Require an app protection policy on Windows devices
App protection policies apply mobile application management (MAM) to specific applications on a device. These policies allow for securing data within an application in support of scenarios like bring your own device (BYOD).
Prerequisites
- We support applying policy to the Microsoft Edge browser on devices running Windows 11 and Windows 10 version 20H2 and higher with KB5031445.
- Configured app protection policy targeting Windows devices.
- Currently unsupported in sovereign clouds.
User exclusions
Conditional Access policies are powerful tools, we recommend excluding the following accounts from your policies:
- Emergency access or break-glass accounts to prevent tenant-wide account lockout. In the unlikely scenario all administrators are locked out of your tenant, your emergency-access administrative account can be used to log into the tenant to take steps to recover access.
- More information can be found in the article, Manage emergency access accounts in Microsoft Entra ID.
- Service accounts and service principals, such as the Microsoft Entra Connect Sync Account. Service accounts are non-interactive accounts that aren't tied to any particular user. They're normally used by back-end services allowing programmatic access to applications, but are also used to sign in to systems for administrative purposes. Service accounts like these should be excluded since MFA can't be completed programmatically. Calls made by service principals won't be blocked by Conditional Access policies scoped to users. Use Conditional Access for workload identities to define policies targeting service principals.
- If your organization has these accounts in use in scripts or code, consider replacing them with managed identities. As a temporary workaround, you can exclude these specific accounts from the baseline policy.
Create a Conditional Access policy
The following policy is put in to Report-only mode to start so administrators can determine the impact they have on existing users. When administrators are comfortable that the policy applies as they intend, they can switch to On or stage the deployment by adding specific groups and excluding others.
Require app protection policy for Windows devices
The following steps help create a Conditional Access policy requiring an app protection policy when using a Windows device accessing the Office 365 apps grouping in Conditional Access. The app protection policy must also be configured and assigned to your users in Microsoft Intune. For more information about how to create the app protection policy, see the article App protection policy settings for Windows. The following policy includes multiple controls allowing devices to either use app protection policies for mobile application management (MAM) or be managed and compliant with mobile device management (MDM) policies.
Tip
App protection policies (MAM) support unmanaged devices:
- If a device is already managed through mobile device management (MDM), then Intune MAM enrollment is blocked, and app protection policy settings aren't applied.
- If a device becomes managed after MAM enrollment, app protection policy settings are no longer applied.
- Sign in to the Microsoft Entra admin center as at least a Conditional Access Administrator.
- Browse to Protection > Conditional Access > Policies.
- Select New policy.
- Give your policy a name. We recommend that organizations create a meaningful standard for the names of their policies.
- Under Assignments, select Users or workload identities.
- Under Include, select All users.
- Under Exclude, select Users and groups and choose at least your organization's emergency access or break-glass accounts.
- Under Target resources > Cloud apps > Include, select Office 365.
- Under Conditions:
- Device platforms set Configure to Yes.
- Under Include, Select device platforms.
- Choose Windows only.
- Select Done.
- Client apps set Configure to Yes.
- Select Browser only.
- Device platforms set Configure to Yes.
- Under Access controls > Grant, select Grant access.
- Select Require app protection policy and Require device to be marked as compliant.
- For multiple controls select Require one of the selected controls
- Confirm your settings and set Enable policy to Report-only.
- Select Create to create to enable your policy.
After administrators confirm the settings using report-only mode, they can move the Enable policy toggle from Report-only to On.
Tip
Organizations should also deploy a policy that blocks access from unsupported or unknown device platforms along with this policy.
Sign in to Windows devices
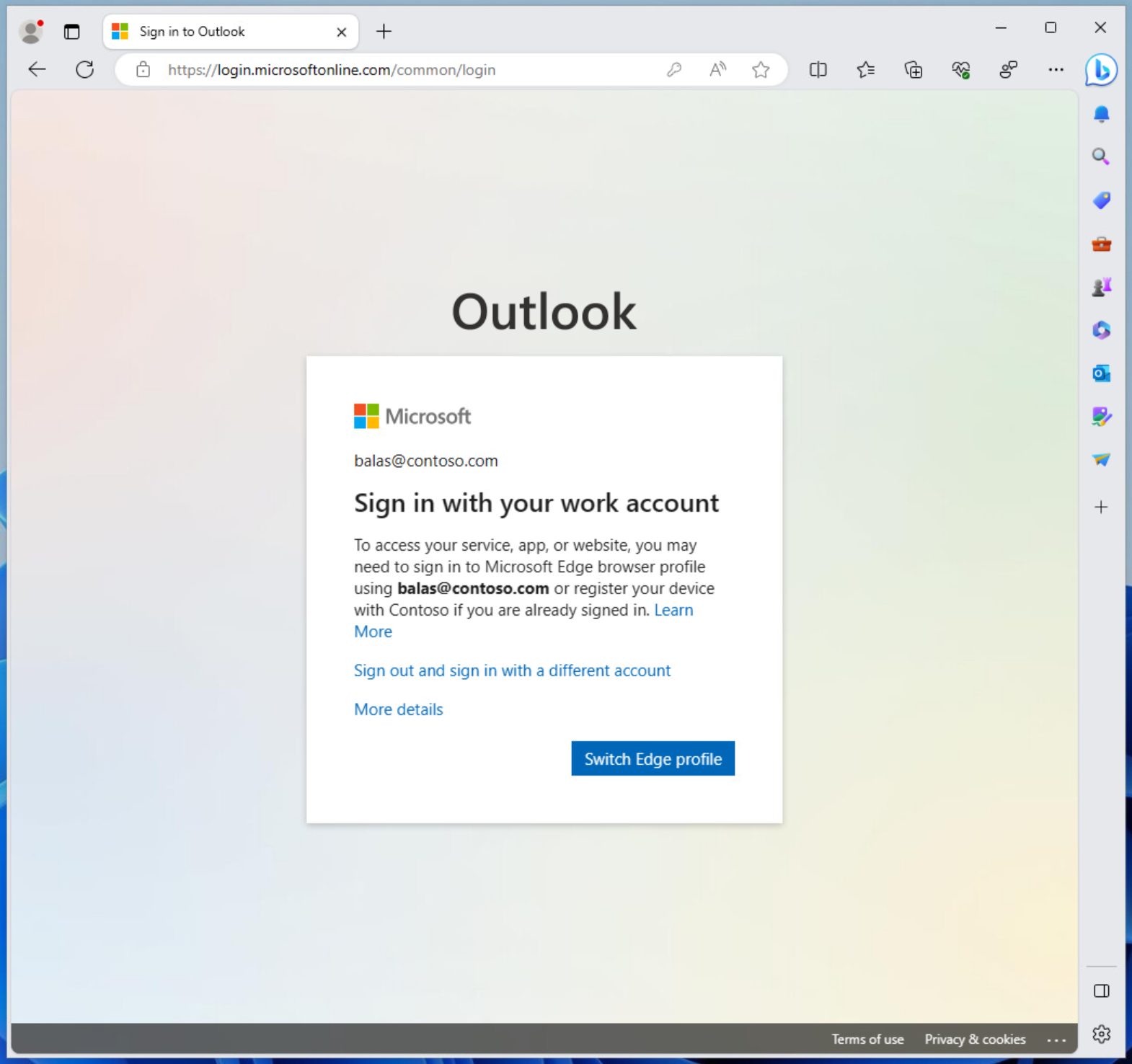
When users attempt to sign in to a site that is protected by an app protection policy for the first time, they're prompted: To access your service, app, or website, you might need to sign in to Microsoft Edge using username@domain.com or register your device with organization if you're already signed in.
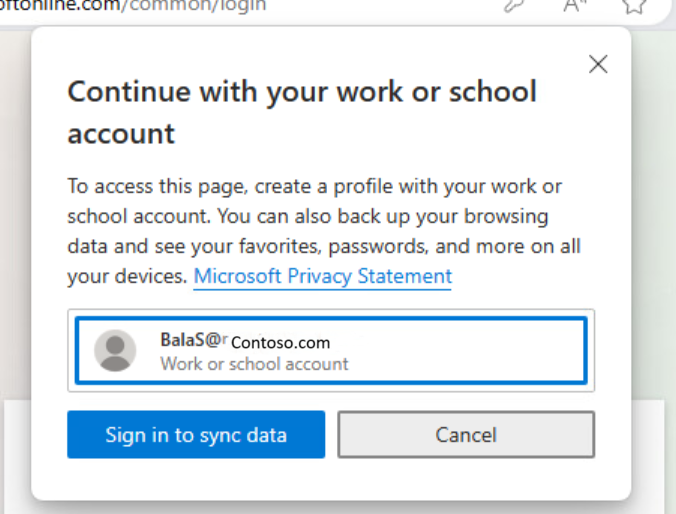
Clicking on Switch Edge profile opens a window listing their Work or school account along with an option to Sign in to sync data.
This process opens a window offering to allow Windows to remember your account and automatically sign you in to your apps and websites.
Caution
You must CLEAR THE CHECKBOX Allow my organization to manage my device. Leaving this checked enrolls your device in mobile device management (MDM) not mobile application management (MAM).
Don't select No, sign in to this app only.
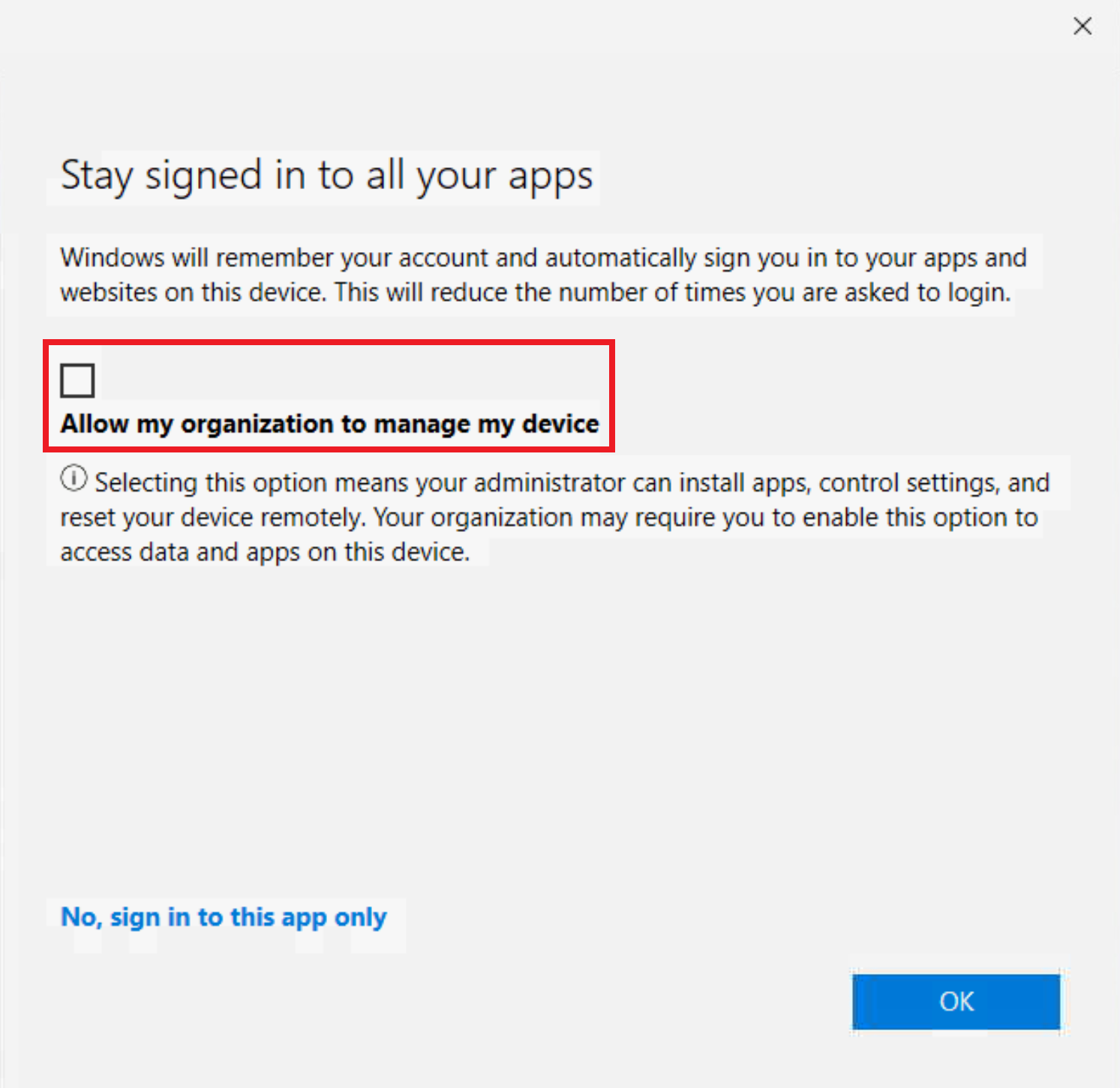
After selecting OK, you might see a progress window while policy is applied. After a few moments, you should see a window saying You're all set, app protection policies are applied.
Troubleshooting
Common issues
In some circumstances, after getting the "you're all set" page you might still be prompted to sign in with your work account. This prompt might happen when:
- Your profile is added to Microsoft Edge, but MAM enrollment is still being processed.
- Your profile is added to Microsoft Edge, but you selected "this app only" on the heads up page.
- You enrolled into MAM but your enrollment expired or you aren't compliant with your organization's requirements.
To resolve these possible scenarios:
- Wait a few minutes and try again in a new tab.
- Contact your administrator to check that Microsoft Intune MAM policies are applying to your account correctly.
Existing account
There's a known issue where there's a pre-existing, unregistered account, like user@contoso.com in Microsoft Edge, or if a user signs in without registering using the Heads Up Page, then the account isn't properly enrolled in MAM. This configuration blocks the user from being properly enrolled in MAM.
Next steps
Feedback
Coming soon: Throughout 2024 we will be phasing out GitHub Issues as the feedback mechanism for content and replacing it with a new feedback system. For more information see: https://aka.ms/ContentUserFeedback.
Submit and view feedback for