Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Important
Some information in this article relates to a prereleased product which may be substantially modified before it's commercially released. Microsoft makes no warranties, expressed or implied, with respect to the information provided here.
Quickly respond to detected attacks by isolating devices or collecting an investigation package. After taking action on devices, you can check activity details on the Action center.
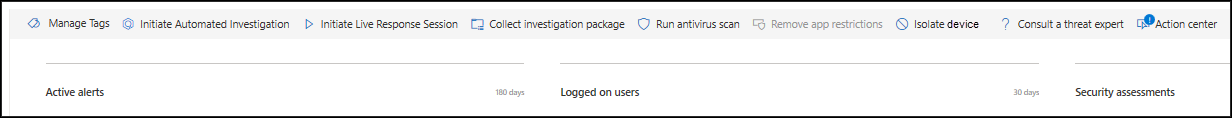
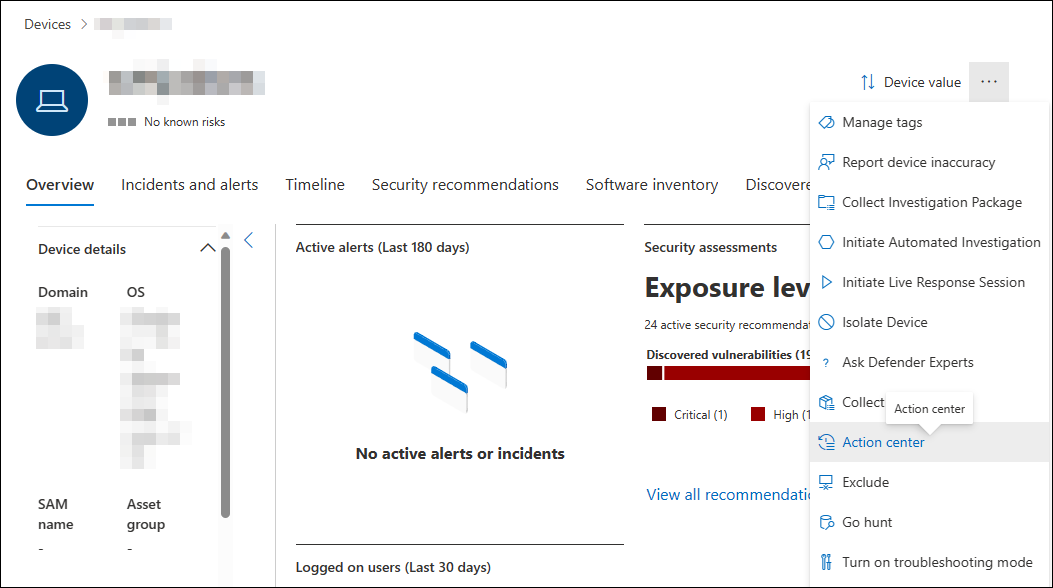
Response actions run along the top of a specific device page and include:
- Manage tags
- Initiate automated investigation
- Initiate live response Session
- Collect investigation package
- Run antivirus scan
- Restrict app execution
- Isolate device
- Contain device
- Consult a threat expert
- Action center
Note
Defender for Endpoint Plan 1 includes only the following manual response actions:
- Run antivirus scan
- Isolate device
- Stop and quarantine a file
- Add an indicator to block or allow a file.
Microsoft Defender for Business doesn't include the "Stop and quarantine a file" action at this time.
Your subscription must include Defender for Endpoint Plan 2 to have all of the response actions described in this article.
You can find device pages from any of the following views:
- Alerts queue: Select the device name beside the device icon from the alerts queue.
- Devices list: Select the heading of the device name from the devices list.
- Search box: Select Device from the drop-down menu and enter the device name.
Important
For information on availability and support for each response action, see the supported minimum operating system requirements for each feature.
Limiting high-impact response actions on high-value assets
Some high-impact response actions can be restricted on high-value assets to prevent potential business disruption. For more information, see Restrict response actions on high-value assets.
Manage tags
Add or manage tags to create a logical group affiliation. Device tags support proper mapping of the network, enabling you to attach different tags to capture context and to enable dynamic list creation as part of an incident.
For more information on device tagging, see Create and manage device tags.
Initiate automated investigation
You can start a new, general-purpose automated investigation on the device if needed. While an investigation is running, any other alert generated from the device is added to an ongoing automated investigation until that investigation completes. In addition, if the same threat is seen on other devices, those devices are added to the investigation.
For more information on automated investigations, see Overview of Automated investigations.
Initiate live response session
Live response is a capability that gives you instantaneous access to a device by using a remote shell connection. This gives you the power to do in-depth investigative work and take immediate response actions to promptly contain identified threats in real time.
Live response is designed to enhance investigations by enabling you to collect forensic data, run scripts, send suspicious entities for analysis, remediate threats, and proactively hunt for emerging threats.
For more information on live response, see Investigate entities on devices using live response.
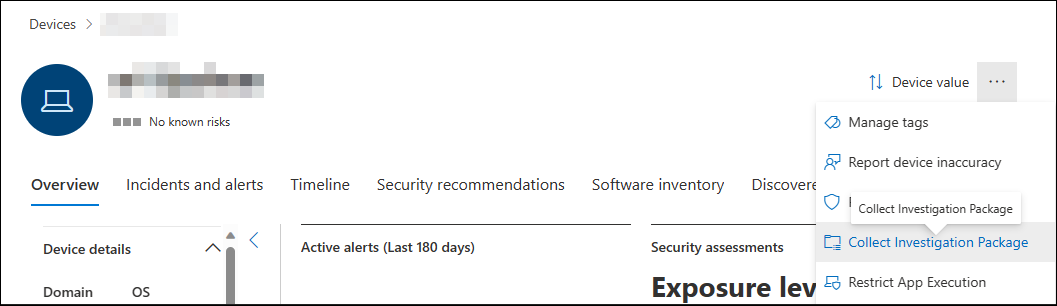
Collect investigation package from devices
As part of the investigation or response process, you can collect an investigation package from a device. By collecting the investigation package, you can identify the current state of the device and further understand the tools and techniques used by the attacker.
To download the package (zipped folder) and investigate the events that occurred on a device, follow these steps:
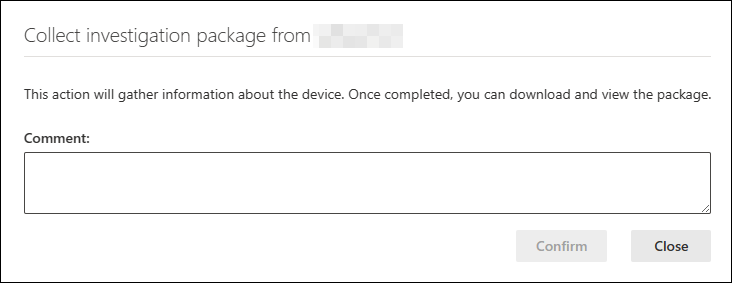
Select Collect investigation package from the row of response actions at the top of the device page.
Specify in the text box why you want to perform this action. Select Confirm.
The zip file downloads.
Or, use this alternate procedure:
Select Collect Investigation Package from the response actions section of the device page.
Add comments and then select Confirm.
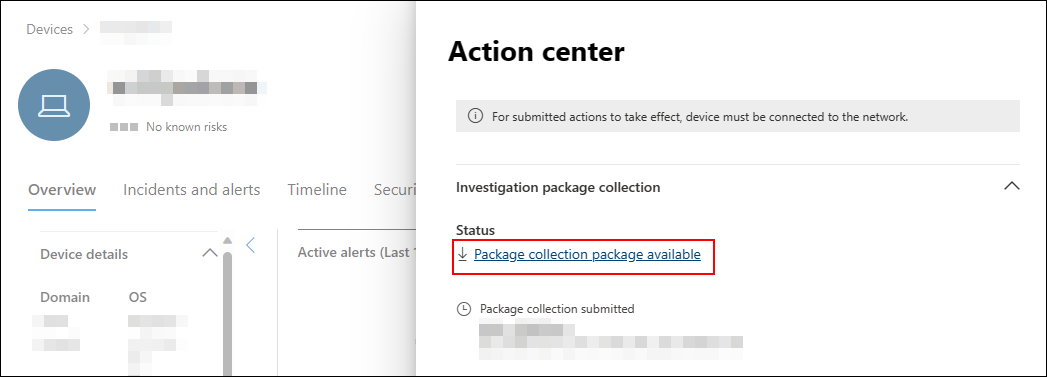
Select Action center from the response actions section of the device page.
Select Package collection package available to download the collection package.
Note
The collection of the investigation package might fail if a device has a low battery level or is on a metered connection.
Investigation package contents for Windows devices
For Windows devices, the package contains the folders described in the following table:
| Folder | Description |
|---|---|
| Autoruns | Contains a set of files that each represent the content of the registry of a known auto start entry point (ASEP) to help identify attacker's persistency on the device. If the registry key isn't found, the file contains the following message: "ERROR: The system was unable to find the specified registry key or value." |
| Installed programs | This .CSV file contains the list of installed programs that can help identify what is currently installed on the device. For more information, see Win32_Product class. |
| Network connections | This folder contains a set of data points related to the connectivity information that can help in identifying connectivity to suspicious URLs, attacker's command and control (C&C) infrastructure, any lateral movement, or remote connections. - ActiveNetConnections.txt: Displays protocol statistics and current TCP/IP network connections. Enables you to look for suspicious connectivity made by a process.- Arp.txt: Displays the current address resolution protocol (ARP) cache tables for all interfaces. ARP cache can reveal other hosts on a network that were compromised or suspicious systems on the network that might be used to run an internal attack.- DnsCache.txt: Displays the contents of the DNS client resolver cache, which includes both entries preloaded from the local Hosts file and any recently obtained resource records for name queries resolved by the computer. This can help in identifying suspicious connections.- IpConfig.txt: Displays the full TCP/IP configuration for all adapters. Adapters can represent physical interfaces, such as installed network adapters, or logical interfaces, such as dial-up connections.- FirewallExecutionLog.txt and pfirewall.logThe pfirewall.log file must exist in %windir%\system32\logfiles\firewall\pfirewall.log. It's included in the investigation package. For more information on creating the firewall log file, see Configure the Windows Firewall with Advanced Security Log. |
| Prefetch files | Windows Prefetch files are designed to speed up the application startup process. It can be used to track all the files recently used in the system and find traces for applications that might be deleted but can still be found in the prefetch file list. - Prefetch folder: Contains a copy of the prefetch files from %SystemRoot%\Prefetch. We recommend downloading a prefetch file viewer to view the prefetch files.- PrefetchFilesList.txt: Contains the list of all the copied files that can be used to track if there were any copy failures to the prefetch folder. |
| Processes | Contains a .CSV file listing the processes currently running on the device. This can be useful when identifying a suspicious process and its state. |
| Scheduled tasks | Contains a .CSV file listing the scheduled tasks, which can be used to identify routines performed automatically on a chosen device to look for suspicious code that was set to run automatically. |
| Security event log | Contains the security event log, which contains records of sign-in or sign out activity, or other security-related events specified by the system's audit policy. Open the event log file using Event viewer. |
| Services | Contains a .CSV file that lists services and their states. |
| Windows Server Message Block (SMB) sessions | Lists shared access to files, printers, and serial ports and miscellaneous communications between nodes on a network. This can help identify data exfiltration or lateral movement. Contains files for SMBInboundSessions and SMBOutboundSession. If there are no sessions (inbound or outbound), you get a text file that tells you that there are no SMB sessions found. |
| System Information | Contains a SystemInformation.txt file that lists system information such as OS version and network cards. |
| Temp Directories | Contains a set of text files that lists the files located in %Temp% for every user in the system. This can help to track suspicious files that an attacker might have dropped on the system. If the file contains the following message: "The system can't find the path specified," it means that there's no temp directory for this user, and might be because the user didn't sign in to the system. |
| Users and Groups | Provides a list of files that each represent a group and its members. |
| WdSupportLogs | Provides the MpCmdRunLog.txt and MPSupportFiles.cab. This folder is only created on Windows 10, version 1709 or later with February 2020 update rollup or more recent versions installed: - Win10 1709 (RS3) Build 16299.1717: KB4537816 - Win10 1803 (RS4) Build 17134.1345: KB4537795 - Win10 1809 (RS5) Build 17763.1075: KB4537818 - Win10 1903/1909 (19h1/19h2) Builds 18362.693 and 18363.693: KB4535996 |
| CollectionSummaryReport.xls | This file is a summary of the investigation package collection, it contains the list of data points, the command used to extract the data, the execution status, and the error code if there's failure. You can use this report to track if the package includes all the expected data and identify if there were any errors. |
Investigation package contents for Mac and Linux devices
The following table lists the contents of the collection packages for Mac and Linux devices:
| Object | macOS | Linux |
|---|---|---|
| Applications | A list of all installed applications | Not applicable |
| Disk volume | - Amount of free space - List of all mounted disk volumes - List of all partitions |
- Amount of free space - List of all mounted disk volumes - List of all partitions |
| File | A list of all open files with the corresponding processes using these files | A list of all open files with the corresponding processes using these files |
| History | Shell history | Not applicable |
| Kernel modules | All loaded modules | Not applicable |
| Network connections | - Active connections - Active listening connections - ARP table - Firewall rules - Interface configuration - Proxy settings - VPN settings |
- Active connections - Active listening connections - ARP table - Firewall rules - IP list - Proxy settings |
| Processes | A list of all running processes | A list of all running processes |
| Services and scheduled tasks | - Certificates - Configuration profiles - Hardware information |
- CPU details - Hardware information - Operating system information |
| System security information | - Extensible Firmware Interface (EFI) integrity information - Firewall status - Malware Removal Tool (MRT) information - System Integrity Protection (SIP) status |
Not applicable |
| Users and groups | - Sign-in history - Sudoers |
- Sign-in history - Sudoers |
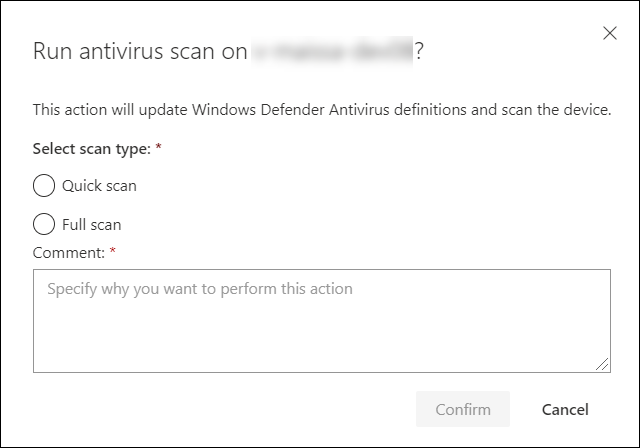
Run Microsoft Defender Antivirus scan on devices
As part of the investigation or response process, you can remotely initiate an antivirus scan to help identify and remediate malware that might be present on a compromised device.
Important
- This action is supported for macOS and Linux for client version 101.98.84 and above. You can also use live response to run the action. For more information on live response, see Investigate entities on devices using live response
- A Microsoft Defender Antivirus scan can run alongside other antivirus solutions, whether Microsoft Defender Antivirus is the active antivirus solution or not. Microsoft Defender Antivirus can be in Passive mode. For more information, see Microsoft Defender Antivirus compatibility.
One you have selected Run antivirus scan, select the scan type that you'd like to run (quick or full) and add a comment before confirming the scan.
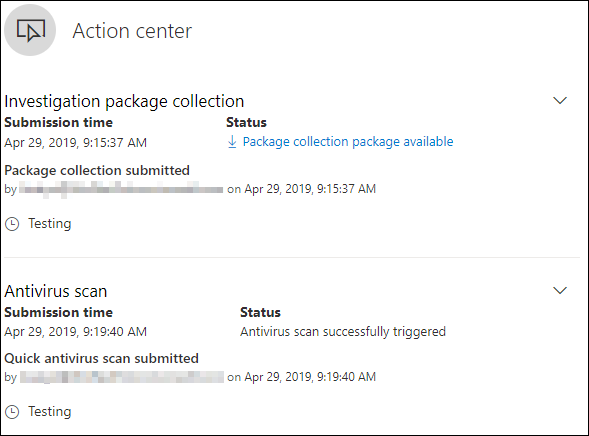
The Action center shows the scan information and the device timeline include a new event, reflecting that a scan action was submitted on the device. Microsoft Defender Antivirus alerts reflect any detections that surfaced during the scan.
Note
When triggering a scan using Defender for Endpoint response action, Microsoft Defender antivirus ScanAvgCPULoadFactor value applies and limits the CPU impact of the scan.
If ScanAvgCPULoadFactor isn't configured, the default value is a limit of 50% maximum CPU load during a scan.
For more information, see configure-advanced-scan-types-microsoft-defender-antivirus.
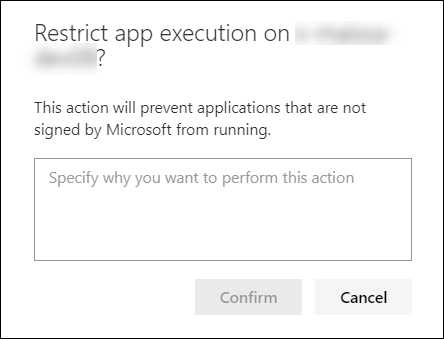
Restrict app execution
In addition to containing an attack by stopping malicious processes, you can also lock down a device and prevent subsequent attempts of potentially malicious programs from running.
Important
- This action is available for devices on Windows 10, version 1709 or later, Windows 11, and Windows Server 2019 or later.
- This feature is available if your organization uses Microsoft Defender Antivirus.
- This action needs to meet the Windows Defender Application Control code integrity policy formats and signing requirements. For more information, see Code integrity policy formats and signing).
To restrict an application from running, a code integrity policy is applied that only allows files to run if they're signed by a Microsoft issued certificate. This method of restriction can help prevent an attacker from controlling compromised devices and performing further malicious activities.
Note
You are able to reverse the restriction of applications from running at any time. The button on the device page changes to say Remove app restrictions, and then you take the same steps as restricting app execution.
Once you have selected Restrict app execution on the device page, type a comment and select Confirm. The Action center shows the scan information and the device timeline include a new event.
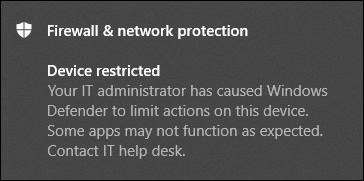
Notification on device user
When an app is restricted, the following notification is displayed to inform the user that an app is being restricted from running:
Note
The notification isn't available on Windows Server 2016 and Windows Server 2012 R2.
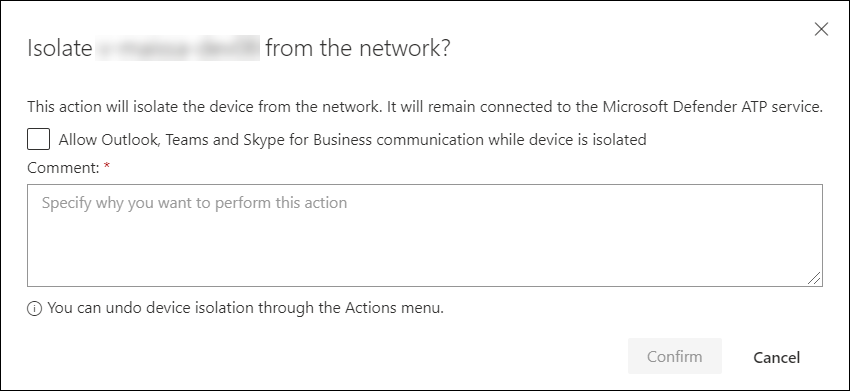
Isolate devices from the network
Depending on the severity of the attack and the sensitivity of the device, you might want to isolate the device from the network. This action can help prevent the attacker from controlling the compromised device and performing further activities such as data exfiltration and lateral movement.
Important points to keep in mind:
In environments that use web proxies (including Proxy Auto Configuration (PAC), WPAD, or static/direct proxy configurations), devices might not be able to recover from network isolation. Use selective isolation in such cases. When using selective isolation, exclusion settings aren't required to avoid this scenario.
Isolating devices from the network is supported for macOS for client version 101.98.84 and above. You can also use live response to run the action. For more information on live response, see Investigate entities on devices using live response
Full isolation is available for devices running Windows 11, Windows 10, version 1703 or later, Windows Server 2012 R2 and later, and Azure Stack HCI OS, version 23H2 and later.
Isolating devices from the network is supported when Defender is running in passive mode on all supported Windows operating systems, macOS and Linux supported versions.
You can use the device isolation capability on all supported Microsoft Defender for Endpoint on Linux listed in System requirements. Ensure that the following prerequisites are enabled:
iptablesip6tables- Linux kernel with
CONFIG_NETFILTER,CONFIG_IP_NF_IPTABLES, andCONFIG_IP_NF_MATCH_OWNERfor kernel version lower than 5.x andCONFIG_NETFILTER_XT_MATCH_OWNERfrom 5.x kernel.
Selective isolation is available for devices running on Windows 11, Windows 10 version 1703 or later, Windows Server 2012 R2 and later, Azure Stack HCI OS, version 23H2 and later, and macOS. For more information about selective isolation, see Isolation exclusions.
When isolating a device, only certain processes and destinations are allowed. Therefore, devices that are behind a full VPN tunnel won't be able to reach the Microsoft Defender for Endpoint cloud service after the device is isolated. We recommend using a split-tunneling VPN for Microsoft Defender for Endpoint and Microsoft Defender Antivirus cloud-based protection-related traffic.
The feature supports VPN connection.
You must have at least the
Active remediation actionsrole assigned. For more information, see Create and manage roles.You must have access to the device based on the device group settings. For more information, see Create and manage device groups.
Exclusions, such as e-mail, messaging application, and other applications for both macOS and Linux isolation aren't supported.
An isolated device is removed from isolation when an administrator modifies or adds a new
iptablerule to the isolated device.Isolating a server running on Microsoft Hyper-V blocks network traffic to all child virtual machines of the server.
The device isolation feature disconnects the compromised device from the network while retaining connectivity to the Defender for Endpoint service, which continues to monitor the device. On Windows 10, version 1709 or later, you can use selective isolation for more control over the network isolation level. You can also choose to enable Outlook and Microsoft Teams connectivity.
Note
You can reconnect the device back to the network at any time. The button on the device page changes to say Release from isolation. At this stage, you can take the same steps as isolating the device.
If a device is inactive or offline when an isolation action is submitted, Microsoft Defender for Endpoint retries enforcing the isolation for up to three days. If the device doesn't reconnect in that time, the isolation won't be retried, and administrators should reissue the isolation action after the device becomes active.
Once you have selected Isolate device on the device page, type a comment and select Confirm. The Action center shows the scan information and the device timeline include a new event.
Note
The device remains connected to the Defender for Endpoint service even if it's isolated from the network. If you've chosen to enable Outlook and Skype for Business communication, then you're able to communicate to the user while the device is isolated. Selective isolation only works on the classic versions of Outlook and Microsoft Teams.
Forcibly release device from isolation
The device isolation feature is an invaluable tool for safeguarding devices against external threats. However, there are instances when isolated devices become unresponsive.
There's a downloadable script for these instances that you can run to forcibly release devices from isolation. The script is available through a link in the UI.
Note
- Admins and manage security settings in Security Center permissions can forcibly release devices from isolation.
- The script is valid for the specific device only.
- The script expires in three days.
To forcibly release device from isolation:
On the device page, select Download script to force-release a device from isolation from the action menu.
In the pane on the right, select Download script.
Minimum requirements for forcible device release
To forcibly release a device from isolation, the device must be running Windows. The following versions are supported:
- Windows 10 21H2 and 22H2 with KB KB5023773.
- Windows 11 version 21H2, all editions with KB5023774.
- Windows 11 version 22H2, all editions with KB5023778.
Notification on device user
When a device is being isolated, the following notification is displayed to inform the user that the device is being isolated from the network:
Note
The notification isn't available on non-Windows platforms.
Containing critical assets
When a critical asset is compromised and used to spread threats within an organization, stopping the spread can be challenging because these assets must continue to function to avoid productivity loss. Defender for Endpoint addresses this by granularly containing the critical asset, preventing the spread of the attack while ensuring the asset remains operational for business continuity.
Through automatic attack disruption, Defender for Endpoint incriminates a malicious device, identifies the role of the device to apply a matching policy to automatically contain a critical asset. The granular containment is done by blocking only specific ports and communication directions.
You can identify critical assets by the critical asset tag on the device or IP page. Device containment supports critical asset types like domain controllers, DNS servers, and DHCP servers.
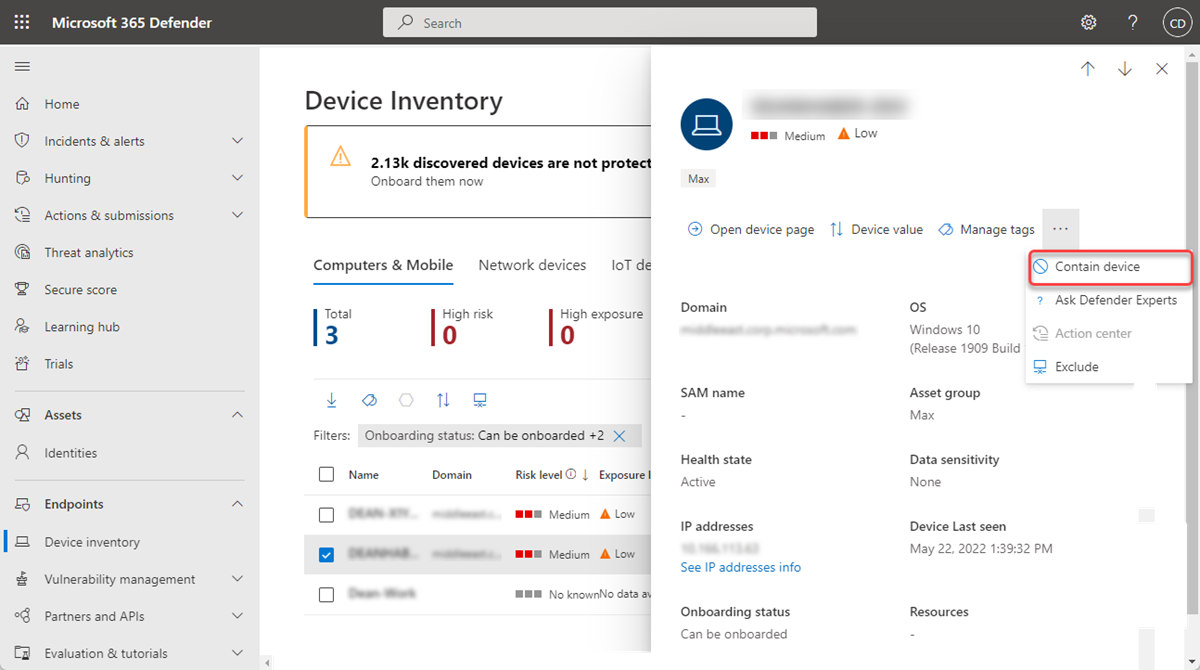
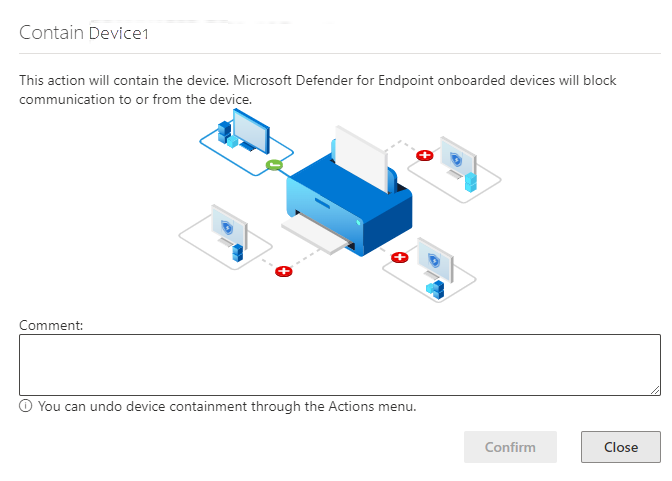
Contain devices from the network
When you have identified an unmanaged device that is compromised or potentially compromised, you might want to contain that device from the network to prevent the potential attack from moving laterally across the network. When you contain a device any Microsoft Defender for Endpoint onboarded device blocks incoming and outgoing communication with that device. This action can help prevent neighboring devices from becoming compromised while the security operations analyst locates, identifies, and remediates the threat on the compromised device.
Note
Blocking incoming and outgoing communication with a 'contained' device is supported on onboarded Microsoft Defender for Endpoint Windows 10 and Windows Server 2019+ devices.
Once devices are contained, we recommend investigating and remediating the threat on the contained devices as soon as possible. After remediation, you should remove the devices from containment.
How to contain a device
Go to the Device inventory page and select the device to contain.
Select Contain device from the actions menu in the device flyout.
On the contain device popup, type a comment, and select Confirm.
Important
Containing a large number of devices might cause performance issues on Defender for Endpoint-onboarded devices. To prevent any issues, Microsoft recommends containing up to 100 devices at any given time.
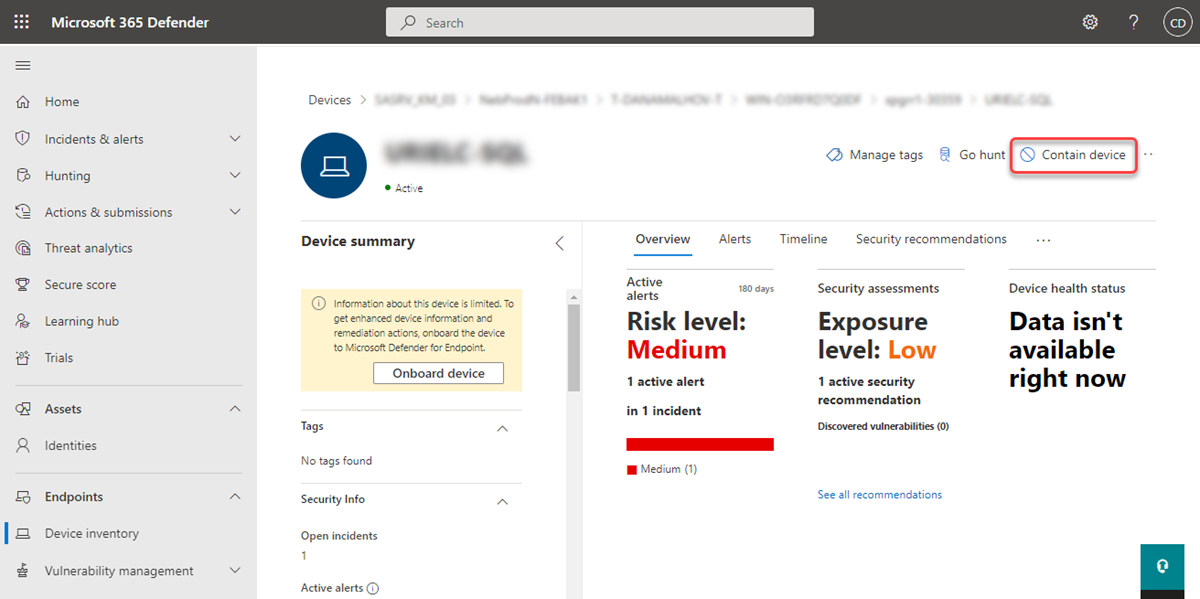
Contain a device from the device page
A device can also be contained from the device page by selecting Contain device from the action bar:
Note
It can take up to 5 minutes for the details about a newly contained device to reach Microsoft Defender for Endpoint onboarded devices.
Important
- If a contained device changes its IP address, all Microsoft Defenders for Endpoint onboarded devices recognize this and start blocking communications with the new IP address. The original IP address is no longer be blocked (It might take up to 5 minutes to see these changes).
- In cases where the contained device's IP is used by another device on the network, a warning while containing the device with a link to advanced hunting (with a pre-populated query) is displayed. This provides visibility to other devices using the same IP to help you make a conscious decision if you'd like to continue containing the device.
- In cases where the contained device is a network device, a warning appears with a message that containment can cause network connectivity issues (for example, containing a router that's acting as a default gateway). At this point, you're able to choose whether to contain the device or not.
After you contain a device, if the behavior isn't as expected, verify the Base Filtering Engine (BFE) service is enabled on the Defender for Endpoint onboarded devices.
Stop containing a device
You can stop containing a device at any time.
Select the device from the Device inventory or open the device page.
Select Release from containment from the action menu. This action restores the device's connection to the network.
Contain IP addresses of undiscovered devices
Important
Some information in this article relates to prereleased product, which might be substantially modified before it's commercially released. Microsoft makes no warranties, express or implied, with respect to the information provided here.
Defender for Endpoint can also contain IP addresses associated with devices that are undiscovered or aren't onboarded to Defender for Endpoint. The capability to contain an IP address prevents attackers from spreading attacks to other noncompromised devices. Containing an IP address results in Defender for Endpoint-onboarded devices blocking incoming and outgoing communication with devices using the contained IP address
Note
Blocking incoming and outgoing communication with a 'contained' device is supported on onboarded Defender for Endpoint Windows 10, Windows 11, Windows 2012 R2, and Windows 2016 devices.
Containing an IP address associated with undiscovered devices or devices not onboarded to Defender for Endpoint is done automatically through automatic attack disruption. The Contain IP policy automatically blocks a malicious IP address when Defender for Endpoint detects the IP address to be associated with an undiscovered device or a device not onboarded.
A message indicating that the action is applied appears on the applicable incident, device, or IP page. Here’s an example.
After an IP address is contained, you can view the action in the History view of the Action Center. You can see when the action occurred and identify the IP addresses that were contained.
If a contained IP address is part of an incident, an indicator is present on the incident graph and on the incident's evidence and response tab. Here’s an example.
You can stop an IP address' containment at any time. To stop containment, select the Contain IP action in the Action Center. In the flyout, select Undo. This action restores the IP address’ connection to the network.
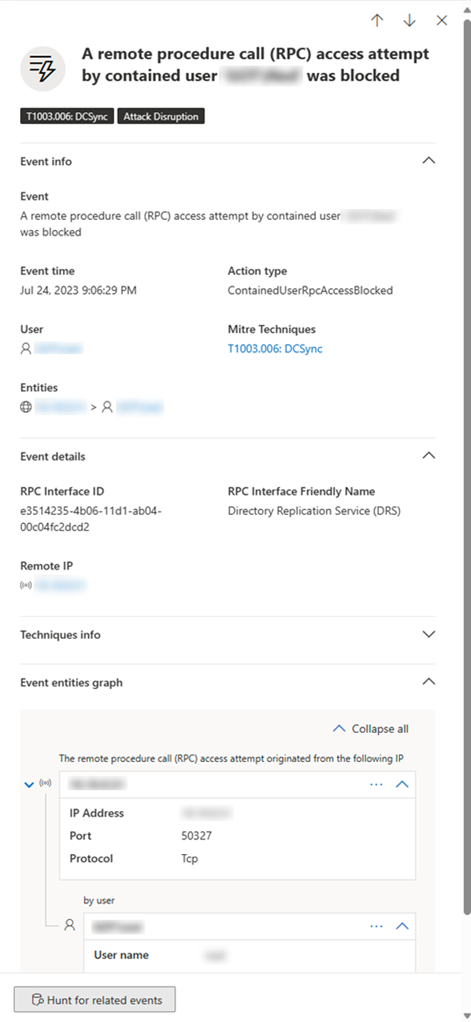
Contain user from the network
When an identity in your network might be compromised, you must prevent that identity from accessing the network and different endpoints. Defender for Endpoint can contain an identity, blocking it from access, and helping prevent attacks, specifically, ransomware. When an identity is contained, any supported Microsoft Defender for Endpoint onboarded device blocks incoming traffic in specific protocols related to attacks (deny network logons, RPC, SMB, RDP), terminate ongoing remote sessions and logoff existing RDP connections (terminating the session itself including all its related processes), while enabling legitimate traffic. This action can significantly help to reduce the impact of an attack. When an identity is contained, security operations analysts have extra time to locate, identify, and remediate the threat to the compromised identity. Once contained by automatic attack disruption, a user is automatically removed from containment in the next five days.
Contain user important notes
- Defender for Endpoint enforces user containment at the endpoint layer and doesn't disable the account in the identity provider. Defender for Endpoint blocks attacker use of compromised identities on protected devices and limits authentication-based access, file system access, and network communication paths. This action applies controls at a granular level, so Microsoft can target attack-related activity and preserve normal business communication where possible.
- When the contain user action is triggered by predictive shielding (Preview), the contain user action applies restrictions more selectively, with a focus on users identified as high risk through prediction logic. The contain user action in predictive shielding prevents new sessions rather than terminating existing ones.
- While the predictive shielding feature as a whole is in Preview, this action is generally available, both when triggered by attack disruption and predictive shielding.
- Blocking incoming communication with a "contained" user is supported on onboarded Microsoft Defender for Endpoint Windows 10 and 11 devices (Sense version 8740 and higher), Windows Server 2019+ devices, and Windows Servers 2012R2 and 2016 with the modern agent.
- Important: Once a Contain user action is enforced on a domain controller, it starts a GPO update on the Default Domain Controller policy. A change of a GPO starts a sync across the domain controllers in your environment. This is expected behavior, and if you monitor your environment for AD GPO changes, you might be notified of such changes. Undoing the Contain user action reverts the GPO changes to their previous state, which will then start another AD GPO synchronization in your environment. Learn more about merging of security policies on domain controllers.
How to contain a user
Currently, containing users is only available automatically by using automatic attack disruption. When Microsoft detects a user as being compromised a "Contain User" policy is automatically set.
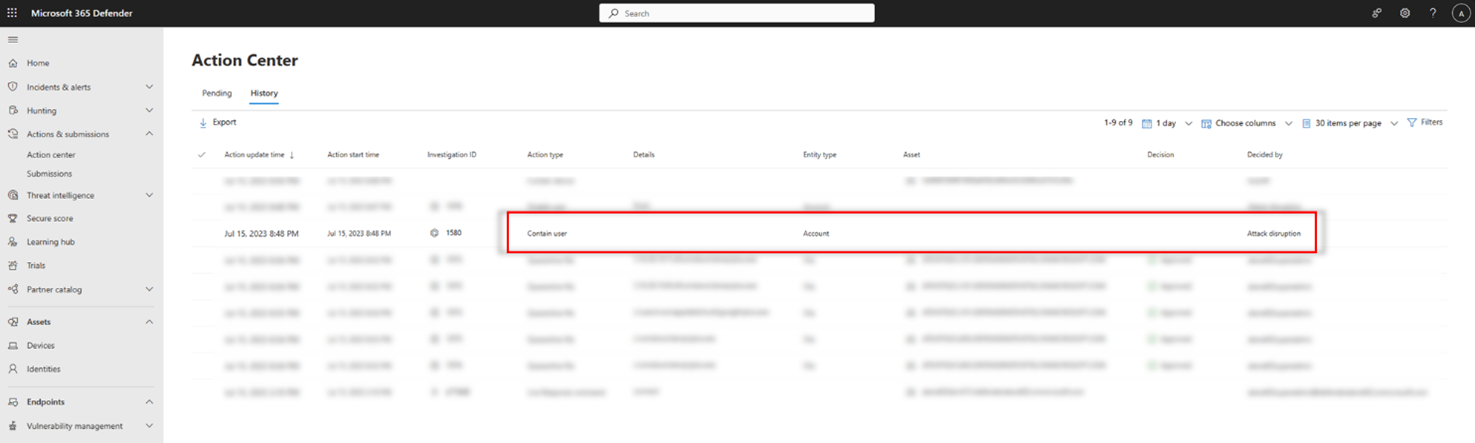
View the contain user actions
After a user is contained, you can view the action in this History view of the Action Center. Here, you can see when the action occurred, and which users in your organization were contained:
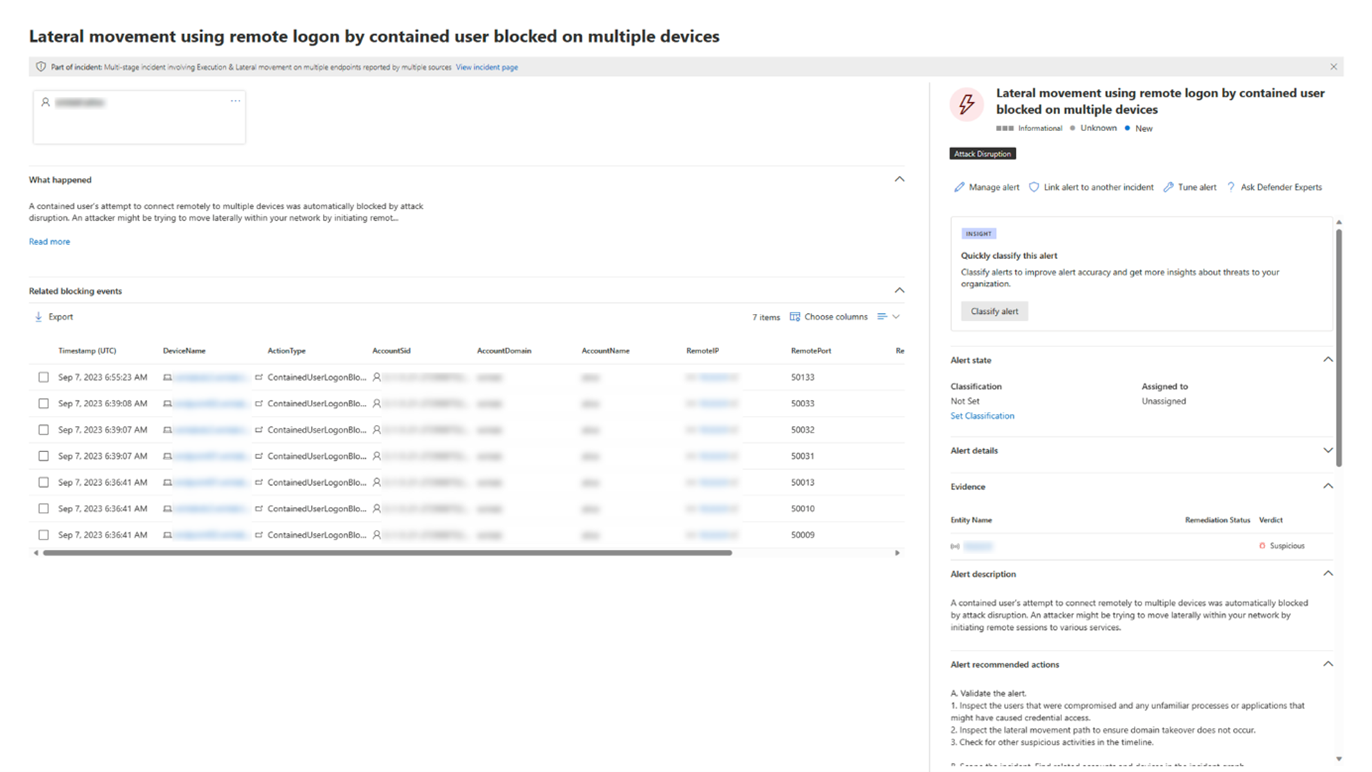
Furthermore, after an identity is considered "contained", that user will be blocked by Defender for Endpoint and can't perform any malicious lateral movement or remote encryption on or to any supported Defender for Endpoint onboarded device. These blocks show up as alerts to help you quickly see the devices the compromised user attempted access and potential attack techniques:
To view the current status of the contain user action and other actions, see Track the action status in the Activities tab (Preview).
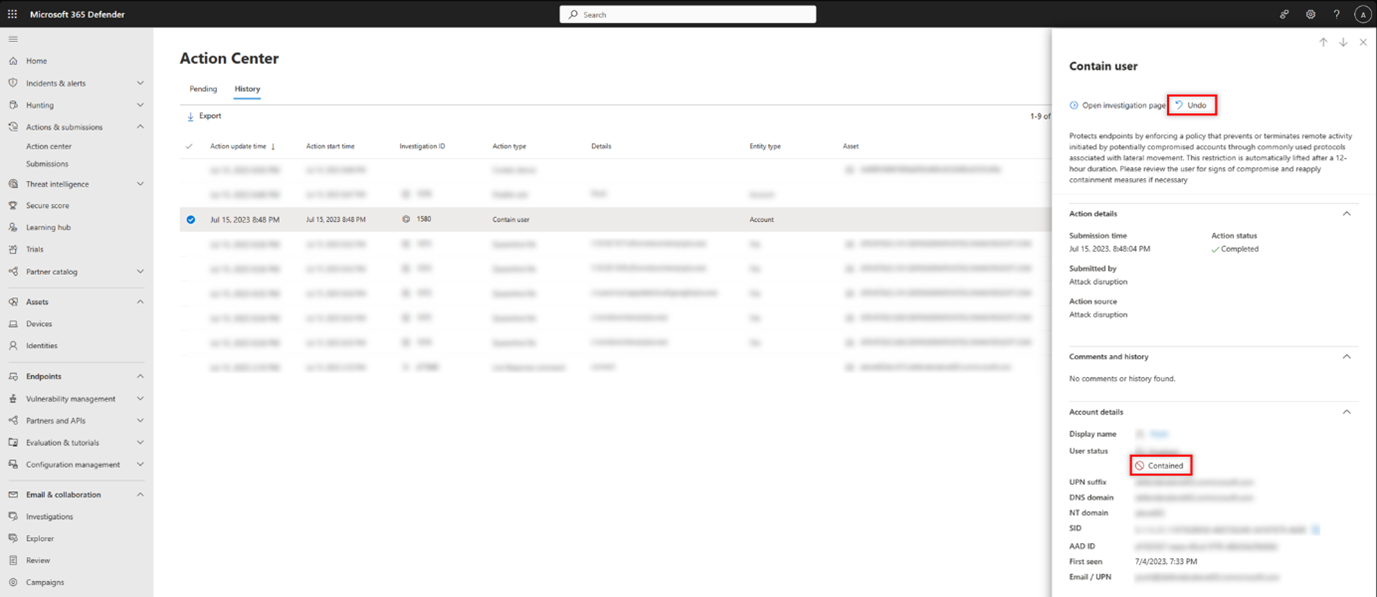
Undo contain user actions
Tip
Undoing contain user actions requires membership in the Global Administrator* role in Microsoft Entra permissions.
* Microsoft strongly advocates for the principle of least privilege. Assigning accounts only the minimum permissions necessary to perform their tasks helps reduce security risks and strengthens your organization's overall protection. Global Administrator is a highly privileged role that you should limit to emergency scenarios or when you can't use a different role.
You can release the blocks and containment on a user at any time:
Select the Contain User action in the Action Center. In the side pane, select Undo.
Select the user from either the user inventory, Incident page side pane, or alert side pane and select Undo.
This action restores the user's connection to the network.
Investigation capabilities with Contain User
After a user is contained, you can investigate the potential threat by viewing the blocked actions by the compromised user. In the device timeline view, you can see information about specific events, including protocol and interface granularity, and the relevant MITRE Technique associated it.
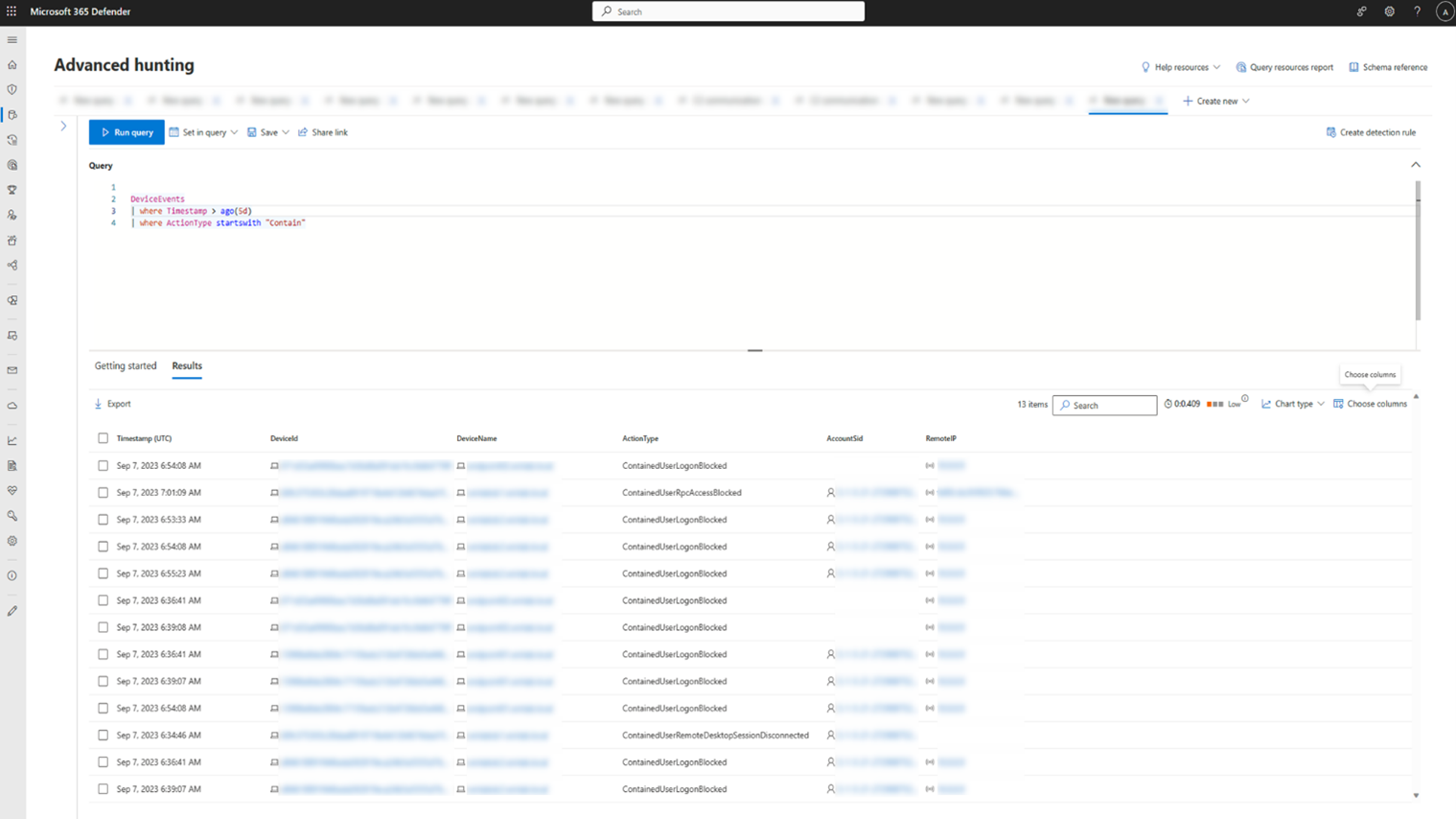
In addition, you can expand the investigation by using advanced hunting. Look for any action type starting with contain in the DeviceEvents table. Then, you can view all the different singular blocking events in relation to Contain User in your tenant, dive deeper into the context of each block, and extract the different entities and techniques associated with those events.
GPO hardening (Preview)
As part of the predictive shielding (Preview) feature, Defender for Endpoint automatically applies the GPO hardening action. Group Policy Object (GPO) hardening temporarily stops new GPO policies from being applied to devices identified as high risk. This action helps prevent potential compromise by limiting changes to critical configurations.
To enrich predictive shielding actions, we recommend you use the Microsoft Defender for Identity sensor in your environment. For more information, see Enrich predictive shielding with Microsoft Defender for Identity.
After the action is applied, you can view the action impact in the incident graph, track the actions in the Action center, and investigate further using advanced hunting. For more information, see Manage predictive shielding actions.
Safeboot hardening (Preview)
As part of the predictive shielding (Preview) feature, Defender for Endpoint automatically applies the Safeboot hardening action. Safeboot hardening helps protect devices from being compromised by enforcing stricter boot settings on devices that are predicted to be at high risk of compromise.
To enrich predictive shielding actions, we recommend you use the Microsoft Defender for Identity sensor in your environment. For more information, see Enrich predictive shielding with Microsoft Defender for Identity.
After the action is applied, you can view the action impact in the incident graph, track the actions in the Action center, and investigate further using advanced hunting. For more information, see Manage predictive shielding actions.
To view the current status of the Safeboot hardening action and other actions, see Track the action status in the Activities tab (Preview).
Consult a threat expert
You can consult a Microsoft threat expert for more insights regarding a potentially compromised device or already compromised ones. Microsoft Threat Experts can be engaged directly from within the Microsoft Defender XDR for timely and accurate response. Experts provide insights not just regarding a potentially compromised device, but also to better understand complex threats, targeted attack notifications that you get, or if you need more information about the alerts, or a threat intelligence context that you see on your portal dashboard.
See Configure and manage Endpoint Attack Notifications for details.
Check activity details and status
The Action center (https://security.microsoft.com/action-center) provides information on actions that were taken on a device or file. You are able to view the following details:
- Investigation package collection
- Antivirus scan
- App restriction
- Device isolation
All other related details are also shown, for example, submission date/time, submitting user, and if the action succeeded or failed.
The Activities tab in the Incident page shows the details and status of actions that were taken as part of the incident response. For more information, see Track the action status in the Activities tab (Preview).