3.2.2 Interactive Domain Logon by Using an X.509 Certificate
This example describes interactive domain logon by using an X.509 certificate to obtain a service ticket. It covers the use cases Authenticate User or Computer Identity Using an X.509 Certificate (section 2.5.5.1.2) and Interactive Domain Logon: Service Ticket for Client Computer (section 2.5.3.1.1).
Prerequisites
The Authentication Authority (AA) is available.
The Authentication Client has access to the X.509 certificate and private key of the requested user account.
Initial System State
The user has not been authenticated to the AA.
The Authentication Client does not have a service ticket for the client computer.
Final System State
The AA has interactively authenticated the user, and the Authentication Client has obtained a service ticket for the client computer.
Sequence of Events
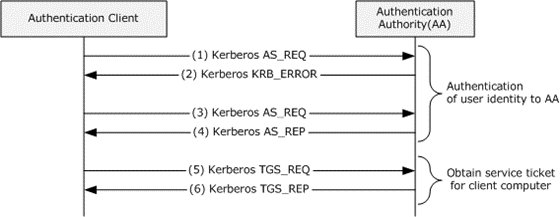
Figure 31: Interactive domain logon by using an X.509 certificate
Authentication of User Identity to Authentication Authority (see section 2.5.5.1.2)
Step 1: Same as step 1 in section 3.2.1.
Step 2: Same as step 2 in section 3.2.1.
Step 3: The Authentication Client sends a KRB_AS_REQ message for a ticket-granting ticket (TGT) with PA-PK-AS-REQ as pre-authentication data to the KDC. The client builds the pre-authentication data as described in [RFC4556] section 3.2.1.
Step 4: The KDC validates the KRB_AS_REQ message ([RFC4120] section 3.1.2), which includes verifying the user's signature and validating the certificate ([RFC4556] section 3.2.2). If the KRB_AS_REQ message is valid, the KDC builds the TGT with a PAC ([MS-KILE] section 3.3.5.6.4) that contains group membership information in the authorization_data field of the TGT, generates a KRB_AS_REP message ([RFC4556] section 3.2.3) from the TGT and the session key, and sends the reply to the client.
Service Ticket for Client Computer (see section 2.5.3.1.1)
Step 5: Same as step 5 in section 3.2.1.
Step 6: Same as step 6 in section 3.2.1.
The client validates the KRB_TGS_REP message ([MS-KILE] section 3.3.4). If the KRB_TGS_REP message is valid, the service ticket is interpreted by the Kerberos runtime within the local client computer.