Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this article, you learn how to integrate Authenion with Microsoft Entra ID. When you integrate Authenion with Microsoft Entra ID, you can:
- Use Microsoft Entra ID to control who can access Authenion.
- Enable your users to be automatically signed in to Authenion with their Microsoft Entra accounts.
- Manage your accounts in one central location: the Azure portal.
Prerequisites
To get started, you need the following items:
- A Microsoft Entra subscription. If you don't have a subscription, you can get a free account.
- Authenion single sign-on (SSO) enabled subscription.
Add Authenion from the gallery
To configure the integration of Authenion into Microsoft Entra ID, you need to add Authenion from the gallery to your list of managed SaaS apps.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Entra ID > Enterprise apps > New application.
In the Add from the gallery section, enter Authenion in the search box.
Select Authenion in the results panel and then add the app. Wait a few seconds while the app is added to your tenant.
Configure Microsoft Entra SSO
Follow these steps to enable Microsoft Entra SSO in the Microsoft Entra admin center.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
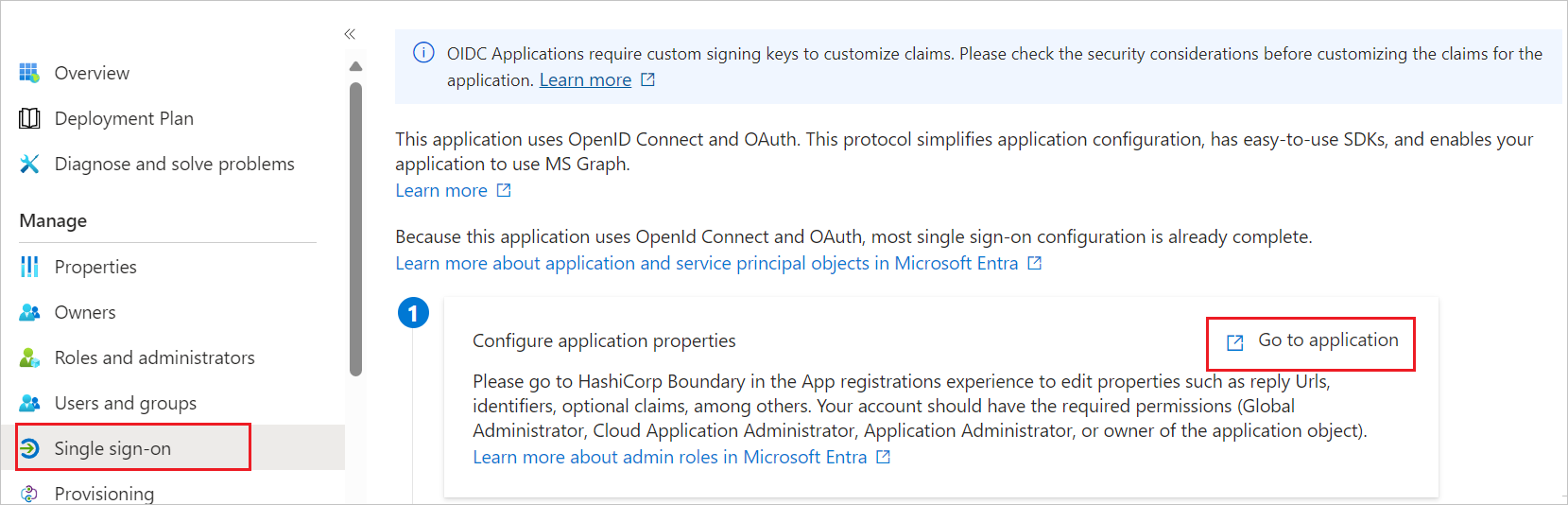
Browse to Entra ID > Enterprise apps > Authenion > Single sign-on.
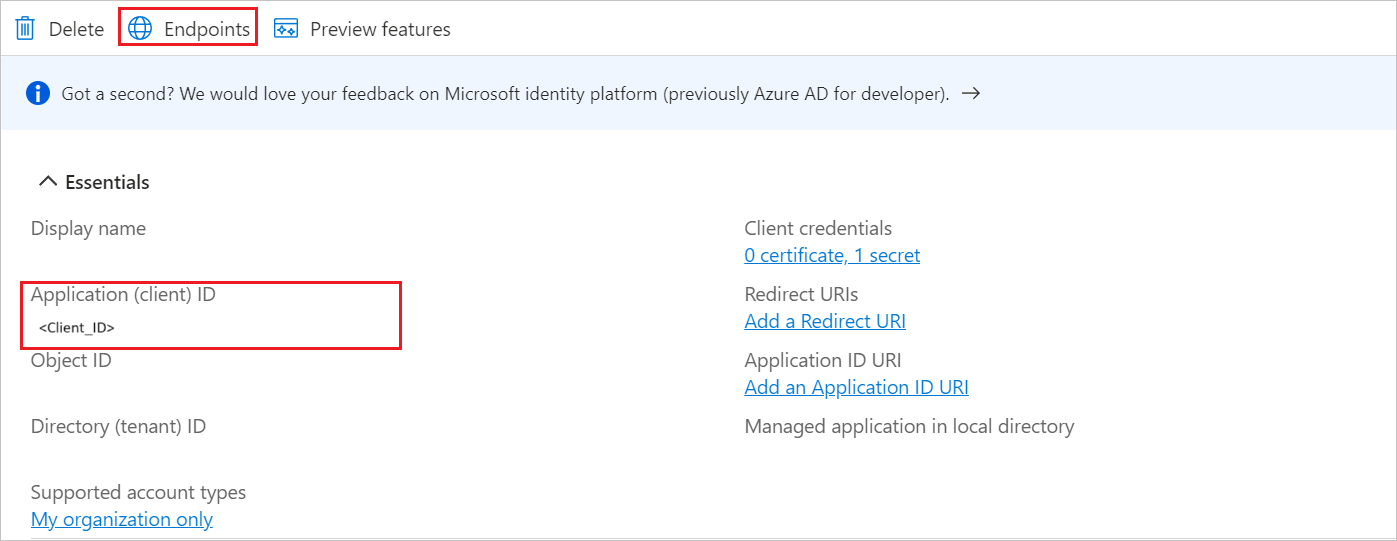
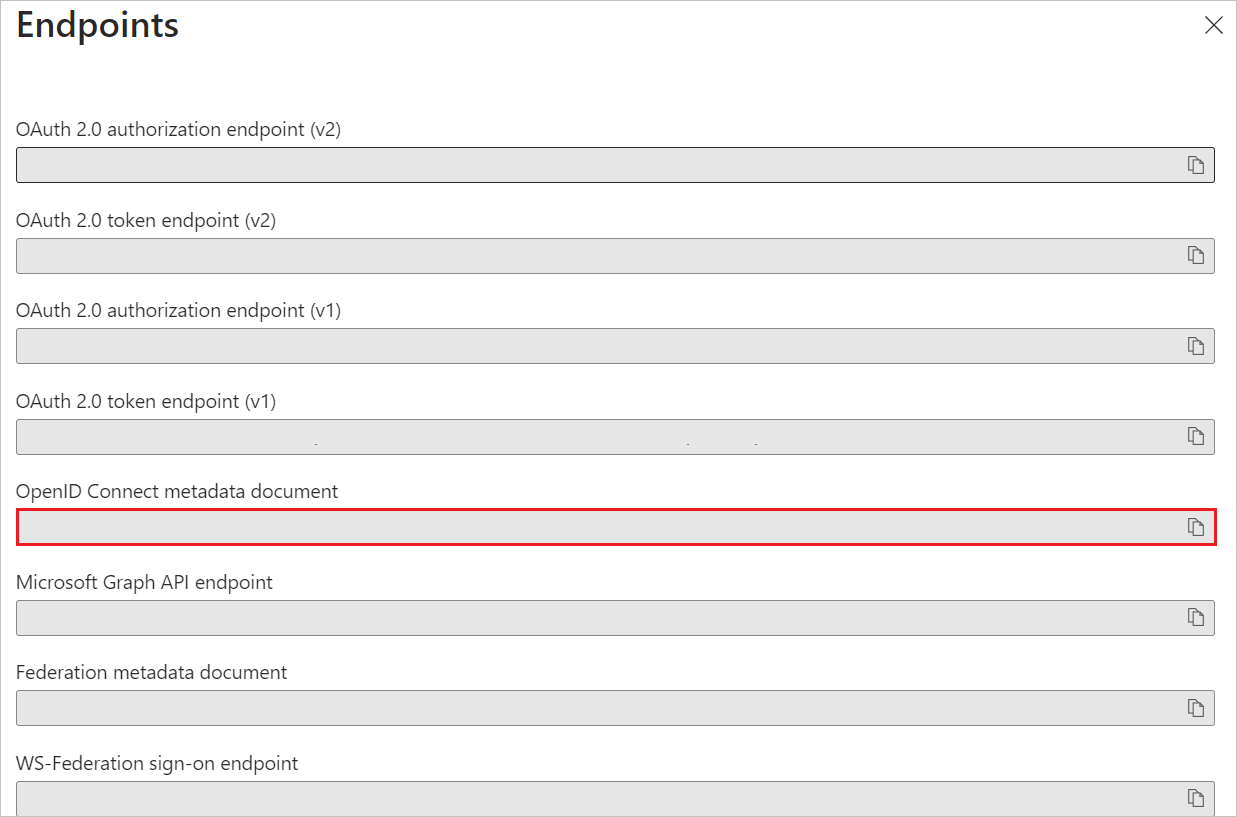
Perform the following steps in the below section:
Navigate to Authentication tab on the left menu and perform the following steps:
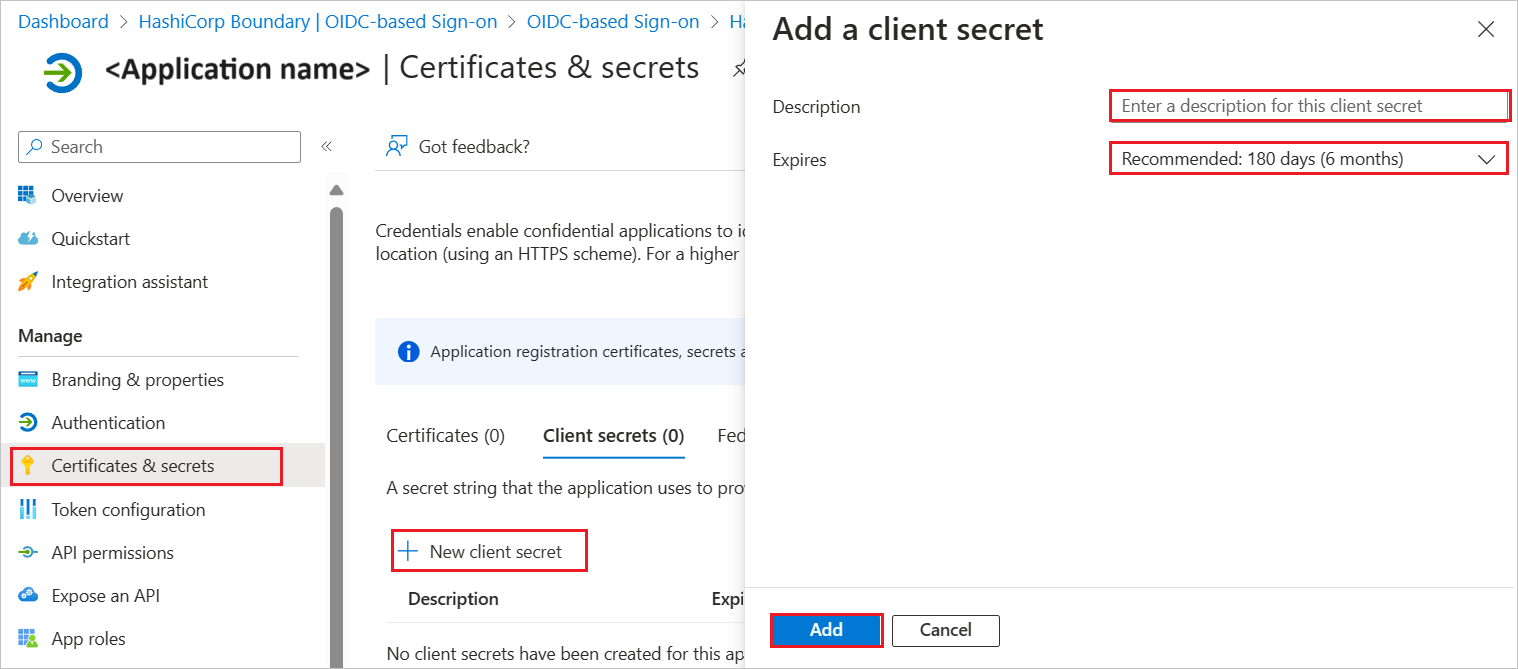
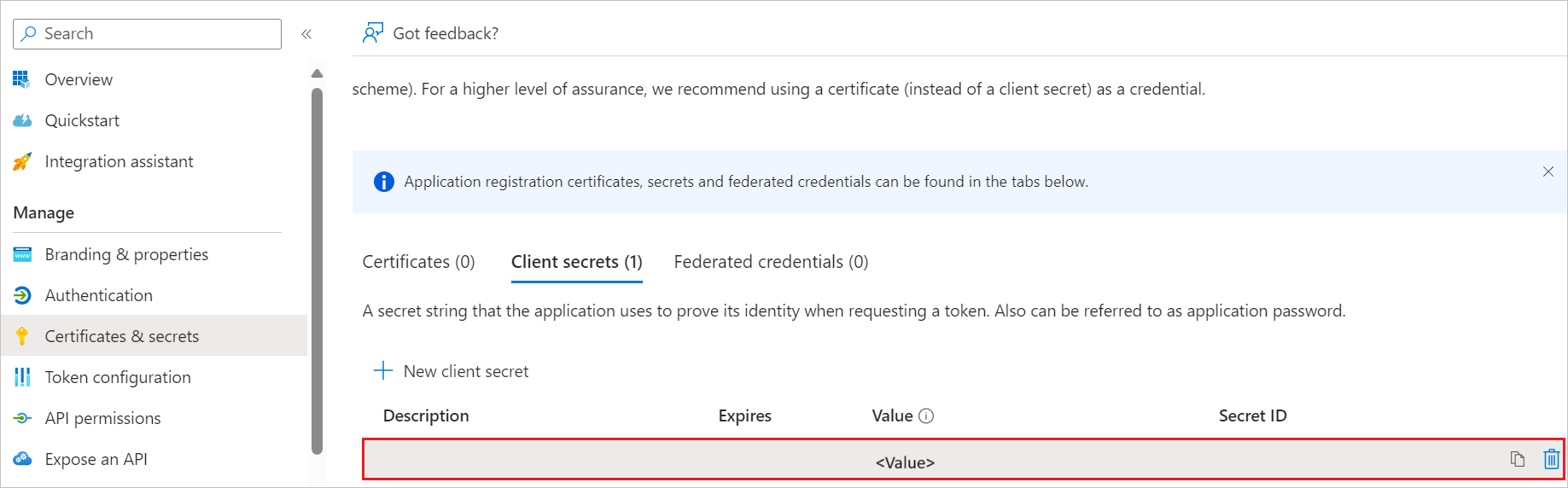
Navigate to Certificates & secrets on the left menu and perform the following steps:
Create a Microsoft Entra test user
In this section, you create a test user called B.Simon.
- Sign in to the Microsoft Entra admin center as at least a User Administrator.
- Browse to Entra ID > Users.
- Select New user > Create new user, at the top of the screen.
- In the User properties, follow these steps:
- In the Display name field, enter
B.Simon. - In the User principal name field, enter the username@companydomain.extension. For example,
B.Simon@contoso.com. - Select the Show password check box, and then write down the value that's displayed in the Password box.
- Select Review + create.
- In the Display name field, enter
- Select Create.
Assign the Microsoft Entra test user
In this section, you enable B.Simon to use single sign-on by granting access to Authenion.
- Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
- Browse to Entra ID > Enterprise apps > Authenion.
- In the app's overview page, select Users and groups.
- Select Add user/group, then select Users and groups in the Added Assignment dialog.
- In the Users and groups dialog, select B.Simon from the Users list, then select the Select button at the bottom of the screen.
- If you're expecting a role to be assigned to the users, you can select it from the Select a role dropdown. If no role has been set up for this app, you see "Default Access" role selected.
- In the Added Assignment dialog, select the Assign button.
Configure Authenion SSO
To complete the OAuth/OIDC federation setup on Authenion side, you need to send the copied values like Tenant ID, Application ID, and Client Secret from Microsoft Entra to Authenion support team. They set this setting to have the OIDC connection set properly on both sides.