongoing efforts to enhance security and data privacy, we have reviewed the permissions associated with this connector and are planning to provide improved identity isolation controls.
Currently, the HTTP with Microsoft Entra ID (preauthorized) connector operates through a Microsoft 1st party trusted application. This application includes preauthorization for various Microsoft services, including but not limited to Microsoft Graph, SharePoint, and other Microsoft offerings. This preauthorization empowers the connector to interact with these services using delegated access on behalf of the user. Rest assured that this approach fully respects the user's privileges and does not permit access to data or actions beyond their authorized scope.
With the existing connector, there is no need for administrators to explicitly grant consent for actions to be executed by the application on behalf of the user. However, we released a new version of this connector. The new version of the connector uses a new application without any preauthorization. This allows an administrator to grant discrete consent.
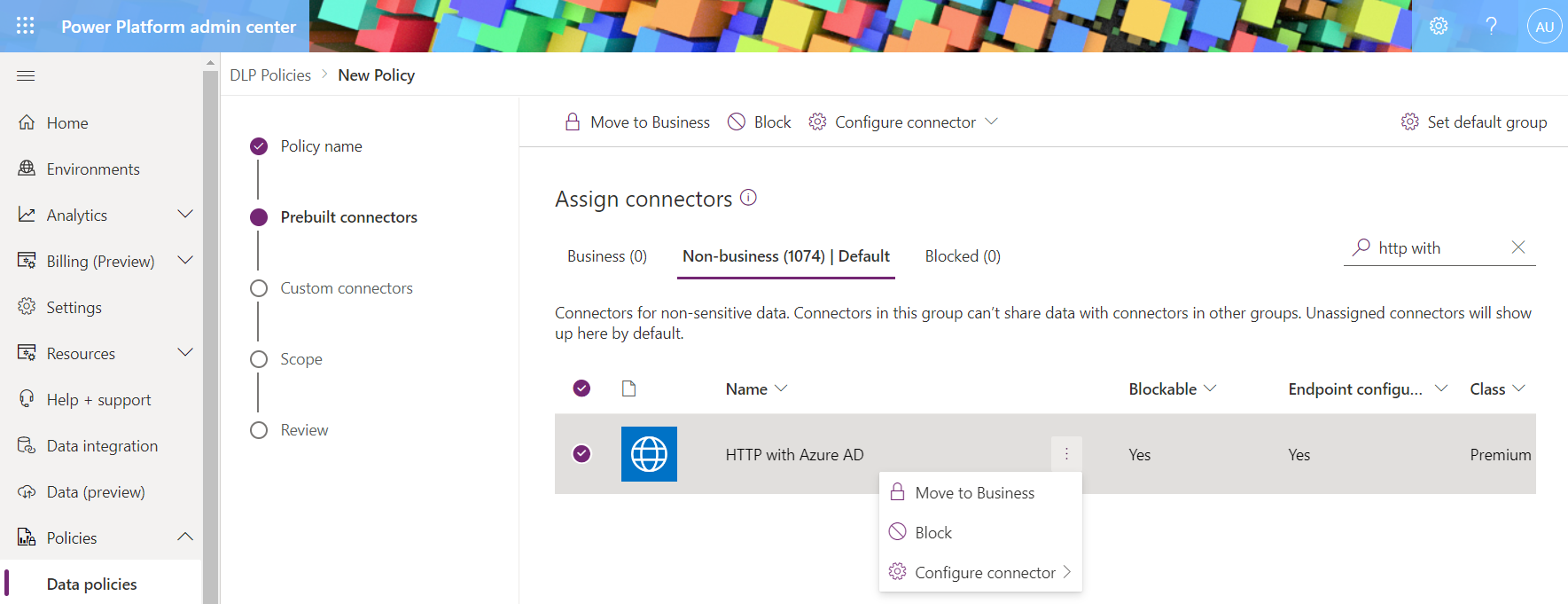
If you wish to restrict the use of this connector, you can leverage the existing Data Loss Prevention (DLP) capabilities. You have the option to create a new policy or update an existing one to block the utilization of this connector. It is important to note that some other connectors and features depend on the HTTP with Microsoft Entra ID (preauthorized) connector. For additional information, click here.
Virtual Network support (Subnet Delegation)
When the connector is used in a Power Platform environment linked to a Virtual Network, limitations apply:
- The following actions are NOT supported actions:
Known Issues and Limitations
The connector encodes the request body into base64 encoding, hence it should be used to call backend services which expect the request body in this format. You cannot use this connector to call a backend service that expects the request body in raw binary format.
If you get an error similar to:
{ "error": { "code": "Forbidden", "message": "" } }{ "error": { "code": "Authorization_RequestDenied", "message": "Insufficient privileges to complete the operation." } }then it could be because this connector has a limited set of scopes.- Users may also face pre-authorization errors when connecting to some resources that are not supported.
- If your scenario requires something more advanced, please use the "HTTP" connector or create a custom connector.
The connector is based on multi-tenant application registration. The application cannot tell what tenant the user is from until the user signs into it. Therefore, we only support specifying resources under users' default tenant ('common').
Resources based on ADFS SSO (Microsoft Entra ID Federation Services for Single Sign-On) are not supported. As a workaround, please use the "HTTP" connector.
When using this connector in a national cloud environment the resource must be their national cloud endpoint equivalent. Attempts to try to connect to public cloud (https://graph.microsoft.com, https://bing.com for example) from most national cloud environments will fail with a pre-authorization error.
- GCC and Fairfax environments can continue to use public cloud endpoints (https://graph.microsoft.com, for example).
- GCC-High resource example: https://graph.microsoft.us.
- China resource example: https://microsoftgraph.chinacloudapi.cn.
The use of cookie authorization request header is not supported in case of on-premises data gateway enabled connection.
The asynchronous pattern based on the response Location header is not supported. Please use Azure Resource Manager connector instead if applicable.
For the ‘HTTP with Microsoft Entra ID’ connector to successfully retrieve data from another service, the app used by the connector must be granted access to the required scope. For details on how to grant the required access to the app, refer to Authorize the app to act on behalf of a signed-in user. If the required access is not granted, you may receive one of the following errors when you attempt to create the connection:
Consent Required: To enable the HTTP With Microsoft Entra ID connector to access resources on behalf of a signed-in user, grant consent to this application.
If a scope (permission) has been granted but not all of the required scopes are included, the creation of the connection will succeed but you will encounter a Forbidden (403) error at runtime. The error details may include additional information such as:
"code": "Authorization_RequestDenied" "message": "Insufficient privileges to complete the operation."If issues are faced creating a connection or an error is received around a missing parameter value, try creating a connection with Power Automate's Old Designer instead of the New Designer.
Removing or adding preauthorizations can take up to 1 hour to reflect for connections existing prior to the update. However, new connections should reflect the updated authorizations instantly.
Authorize the connector to act on behalf of a signed-in user
As a user with the Global Administrator role, you need to create oAuth2PermissionGrants to approve the necessary permissions (scopes) for the required service.
For example, if you are using Microsoft Graph (https://graph.microsoft.com) and need to read calendar information, you can follow the Graph documentation to identify the permissions required (Calendar.Read). By granting the app (used by the connector) the Calendar.Read scope, it will allow the app to access this data from the service on behalf of the user. One important thing to note is that the data that can be accessed by the app is still limited to the data the user has access to in the service. It is not possible to use the Azure Portal to grant consent to this app. For this reason, a PowerShell script has been created by Microsoft to simplify granting consent to the app used by the HTTP with Microsoft Entra ID connector.
Important
PowerShell version 7 or later needs to be installed to run this script.
Download the required PowerShell script from here or create a script named 'ManagePermissionGrant.ps1' referring to the steps mentioned here. This script is mainly for reference, you can modify the script as per your use case.
Right-click on the downloaded ManagePermissionGrant.ps1 file and then click Properties.
Click the Unblock checkbox and then click OK.

If you do not check the Unblock checkbox, you will receive an error indicating the script cannot be loaded because it is not digitally signed.
Open a PowerShell command window.
Change the path to the location where you downloaded the script.
Type the following command and press Enter:
.\ ManagePermissionGrant.ps1
You will be prompted to choose whether to authenticate to Azure Global (recommended) or to select from a list (advanced). If you are not connecting to subscriptions in US Gov, US Gov DoD, China, or Germany, press Enter.

If you have not already, you may be prompted to authenticate to the Microsoft identity platform in a new browser window. Authenticate as a user with the Global Administrator role.
To grant consent to some of the most used services such as Microsoft Graph or SharePoint, press Enter. If the service you need to consent to is not on the list of commonly used apps, use option A.

A dialog will appear. Select the application you want to consent to allowing the connector to act on behalf of a user. You can use the textbox at the top to filter the results.

Click OK.
Select one or more scopes (permissions) you want to consent to and then click OK. Multiple scopes can be selected by pressing and holding the CTRL key while selecting rows.
In the PowerShell window you will be prompted to choose the consent type. You can choose whether to allow the app to act on behalf of any logged in user or if you want to limit the consent to a specific user. If you want to provide consent for all users, press Enter. If you want to provide consent for only a specific user, type N and then press Enter. If you choose to consent for a specific user, you will be prompted to select the user.
If consent for any scopes already exist for the selected resource, you will be prompted to choose if you want to delete the existing grants first. If you want to delete existing grants, type Y and press Enter. If you want to keep the existing grants, press Enter.
A summary of the scopes you selected will be displayed in the PowerShell window. If you want to proceed with granting the selected scopes, type Y and then press Enter.
If the script can grant the consent successfully, you will see a message that script execution completed.
Creating a connection
The connector supports the following authentication types:
| Default | Parameters for creating connection. | All regions | Not shareable |
Default
Applicable: All regions
Parameters for creating connection.
This is not shareable connection. If the power app is shared with another user, another user will be prompted to create new connection explicitly.
| Name | Type | Description | Required |
|---|---|---|---|
| Microsoft Entra ID Resource URI (Application ID URI) | string | The identifier used in Microsoft Entra ID to identify the target resource. For SharePoint Online and OneDrive for Business, use https://{contoso}.sharepoint.com. Usually, it is the base URL of your resource. | True |
| Base Resource URL | string | Specify the base URL of the HTTP resources or Application (client) ID in the form of the GUID you want to connect to. | True |
| Username | securestring | Username credential | |
| Password | securestring | Password credential | |
| Authentication Type | string | Authentication type to connect to your on-premise HTTP resource | |
| Gateway | gatewaySetting | On-prem gateway (see https://docs.microsoft.com/data-integration/gateway for more details |
Throttling Limits
| Name | Calls | Renewal Period |
|---|---|---|
| API calls per connection | 100 | 60 seconds |
Actions
| Get web resource |
Retrieves a web resource by issuing an HTTP GET request. |
| Invoke an HTTP request |
Invokes an HTTP endpoint. |
Get web resource
Retrieves a web resource by issuing an HTTP GET request.
Parameters
| Name | Key | Required | Type | Description |
|---|---|---|---|---|
|
Resource path
|
path | True | string |
File identifier |
Returns
The content of the file.
- File Content
- binary
Invoke an HTTP request
Invokes an HTTP endpoint.
Parameters
| Name | Key | Required | Type | Description |
|---|---|---|---|---|
|
Method
|
method | True | string |
One of the known HTTP verbs: GET, DELETE, PATCH, POST, PUT. |
|
Url of the request
|
url | True | string |
A full or relative URL to the resource. If it is a full URL , it must match the base resource URL set in the connection. |
|
Headers
|
headers | object |
The request headers. |
|
|
Body of the request
|
body | byte |
Body of the request when the method requires it. |
Returns
The content of the response.
- Body
- string
Definitions
binary
This is the basic data type 'binary'.