Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
In this article, you learn how to integrate SAP Cloud Identity Services with Microsoft Entra ID. When you integrate SAP Cloud Identity Services with Microsoft Entra ID, you can:
- Control in Microsoft Entra ID who has access to SAP Cloud Identity Services.
- Enable your users to be automatically signed-in to SAP Cloud Identity Services and downstream SAP applications with their Microsoft Entra accounts.
- Manage your accounts in one central location.
Tip
Follow the recommendations and best-practice guide "Using Microsoft Entra ID to secure access to SAP platforms and applications" to operationalize the setup.
Prerequisites
The scenario outlined in this article assumes that you already have the following prerequisites:
- A Microsoft Entra user account with an active subscription. If you don't already have one, you can Create an account for free.
- One of the following roles:
- An SAP Cloud Identity Services tenant
- A user account in SAP Cloud Identity Services with Admin permissions.
If you don't yet have users in Microsoft Entra ID, then start with the article plan deploying Microsoft Entra for user provisioning with SAP source and target apps. That article illustrates how to connect Microsoft Entra with authoritative sources for the list of workers in an organization, such as SAP SuccessFactors. It also shows you how to use Microsoft Entra to set up identities for those workers, so they can sign in to one or more SAP applications, such as SAP ECC or SAP S/4HANA.
If you're configuring single sign-in into SAP Cloud Identity Services in a production environment, where you be governing access to SAP workloads using Microsoft Entra ID Governance, then review the prerequisites before configuring Microsoft Entra ID for identity governance before proceeding.
Scenario description
In this article, you configure and test Microsoft Entra single sign-on in a test environment.
- SAP Cloud Identity Services supports service provider (SP) and identity provider (IDP) initiated SSO.
- SAP Cloud Identity Services supports Automated user provisioning.
Before you dive into the technical details, it's vital to understand the concepts you're going to look at. SAP Cloud Identity Services enable you to implement SSO across SAP applications and services, with the same SSO experience as non-SAP applications integrated directly with Microsoft Entra ID as an Identity Provider.
SAP Cloud Identity Services acts as a Proxy Identity Provider to other SAP applications as target systems. Microsoft Entra ID in turn acts as the leading Identity Provider in this setup.
The following diagram illustrates the trust relationship:
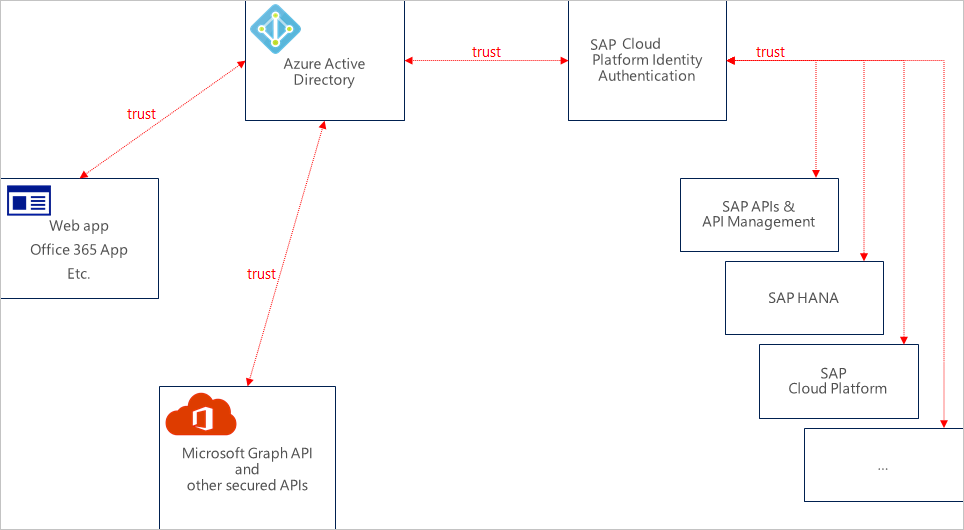
With this setup, your SAP Cloud Identity Services is configured as one or more applications in Microsoft Entra ID. Microsoft Entra is configured as a Corporate Identity Provider in your SAP Cloud Identity Services.
All SAP applications and services that you want to provide single sign-in for this way are subsequently configured as applications in SAP Cloud Identity Services.

User assignment to an SAP Cloud Identity Services application role in Microsoft Entra controls Microsoft Entra token issuance to SAP Cloud Identity Services. The authorization for granting access to specific SAP applications and services, and role assignments for those SAP applications, takes place in SAP Cloud Identity Services and the applications themselves. This authorization can be based on user and groups provisioned from Microsoft Entra ID.
Note
Currently only Web SSO has been tested by both parties. The flows that are necessary for App-to-API or API-to-API communication should work but have not been tested yet. They is tested during subsequent activities.
Adding SAP Cloud Identity Services from the gallery
To configure the integration of SAP Cloud Identity Services into Microsoft Entra ID, you need to add SAP Cloud Identity Services from the gallery to your list of managed SaaS apps.
- Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
- Browse to Entra ID > Enterprise apps > New application.
- In the Add from the gallery section, type SAP Cloud Identity Services in the search box.
- Select SAP Cloud Identity Services from results panel and then add the app. Wait a few seconds while the app is added to your tenant.
Alternatively, you can also use the Enterprise App Configuration Wizard. In this wizard, you can add an application to your tenant, add users/groups to the app, assign roles, and walk through the SSO configuration as well. Learn more about Microsoft 365 wizards.
Configure and test Microsoft Entra SSO for SAP Cloud Identity Services
Configure and test Microsoft Entra SSO with SAP Cloud Identity Services using a test user called B.Simon. For SSO to work, you need to establish a link relationship between a Microsoft Entra user and the related user in SAP Cloud Identity Services.
To configure and test Microsoft Entra SSO with SAP Cloud Identity Services, perform the following steps:
- Configure Microsoft Entra SSO - to enable your users to use this feature.
- Create a Microsoft Entra test user - to test Microsoft Entra single sign-on with B.Simon.
- Assign the Microsoft Entra test user - to enable B.Simon to use Microsoft Entra single sign-on.
- Configure SAP Cloud Identity Services SSO - to configure the single sign-on settings on application side.
- Create SAP Cloud Identity Services test user - to have a counterpart of B.Simon in SAP Cloud Identity Services that's linked to the Microsoft Entra representation of user.
- Test SSO - to verify whether the configuration works.
Obtain the SAP Cloud Identity Services federation metadata
Sign in to the SAP Cloud Identity Services administration console. The URL has the following pattern:
https://<tenant-id>.accounts.ondemand.com/adminorhttps://<tenant-id>.trial-accounts.ondemand.com/admin.Under Applications and Resources, select Tenant Settings.
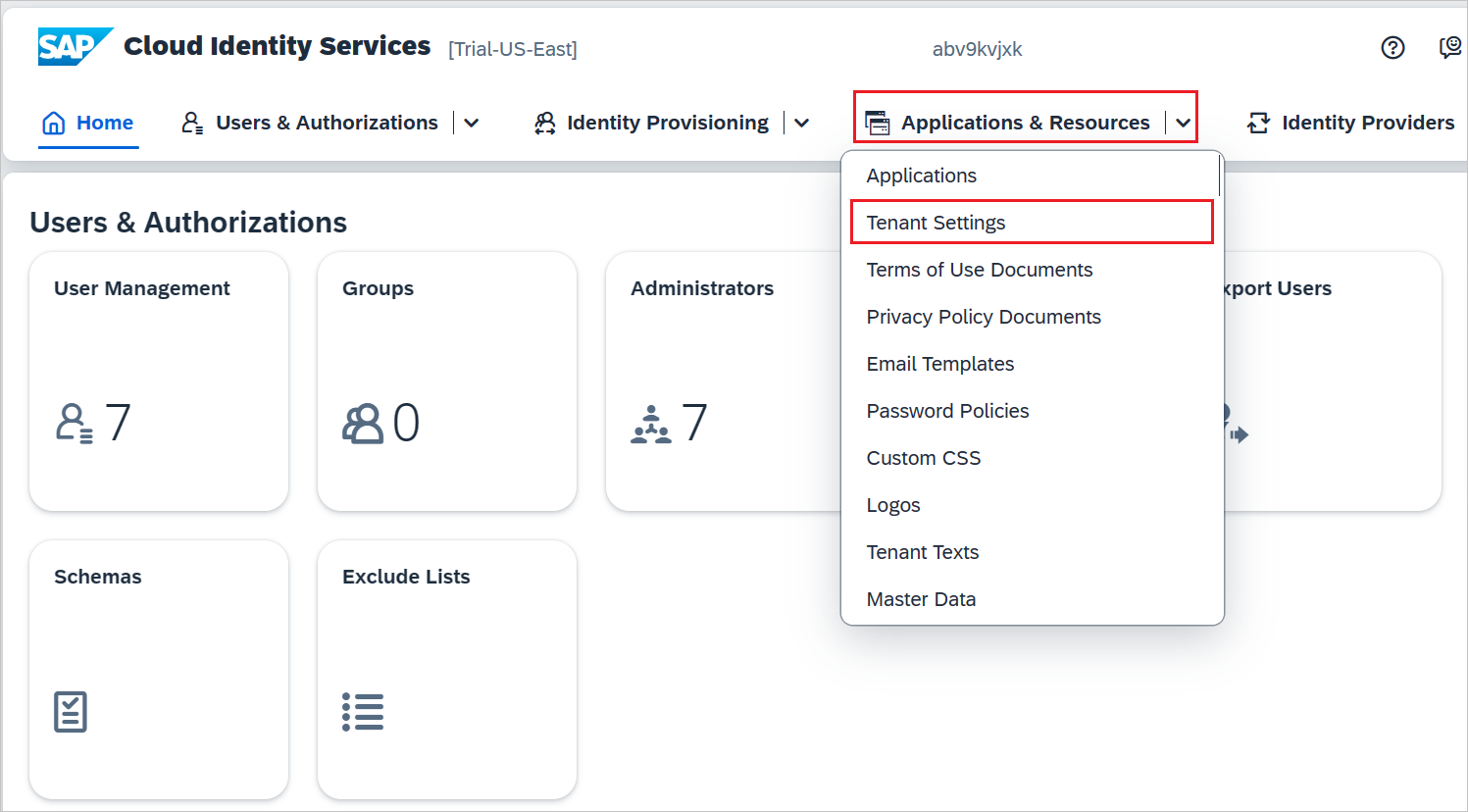
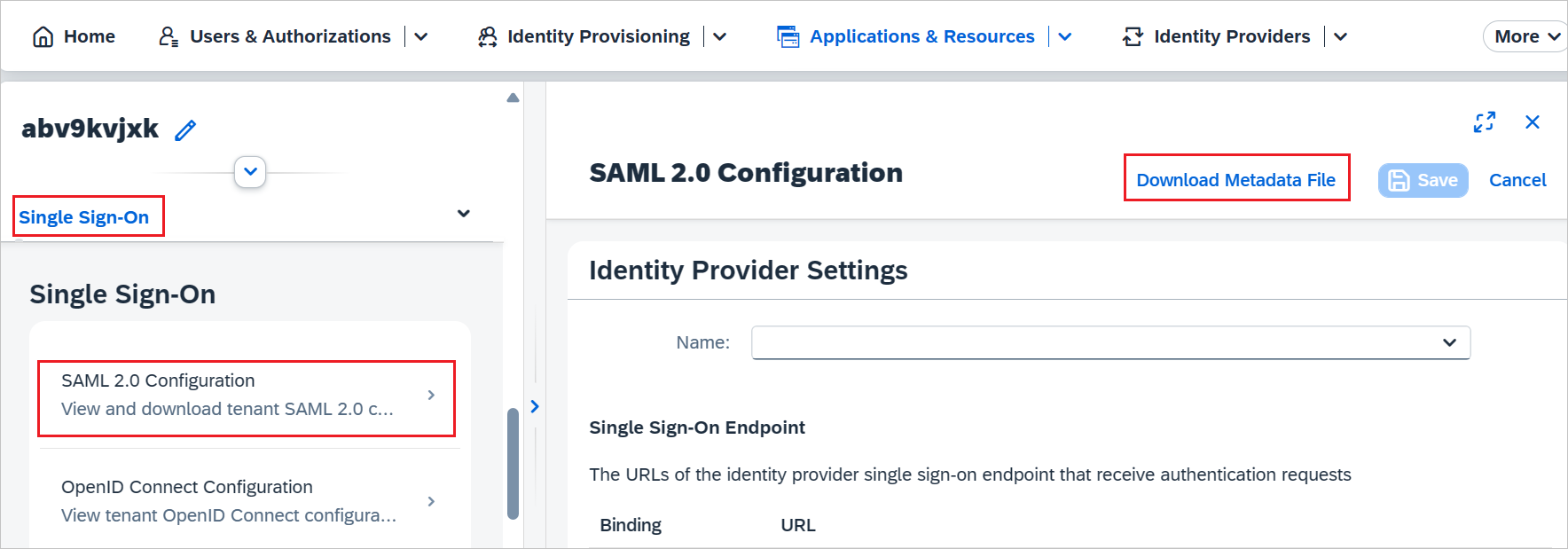
In the Single Sign-On tab, select SAML 2.0 Configuration. Then select Download Metadata File to download the federation metadata of SAP Cloud Identity Services.
Configure Microsoft Entra SSO
Follow these steps to enable Microsoft Entra SSO.
Sign in to the Microsoft Entra admin center as at least a Cloud Application Administrator.
Browse to Entra ID > Enterprise apps. Type the name of your application, such as SAP Cloud Identity Services. Select the application, then select Single sign-on.
On the Select a single sign-on method page, select SAML.
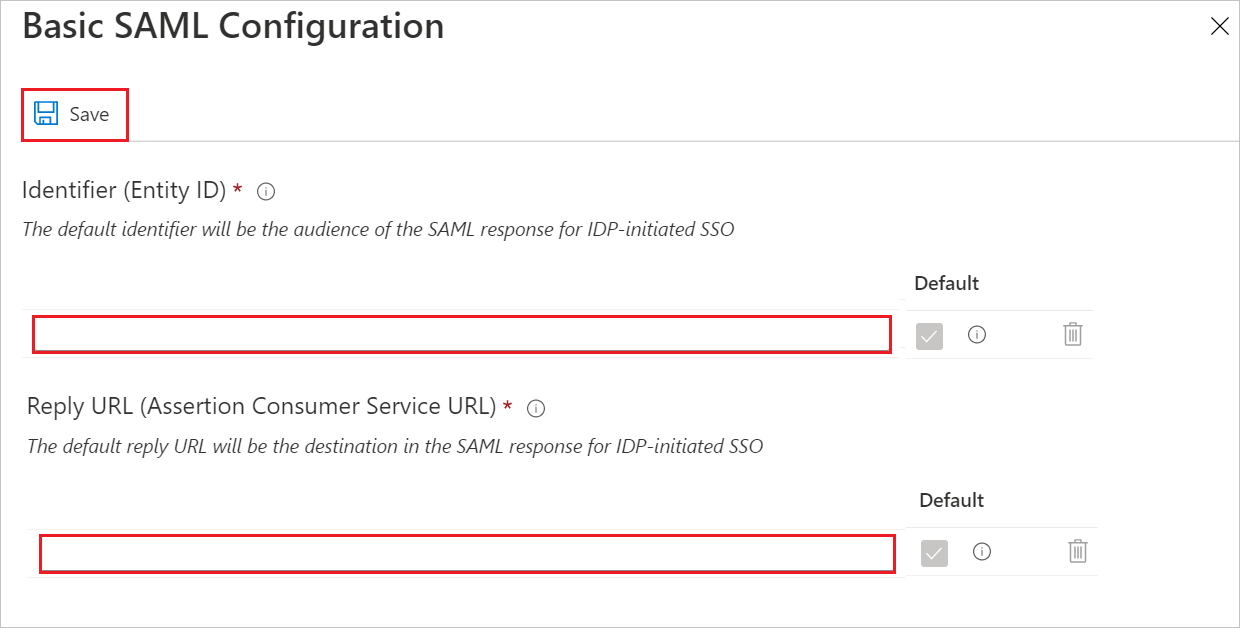
On the Basic SAML Configuration section, if you have Service Provider metadata file from SAP Cloud Identity Services, perform the following steps:
a. Select Upload metadata file.
b. Select folder logo to select the metadata file which you have downloaded from SAP and select Upload.

c. After the metadata file is successfully uploaded, the Identifier and Reply URL values get auto populated in Basic SAML Configuration section.
Note
If the Identifier and Reply URL values don't get auto populated, then fill in the values manually according to your requirement.
If you wish to make further configurations, then on the Set up single sign-on with SAML page, select the pencil icon for Basic SAML Configuration to edit the settings.
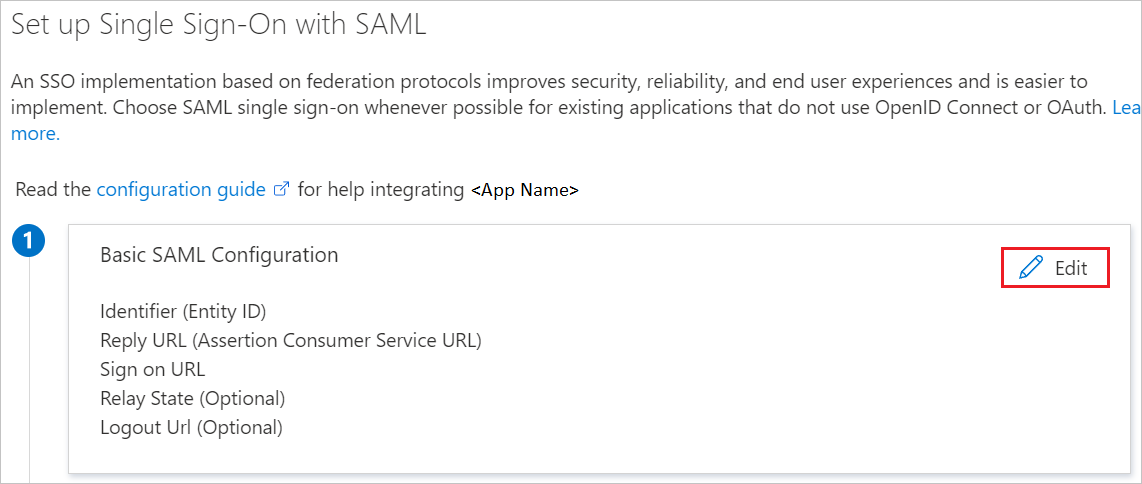
In the Sign on URL (Optional) text box, type your specific business application Sign-on URL.
Note
Update this value with the actual sign-on URL. For more information, see SAP knowledge base article 3128585. Contact the SAP Cloud Identity Services Client support team if you have any questions.
SAP Cloud Identity Services application expects the SAML assertions in a specific format, which requires you to add custom attribute mappings to your SAML token attributes configuration. The following screenshot shows the list of default attributes.
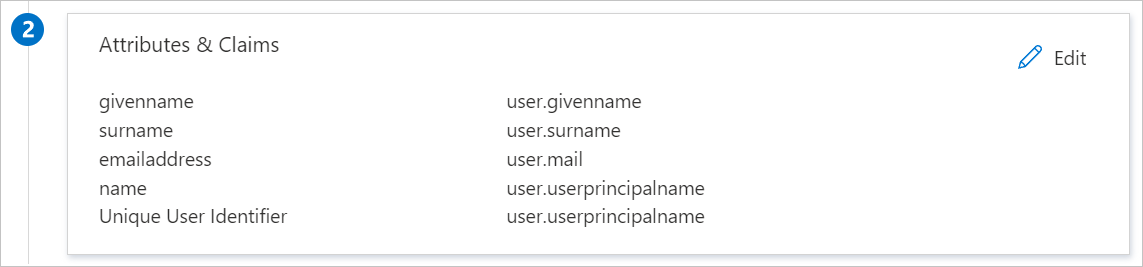
In addition to above, SAP Cloud Identity Services application expects few more attributes to be passed back in SAML response, which are shown below. These attributes are also pre populated but you can review them as per your requirements.
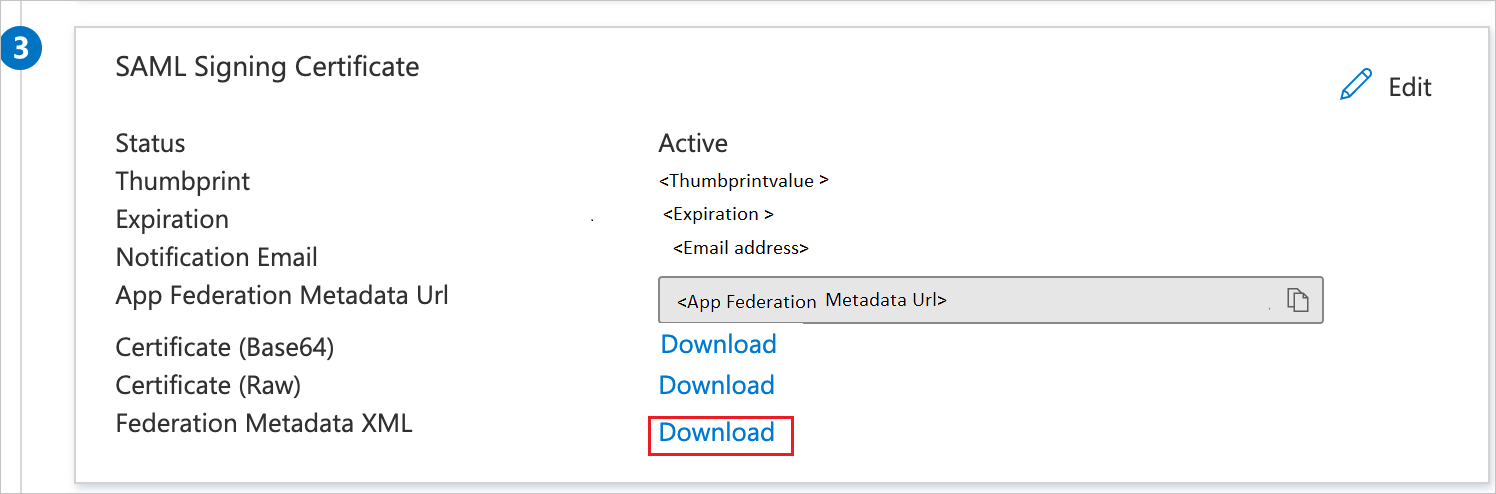
Name Source Attribute firstName user.givenname On the Set up Single Sign-On with SAML page, in the SAML Signing Certificate section, select Download to download the Metadata XML from the given options as per your requirement and save it on your computer.
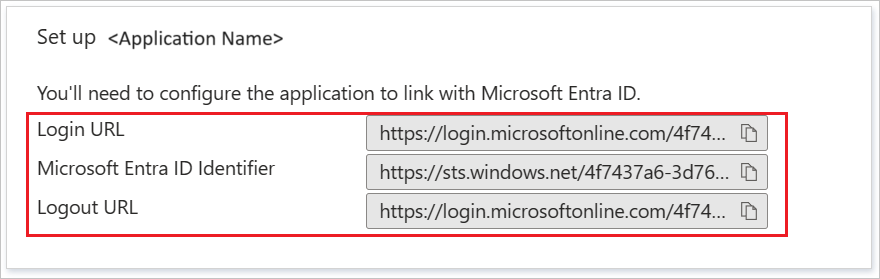
On the Set up SAP Cloud Identity Services section, copy the appropriate URL(s) as per your requirement.
Create and assign Microsoft Entra test user
Follow the guidelines in the create and assign a user account quickstart to create a test user account called B.Simon.
Configure SAP Cloud Identity Services SSO
In this section, you create a Corporate Identity Provider in the SAP Cloud Identity Services administration console. For more information, see Create Corporate IdP in Administration Console.
Sign in to the SAP Cloud Identity Services administration console. The URL has the following pattern:
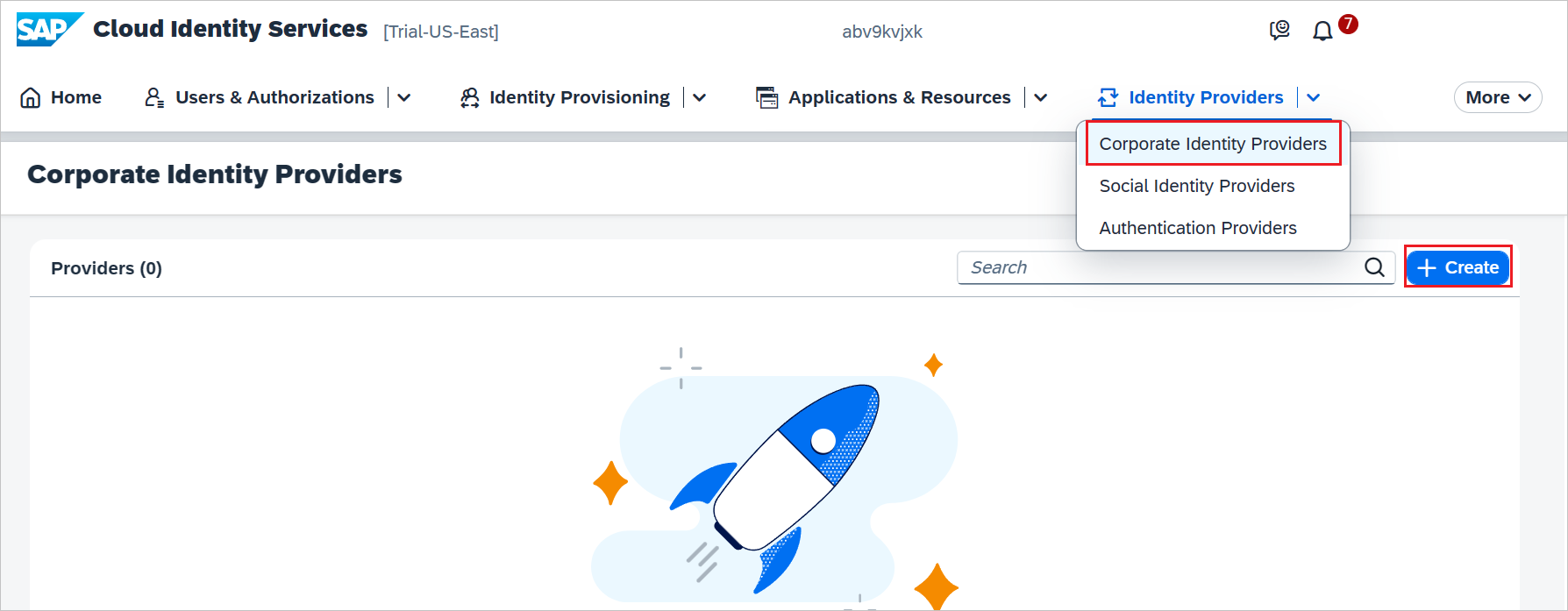
https://<tenant-id>.accounts.ondemand.com/adminorhttps://<tenant-id>.trial-accounts.ondemand.com/admin.Under Identity Providers, choose the Corporate Identity Providers tile.
Select + Create to create an identity provider.
Perform the following steps on Create Identity Provider dialog box.
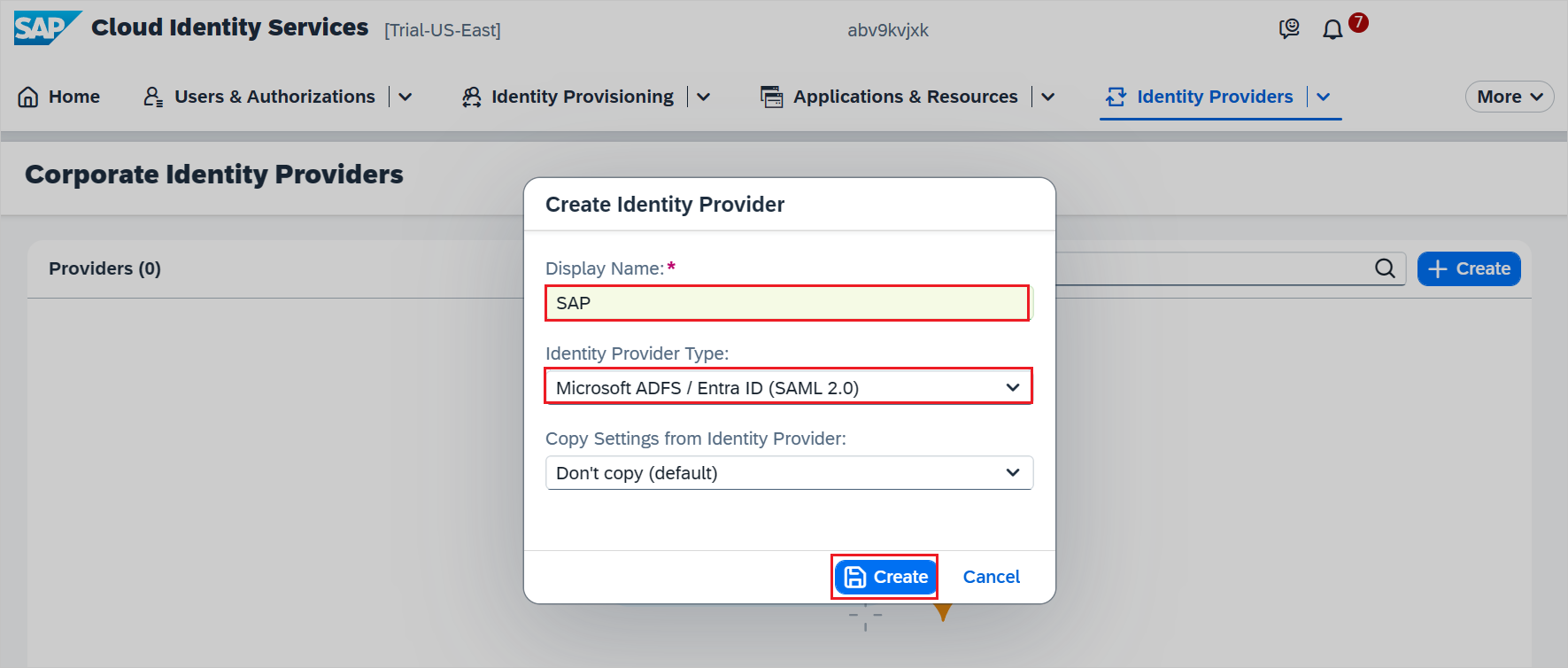
a. Give a valid name in Display Name.
b. Select Microsoft ADFS/Entra ID (SAML 2.0) from the dropdown.
c. Select Create.
Go to Trust -> SAML 2.0 Configuration. On the field for Metadata File, select Browse to upload the Metadata XML file which you have downloaded from the Microsoft Entra SSO configuration.
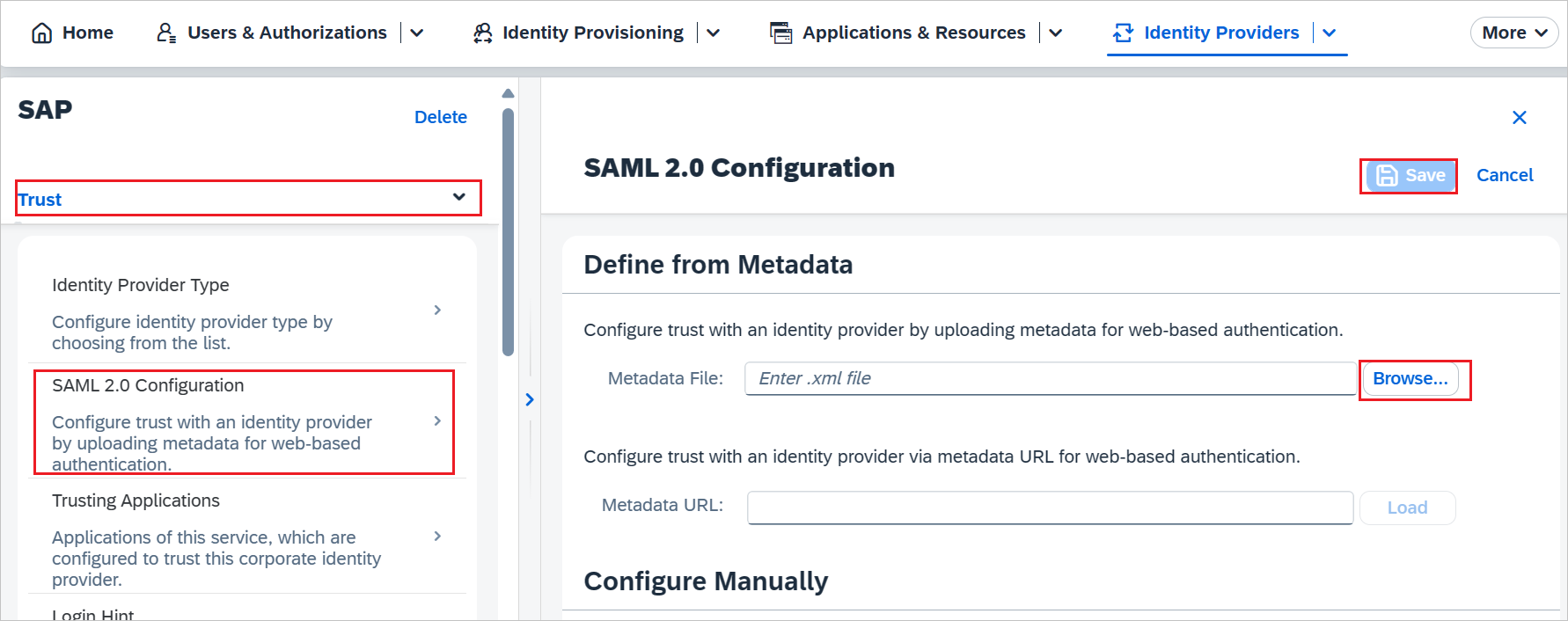
Select Save.
Continue with the following only if you want to add and enable SSO for another SAP application. Repeat the steps under the section Adding SAP Cloud Identity Services from the gallery.
In the Entra side, on the SAP Cloud Identity Services application integration page, select Linked Sign-on.
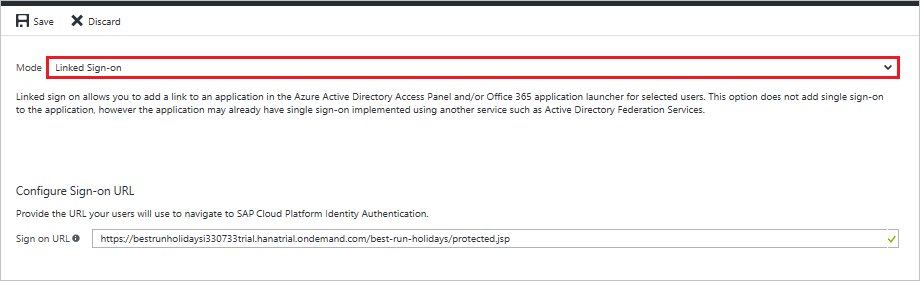
Save the configuration.
For more information, please read the documentation about SAP Cloud Identity Services at Integration with Microsoft Entra ID.
Note
The new application leverages the single sign-on configuration of the previous SAP application. Make sure you use the same Corporate Identity Providers in the SAP Cloud Identity Services administration console.
Create SAP Cloud Identity Services test user
You don't need to create a user in SAP Cloud Identity Services. Users who are in the Microsoft Entra user store can use the SSO functionality.
SAP Cloud Identity Services supports the Identity Federation option. This option allows the application to check whether users who are authenticated by the corporate identity provider exist in the user store of SAP Cloud Identity Services.
The Identity Federation option is disabled by default. If Identity Federation is enabled, only the users that are imported in SAP Cloud Identity Services can access the application.
For more information about how to enable or disable Identity Federation with SAP Cloud Identity Services, see "Enable Identity Federation with SAP Cloud Identity Services" in Configure Identity Federation with the User Store of SAP Cloud Identity Services.
Note
SAP Cloud Identity Services also supports automatic user provisioning, you can find more details here on how to configure automatic user provisioning.
Test SSO
In this section, you test your Microsoft Entra single sign-on configuration with following options, SP initiated and IDP initiated.
If you encounter errors from signing into SAP Cloud Identity Services, with a correlation ID, then in the SAP Cloud Identity Services administration console you can search the troubleshooting logs for that correlation ID. For more information, see SAP knowledge base article 2698571 and SAP knowledge base article 3201824.
SP initiated:
Select Test this application, this option redirects to SAP Cloud Identity Services Sign on URL where you can initiate the login flow.
Go to SAP Cloud Identity Services Sign on URL directly and initiate the login flow from there.
IDP initiated:
- Select Test this application, and you should be automatically signed in to the SAP Cloud Identity Services for which you set up the SSO
You can also use Microsoft My Apps to test the application in any mode. When you select the SAP Cloud Identity Services tile in the My Apps, if configured in SP mode you would be redirected to the application sign-on page for initiating the login flow and if configured in IDP mode, you should be automatically signed in to the SAP Cloud Identity Services for which you set up the SSO. For more information about the My Apps, see Introduction to the My Apps.
Related content
To synchronize users from Microsoft Entra to SAP Cloud Identity Services, enable automated user provisioning.
Once you configure single-sign on to SAP Cloud Identity Services, you can also configure SAP Cloud Identity Services to forward all SSO requests to Microsoft Entra. When this option is enabled in SAP Cloud Identity Services, then each time a user tries to access an application connected to SAP Cloud Identity Services for the first time, SAP Cloud Identity Services will forward an authentication request to Microsoft Entra, even when the user has an active session in SAP Cloud Identity Services.
You can also enforce session controls, which protect exfiltration and infiltration of your organization’s sensitive data in real time. Session controls extend from Conditional Access. Learn how to enforce session control with Microsoft Defender for Cloud Apps.
You can also manage access to SAP BTP applications, using Microsoft Entra ID Governance to populate groups associated to roles in the BTP role collection. For more information, see Managing access to SAP BTP.
Consult the recommendations and best-practice guide to operationalize the setup.