Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this article, learn to secure Oracle PeopleSoft (PeopleSoft) using Microsoft Entra ID, with F5 BIG-IP Easy Button Guided Configuration 16.1.
Integrate BIG-IP with Microsoft Entra ID for many benefits:
- Improved Zero Trust governance through Microsoft Entra preauthentication and Conditional Access
- Single sign-on (SSO) between Microsoft Entra ID and BIG-IP published services
- Manage identities and access from the Microsoft Entra admin center
Learn more:
Scenario description
For this tutorial, there's use of a PeopleSoft application using HTTP authorization headers to manage access to protected content.
Legacy applications lack modern protocols to support Microsoft Entra integration. Modernization is costly, requires planning, and introduces potential downtime risk. Instead, use an F5 BIG-IP Application Delivery Controller (ADC) to bridge the gap between legacy applications and modern ID control, with protocol transitioning.
With a BIG-IP in front of the app, you overlay the service with Microsoft Entra preauthentication and header-based SSO. This action improves the application's security posture.
Note
Gain remote access to this type of application with Microsoft Entra application proxy.
See, Remote access to on-premises applications through Microsoft Entra application proxy.
Scenario architecture
The secure hybrid access (SHA) solution for this tutorial has the following components:
- PeopleSoft Application - BIG-IP published service secured by Microsoft Entra SHA
- Microsoft Entra ID - Security Assertion Markup Language (SAML) identity provider (IdP) that verifies user credentials, Conditional Access, and SAML-based SSO to the BIG-IP
- Through SSO, Microsoft Entra ID provides session attributes to the BIG-IP
- BIG-IP - reverse-proxy and SAML service provider (SP) to the application. It delegates authentication to the SAML IdP, then performs header-based SSO to the PeopleSoft service.
For this scenario, SHA supports SP- and IdP-initiated flows. The following diagram illustrates the SP-initiated flow.
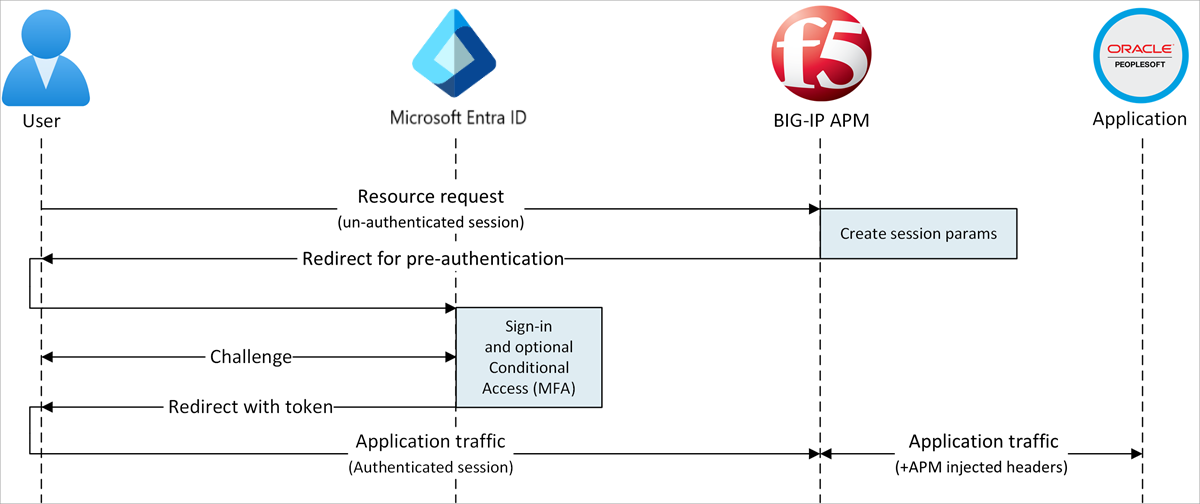
- User connects to application endpoint (BIG-IP).
- BIG-IP APM access policy redirects user to Microsoft Entra ID (SAML IdP).
- Microsoft Entra preauthenticates user and applies Conditional Access policies.
- User is redirected to BIG-IP (SAML SP) and SSO occurs with issued SAML token.
- BIG-IP injects Microsoft Entra attributes as headers in the request to the application.
- Application authorizes request and returns payload.
Prerequisites
- A Microsoft Entra ID Free account, or higher
- If you don't have one, get an Azure free account
- A BIG-IP or a BIG-IP Virtual Edition (VE) in Azure
- Any of the following F5 BIG-IP licenses:
- F5 BIG-IP® Best bundle
- F5 BIG-IP APM standalone license
- F5 BIG-IP APM add-on license on an existing BIG-IP F5 BIG-IP® Local Traffic Manager™ (LTM)
- 90-day BIG-IP full feature trial license
- User identities synchronized from an on-premises directory to Microsoft Entra ID, or created in Microsoft Entra ID and flowed back to the on-premises directory
- One of the following roles: Cloud Application Administrator, or Application Administrator.
- An SSL Web certificate to publish services over HTTPS, or use default BIG-IP certs for testing
- A PeopleSoft environment
BIG-IP configuration
This tutorial uses Guided Configuration 16.1 with an Easy button template.
With the Easy Button, admins don't go between Microsoft Entra ID and a BIG-IP to enable services for SHA. APM Guided Configuration wizard and Microsoft Graph handle deployment and policy management. The integration ensures applications support identity federation, SSO, and Conditional Access.
Note
Replace example strings or values in this tutorial with those in your environment.
Register the Easy Button
Before a client or service accesses Microsoft Graph, the Microsoft identity platform must trust it.
Learn more: Quickstart: Register an application with the Microsoft identity platform
The following instructions help you create a tenant app registration to authorize Easy Button access to Graph. With these permissions, the BIG-IP pushes the configurations to establish a trust between a SAML SP instance for published application, and Microsoft Entra ID as the SAML IdP.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Entra ID > App registrations > New registration.
Enter an application Name.
For Accounts in this organizational directory only, specify who uses the application.
Select Register.
Navigate to API permissions.
Authorize the following Microsoft Graph Application permissions:
- Application.ReadWrite.All
- Application.ReadWrite.OwnedBy
- Directory.Read.All
- Group.Read.All
- IdentityRiskyUser.Read.All
- Policy.Read.All
- Policy.ReadWrite.ApplicationConfiguration
- Policy.ReadWrite.ConditionalAccess
- User.Read.All
Grant admin consent to your organization.
Go to Certificates & Secrets.
Generate a new Client Secret and note it.
Go to Overview and note the Client ID and Tenant ID.
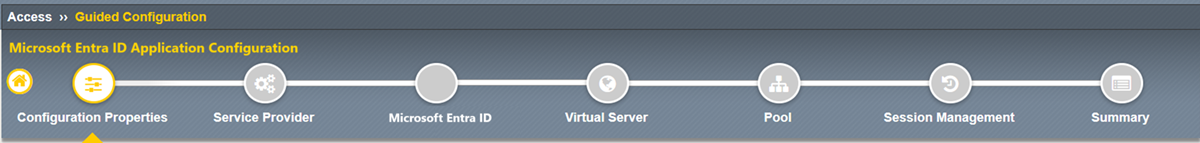
Configure the Easy Button
- Initiate the APM Guided Configuration.
- Launch the Easy Button template.
- Navigate to Access > Guided Configuration.
- Select Microsoft Integration.
- Select Microsoft Entra Application.
- Review the configuration sequence.
- Select Next
- Follow the configuration sequence.
Configuration Properties
Use the Configuration Properties tab to create new application configurations and SSO objects. The Azure Service Account Details section represents the client you registered in the Microsoft Entra tenant, as an application. Use the settings for BIG-IP OAuth client to register a SAML SP in the tenant, with SSO properties. Easy Button does this action for BIG-IP services published and enabled for SHA.
Note
Some of the following settings are global. You can reuse them to publish more applications.
- Enter a Configuration Name. Unique names help distinguish configurations.
- For Single Sign-On (SSO) & HTTP Headers, select On.
- Enter the Tenant ID, Client ID, and Client Secret you noted.
- Confirm the BIG-IP connects to the tenant.
- Select Next.
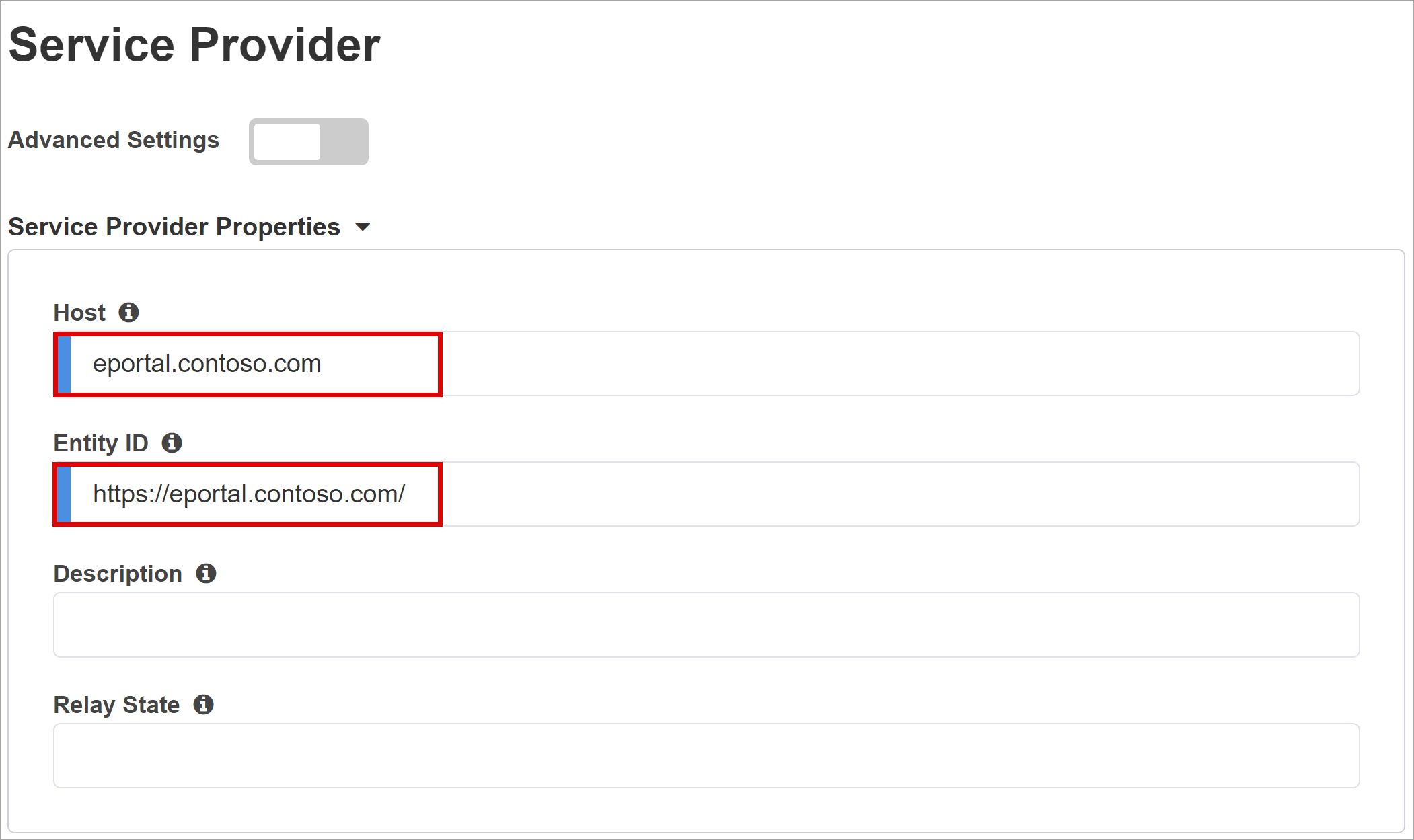
Service Provider
Use the Service Provider settings to define SAML SP properties for the APM instance that represents the SHA-secured application.
- For Host, enter the public FQDN of the secured application.
- For Entity ID, enter the identifier Microsoft Entra ID uses to identify the SAML SP requesting a token.
(Optional) For Security Settings, indicate Microsoft Entra ID encrypts issued SAML assertions. This option increases assurance that content tokens aren't intercepted, nor data compromised.
From the Assertion Decryption Private Key list, select Create New.
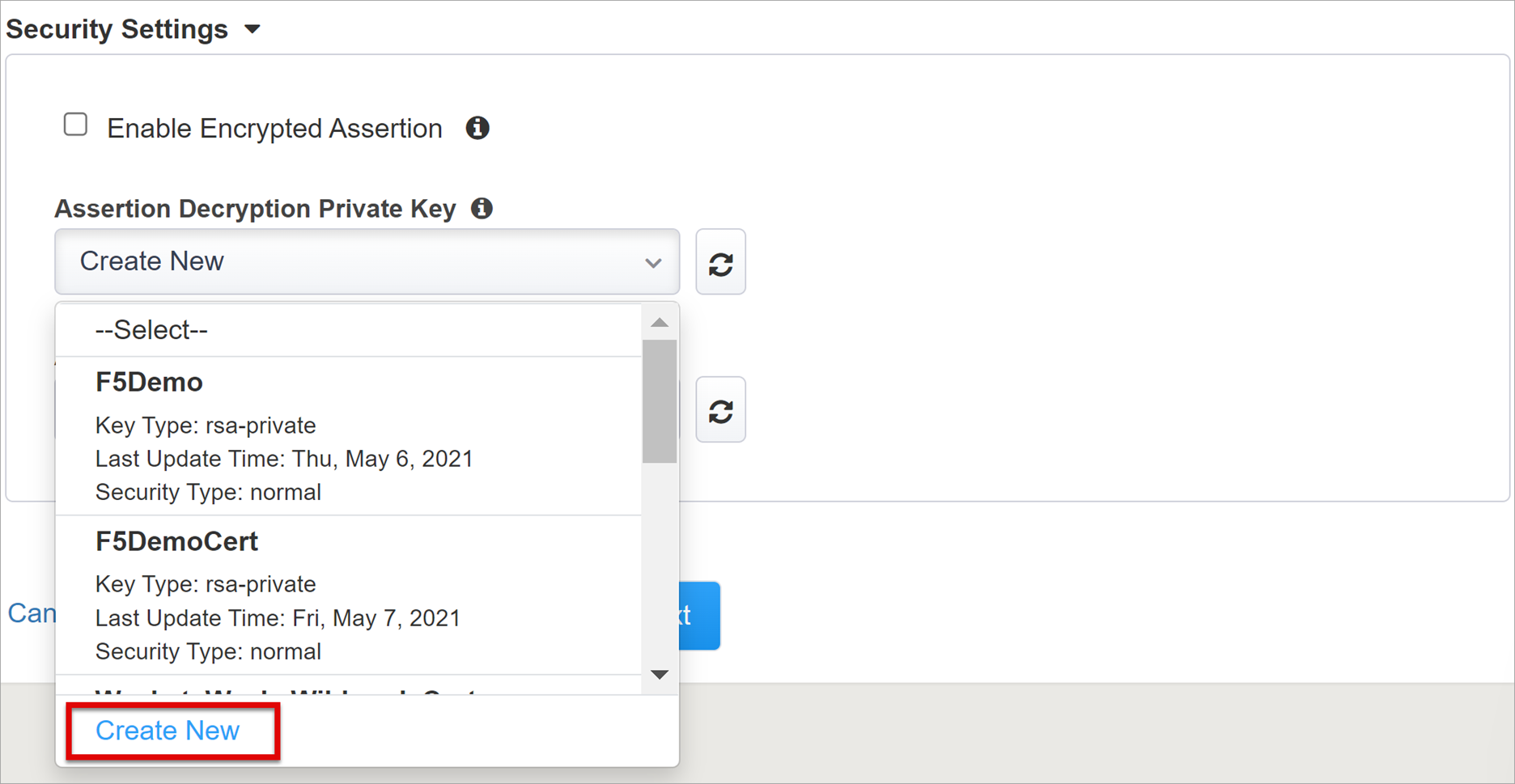
- Select OK.
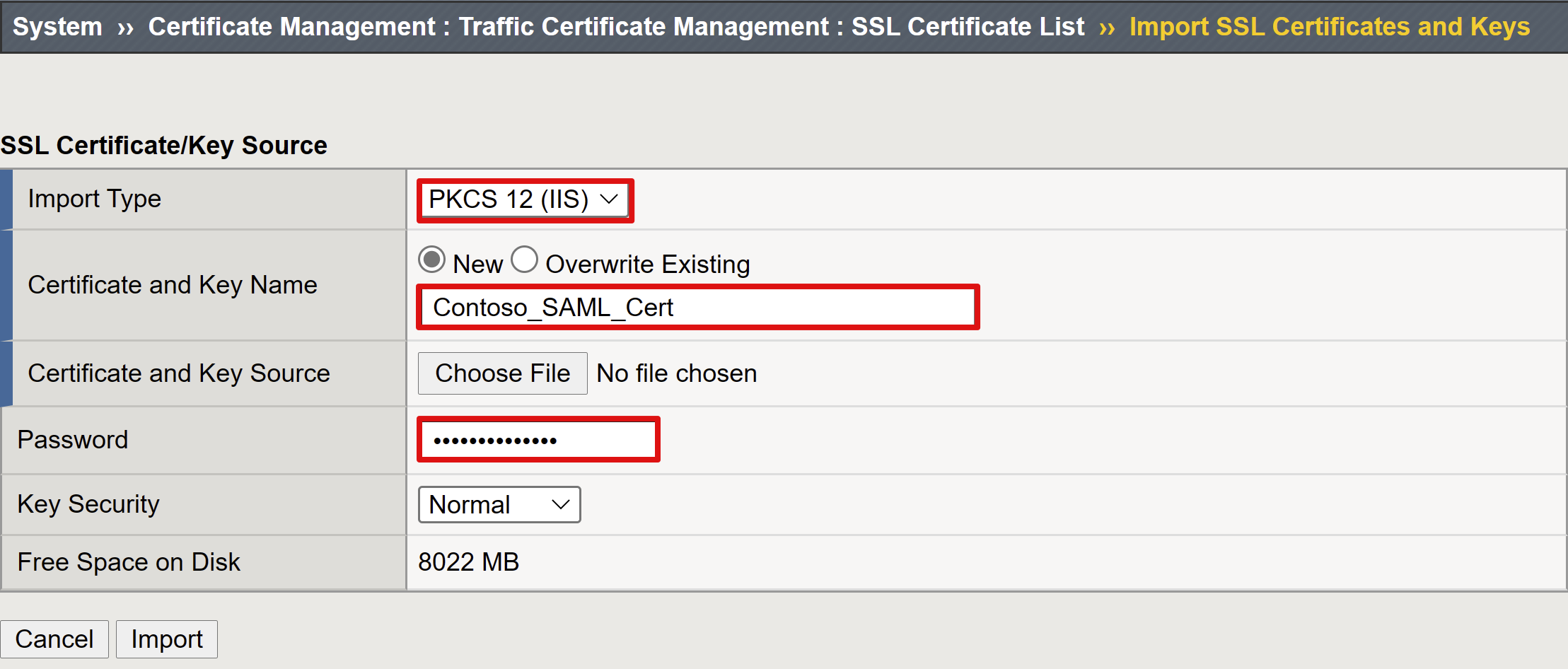
- The Import SSL Certificate and Keys dialog appears in a new tab.
- For Import Type, select PKCS 12 (IIS). This option imports your certificate and private key.
- Close the browser tab to return to the main tab.
- For Enable Encrypted Assertion, check the box.
- If you enabled encryption, from the Assertion Decryption Private Key list, select your certificate. This private key is for the certificate that BIG-IP APM uses to decrypt Microsoft Entra assertions.
- If you enabled encryption, from the Assertion Decryption Certificate list, select your certificate. BIG-IP uploads this certificate to Microsoft Entra ID to encrypt issued SAML assertions.

Microsoft Entra ID
The Easy Button has templates for Oracle PeopleSoft, Oracle E-Business Suite, Oracle JD Edwards, SAP ERP and a generic SHA template.
- Select Oracle PeopleSoft.
- Select Add.
Azure Configuration
Enter Display Name for the app BIG-IP creates in the tenant. The name appears on an icon in My Apps.
(Optional) For Sign On URL enter the PeopleSoft application public FQDN.
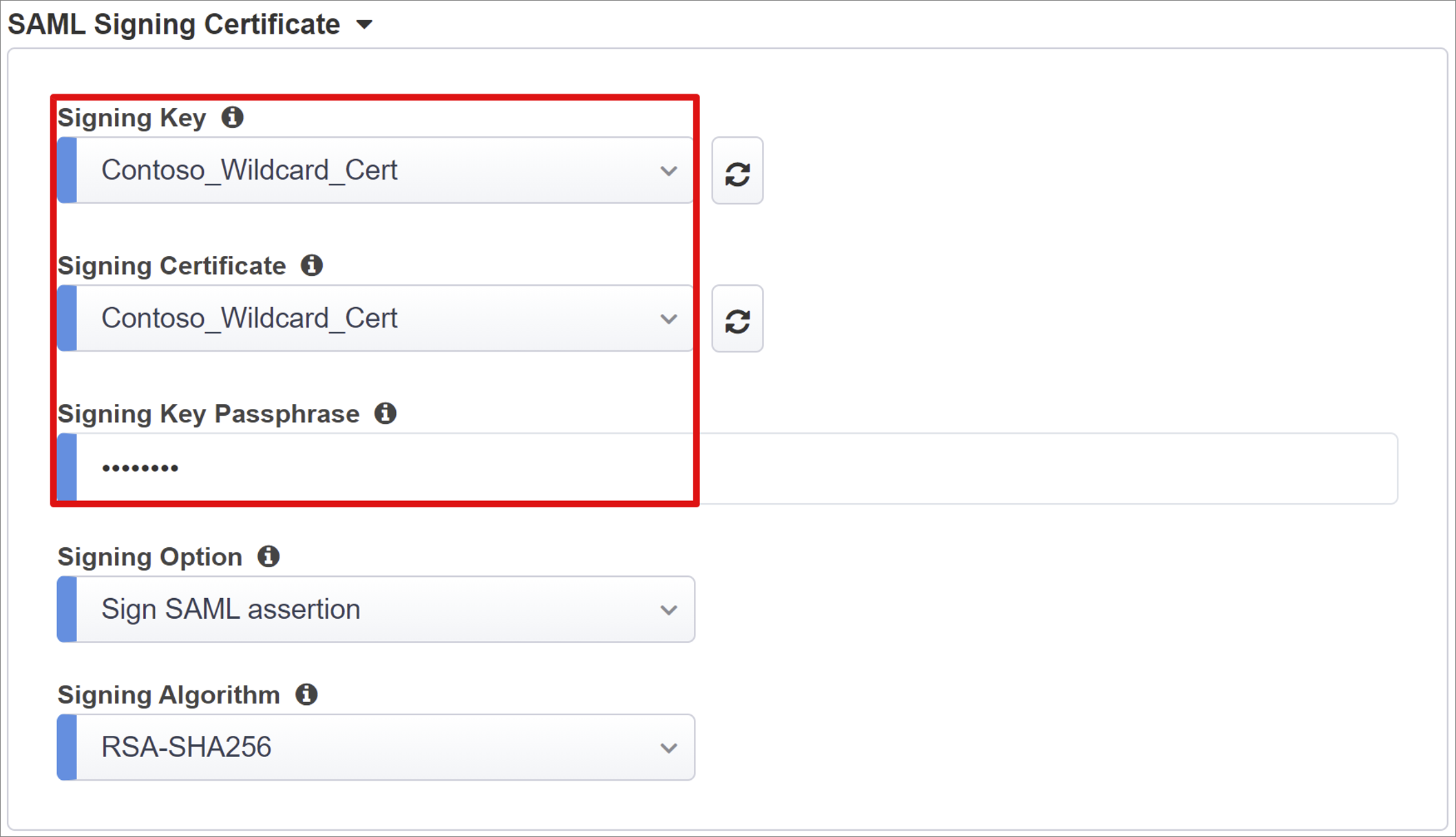
Next to the Signing Key and Signing Certificate, select refresh. This action locates the certificate you imported.
For Signing Key Passphrase, enter the certificate password.
(Optional) For Signing Option, select an option. This selection ensures BIG-IP accepts tokens and claims signed by Microsoft Entra ID.
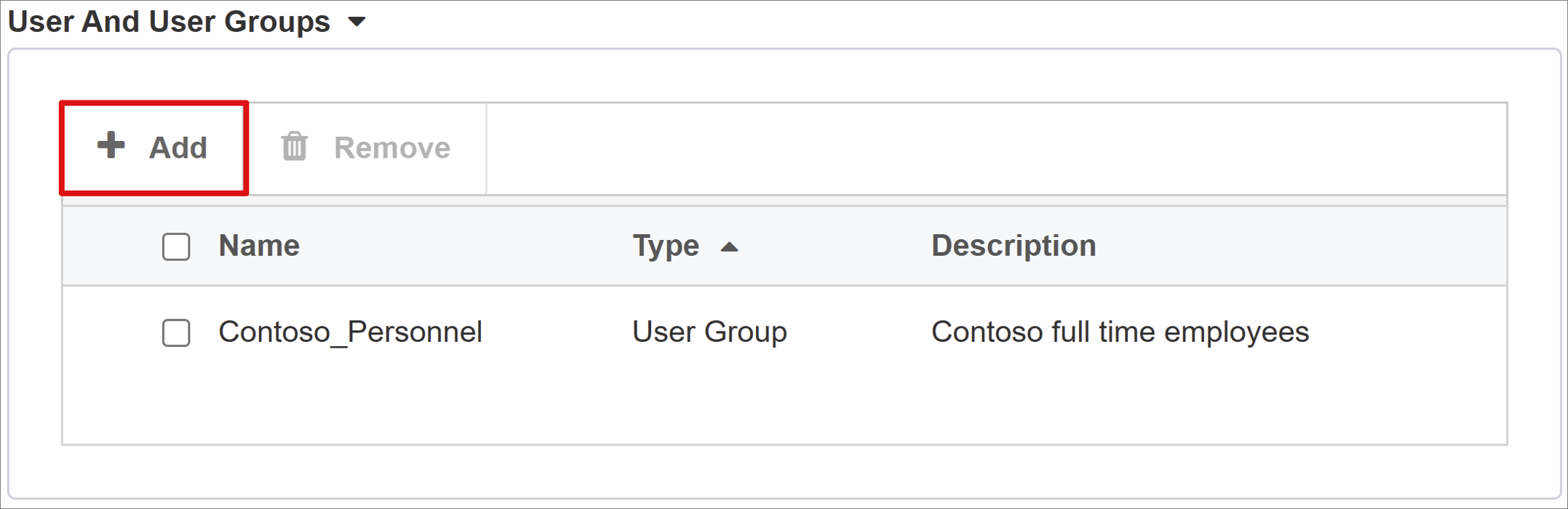
- User And User Groups are dynamically queried from the Microsoft Entra tenant.
- Add a user or group for testing, otherwise access is denied.
User Attributes & Claims
When a user authenticates, Microsoft Entra ID issues a SAML token with default claims and attributes identifying the user. The User Attributes & Claims tab has default claims to issue for the new application. Use it to configure more claims. The Easy Button template has the employee ID claim required by PeopleSoft.
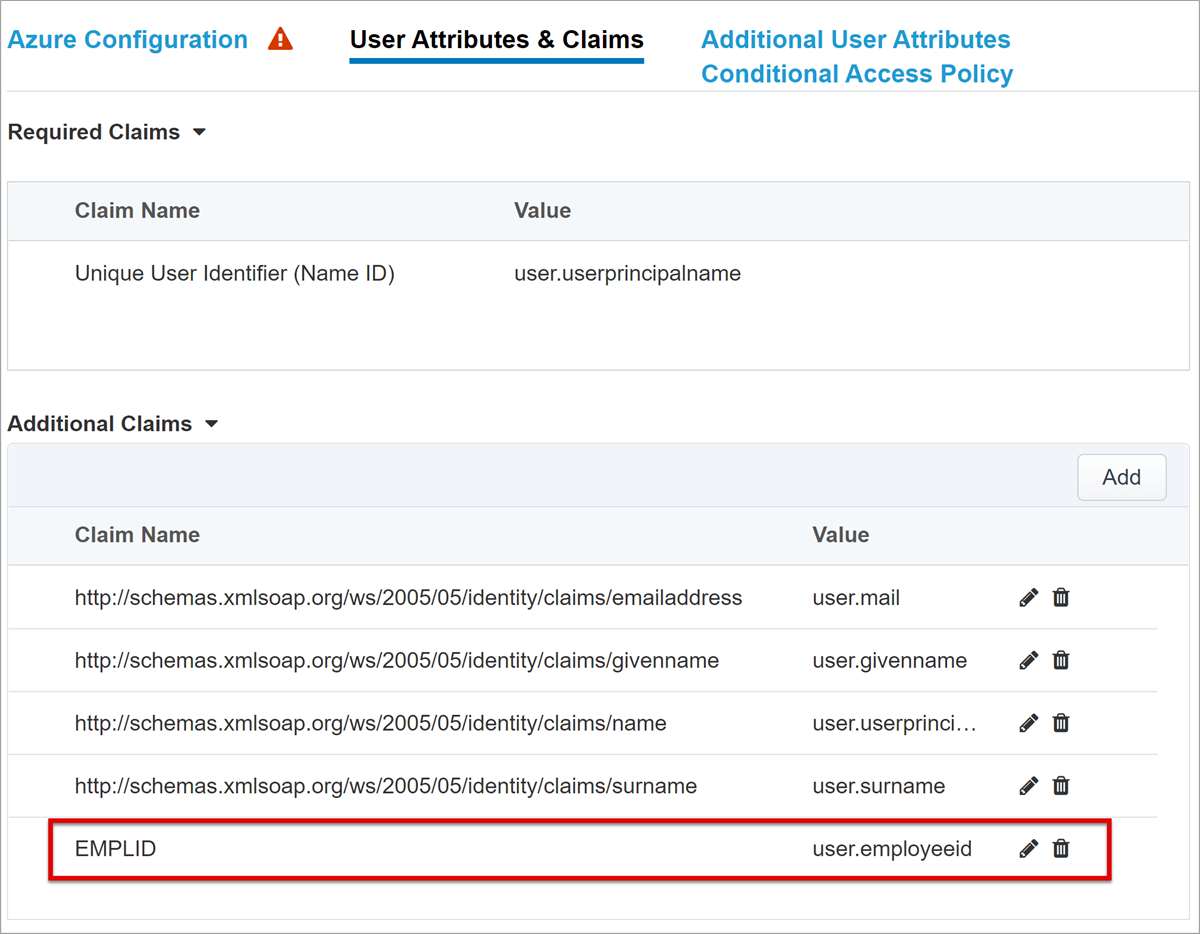
If needed, include other Microsoft Entra attributes. The sample PeopleSoft application requires predefined attributes.
Additional User Attributes
The Additional User Attributes tab supports distributed systems that require attributes are stored in other directories for session augmentation. Attributes from an LDAP source are injected as more SSO headers to control access based on roles, Partner IDs, and so on.
Note
This feature has no correlation to Microsoft Entra ID; it's another attribute source.
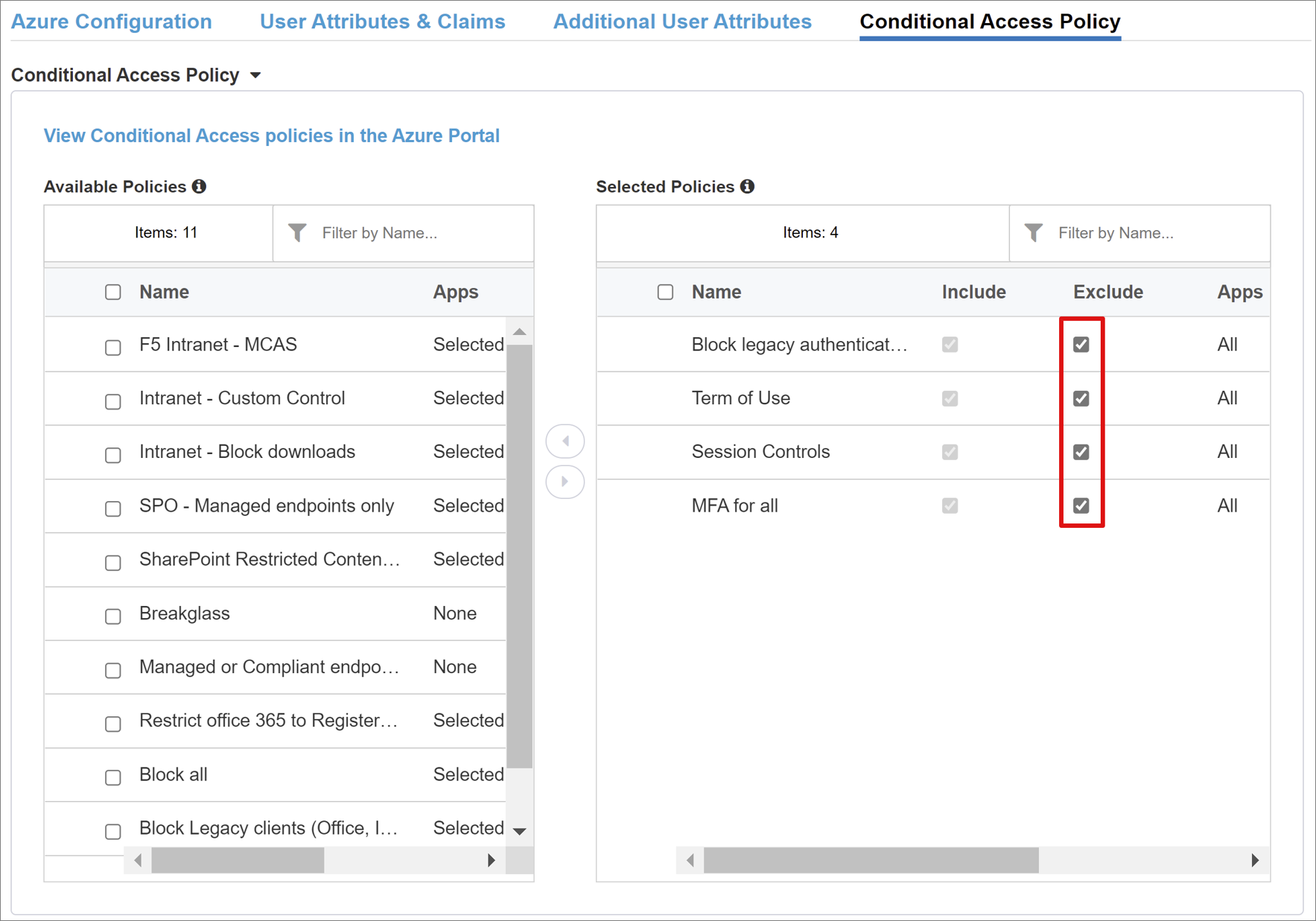
Conditional Access Policy
Conditional Access policies are enforced after Microsoft Entra preauthentication to control access based on device, application, location, and risk signals. The Available Policies view has Conditional Access policies with no user actions. The Selected Policies view has policies targeting cloud apps. You can't deselect or move these policies to the Available Policies list because they're enforced at the tenant level.
Select a policy for the application.
- In the Available Policies list, select a policy.
- Select the right arrow and move the policy to Selected Policies.
Selected policies have the Include or Exclude option checked. If both options are checked, the policy isn't enforced.
Note
The policy list appears once, when you select the tab. Use Refresh for the wizard to query the tenant. This option appears after the application is deployed.
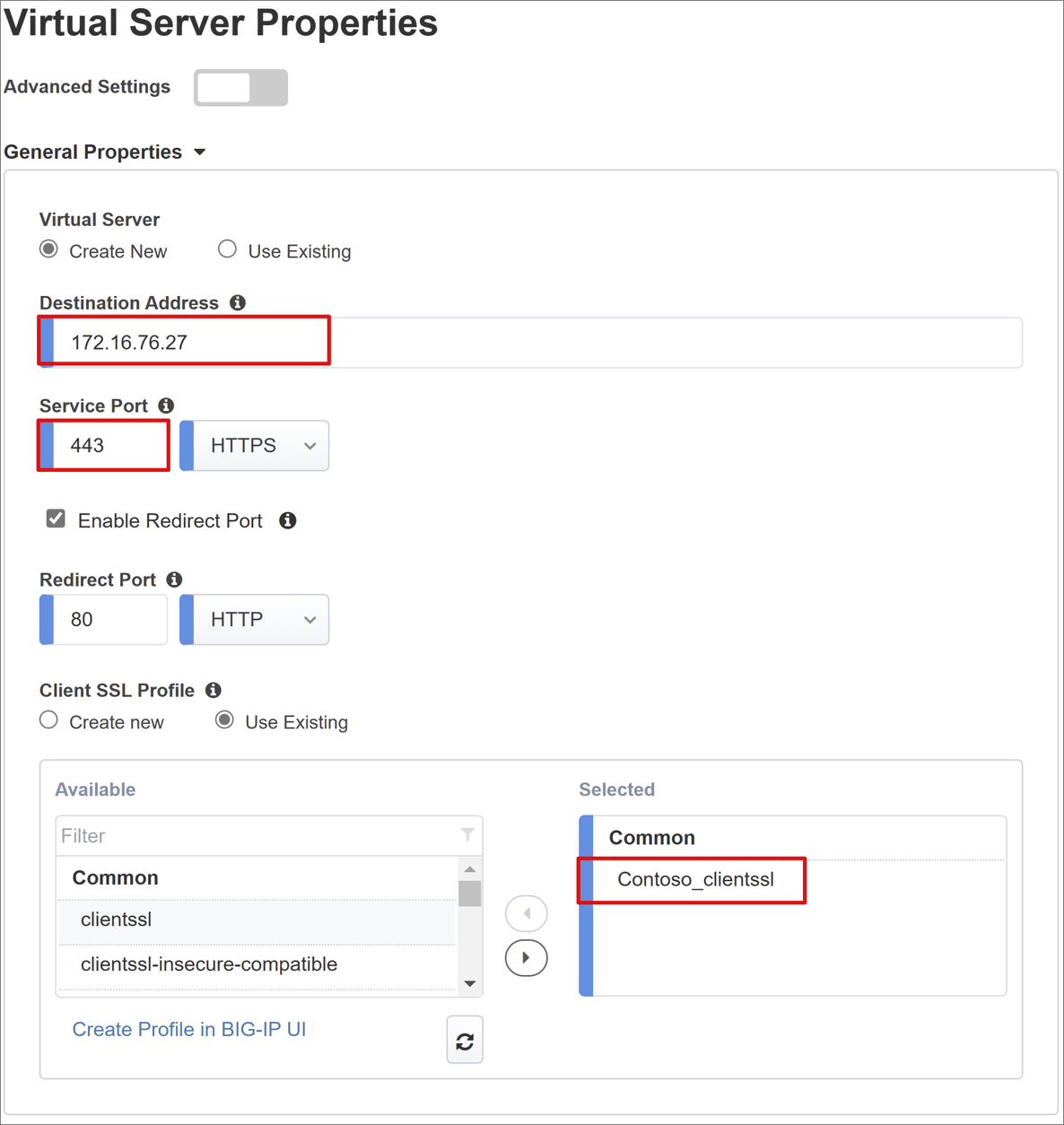
Virtual Server Properties
A virtual server is a BIG-IP data plane object represented by a virtual IP address. The server listens for client requests to the application. Received traffic is processed and evaluated against the virtual server APM profile. Then, traffic is directed according to policy.
- For Destination Address, enter the IPv4 or IPv6 address BIG-IP uses to receive client traffic. A corresponding record appears in DNS, which enables clients to resolve the published application's external URL to the IP. Use a test computer localhost DNS for testing.
- For Service Port, enter 443 and select HTTPS.
- For Enable Redirect Port, check the box.
- For Redirect Port, enter 80 and select HTTP. This option redirects incoming HTTP client traffic to HTTPS.
- For Client SSL Profile, select Use Existing.
- Under Common select the option you created. If testing, leave the default. Client SSL Profile enables the virtual server for HTTPS, so client connections are encrypted over TLS.
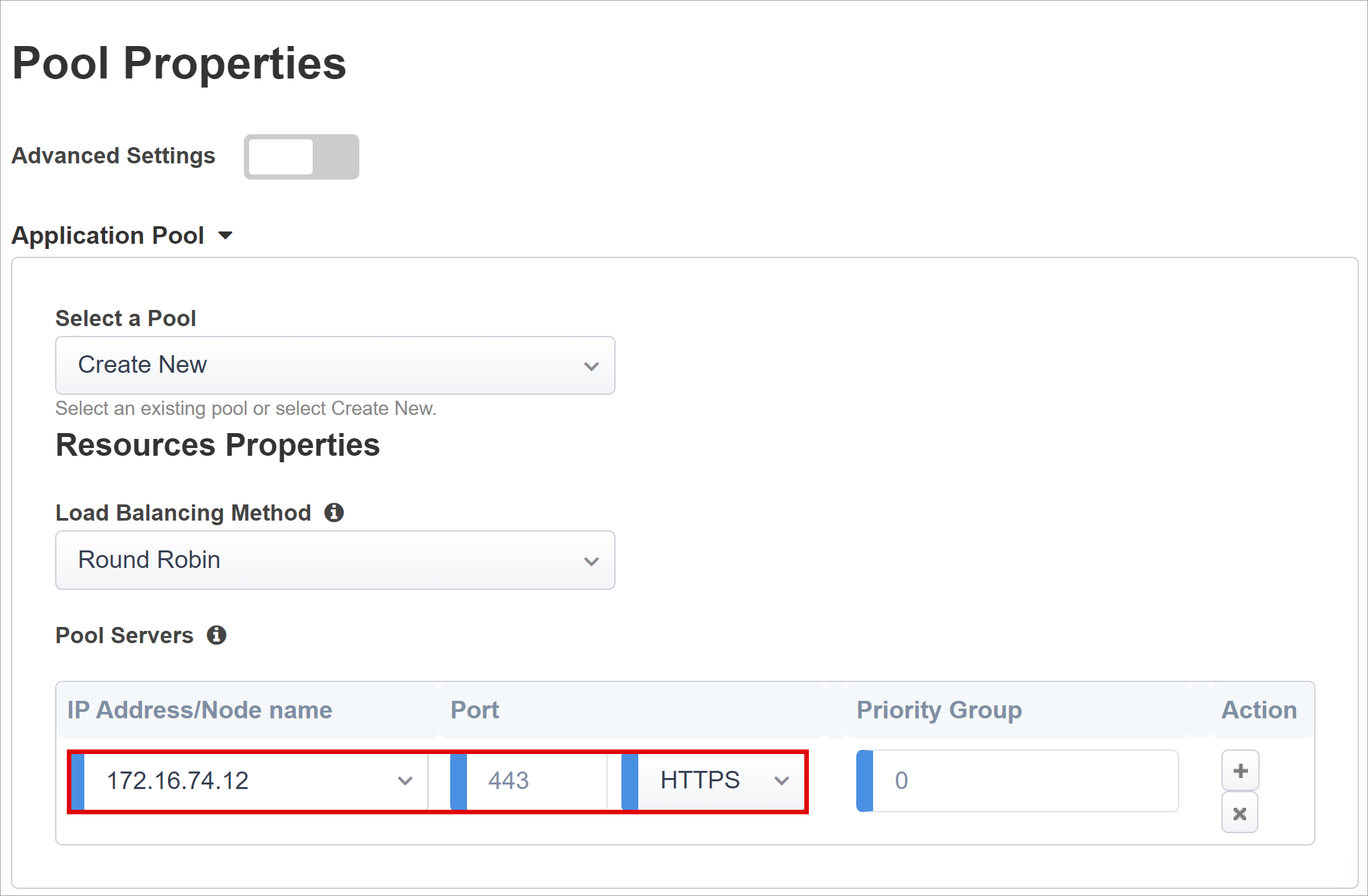
Pool Properties
The Application Pool tab has services behind a BIG-IP, represented as a pool with application servers.
- For Select a Pool, select Create New, or select one.
- For Load Balancing Method, select Round Robin.
- For Pool Servers, in IP Address/Node Name select a node, or enter an IP and port for servers hosting the PeopleSoft application.
Single sign-on & HTTP Headers
The Easy Button wizard supports Kerberos, OAuth Bearer, and HTTP authorization headers for SSO to published applications. The PeopleSoft application expects headers.
- For HTTP Headers, check the box.
- For Header Operation, select replace.
- For Header Name, enter PS_SSO_UID.
- For Header Value, enter %{session.sso.token.last.username}.

Note
APM session variables in curly brackets are case-sensitive. For instance, if you enter OrclGUID, and the attribute name is orclguid, attribute mapping fails.
Session Management
Use BIG-IP session management settings to define conditions for user sessions termination or continuation. Set limits for users and IP addresses, and corresponding user info.
To learn more, go to support.f5.com for K18390492: Security | BIG-IP APM operations guide
Not covered in the operations guide is single log-out (SLO) functionality, which ensures IdP, BIG-IP, and user agent sessions terminate when users sign out. When the Easy Button instantiates a SAML application in the Microsoft Entra tenant, it populates the Logout URL with the APM SLO endpoint. IdP-initiated sign out from My Apps terminates BIG-IP and client sessions.
Published-application SAML federation data is imported from the tenant. This action provides the APM with the SAML sign-out endpoint for Microsoft Entra ID, which ensures SP-initiated sign out terminates client and Microsoft Entra sessions. The APM needs to know when a user signs out.
When the BIG-IP webtop portal accesses published applications, the APM processes a sign out to call the Microsoft Entra sign-out endpoint. If the BIG-IP webtop portal isn't used, the user can't instruct the APM to sign out. If the user signs out of the application, the BIG-IP is oblivious. SP-initiated sign out needs secure session termination. Add an SLO function to your application Sign out button, to redirect your client to the Microsoft Entra SAML or BIG-IP sign out endpoint. The SAML sign out endpoint URL for your tenant in App Registrations > Endpoints.
If you can't change the app, consider having the BIG-IP listen for application sign out calls, and trigger SLO. For more information, see PeopleSoft Single Logout in the following section.
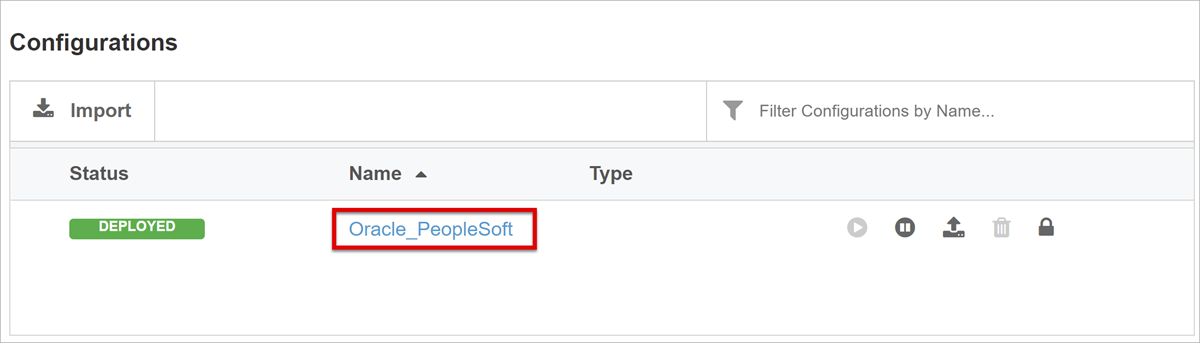
Deployment
- Select Deploy.
- Verify the application in the tenant list of Enterprise applications.
- The application is published and accessible with SHA.
Configure PeopleSoft
Use Oracle Access Manager for PeopleSoft application identity and access management.
To learn more, got o docs.oracle.com for Oracle Access Manger Integration Guide, Integrating PeopleSoft
Configure Oracle Access Manager SSO
Configure Oracle Access Manager to accept SSO from the BIG-IP.
- Sign into the Oracle console with admin permissions.
- Navigate to PeopleTools > Security.
- Select User Profiles.
- Select User Profiles.
- Create a new user profile.
- For User ID, enter OAMPSFT
- For User Role, enter PeopleSoft User.
- Select Save.
- Navigate to People Tools > Web Profile.
- Select the web profile.
- On Security tab, in Public Users, select Allow Public Access.
- For User ID, enter OAMPSFT.
- Enter the Password.
- Leave the Peoplesoft console.
- Start PeopleTools Application Designer.
- Right-click the LDAPAUTH field.
- Select View PeopleCode.
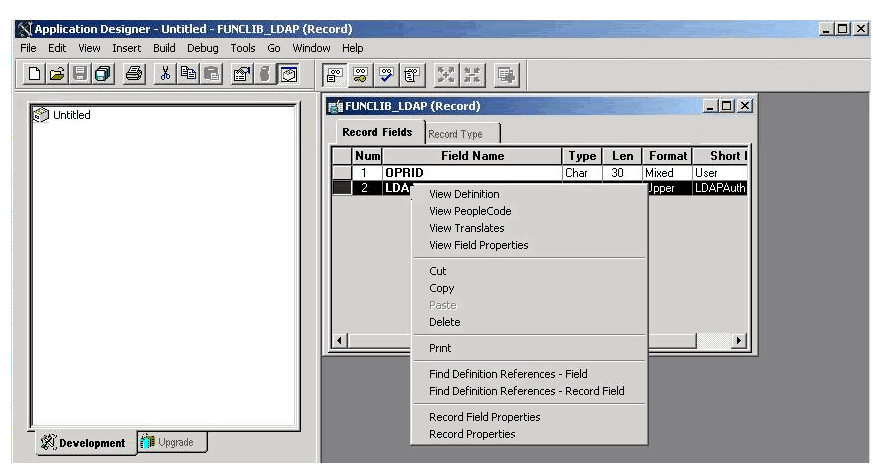
The LDAPAUTH code windows opens.
Locate the OAMSSO_AUTHENTICATION function.
Replace the &defaultUserId value with OAMPSFT.
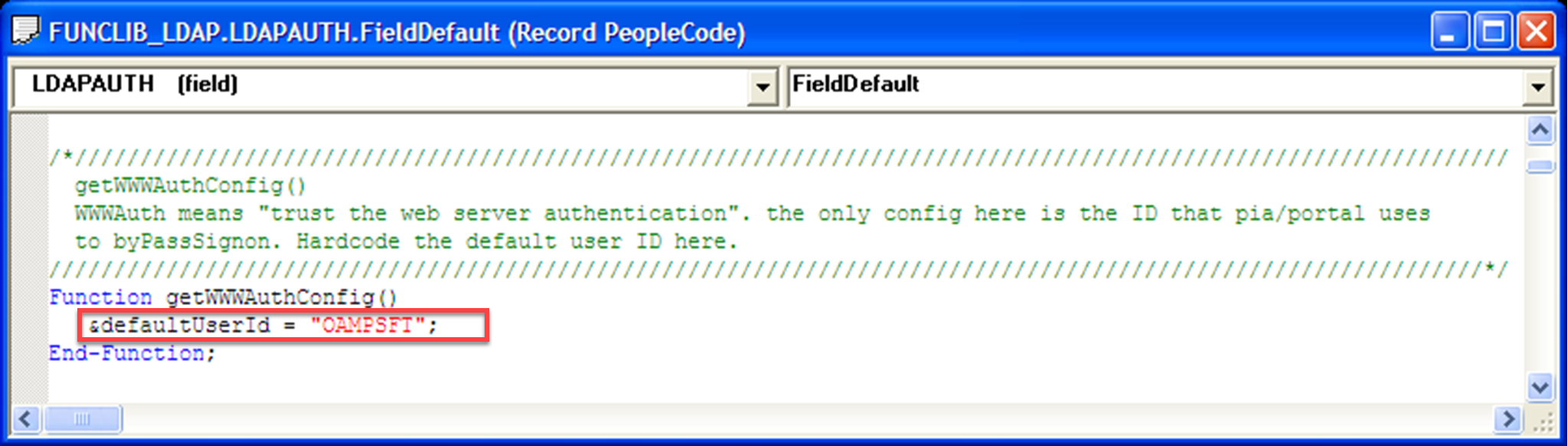
Save the record.
Navigate to **PeopleTools > Security.
Select Security Objects.
Select Sign on PeopleCode.
Enable OAMSSO_AUTHENTICATION.
PeopleSoft Single Logout
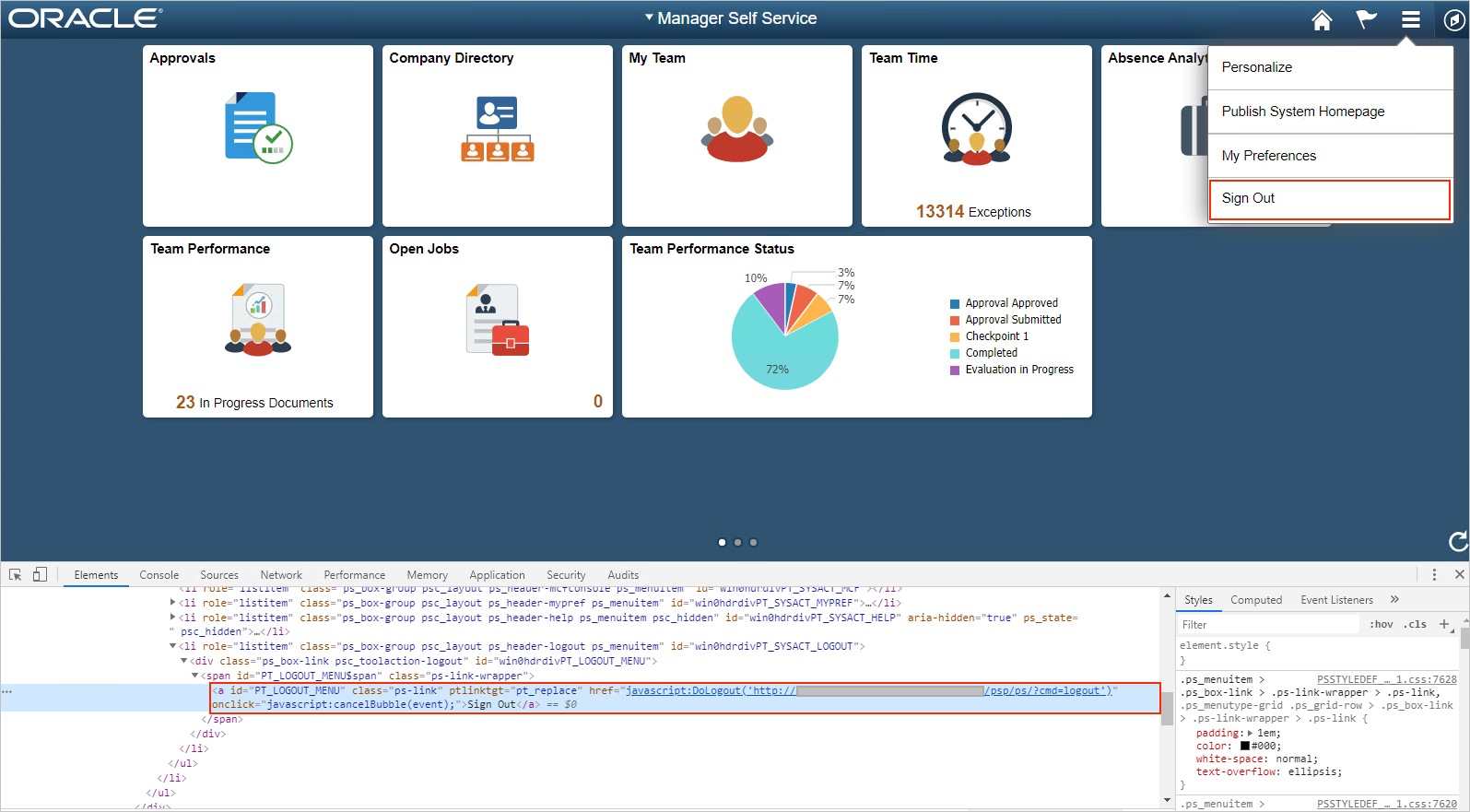
When you sign out of My Apps, PeopleSoft SLO is initiated, which in turn calls the BIG-IP SLO endpoint. BIG-IP needs instructions to perform SLO on behalf of the application. Have the BIG-IP listen for user sign out requests to PeopleSoft, and then trigger SLO.
Add SLO support for PeopleSoft users.
- Obtain the PeopleSoft portal sign-out URL.
- Open the portal with a web browser.
- Enable the debug tools.
- Locate the element with the PT_LOGOUT_MENU ID.
- Save the URL path with the query parameters. In this example:
/psp/ps/?cmd=logout.
Create a BIG-IP iRule to redirect users to the SAML SP sign out endpoint: /my.logout.php3.
- Navigate to **Local Traffic > iRules List.
- Select Create.
- Enter a rule Name.
- Enter the following command lines.
when HTTP_REQUEST {switch -glob -- [HTTP::uri] { "/psp/ps/?cmd=logout" {HTTP::redirect "/my.logout.php3" }}}
- Select Finished.
Assign the iRule to the BIG-IP Virtual Server.
- Navigate to Access > Guided Configuration.
- Select the PeopleSoft application configuration link.
- From the top navigation bar, select Virtual Server.
- For Advanced Settings, select *On.
- Scroll to the bottom.
- Under Common, add the iRule you created.
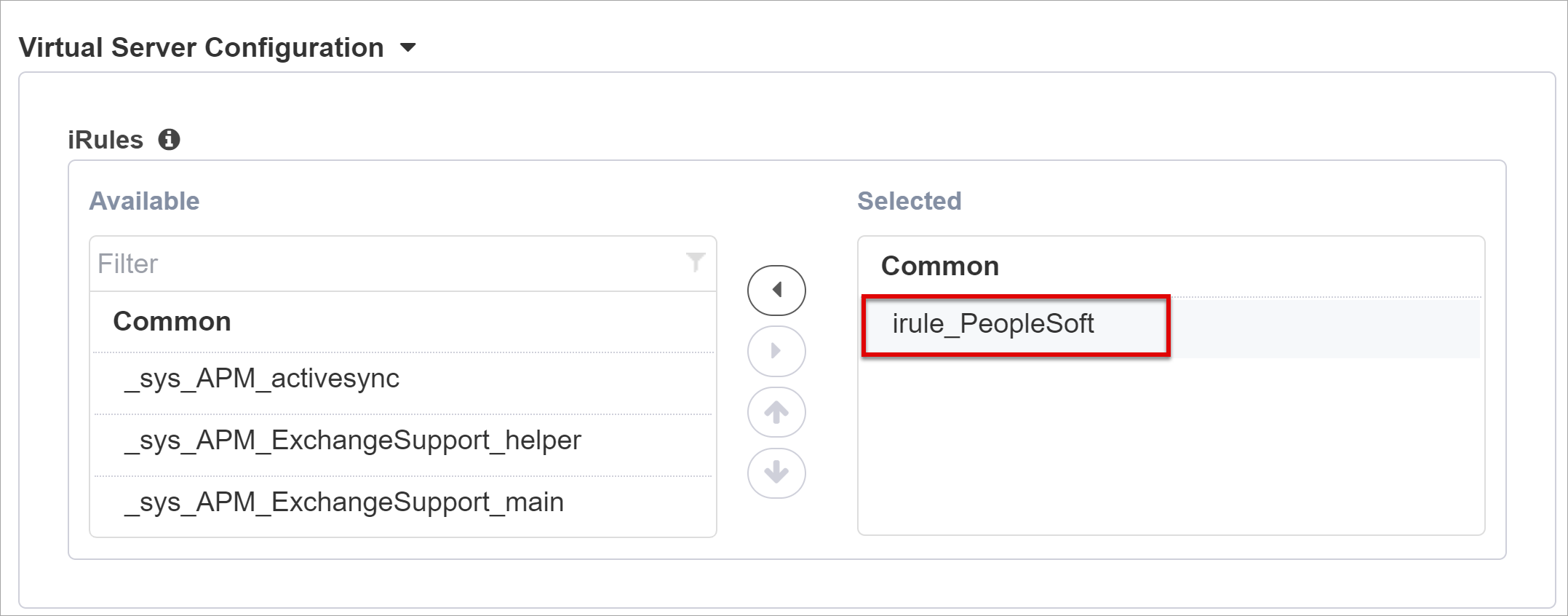
- Select Save.
- Select Next.
- Continue to configure settings.
To learn more, go to support.f5.com for:
- K42052145: Configuring automatic session termination (logout) based on a URI-referenced file name
- K12056: Overview of the Logout URI Include option
Default to PeopleSoft landing page
Redirect user requests from the root ("/") to the external PeopleSoft portal, usually located in: "/psc/ps/EXTERNAL/HRMS/c/NUI_FRAMEWORK.PT_LANDINGPAGE.GBL"
- Navigate to Local Traffic > iRule.
- Select iRule_PeopleSoft.
- Add the following command lines.
when HTTP_REQUEST {switch -glob -- [HTTP::uri] {"/" {HTTP::redirect "/psc/ps/EXTERNAL/HRMS/c/NUI_FRAMEWORK.PT_LANDINGPAGE.GB"/psp/ps/?cmd=logout" {HTTP::redirect "/my.logout.php3"} } }
- Assign the iRule to the BIG-IP Virtual Server.
Confirm configuration
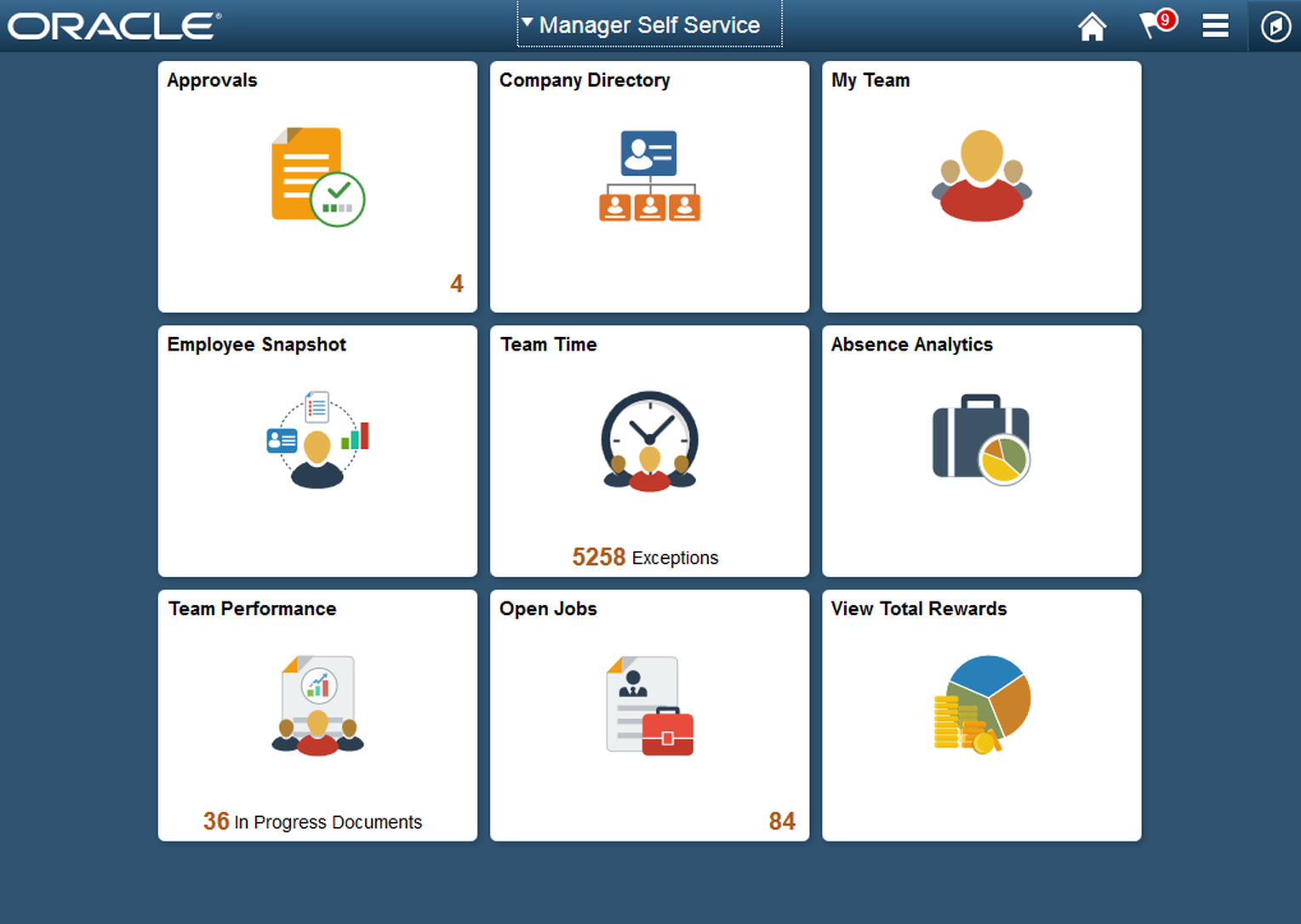
With a browser, go to the PeopleSoft application external URL, or select the application icon in My Apps.
Authenticate to Microsoft Entra ID.
You're redirected to the BIG-IP virtual server and signed in with SSO.
Note
You can block direct access to the application, thereby enforcing a path through the BIG-IP.
Advanced deployment
Sometimes, the Guided Configuration templates lack flexibility.
Learn more: Tutorial: Configure F5 BIG-IP Access Policy Manager for header-based SSO
Alternatively, in BIG-IP disable the Guided Configuration strict management mode. You can manually change configurations, although most configurations are automated with wizard templates.
- Navigate to Access > Guided Configuration.
- At the end of the row, select the padlock.

Changes with the wizard UI aren't possible, however BIG-IP objects associated with the application published instance are unlocked for management.
Note
When you reenable strict mode and deploy a configuration, settings performed outside Guided Configuration are overwritten. We recommend advanced configuration for production services.
Troubleshooting
Use BIG-IP logging to isolate issues with connectivity, SSO, policy violations, or misconfigured variable mappings.
Log verbosity
- Navigate to Access Policy > Overview.
- Select Event Logs.
- Select Settings.
- Select the row of your published application.
- SelectEdit.
- Select Access System Logs
- From the SSO list, select Debug.
- Select OK.
- Reproduce your issue.
- Inspect the logs.
When complete, revert this feature because verbose mode generates lots of data.
BIG-IP error message
If a BIG-IP error appears after Microsoft Entra preauthentication, it's possible the issue relates to Microsoft Entra ID to BIG-IP SSO.
- Navigate to Access > Overview.
- Select Access reports.
- Run the report for the last hour.
- Review the logs for clues.
Use the session's View session link to confirm the APM receives expected Microsoft Entra claims.
No BIG-IP error message
If no BIG-IP error message appears, the issue might be related to the back-end request, or BIG-IP to application SSO.
- Navigate to Access Policy > Overview.
- Select Active Sessions.
- Select the active session link.
Use the View Variables link to determine SSO issues, particularly if BIG-IP APM obtains incorrect attributes from session variables.
Learn more:
- Go to devcentral.f5.com for APM variable assign examples
- Go to techdocs.f5.com for Session Variables